Buy the Dip Crypto: Master Smart Entry Strategies
Buy the dip crypto - Master buy the dip crypto without getting burned. Learn step-by-step signals, optimal entry timing, risk management, & how to mirror smart

May 9, 2026
Wallet Finder

March 10, 2026
A DeFi wallet isn't just a place to store your crypto. Think of it as your personal digital vault and your all-access pass to the world of decentralized finance. It's a non-custodial wallet, which simply means you—and only you—have complete control over your private keys and digital assets. This setup lets you plug directly into financial apps without needing a bank or any other middleman.

The easiest way to wrap your head around a DeFi wallet is to compare it to something we all know: a traditional bank account. With a bank, you can access your money, but they ultimately hold the reins. The bank holds your funds, approves your transactions, and can even freeze your account if they see fit.
A DeFi wallet completely flips that model on its head.
It’s the difference between owning your house and renting an apartment. When you own the deed, you call the shots. No landlord can lock you out. A DeFi wallet works the same way. You hold the private keys, which are like the cryptographic "deed" to your digital assets.
This principle of self-custody is the absolute bedrock of decentralized finance. It means you are your own bank, with all the freedom—and responsibility—that comes with it. Nobody can access, freeze, or take your funds unless they have your private keys.
This direct ownership is what opens the door to a massive ecosystem of decentralized applications, or dApps. These are the tools built on the blockchain for lending, borrowing, trading, and earning interest, all without an intermediary taking a cut or telling you what you can and can't do.
To really get a handle on DeFi wallets, you have to pop the hood and see what's running the show. It all comes down to a powerful duo of cryptographic keys: a public key and a private key. If you can get your head around this one concept, you're already halfway there.
Think of your wallet’s public key as your bank account number. You can share it freely with anyone who needs to send you money. When someone wants to send you crypto, this is the address they use. It's totally safe to share and doesn't put your funds at risk.
Your private key, on the other hand, is the PIN to your bank card. It's a secret code that absolutely must stay private. This key is the only thing that can authorize sending crypto out of your wallet. If anyone else gets their hands on it, they have complete control of your money.
It's a common mistake to think your wallet "holds" your crypto. In reality, your funds always live on the blockchain. Your wallet is more like a high-tech keychain holding the secret keys that prove you own those funds and give you access to them.
This key system is what makes DeFi wallets the go-to interface for the entire ecosystem. They grant you direct, non-custodial access to protocols like Uniswap or Aave without needing a bank as a middleman. By late 2023, the total value locked (TVL) in DeFi protocols was hovering around $50 billion, which shows you just how big this user-controlled financial world has become. While this gives you incredible freedom, it also means you're 100% in charge of your own security. You can find more data on DeFi user growth over at Statista.
So, how do these keys team up to send crypto? The process is surprisingly straightforward but incredibly secure.
Let's say you want to send 1 ETH to a friend. Here's a quick look at what your wallet is doing in the background:
The beauty of it all is that this happens without your private key ever being revealed. It's like signing a check with a special, unforgeable signature that anyone can verify is yours without ever seeing you actually sign it.
But what if you lose your phone or your laptop dies? That's where the seed phrase (also called a secret recovery phrase) saves the day.
When you create a new DeFi wallet, it generates a unique list of 12 to 24 simple words. This is your seed phrase. This phrase is the master key that can be used to regenerate all of your private keys and restore your entire wallet on a new device.
You have to treat this phrase like gold. Seriously.
Think of it as the ultimate emergency backup. As long as you have that list of words, you can never truly lose access to your crypto, no matter what happens to your hardware. This is the very essence of self-custody.
When you first jump into crypto, one of the biggest choices you'll make is between a custodial and a non-custodial wallet. It sounds technical, but it really boils down to one simple question: who actually controls your funds?
Think of a custodial wallet like your bank account. A third party—usually a big crypto exchange—holds your assets for you. They manage the security, and you just log in. Super convenient, right?
A non-custodial DeFi wallet, on the other hand, is like having a vault in your own home. You, and only you, have the keys. This is the entire point of a DeFi wallet—to give you absolute, sovereign control over your own money.
Going the non-custodial route unlocks a world of benefits you just can't get with a custodial setup. For starters, your funds are completely censorship-resistant. No company or government can freeze your account or block a transaction. It also gives you a direct, frictionless passport to the entire universe of decentralized applications (dApps).
But with great power comes great responsibility. Being your own bank means security is 100% on you. If you lose your seed phrase—that secret string of words that acts as your master key—there's no "forgot password" link or customer support line to call. Your funds could be gone for good.
This is why understanding the relationship between your seed phrase and your keys is so crucial.
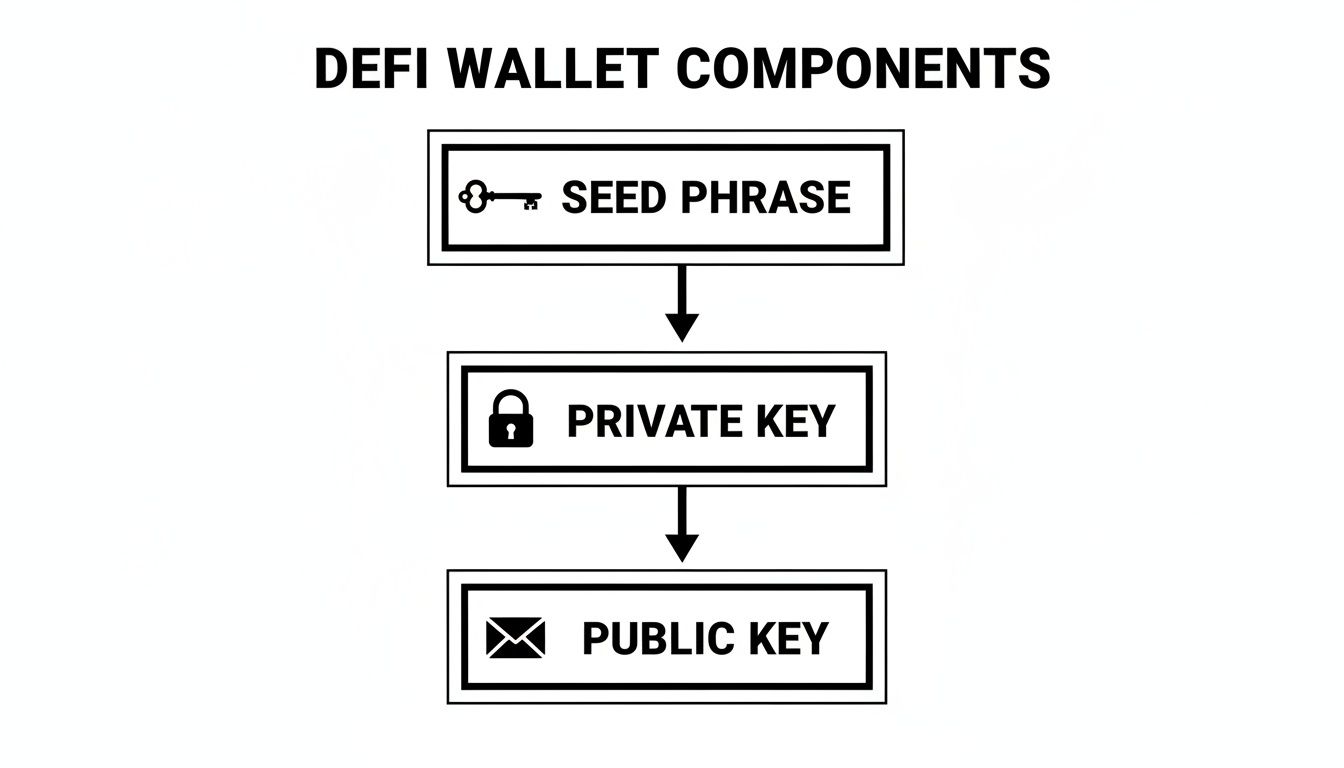
As the diagram shows, everything starts with that seed phrase. It's the ultimate backup, generating all the private and public keys you need to operate on the blockchain. Guard it with your life.
Custodial wallets, like the ones you get on major exchanges, offer a familiar, comfortable experience. They handle all the complex key management behind the scenes, making it feel just like a regular banking app. The trade-off? You’re trusting that exchange won’t get hacked, go bankrupt, or suddenly decide to restrict your access. The differences are massive, and we dive deeper in our guide on crypto exchange vs wallet.
The core ethos of DeFi is captured in a simple phrase: Not your keys, not your crypto. A non-custodial wallet is the only way to truly own your digital assets, shielding them from third-party risks and control.
To make the choice crystal clear, let's break down the main differences side-by-side.
The choice between a custodial and a non-custodial wallet comes down to five fundamental trade-offs, and understanding each one clearly is more useful than any feature list.
Private key control is the most foundational difference. With a custodial wallet, a third party holds and manages your keys on your behalf, meaning the assets in your account are technically theirs to custody. A non-custodial wallet puts you in full control and full responsibility for those keys, with no intermediary in the chain of ownership.
The security model follows directly from that distinction. Custodial wallets ask you to trust the exchange's security infrastructure, their servers, their access controls, and their organizational integrity. Non-custodial wallets transfer that responsibility entirely to you, which is either reassuring or daunting depending on how confident you are in your own security practices.
dApp access is where the practical consequences of that custody difference become most visible. A custodial wallet offers limited or nonexistent access to decentralized applications because your funds are held inside a platform's proprietary system rather than on-chain under your direct control. A non-custodial wallet connects directly and seamlessly to the full ecosystem of DeFi protocols, because your wallet address is a first-class participant on the blockchain itself.
Censorship risk cuts to the heart of why self-custody matters to many DeFi participants. A custodial account can be frozen, restricted, or closed by the exchange for any reason, including regulatory pressure, internal policy, or simple business decisions. A non-custodial wallet has no such exposure: no company controls access to your funds, and no third party can block a transaction you initiate with your own keys.
Recovery works differently in each model in a way that reflects the broader trade-off between convenience and sovereignty. Custodial wallets offer familiar account recovery through customer support and password resets, the same experience you would expect from any online platform. Non-custodial wallets have no such fallback: your secret recovery phrase is the sole mechanism for restoring access, which means losing it means losing your funds permanently. That finality is the price of genuine ownership.
Ultimately, while custodial wallets are a great, easy starting point, a non-custodial DeFi wallet is the true standard for anyone serious about DeFi. It’s the tool that unlocks genuine financial freedom and lets you engage directly with the future of finance, on your own terms.
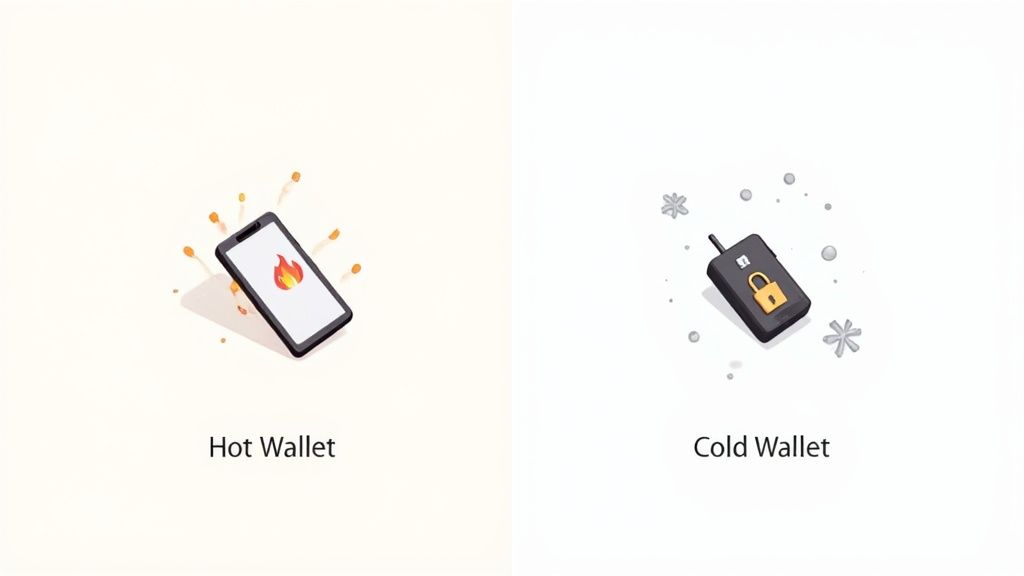
Alright, you've grasped the core idea of a non-custodial wallet—you're the boss. The next choice you'll face is about where that wallet "lives." Not all wallets are built the same, and they generally fall into two camps based on their internet connection: hot wallets and cold wallets.
Think of a hot wallet like your physical wallet. It's the one you carry around every day for quick, easy access. It's a software app on your phone or a browser extension that's always online, making it perfect for frequent, small transactions and daily interactions with DeFi apps (dApps).
A cold wallet, on the other hand, is your personal Fort Knox. It’s a physical hardware device that keeps your private keys completely offline. To sign any transaction, you have to physically approve it on the device itself, creating an "air gap" that shields you from online threats like hackers and phishing scams.
Hot wallets are the real workhorses of DeFi. They're designed for people who are actively swapping tokens, providing liquidity, or jumping into the latest protocols.
Their main selling point is pure convenience. You can approve transactions with a simple click, which makes for a super smooth experience. Some of the most popular ones you'll run into are:
Here's the catch: because they're always online, hot wallets are more exposed to cyberattacks. They're fantastic for managing the crypto you plan to actively use, but you wouldn't want to store your life savings in one.
When it comes to securing large sums of crypto for the long haul, a cold wallet is an absolute must. These hardware devices are engineered for one purpose and one purpose only: to keep your private keys completely isolated from the internet.
Industry leaders like Ledger and Trezor dominate this space. Even when you plug one into your computer to send crypto, your private key never leaves the secure chip inside the device. The transaction is signed offline, right there on your little gadget.
This process makes them virtually immune to remote hacks. The trade-off, of course, is convenience. They're a bit slower to use and require you to have the physical device on hand for every single transaction.
For most people, the smartest move is a hybrid approach. Use a hot wallet for your "spending cash"—the funds you're actively trading or using in DeFi. Meanwhile, keep the lion's share of your holdings tucked away safely in a cold wallet, moving funds between the two only when necessary. It's the perfect balance of everyday convenience and long-term peace of mind.
In DeFi, the saying "be your own bank" isn't just a cool slogan—it's your new job description. You are the one and only guardian of your assets. Security isn't just another feature; it's everything.
But don't let that scare you. Mastering a few fundamental security habits can turn that responsibility into a source of confidence, not anxiety.
The first, most sacred rule of crypto is to protect your seed phrase. Think of it as the master key to your entire financial world, a key that must be stored completely offline where no hacker can ever reach it.
Getting this one practice right is the single most powerful defense you have. Losing your seed phrase is like losing the deed to your house and the keys to your vault at the same time. It's game over.
Beyond guarding your seed phrase, your daily interactions with dApps demand constant vigilance. Scammers are relentlessly creative, building pixel-perfect fake websites to trick you into connecting your wallet and signing away your funds.
Always triple-check the URL before connecting your wallet to any site. A great habit is to bookmark your most-used dApps to avoid accidentally clicking a malicious link from a Google search or social media.
Another sneaky threat is smart contract approvals. Every time you use a dApp, you grant it permission to access specific tokens in your wallet. These permissions can stick around forever, creating a potential backdoor if that protocol ever gets hacked.
This is a massive issue. Losses from DeFi exploits and fraud run into the billions, and it's not slowing down. Research shows that only about 10.8% of users regularly check and revoke these old approvals, leaving a huge attack surface wide open.
Building a strong security routine isn't optional. It takes a proactive mindset and consistent habits to keep what's yours, yours.
By taking these steps, you build layers of defense around your digital wealth. For a much deeper dive into the specific tactics scammers use, be sure to read our guide to avoiding DeFi wallet scams.
Think of your DeFi wallet as more than just a digital safe for your crypto. It's your passport to an entirely new financial system—your key to actually using your assets instead of just holding them.
Owning your keys is the first critical step, but the real magic happens when you connect that wallet to decentralized applications (dApps) and put your crypto to work. This is where the theoretical potential of DeFi becomes a practical reality.
Suddenly, you can perform actions that were once reserved for big banks and financial institutions, all without asking for permission. This direct participation is what makes the space so exciting.
Your DeFi wallet is essentially your universal login for the decentralized web. Once you're in, a whole world of possibilities opens up.
Here are a few of the most common things people are doing right now:
And people are jumping in fast. The number of active DeFi users has already swelled to around 14.2 million unique wallets. On a good week, transaction volumes can blast past $48 billion. This isn't a niche hobby anymore; it's a bustling on-chain economy, and your wallet is your ticket in. You can dig into more DeFi market statistics from CoinLaw.io.
Once you get comfortable with the basics, you'll find the ecosystem is packed with more sophisticated opportunities. You can use your tokens to vote on a protocol's future, participating in decentralized governance, or you can dive into the world of NFTs by collecting digital art and other unique assets.
A DeFi wallet transforms you from a passive holder into an active participant. It’s the difference between storing gold in a vault and using it as capital to generate further returns.
The space is also getting smarter. Innovative platforms are popping up that use on-chain data to give you a serious edge. Tools like Wallet Finder.ai let you connect your wallet (in a secure, read-only mode) to see what the most successful traders are doing. By analyzing their moves, you can spot trends early, discover promising new tokens, and even copy their trades, turning the public blockchain into your own source of alpha.
The market for non-custodial wallets has grown to the point where new users face a genuine selection problem. There are dozens of options across different blockchains and form factors, and the differences between them matter more than most beginner guides acknowledge. Choosing the wrong wallet for your situation does not necessarily mean losing funds, but it does mean friction, limited access to the protocols you want to use, and in some cases a migration process that exposes you to unnecessary risk when you eventually switch.
A structured evaluation process eliminates most of that friction before it happens. The questions below narrow the field quickly and point you toward the wallet type and specific product that fits your actual use case rather than the one with the most aggressive marketing presence.
The single most important input into wallet selection is a clear answer to one question: what are you primarily going to use this wallet for? This question sounds obvious but most beginners skip it entirely, defaulting instead to whichever wallet they encountered first in a tutorial or a community recommendation.
If your primary goal is actively trading tokens on decentralized exchanges, your priority is a hot wallet with seamless browser extension integration and support for the specific chains where the DEXs you plan to use are deployed. MetaMask remains the dominant choice for Ethereum Virtual Machine (EVM) compatible chains, including Ethereum mainnet, Arbitrum, Optimism, Base, and Polygon, because its browser extension integrates natively with virtually every major DEX and DeFi protocol in those ecosystems. If your trading activity centers on Solana, Phantom is the equivalent standard with the same native dApp integration advantage.
If your primary goal is long-term holding of significant value, the correct starting point is a hardware wallet rather than any software option. The convenience trade-off of a hardware wallet, meaning you need the physical device present to sign transactions, is a minor inconvenience that is completely justified the moment your holdings reach a level where their loss would materially affect you. Ledger and Trezor are the two established hardware wallet manufacturers with the longest operational track records and the most extensive third-party security audits.
If your primary goal is exploring new protocols and ecosystems, you likely need a multi-chain wallet that can operate across different blockchain architectures without requiring you to maintain separate wallet instances for each chain. Rabby Wallet has gained significant adoption among active DeFi participants for this reason, offering cross-chain portfolio visibility and transaction simulation that shows you what a smart contract interaction will actually do to your wallet before you confirm it.
Once you have identified your use case, the next evaluation criterion is whether the wallet you are considering supports the specific chains and protocols you intend to use. This sounds trivial but produces a surprisingly common frustration: a new user downloads a popular wallet, attempts to interact with a protocol they read about, and discovers the wallet either does not support that chain or requires a manual network configuration process that is not obviously documented.
Chain support divides wallets into two broad categories. EVM wallets support all chains built on Ethereum's architecture, which covers the large majority of DeFi activity by total value. Non-EVM wallets support chains like Solana, Aptos, Sui, and NEAR, which use different cryptographic standards and transaction formats that EVM wallets cannot accommodate. Some wallets, including Trust Wallet and Exodus, support both EVM and non-EVM chains within a single interface, which adds convenience for users who want exposure to multiple ecosystems.
Protocol compatibility is a more granular consideration than chain support. Even within a supported chain, some wallets implement features or limitations that affect your ability to interact with specific protocols. WalletConnect integration, which allows mobile wallets to connect to desktop browser dApps by scanning a QR code, is a feature that dramatically expands protocol accessibility for mobile-first users. Before committing to any wallet, verify that it supports WalletConnect if you intend to use a mobile wallet for desktop protocol access, and verify that the specific protocols you plan to use have documented compatibility with your chosen wallet.
Security track record is the most important criterion that most wallet selection guides underweight. The user interface, the supported token list, and the fee structure are all secondary to the fundamental question of whether the wallet software has a documented history of protecting user funds under adversarial conditions.
A wallet's security track record has two components worth researching before you commit. The first is audit history: has the wallet's code been reviewed by independent security firms, and are those audit reports publicly available? Legitimate wallet providers publish their audit reports from firms like Trail of Bits, Cure53, or Least Authority. The absence of published audits does not guarantee the software is insecure, but it removes the most important independent verification mechanism available to you as a non-technical user.
The second component is incident history: has the wallet been involved in security incidents, and if so, how did the team respond? A wallet that experienced a minor vulnerability, disclosed it promptly, patched it quickly, and reimbursed affected users has demonstrated a security culture that is more reassuring than a wallet with no public incident history simply because it has not yet been tested at scale. The DeFi ecosystem's history is long enough now that most major wallets have some incident history, and the quality of the response tells you more about the team's priorities than the incident itself.
Most DeFi wallet guides stop at setup and basic security hygiene. That is appropriate for absolute beginners, but it leaves active DeFi participants without the operational practices that separate well-managed wallets from poorly managed ones. The gap between knowing how to use a wallet and knowing how to manage one as a component of a sophisticated on-chain strategy is substantial, and closing it produces a meaningfully better security posture and a cleaner analytical picture of your own activity.
This section covers the wallet management practices that experienced DeFi participants use but rarely document explicitly, because they have become habitual rather than instructional.
The single-wallet approach that most beginners start with is a liability that compounds as your DeFi activity grows. Every protocol you interact with receives a token approval that persists indefinitely. Every transaction you make leaves a permanent on-chain record that connects your entire activity history under one address. Every new protocol you test exposes your full holdings to whatever smart contract risk that protocol carries.
A multi-wallet architecture addresses all three of these problems simultaneously by separating your capital and activity across wallets designed for distinct purposes. The structure that most experienced participants converge on involves three tiers of wallet with clearly defined roles.
The first tier is your primary cold storage wallet, a hardware wallet that holds the majority of your capital and interacts with only a small number of thoroughly audited, long-established protocols. This wallet is connected to dApps rarely and deliberately. Its transaction history is sparse by design, and it carries approvals from only the protocols where your long-term capital is deployed.
The second tier is your active trading wallet, a hot wallet that connects to DEXs, liquidity protocols, and other regularly used applications. This wallet holds a working balance sufficient for your current DeFi activity but does not carry your long-term holdings. When you need more capital in this wallet, you transfer it from cold storage. When profits accumulate, you transfer them out. The separation means that a compromised approval or a malicious contract interaction in your active wallet cannot access the capital in your cold storage wallet.
The third tier is a dedicated experimentation wallet that holds a small amount of funds specifically budgeted for testing new protocols, participating in new token launches, and interacting with unaudited contracts that carry elevated smart contract risk. By containing this activity in an isolated address with a defined maximum exposure, you preserve the cleanliness of your primary wallets and limit the blast radius of any interaction that turns out to be malicious.
One of the most significant capability advances in non-custodial wallet software over the past two years is the widespread adoption of transaction simulation, which shows you the predicted outcome of a smart contract interaction before you sign and broadcast it. Wallets including Rabby, recent versions of MetaMask, and several mobile alternatives now display a plain-language summary of what will happen to your wallet if you confirm a transaction: which tokens will leave, which tokens or positions you will receive, and what approvals you will be granting.
Transaction simulation does not eliminate smart contract risk. A simulation is only as reliable as the code doing the simulating, and sophisticated exploits can produce transactions that simulate differently from how they execute. But simulation eliminates a large class of common mistakes and scams, particularly the drainer contracts that are designed to look like routine protocol interactions in your wallet's transaction queue while actually executing unlimited approval grants to attacker-controlled addresses.
The habit to build is treating every transaction simulation as mandatory reading before you click confirm, regardless of how familiar the protocol appears. Phishing sites that impersonate legitimate protocols produce transaction simulations that look different from what the legitimate protocol would generate, because they are requesting different permissions. A legitimate DEX swap should show you the token being spent and the token being received. A transaction that simulates as granting unlimited token access to an unknown address while claiming to be a swap is a drainer contract, and reading the simulation prevents you from signing it.
Your wallet address is a permanent, public record of every financial decision you have made since the address was created. Most DeFi participants check their wallet balance and recent transactions regularly but do not maintain a systematic view of their wallet's broader on-chain footprint, including outstanding token approvals, protocol positions across multiple chains, and the full history of addresses that have interacted with theirs.
Maintaining awareness of this footprint serves two practical purposes. The first is security: outstanding token approvals from protocols you no longer use are persistent attack vectors. If a protocol you approved six months ago is exploited, the attacker can use the approval you granted to access the specific token you approved even if you have not interacted with that protocol since. A monthly approval audit using a tool like Revoke.cash, which the existing article correctly recommends, removes this attack surface systematically.
The second purpose is analytical: your own wallet's on-chain history is a detailed record of your DeFi activity that can inform your research and strategy refinement in the same way that any performance record does. Tools like Zerion and DeBank aggregate your positions, transaction history, and realized performance across all chains into a single dashboard, giving you a portfolio-level view of your on-chain activity that individual protocol interfaces and block explorers cannot provide.
This same transparency that makes your wallet's history visible to you also makes it visible to anyone else with your address. Wallet Finder uses this transparency in the other direction: by tracking the on-chain history of high-performing wallets, it surfaces the patterns and positions of the most successful DeFi participants so you can incorporate their activity into your own research process. Understanding how your own wallet's footprint looks to an outside observer also deepens your intuition for what to look for when you are analyzing other wallets for signals.
Jumping into DeFi wallets always brings up a few key questions. It's totally normal. Getting straight answers is the best way to build the confidence you need to manage your assets securely. Let's tackle some of the most common ones.
Absolutely, and you probably should. In fact, most seasoned crypto users run multiple wallets for different purposes. It’s a smart security strategy called wallet segmentation, and it’s all about separating your risk.
Think of it like this:
This way, if one of your more active wallets ever gets compromised, the damage is contained. Your most important assets stay completely secure.
Don't panic! Your funds are perfectly safe as long as you have your secret recovery phrase (sometimes called a seed phrase). This is a critical concept to understand: your crypto doesn't actually live on your phone or laptop. It lives on the blockchain. Your device just holds the private keys that prove you own it.
If your device is lost, stolen, or just stops working, you simply install your wallet on a new device. Then, you'll use your 12 or 24-word seed phrase to restore full access to all your funds. This is why that phrase is everything. Guard it with your life—it’s the one master key to your entire crypto portfolio.
Not exactly. DeFi transactions are pseudonymous, which is a fancy way of saying they aren't directly tied to your real name, but they are completely public. Every single transaction is etched into the blockchain's public ledger for anyone to see forever.
Your wallet address is your pseudonym. But if that address is ever linked to your real identity—maybe you sent funds to it from an exchange where you did a KYC (Know Your Customer) verification—then your entire transaction history can be traced back to you. The public nature of the blockchain is great for transparency, but it's not truly anonymous.
Moving funds between a hot wallet and a cold wallet is one of the most common operational tasks for active DeFi participants who use a tiered wallet architecture, and doing it safely requires attention to a few details that are easy to overlook when the process starts to feel routine.
The most important practice when transferring funds to a cold wallet for the first time is to verify the destination address through the hardware wallet's own display rather than relying solely on what you see on your computer screen. Clipboard hijacking malware exists specifically to replace a copied wallet address with an attacker's address the moment it is pasted into a transaction field. Your hardware wallet's screen shows you the address it is about to receive funds at independently of your computer's display, and confirming that both screens show the same address eliminates the clipboard substitution attack entirely.
A second practice that eliminates a large class of costly errors is to perform a small test transfer before sending any significant amount. Send a minimal amount, confirm it arrives at the correct address by checking the destination on a block explorer, and only then send the full amount. The gas cost of the test transaction is trivial insurance against the irreversible loss that comes from sending a large transfer to a mistyped or substituted address. This habit is especially important when sending to a new address for the first time, including your own hardware wallet address if you have not received funds there before.
When moving funds from cold storage back to a hot wallet for active use, apply the same address verification discipline in reverse. Connect your hardware wallet, verify the destination address on the hardware wallet's screen before confirming, and limit the transfer to the amount you actually need for your planned activity rather than moving more capital into a hot wallet environment than the situation requires.
Speed and decisive action are the most important variables in limiting damage when you suspect a wallet compromise. The blockchain is irreversible, which means every second that passes after a compromise is an opportunity for an attacker to drain assets that cannot be recovered. The response protocol below applies whether you have clicked a phishing link, signed a suspicious transaction, or simply noticed unexpected activity in your wallet history.
The first action is to stop all interaction with the suspected wallet immediately and do not attempt to investigate from the same device or browser session where the compromise may have occurred. If your device may be infected with malware, using it to take protective action can make things worse by exposing additional addresses or seed phrases you access during the response process.
The second action, executed from a clean device, is to identify which assets remain in the compromised wallet and whether any unlimited token approvals have been granted to unknown addresses. A tool like Revoke.cash allows you to see and revoke outstanding approvals. If the attacker has not yet moved your assets, revoking their approval before they execute a drain may preserve your funds, though this is a race condition that does not always go in your favor.
The third action is to migrate any remaining funds to a completely new wallet address, not to a different account within the same seed phrase. If your seed phrase has been exposed, every address derived from it is compromised, because an attacker with your seed phrase can generate the same address sequence you use. A genuine compromise of your seed phrase requires generating an entirely new seed phrase on a clean device and treating the old seed phrase as permanently compromised. Notify any counterparties who may have your old address on record, and do not reuse it for any purpose.
Yes, and this is a normal part of active DeFi participation. Connecting your wallet to a protocol does not create an ongoing privileged relationship between that protocol and your wallet in most cases. What it does create is a browser or mobile session that allows the protocol's interface to read your wallet's public address for display purposes and to propose transactions for your signature.
The important distinction is between a read connection and a token approval. When you connect your wallet to a DEX interface, you are granting that interface permission to read your public address and propose transactions. You are not granting it permission to move your funds. Your funds only move when you explicitly sign and confirm a specific transaction. The connection itself carries no financial risk.
Token approvals are the mechanism that does carry ongoing risk. When a DEX or lending protocol asks you to approve a token before you can trade or deposit it, you are signing a transaction that grants that protocol's smart contract permission to move a specified amount of that token from your wallet. This approval persists on-chain until you explicitly revoke it, regardless of whether you ever use that protocol again. Most protocols request unlimited approval by default because it eliminates the need for repeat approval transactions as your usage continues, but unlimited approval means the approved contract can move your entire balance of that token whenever it chooses, not just during the specific transaction you initiated.
The practical implication is that maintaining connections to multiple protocols simultaneously is operationally normal and carries no direct risk, while managing your outstanding token approvals proactively is a genuine security responsibility. Limiting approval amounts to the specific transaction value rather than accepting unlimited approvals, where the protocol's interface allows it, significantly reduces your exposure to approval-based exploits across your entire connected protocol history.
Ready to turn on-chain data into your competitive advantage? Wallet Finder.ai helps you discover the strategies of top-performing traders, track their moves in real time, and replicate their success. Start your 7-day trial and see what the smart money is doing at https://www.walletfinder.ai.