Chain Trade Size Chart: Spot Smart Money Moves
Master the on-chain trade size chart to analyze market structure and copy trade with precision. Learn to build and read charts with Wallet Finder.ai.

May 24, 2026
Wallet Finder

March 5, 2026
DeFi protocols face significant risks from authorization flaws, which can lead to financial losses, reduced user trust, and increased regulatory scrutiny. These vulnerabilities often arise from weak access controls, poor key management, and governance token centralization. Attackers exploit these flaws using tactics like flash loan attacks, admin key compromises, and governance manipulation. High-profile incidents, such as the Ronin Bridge hack and Terra's stablecoin collapse, highlight the severe consequences of these issues.
Insufficient audits: Many protocols launch without proper security reviews, leaving critical vulnerabilities.
Governance token risks: Centralized voting power can lead to malicious protocol changes.
Flash loan attacks: Exploit system states within a single transaction block.
Admin key compromises: Poor key management opens doors for attackers.

WalletFinder.ai enhances security by monitoring wallet activity across Ethereum, Solana, and Base. Features include:
Take control of DeFi risks. Start your free trial with WalletFinder.ai today.
Understanding the vulnerabilities and techniques used by attackers is essential for protecting DeFi protocols. These risks open the door to potential exploits, jeopardizing both the systems and the trust of their users. Below, we explore some of the most common risk factors in DeFi authorization and the methods attackers use to exploit them. To see how human behavior and online discussions influence market movements, check out How Social Media Sentiment Predicts Crypto Prices for insights into the connection between hype, emotion, and price trends.
One of the most pressing issues is insufficient smart contract auditing. Many DeFi projects rush to launch without conducting thorough security reviews. This haste often leaves critical vulnerabilities undetected. Smart contracts that manage millions - or even billions - of dollars may contain coding errors that allow excessive permissions or fail to implement proper access controls. Such oversights can have devastating consequences.
Another key issue is poor key management, which leaves protocols vulnerable to key compromises. For instance, using single-signature wallets for administrative tasks or storing private keys in insecure locations makes these systems easy targets for attackers. While implementing multi-signature wallets and hardware security modules can reduce these risks, many projects skip these measures during development, exposing themselves to attacks.
Governance token concentration is another significant risk. When a small group of addresses holds the majority of voting power, they can manipulate protocol parameters, execute malicious upgrades, or even drain treasury funds. This kind of centralization undermines the decentralized principles that DeFi is built upon and creates single points of failure.
Inadequate role-based access controls are also a frequent issue. Many protocols grant broad permissions to multiple addresses without carefully defining roles or implementing checks and balances. This lack of structure allows unauthorized users to access critical functions, such as minting tokens, altering interest rates, or pausing operations, increasing the likelihood of misuse.
Lastly, weak oracle dependencies introduce vulnerabilities that attackers can exploit. Protocols relying on a single oracle source or failing to validate data properly are susceptible to price manipulation attacks. Since oracle data often influences key decisions - like liquidation thresholds or collateral requirements - flawed or manipulated data can lead to unauthorized actions.
Attackers exploit these weaknesses through a variety of sophisticated methods, which are detailed below.
Flash loan attacks are a common tactic that targets authorization flaws. In these attacks, an attacker borrows a large amount of cryptocurrency without collateral, manipulates the protocol's state to gain unauthorized access, executes malicious transactions, and repays the loan - all within a single block. This rapid execution leaves little time for detection or intervention.
Admin key compromises directly target the private keys of protocol administrators. Attackers often use phishing, social engineering, or exploit insecure key storage to gain access. Once they have administrative privileges, they can alter smart contract parameters, drain treasury funds, or redirect user assets to their own wallets.
In governance manipulation attacks, attackers exploit voting mechanisms to seize control of a protocol. By acquiring governance tokens - either through market purchases or flash loans - they can propose malicious changes and push them through before the community has a chance to react. Protocols with low voter participation or short voting windows are particularly vulnerable to this type of attack.
Cross-protocol exploitation takes advantage of the interconnected nature of DeFi systems. Attackers identify vulnerabilities in one protocol and use its integration with others to bypass authorization controls. For example, they might manipulate a lending protocol by exploiting its reliance on a compromised price oracle, leading to unauthorized liquidations or other damaging actions.
Time-based attacks exploit delays in authorization mechanisms. While time locks or delayed execution are often implemented to enhance transparency and allow for community oversight, attackers can use these delays to their advantage. By initiating malicious transactions and manipulating protocol states during the waiting period, they can ensure their unauthorized actions succeed.
Finally, reentrancy attacks target the way authorization logic is executed. These attacks involve calling back into a smart contract before a previous function call is completed. By doing so, attackers can bypass authorization checks that assume functions execute in a linear, atomic fashion. This technique allows them to drain funds or gain unauthorized access before the system can complete its checks.
The combination of these risk factors and attack methods creates a challenging environment for DeFi protocols. Addressing these vulnerabilities requires constant vigilance, strong security practices, and a commitment to thorough testing and monitoring.
The article identifies the main attack methods used to exploit authorization flaws but does not address the specific technical methodologies that security teams and protocol developers use to detect authorization vulnerabilities before deployment. Formal verification and static analysis for smart contract authorization represent the most rigorous pre-deployment defenses available, and the gap between protocols that have been subjected to these methods and those that have not correlates strongly with the probability of post-deployment authorization exploits. Understanding these methodologies helps both developers evaluate their security posture and users assess protocol risk before committing capital.
The majority of documented DeFi authorization exploits share a common root cause: the authorization logic in the deployed smart contract did not match the authorization logic the developers intended to implement. This discrepancy can arise from implementation errors where correct intent is translated into incorrect code, from specification errors where the intended logic itself was flawed, or from interaction effects where individually correct components produce incorrect authorization outcomes when composed. Standard audit methodologies that review code quality and test known vulnerability patterns are effective at catching implementation errors but are structurally limited in their ability to detect specification errors and composition effects, which require different verification approaches.
Formal verification addresses this gap by mathematically proving that a smart contract's behavior conforms to a formal specification of its intended behavior across all possible inputs and execution states, rather than testing a finite sample of cases. A formal specification of authorization logic might express properties such as "no address other than the designated admin role can call the setFeeRate function" or "the total amount withdrawable from the treasury in any 24-hour window cannot exceed the governance-approved withdrawal limit." Proving these properties hold across all possible execution paths eliminates entire classes of authorization vulnerabilities that testing-based approaches can only probabilistically reduce.
Specification language frameworks provide the formal mathematical language in which authorization properties are expressed before the verification process can be applied. The three specification frameworks most widely used in DeFi smart contract verification are the K Framework, Certora's Prover specification language CVL, and the Scribble annotation language developed by Diligence. Each operates at a different level of abstraction and integrates differently with the development workflow, creating trade-offs between expressiveness, usability, and the scope of properties that can be formally verified.
The K Framework operates at the level of the EVM bytecode semantics, meaning properties specified in K are verified against the actual compiled bytecode that will be deployed rather than the Solidity source code. This approach eliminates the possibility of compiler translation errors creating discrepancies between verified source behavior and deployed bytecode behavior, which is a meaningful source of risk in high-security contexts. The trade-off is that K Framework specifications require deep expertise in formal methods and EVM semantics, making the methodology most accessible to specialized security teams rather than protocol development teams working within standard timelines.
Certora's Prover operates against Solidity source code and uses the CVL specification language to express authorization invariants that the prover then attempts to verify or falsify. The Certora Prover has been applied to authorization logic in protocols including Aave, Compound, and Balancer, and its integration with standard Solidity development workflows makes it more accessible than lower-level bytecode verification. A CVL rule expressing an authorization property for a treasury withdrawal function might specify that any call to the withdrawFunds function that succeeds must have been initiated by a caller whose address is present in the governance-approved withdrawal role mapping and whose requested amount does not exceed the per-period limit. The prover then exhaustively searches for any execution path that would allow the function to succeed in violation of this specification, returning either a formal proof of compliance or a counterexample demonstrating the violation.
Mutation testing complements formal specification by evaluating the quality of the test suite used alongside formal methods. Mutation testing systematically introduces small changes to the smart contract source code, each representing a plausible authorization logic error such as replacing a require statement with a weaker condition or inverting an access control check, and then measures whether the existing test suite detects each mutation. A test suite that fails to detect a high fraction of plausible mutations is providing false confidence in authorization correctness because the same mutations it misses are the same category of errors that real implementation mistakes would introduce. Protocols with formal verification coverage complemented by high mutation detection rates have demonstrably stronger authorization security guarantees than those relying on either approach alone.
Invariant monitoring extends formal specification methodology from pre-deployment verification into production operation by continuously checking that the authorization invariants proved during verification continue to hold in the live deployed contract as protocol state evolves. The motivation for runtime invariant monitoring is that formal verification proves properties hold across all possible execution paths given the contract code, but does not account for operational conditions including privileged key compromise, governance manipulation, or unexpected state combinations created by interactions with external contracts that post-date the original verification.
OpenZeppelin Defender and Forta represent the two most widely deployed runtime monitoring frameworks for DeFi authorization invariants. Defender operates as a centralized monitoring service where protocol teams configure watchers that alert on specific on-chain conditions, while Forta operates as a decentralized network of detection bots that independently monitor for defined threat patterns and publish alerts to subscribers. The complementary deployment of both frameworks provides defense in depth against both protocol-specific authorization anomalies, which are best detected by Defender watchers configured with protocol-specific knowledge, and known cross-protocol attack patterns, which Forta's community-maintained bot network detects through pattern matching against documented exploit signatures.
Circuit breaker implementation converts runtime invariant monitoring from a passive alerting system into an active authorization defense by automatically triggering protocol pause functionality when monitored invariants are violated. A circuit breaker watching for treasury withdrawal amounts exceeding governance-approved per-period limits can trigger the protocol's pause mechanism without requiring human intervention in the seconds between when an unauthorized withdrawal is detected and when it completes. The trade-off of automated circuit breakers is the risk of false positive triggers that pause legitimate protocol operations, which requires careful calibration of circuit breaker thresholds and reliable governance processes for resuming paused operations. Protocols that have pre-approved circuit breaker override procedures with defined authorization requirements for resumption can deploy more sensitive circuit breakers with lower false negative rates because the cost of false positives, while operationally disruptive, is bounded by the existence of the override process.
Examining real-world incidents in DeFi highlights how authorization flaws can lead to devastating financial losses and compromise the integrity of protocols. Each case sheds light on unique vulnerabilities, emphasizing the importance of addressing these issues.
In this case, a weakness in a layer-2 donation mechanism allowed an attacker to manipulate accounting processes. The incident highlights the dangers of incomplete security audits, which can leave protocols exposed to exploitation.
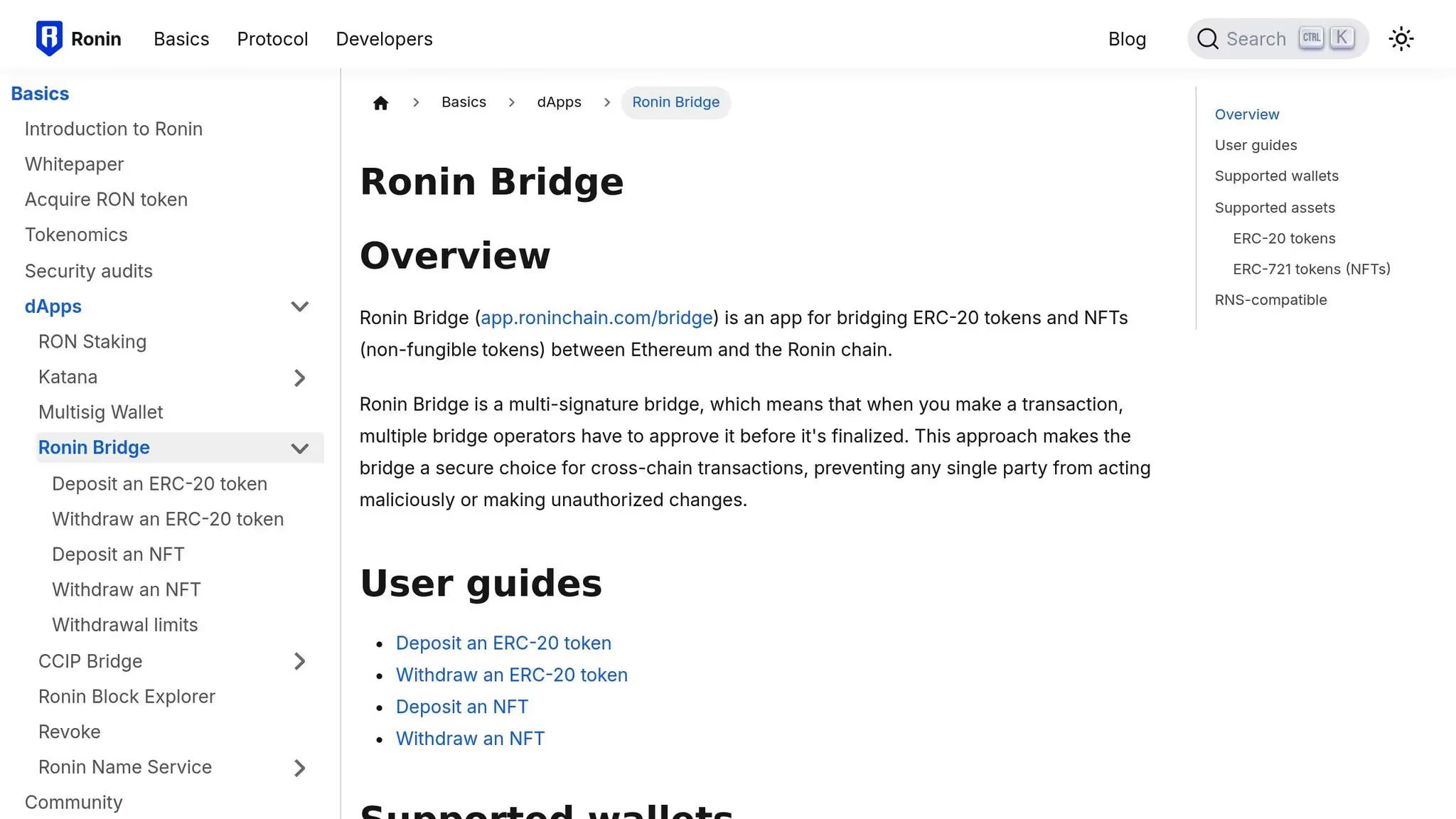
This breach stemmed from poor administrative key management, enabling unauthorized withdrawals through weaknesses in validator controls. The attack revealed that even multi-signature setups are not immune to the risks of centralization when key management is flawed.
Governance missteps and inadequate risk management led to a rapid depeg of Terra's stablecoin, triggering widespread market chaos. The failure of automated stabilization mechanisms in this scenario serves as a stark reminder of the risks tied to poorly managed systems.
These examples make it clear that addressing authorization flaws is not just a technical necessity but a critical step toward ensuring the stability and trustworthiness of DeFi protocols.
Drawing lessons from past incidents, these strategies aim to address and reduce the risks associated with authorization flaws in DeFi systems.
Authorization flaws in DeFi can have far-reaching consequences. They disrupt liquidity, diminish user confidence, and attract increased regulatory scrutiny. When breaches occur, users often withdraw their funds, leading to reduced trading volumes and potentially destabilizing interconnected protocols. Over time, repeated incidents make users more cautious about engaging with DeFi platforms, and this hesitancy can prompt regulators to impose stricter oversight, creating additional challenges for projects in the space.
Addressing authorization flaws requires a layered approach that tackles both technical and operational vulnerabilities. Here are some of the most effective strategies:
Wallet analytics play a crucial role in identifying and addressing potential authorization vulnerabilities, complementing traditional security measures. These tools excel at recognizing patterns that might go unnoticed, tracking fund movements, and issuing timely alerts about suspicious activities. Wallet Finder.ai provides a suite of features that demonstrate how these analytics can mitigate authorization risks in decentralized finance (DeFi) protocols.
Wallet Finder.ai equips users with tools designed to detect and analyze risks tied to authorization flaws. Its real-time monitoring tracks wallet activities across Ethereum, Solana, and Base networks, offering immediate alerts when unusual behaviors arise.
One standout feature is the Telegram alert system, which notifies users of sudden large withdrawals or unusual transaction patterns. These alerts can be customized based on transaction volume, profit changes, or risk levels, enabling users to act swiftly when potential authorization issues are detected.
The platform’s advanced filters allow users to analyze wallets by profit and loss (PnL), win rates, and risk metrics. These insights help pinpoint wallets involved in exploits or exhibiting behavior indicative of authorization bypass attempts. Additionally, cross-chain analytics provide a broader perspective by tracking activities across multiple networks, making it easier to detect coordinated attacks.
Another valuable tool is the token concentration analysis feature, which identifies centralization risks in governance tokens or other protocol-specific assets. By examining token distribution and spotting whale concentrations, users can detect vulnerabilities that might lead to authorization exploits. These features not only enhance risk detection but also support detailed forensic investigations.
When authorization flaws are exploited, Wallet Finder.ai's data export tools become invaluable for forensic analysis. Users can export wallet data in formats like CSV or Excel, enabling a closer examination of transaction patterns before and after suspected incidents.
The wallet overview feature provides a clear view of profit timelines and investment flows. By analyzing historical data, investigators can trace suspicious activities and pinpoint the moments where authorization controls may have been compromised.
Security statistics integration offers another layer of protection by automating contract audits. These audits highlight vulnerabilities such as contract ownership issues, blacklist statuses, or honeypot risks, helping users determine whether wallets are interacting with potentially compromised tokens or protocols.
For a broader perspective, the platform’s X/Twitter sentiment scoring feature measures social sentiment around specific tokens and protocols. Sudden shifts in sentiment can signal growing awareness of authorization flaws or ongoing exploits, offering early warnings for potential threats.
To further enhance monitoring, wallet lists and tracking tools allow users to keep tabs on known bad actors or wallets linked to previous exploits. By maintaining a curated list of suspicious addresses, the community can collectively monitor for new activities that may signal fresh authorization attacks or the reuse of compromised credentials.
Lastly, the trending tokens feature helps identify assets showing unusual activity, which could be tied to authorization exploits. By comparing token performance across chains and analyzing concentration patterns, users can uncover anomalies requiring further investigation.
The article covers prevention strategies and wallet analytics for detecting authorization vulnerabilities but does not address what protocols should do after an authorization exploit has occurred. Post-exploit recovery architecture is a critical but consistently underprepared component of DeFi protocol security planning, and the difference in outcomes between protocols that have pre-defined recovery frameworks and those that improvise responses in real time is substantial both in total losses and in the speed and completeness of user fund recovery. Understanding recovery architecture helps protocol teams prepare more effective response plans and helps users evaluate the resilience of protocols before committing capital.
The first hours following the detection of an authorization exploit are the period of highest potential loss amplification and the period when pre-planned responses provide the greatest value relative to improvised ones. An authorization exploit that drains 20 percent of protocol TVL in the first 10 minutes may drain the remaining 80 percent in the subsequent 20 minutes if the protocol has no automated pause mechanism and requires human coordination to halt operations. Protocols with pre-deployed pause mechanisms triggered by governance multi-sig or automated circuit breakers can contain exploit losses to the initial window of attacker activity, while protocols requiring social coordination to locate keyholders and execute pause transactions may find the attacker has extracted full TVL before pause is achieved.
Pause mechanism architecture determines the authorization structure for halting protocol operations, which is itself a security-critical authorization decision. A pause mechanism controlled by a single admin key is vulnerable to the same key compromise risks that cause many authorization exploits in the first place. A pause mechanism requiring full governance vote execution to trigger is too slow to be useful in the minutes-to-hours window of an active exploit. The design solution widely adopted in protocols including Aave and Compound is a tiered pause architecture where a Guardian role controlled by a protocol-defined multi-sig address can trigger an immediate pause without governance vote, while unpausing requires governance vote execution with appropriate timelock, creating asymmetric authorization requirements that allow fast defensive action while preventing the pause mechanism itself from being abused to disable the protocol maliciously.
White hat coordination has become an increasingly important component of post-exploit recovery as the DeFi security community has developed norms and infrastructure for returning exploited funds in exchange for recognition and bug bounty payments. Several major DeFi exploits have resulted in partial or full fund recovery through white hat coordination, including the Euler Finance exploit of March 2023 where approximately $197 million was eventually returned after the protocol engaged in direct communication with the attacker and offered a substantial bug bounty payment. The structural conditions that make white hat coordination possible include the pseudonymous but traceable nature of blockchain transactions, which means attackers who do not successfully launder funds face meaningful on-chain forensic exposure, and the development of community norms and legal precedents that provide incentive structures encouraging return of funds in exchange for legal safe harbor.
Responsible disclosure frameworks define the authorization and process for security researchers who discover authorization vulnerabilities before they are exploited to report them in exchange for bug bounty payments without public disclosure that would enable exploitation. The Immunefi platform has become the dominant bug bounty infrastructure in DeFi, with total bounty payouts across its platform exceeding $100 million through 2024. The authorization structure of a responsible disclosure program must balance incentive adequacy, where bounty amounts must be large enough relative to exploitation value to make disclosure more attractive than exploitation, with governance controls that prevent abuse of the disclosure process itself as a social engineering vector.
Treasury reserve architecture for post-exploit recovery funds determines whether a protocol can compensate affected users from protocol-owned reserves or must rely entirely on external insurance, governance token raises, or accepting permanent losses. Protocols including Aave have established protocol-owned Safety Modules that accumulate reserves through protocol fee revenue and can be drawn upon through governance vote to compensate users affected by authorization exploits or other protocol failures. The authorization structure for Safety Module deployment must balance accessibility, so that the module can be activated quickly enough to provide meaningful relief to affected users, with governance controls that prevent Safety Module funds from being extracted through the same authorization vulnerabilities that caused the original exploit.
On-chain forensic methodology for tracing funds extracted through authorization exploits follows the stolen assets through the blockchain transaction graph from the initial exploit transaction through any subsequent mixing, bridging, or exchange operations. The methodology is important both for potential fund recovery and for regulatory compliance reporting, as protocols subject to applicable law may have obligations to report known financial crimes to relevant authorities and to cooperate with law enforcement investigations.
Transaction graph analysis begins at the exploit transaction identified by its hash and traces all outbound transfers from the recipient address through subsequent transactions, creating a directed graph where nodes are addresses and edges are transfers with amounts and timestamps. The analysis must handle several categories of obfuscation that sophisticated attackers use to complicate tracing: chain-hopping through cross-chain bridges that create discontinuities in the transaction graph requiring parallel analysis on each destination chain, mixer usage that combines funds from multiple sources and distributes them to multiple recipients in ways designed to break the direct linkage between input and output addresses, and exchange deposits where funds are deposited to centralized exchange addresses that aggregate deposits from many users making individual fund attribution difficult without exchange cooperation.
Heuristic-based re-identification applies clustering analysis to the transaction graph to identify addresses that are likely controlled by the same entity as the initial exploit recipient, using the economic and behavioral linkage methods described in entity resolution analysis. Even after bridge-hopping and partial mixing, sophisticated on-chain forensics has successfully traced the majority of funds from several major DeFi exploits including identifying the destination wallets of Lazarus Group-attributed exploits through characteristic fund movement patterns that persist across obfuscation operations. Publishing preliminary forensic findings publicly on blockchain explorers and security research platforms creates accountability pressure on attackers and facilitates community monitoring of known suspect addresses, which has contributed to exchange-level blocking of identified exploit proceeds in several documented recovery cases.
Authorization flaws pose a serious threat to the stability of DeFi systems. Past incidents highlight how weaknesses like inadequate access controls, insufficient validations, and centralized mechanisms have been exploited, leading to significant vulnerabilities. Whether caused by coding errors or systemic failures, these flaws remain a persistent challenge for DeFi protocols.
Addressing these issues requires a multi-faceted approach. Effective strategies include thorough smart contract audits, decentralized governance models, and continuous monitoring systems. Protocols that adopt a layered defense strategy are better equipped to withstand breaches and mitigate risks.
Adding advanced analytics to this mix further bolsters security efforts. Tools like WalletFinder.ai provide real-time monitoring across Ethereum, Solana, and Base networks, offering insights into fund movements and token concentration. By delivering instant alerts on suspicious activities, such as unusual transaction patterns, these tools help establish a proactive defense framework.
As the DeFi ecosystem evolves, maintaining strong authorization security will remain a critical priority. Through rigorous development practices, advanced monitoring solutions, and an informed community, the path to building secure and resilient decentralized financial systems becomes clearer.
Authorization vulnerabilities in DeFi protocols often reveal themselves through specific warning signs. One common issue lies in flaws within smart contracts, such as weak access controls, which can open the door for unauthorized users to withdraw funds. Other vulnerabilities, like reentrancy attacks or problems with integer overflows and underflows, provide opportunities for hackers to exploit the system.
Another red flag is the absence of thorough smart contract audits. Without detailed reviews, protocols may lack adequate defenses against threats like flash loan attacks or oracle manipulation. These gaps in security can leave the protocol exposed, increasing the risk of authorization breaches.
DeFi enthusiasts can lower their risks tied to governance token concentration by spreading their investments across multiple tokens. By steering clear of heavy reliance on a single token, they can reduce vulnerability to potential manipulation or centralization challenges.
Staying up-to-date with governance proposals and engaging in community votes is another key step. Active participation not only empowers users to shape protocol decisions but also strengthens decentralization, helping to address risks that come with concentrated control.
WalletFinder.ai boosts DeFi security with cutting-edge tools designed for real-time wallet monitoring and performance tracking. By identifying unusual trading behaviors and flagging suspicious activities promptly, it enables users to act quickly to reduce potential risks.
With features like live alerts and in-depth wallet analytics, users can stay ahead of potential threats, manage authorization issues effectively, and strengthen the security of their DeFi interactions.
The most rigorous pre-deployment authorization security combines formal verification with complementary static analysis and mutation testing to cover the three distinct sources of authorization errors: implementation errors, specification errors, and composition effects. Formal verification using tools including Certora's Prover with CVL specifications or the K Framework against EVM bytecode mathematically proves that defined authorization invariants hold across all possible execution paths rather than testing a finite sample of cases. A CVL rule for treasury authorization might specify that any successful call to a withdrawal function must originate from a caller present in the governance-approved role mapping and must not exceed the per-period governance limit, after which the prover exhaustively searches for any execution path violating this specification.
Mutation testing evaluates test suite quality by systematically introducing plausible authorization errors such as inverted access control checks or weakened require conditions and measuring whether the test suite detects each mutation. High mutation detection rates confirm that the test suite would catch the same category of implementation mistakes that real coding errors introduce, while low detection rates indicate false confidence in authorization correctness. Runtime invariant monitoring through frameworks including OpenZeppelin Defender and the Forta detection bot network extends formal verification guarantees into production by continuously checking that proved authorization properties continue to hold as protocol state evolves, with circuit breaker mechanisms that automatically trigger pause functionality when violations are detected. Protocols deploying all three layers — formal pre-deployment verification, mutation-validated test suites, and runtime invariant monitoring with automated circuit breakers — have substantially stronger authorization security profiles than those relying on any single layer alone.
Pre-planned recovery architecture is the single largest determinant of the fraction of user funds recovered following an authorization exploit, with protocols that have pre-deployed pause mechanisms, white hat coordination policies, and treasury reserves for user compensation consistently achieving better recovery outcomes than those improvising responses in real time. Tiered pause architecture is the most operationally critical component: a Guardian role controlled by a protocol-defined multi-sig address that can trigger immediate protocol pause without governance vote allows exploit containment within the initial attacker activity window, while requiring governance vote to unpause prevents the pause mechanism from being abused for malicious protocol disablement. The asymmetric authorization requirement, fast defensive pause and slow governed resumption, is the design pattern adopted by Aave and Compound that balances responsiveness against abuse risk.
White hat coordination frameworks including pre-published responsible disclosure policies and bug bounty programs through platforms such as Immunefi create incentive structures that make returning funds more attractive than retaining them for attackers who have not successfully obfuscated transaction trails, a category that includes the majority of DeFi exploiters based on documented cases. Bounty amounts must be calibrated to exceed the realistic net proceeds from exploitation after accounting for on-chain forensic tracing and exchange-level blocking risks. Treasury reserve architecture through protocol-owned Safety Modules funded from ongoing fee revenue provides compensation capacity for affected users without requiring emergency governance token raises that dilute existing holders and signal protocol distress. On-chain forensic methodology tracing exploit proceeds through chain-hopping, mixer usage, and exchange deposits creates accountability pressure that has contributed to voluntary fund returns in documented major exploit cases, and publishing preliminary forensic findings publicly facilitates community monitoring of identified suspect addresses across all relevant chains.