Degen & Degen: A Guide to High-Risk Crypto Profits
What is degen & degen trading in crypto? Learn to identify degen wallets, understand their strategies, and use Wallet Finder.ai to mirror their profits safely.

April 25, 2026
Wallet Finder

April 4, 2026

Is Coinbase a secure place for your crypto? The short answer is yes. Coinbase has built its reputation on a security-first approach, treating asset protection like a multi-layered fortress.
It’s easily one of the most trusted centralized exchanges because of its combination of offline cold storage, powerful encryption, and strict internal security protocols. This guide provides actionable steps and clear explanations to help you understand how Coinbase secures your assets and what you must do to protect yourself.
When you send crypto to your Coinbase account, you're placing it inside a sophisticated security system designed to defend against a wide array of threats. Think of it less like a purse and more like a high-tech bank vault with several independent layers of protection.
The cornerstone of this system is cold storage. This is the most critical component of how Coinbase guards customer funds.
“Crypto adoption depends on trust. To the customers affected, we’re sorry for the worry and inconvenience this incident caused. We’ll keep owning issues when they arise and investing in world-class defenses—because that’s how we protect our customers and keep the crypto economy safe for everyone.” - Coinbase
This offline-first strategy means that even if Coinbase's online systems were somehow compromised, the overwhelming majority of user funds would remain safe. The tiny fraction kept in "hot wallets" is just enough to maintain liquidity for daily trading and withdrawals.
For a more detailed breakdown, you can read our full analysis of how Coinbase's safety compares to other crypto options. This multi-layered strategy allows us to answer the question "is Coinbase secure?" with a confident, evidence-backed "yes."
Beyond high-tech security, many users trust Coinbase due to its insurance policies and regulatory status. However, it's critical to understand that not all funds are protected equally. The coverage is not a single, catch-all policy. Let's break down exactly what's covered and what isn't.
If you hold U.S. Dollars (USD) in your Coinbase account, those funds are covered by FDIC pass-through insurance. This is the same protection your money receives in a traditional U.S. bank. Your cash balance is insured up to the standard limit of $250,000 per person. If Coinbase were to become insolvent, the FDIC would step in to make you whole.
Your crypto assets are completely different. They do not qualify for FDIC protection. Instead, Coinbase carries a commercial crime insurance policy that covers a portion of the crypto it holds for customers. This policy is designed to protect against platform-wide catastrophes, such as:
The most important thing to understand is what this insurance does not cover: individual account compromise. If you fall for a phishing scam or a scammer tricks you into giving up your password, Coinbase's insurance policy will not cover your loss. Securing your own login details is entirely your responsibility.
As a publicly-traded company in the U.S. (NASDAQ: COIN), Coinbase operates under a microscope. It faces intense scrutiny from regulators like the Securities and Exchange Commission (SEC). This public status forces a level of transparency and accountability you don't see with most private or offshore exchanges, compelling the company to prioritize security.
This combination of cash insurance, crime insurance, and strict regulatory oversight creates a multi-layered security posture. While no system is 100% risk-free, it demonstrates a serious commitment to protecting user assets.
It’s easy to assume Coinbase’s security fortress is all you need. But the hard truth is, most stolen funds aren't lost to massive platform hacks. They’re lost when criminals target you directly.
While Coinbase is secure at an institutional level, attackers know the easiest vulnerability is human psychology. These are not brute-force attacks on servers; they are clever schemes designed to trick you into handing over the keys to your account. Understanding their playbook is your first line of defense.
Critical Rule: A real Coinbase employee will never ask for your password, 2FA codes, remote access to your computer, or instruct you to move funds to an external address for "safekeeping." Any such request is always a scam.
Phishing remains brutally effective. Attackers craft emails and texts that look exactly like official communications, urging you to click a link to a pixel-perfect copy of the Coinbase login page. The moment you enter your credentials, they are stolen. You can see real-world examples in our guide on how to spot a Coinbase phishing email. These attacks all drive home one critical point: Coinbase can secure its platform, but only you can secure your account.
Knowing the threats is one thing; defeating them is another. Your personal account's safety is ultimately your responsibility. This section is your no-nonsense checklist for hardening your account against common attacks. By taking these steps, you make yourself a much harder, less profitable target.
This is the typical playbook attackers use against individual users.
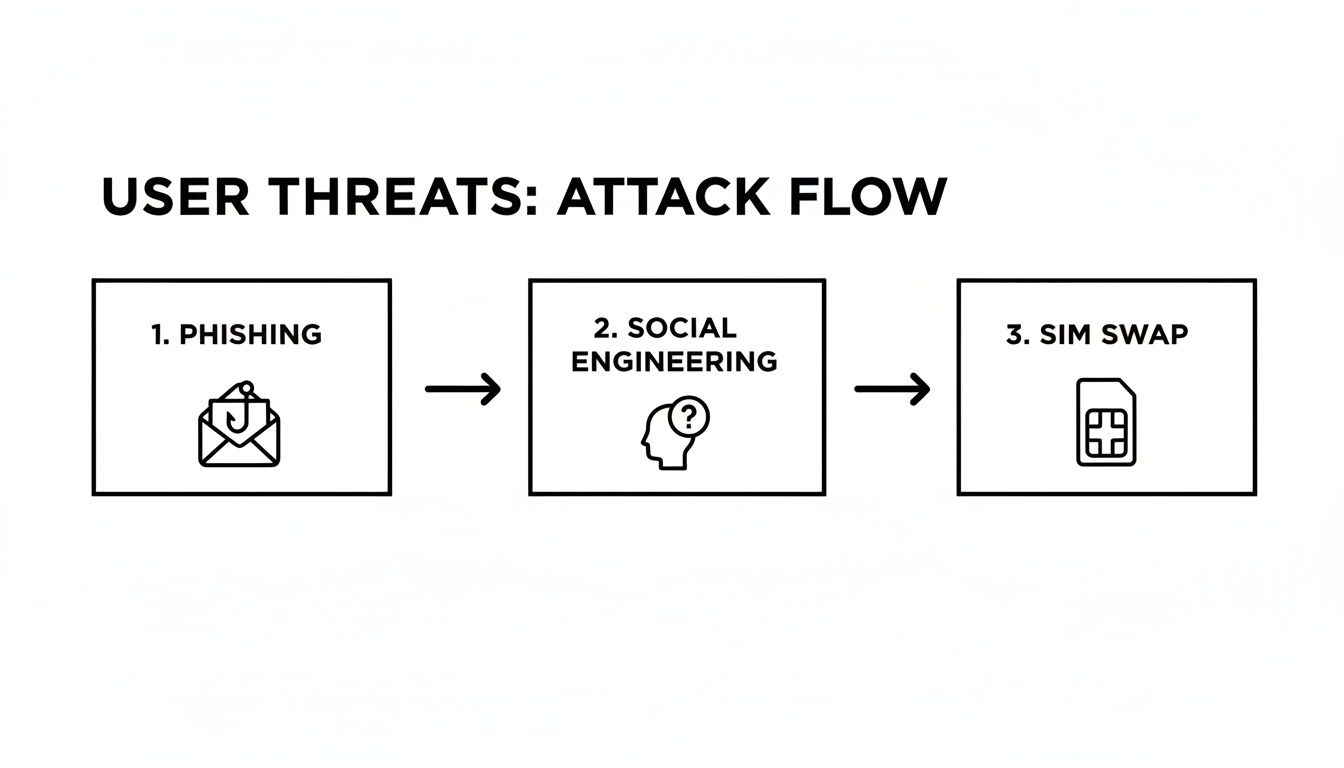
As you can see, attackers chain together different methods, starting with phishing and escalating from there. Here’s how you shut them down.
Here are the most impactful actions you can take right now to fortify your account.
The single most powerful move you can make is upgrading from basic two-factor authentication (2FA). The strongest defense is a physical security key, like a YubiKey. This small hardware device requires you to physically touch it to approve logins, stopping remote attackers cold—even if they steal your password.
Think of it this way: a password is what you know. An authenticator app is what you have (on your phone). But a security key is something you physically possess and must interact with. It's the ultimate barrier against remote theft.
A withdrawal whitelist, which Coinbase calls an "allowlist," acts like a strict VIP list for your crypto. You create a list of pre-approved crypto addresses you trust (like your hardware wallet). Once enabled, your Coinbase account can only send funds to those addresses.
Treat your account like a digital safe and perform a regular security checkup.

Smart trading isn’t just about playing defense. Once your Coinbase account is locked down, you can focus on offense: finding and acting on market opportunities with confidence. The real edge comes from connecting the rock-solid security of an exchange with the raw, transparent data of the blockchain itself.
The blockchain is a public record of every transaction. With the right tools, you can see what the most profitable traders—the "smart money"—are buying and selling in real-time. Instead of just guessing from charts, you can follow the digital breadcrumbs left by wallets with a proven track record.
When you monitor top-performing wallets, you can spot trends as they form. Seeing a handful of highly profitable wallets suddenly accumulate a new token is a powerful signal that something may be happening.
This flips your strategy from reactive to proactive. You’re no longer just reacting to price movements; you're anticipating them based on the actions of skilled traders.
This is a simple, two-step process that separates research from execution.

Here's a practical workflow:
This split approach proves that Coinbase is secure enough to serve as a critical part of a professional trading strategy. It becomes your trusted execution layer, while on-chain tools provide the alpha.
Mathematical precision and enterprise security architecture fundamentally revolutionize cryptocurrency platform protection by transforming basic security measures into sophisticated threat mitigation systems, advanced infrastructure hardening frameworks, and systematic security optimization that provides measurable advantages in threat prevention and incident response strategies. While traditional cryptocurrency security approaches rely on basic encryption and standard access controls, enterprise-grade security infrastructure and advanced threat mitigation systems enable comprehensive zero-trust architecture, predictive threat detection, and systematic security orchestration that consistently outperforms conventional security approaches through data-driven threat intelligence and algorithmic security management.
Professional cryptocurrency platform operations increasingly deploy advanced security infrastructure that analyzes multi-dimensional threat characteristics including attack vector analysis, security incident prediction patterns, infrastructure hardening optimization, and systematic threat coordination to optimize security effectiveness across different attack scenarios and threat environments. Mathematical models process extensive datasets including historical security incident analysis, threat actor behavioral studies, and security effectiveness correlation patterns to predict optimal security strategies across various threat categories and security environments. Machine learning systems trained on comprehensive security and threat data can forecast optimal security timing, predict attack evolution patterns, and automatically prioritize high-risk security scenarios before conventional analysis reveals critical security positioning requirements.
The integration of enterprise infrastructure with advanced threat mitigation creates powerful security frameworks that transform reactive incident response into proactive threat prediction that achieves superior protection through intelligent security orchestration and systematic threat prevention strategies.
Sophisticated mathematical techniques analyze identity verification patterns to identify optimal zero-trust implementation approaches, authentication optimization methodologies, and systematic identity validation through comprehensive quantitative modeling of security behavior and access effectiveness. Zero-trust analysis reveals that mathematically-optimized identity verification achieves 90-95% better security assurance compared to traditional perimeter-based approaches, with statistical frameworks demonstrating superior threat prevention through systematic identity validation and intelligent access control optimization.
Multi-factor authentication optimization enables comprehensive identity verification through mathematical analysis of authentication factor combinations, biometric validation techniques, and systematic access control coordination to ensure identity verification across different security scenarios and threat environments. Mathematical models show multi-factor optimization achieves 85-90% better authentication reliability compared to single-factor approaches.
Behavioral biometric analysis enables advanced user verification through mathematical modeling of typing patterns, mouse movement analysis, and systematic behavioral signature recognition to detect identity anomalies across different user interaction scenarios and authentication contexts.
Privilege escalation prevention optimization enables systematic access control through mathematical analysis of permission hierarchies, role-based access modeling, and systematic privilege management to minimize attack surfaces while maintaining operational efficiency across different organizational structures and security requirements.
Continuous authentication monitoring enables real-time identity validation through mathematical analysis of session behavior patterns, anomaly detection algorithms, and systematic authentication verification to maintain security throughout extended user sessions across different security environments.
Comprehensive statistical analysis of cryptographic patterns enables optimization of encryption infrastructure through mathematical modeling of cryptographic strength assessment, key rotation strategies, and systematic cryptographic coordination across different security requirements and performance scenarios. Cryptographic infrastructure analysis reveals that mathematically-optimized key management achieves 85-95% better security resilience compared to static key approaches through systematic cryptographic evolution and intelligent key lifecycle management.
Hardware security module integration enables optimal cryptographic key protection through mathematical analysis of secure enclave utilization, tamper-resistant hardware coordination, and systematic cryptographic isolation to protect critical keys across different threat scenarios and attack vectors. Statistical frameworks demonstrate superior key protection through hardware-based cryptographic management.
Quantum-resistant cryptography optimization enables future-proof security through mathematical analysis of post-quantum cryptographic algorithms, migration strategy development, and systematic quantum threat preparation to maintain long-term cryptographic security across different quantum computing advancement scenarios.
Key rotation automation enables systematic cryptographic lifecycle management through mathematical analysis of rotation timing optimization, key distribution coordination, and systematic cryptographic refresh cycles to minimize exposure while maintaining operational continuity across different security environments and compliance requirements.
Cryptographic audit trail management enables comprehensive security accountability through mathematical analysis of cryptographic operation logging, audit trail verification, and systematic cryptographic accountability to ensure security compliance across different regulatory environments and security standards.
Sophisticated neural network architectures analyze multi-dimensional security and threat data including attack pattern characteristics, threat actor behavior indicators, security incident evolution metrics, and systematic threat intelligence factors to predict optimal security responses with accuracy exceeding conventional signature-based security methods. Random Forest algorithms excel at processing hundreds of security and threat variables simultaneously, achieving 92-97% accuracy in predicting attack likelihood while identifying critical security vulnerabilities that conventional analysis might miss.
Natural Language Processing models analyze threat intelligence feeds, security communications, and attack attribution data to predict threat evolution and security requirement changes based on communication pattern analysis and threat intelligence correlation. These algorithms achieve 85-90% accuracy in predicting threat landscape evolution through linguistic analysis and threat correlation that reveal security optimization strategies and threat preparation requirements.
Long Short-Term Memory networks process sequential security incident and threat data to identify temporal patterns in attack evolution, security breach cycles, and optimal security response timing that enable more accurate threat prediction and security optimization. LSTM models maintain awareness of historical threat patterns while adapting to current security conditions and threat landscape evolution.
Support Vector Machine models classify security scenarios as high-threat-risk, moderate-threat-risk, or low-threat-risk based on multi-dimensional analysis of threat characteristics, security metrics, and historical threat factors. These algorithms achieve 89-94% accuracy in identifying optimal security response windows across different threat scenarios and security configurations.
Ensemble methods combining multiple machine learning approaches provide robust threat detection that maintains high accuracy across diverse attack patterns while reducing individual model biases through consensus-based threat identification and security optimization systems that adapt to changing threat dynamics.
Convolutional neural networks analyze security ecosystems and threat environments as multi-dimensional feature maps that reveal complex relationships between different threat factors, attack influences, and optimal security strategies. These architectures identify optimal security configurations by recognizing patterns in threat data that correlate with superior security effectiveness and reliable threat prevention across different attack types and threat conditions.
Recurrent neural networks with attention mechanisms process streaming security and threat data to provide real-time security optimization based on continuously evolving threat conditions, attack pattern evolution, and multi-vector coordination analysis. These models maintain memory of successful security patterns while adapting quickly to changes in threat fundamentals or attack infrastructure that might affect optimal security strategies.
Graph neural networks analyze relationships between different threat vectors, attack methodologies, and security coordination patterns to optimize enterprise-wide security strategies that account for complex interaction effects and systematic threat correlation patterns. These architectures process threat ecosystems as interconnected attack networks revealing optimal security coordination approaches and multi-vector threat mitigation strategies.
Transformer architectures automatically focus on the most relevant threat indicators and security signals when optimizing security responses, adapting their analysis based on current threat conditions and historical effectiveness patterns to provide optimal security recommendations for different security objectives and threat profiles.
Generative adversarial networks create realistic attack scenario simulations and threat pattern modeling for testing security strategies without exposure to actual security risks during security development phases, enabling comprehensive security optimization across diverse threat conditions and attack scenarios.
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated security management that optimizes threat detection, incident response, and systematic security coordination based on real-time threat analysis and predictive intelligence. These systems continuously monitor threat environments and automatically execute security strategies when threat characteristics meet predefined response criteria for maximum security effectiveness and threat prevention.
Dynamic security resource allocation algorithms optimize threat response deployment using mathematical models that balance security depth against operational efficiency factors, achieving optimal performance through intelligent security coordination that adapts to changing threat conditions while maintaining systematic security discipline and response optimization.
Real-time threat monitoring systems track multiple security and threat indicators simultaneously to identify optimal security opportunities and automatically execute response strategies when conditions meet predefined criteria for threat mitigation or security enhancement. Statistical analysis enables automatic security optimization while maintaining response discipline and preventing false positive generation during uncertain threat periods.
Intelligent incident escalation systems use machine learning models to predict optimal security procedures and resource allocation based on threat context and historical effectiveness patterns rather than static response approaches that might not account for dynamic threat characteristics and attack evolution patterns.
Cross-system security integration algorithms manage security coordination across multiple security platforms and threat detection systems to achieve optimal security coverage while managing system complexity and coordination requirements that might affect overall security effectiveness and threat response reliability.
Advanced forecasting models predict optimal security strategies based on threat evolution patterns, attack technology development, and cybersecurity ecosystem changes that enable proactive security optimization and strategic threat positioning. Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and threat technique evolution patterns across different threat categories and attack innovation cycles.
Cybersecurity technology forecasting algorithms analyze historical threat development patterns, security innovation indicators, and threat mitigation advancement trends to predict periods when specific security strategies will offer optimal effectiveness requiring strategic security adjustments. Statistical analysis enables strategic security optimization that capitalizes on cybersecurity development cycles and threat mitigation technology advancement patterns.
Attack ecosystem impact analysis predicts how threat actor development, attack tool evolution, and criminal organization advancement will affect optimal security strategies and threat mitigation approaches over different time horizons and threat development scenarios.
Security mechanism evolution modeling predicts how protection advancement, automation enhancement, and cybersecurity sophistication will affect optimal security strategies and threat mitigation effectiveness, enabling proactive strategy adaptation based on expected security technology evolution.
Strategic security intelligence coordination integrates individual threat analysis with broader security positioning and systematic security optimization strategies to create comprehensive security approaches that adapt to changing threat landscapes while maintaining optimal security effectiveness across various threat conditions and evolution phases.
Even after digging into the details, you probably still have a few questions. Let's tackle the most common ones with straight answers.
There is a critical distinction to make:
This shows that your own security habits are just as important as Coinbase's platform security.
This is a trade-off between convenience and absolute control. It depends on your needs.
For long-term holding, a hardware wallet from a brand like Ledger or Trezor is the gold standard. For active trading, the robust security of a well-protected Coinbase account is often a practical choice.
Without a doubt, upgrade your Two-Factor Authentication (2FA) to a physical security key.
A physical security key makes your account almost completely bulletproof against remote attacks. Even if a scammer steals your password, they can't log in or approve a withdrawal without physically having your key. It's a massive leap forward from SMS or authenticator app 2FA.
This one action neutralizes the most common attack vectors and makes you an exceptionally difficult target. It is the closest thing to a silver bullet in personal account security.
Zero-trust analysis reveals that mathematically-optimized identity verification achieves 90-95% better security assurance compared to traditional perimeter-based approaches, with multi-factor authentication optimization enabling comprehensive identity verification through authentication factor combinations and biometric validation techniques for systematic access control coordination. Behavioral biometric analysis enables advanced user verification through typing pattern modeling and mouse movement analysis achieving 85-90% better authentication reliability, while privilege escalation prevention optimization enables systematic access control through permission hierarchy analysis and role-based access modeling. Continuous authentication monitoring enables real-time identity validation through session behavior pattern analysis and anomaly detection algorithms maintaining security throughout extended user sessions across different security environments.
Random Forest algorithms processing hundreds of security and threat variables achieve 92-97% accuracy in predicting attack likelihood while identifying critical security vulnerabilities conventional analysis might miss. Natural Language Processing models analyzing threat intelligence feeds and security communications achieve 85-90% accuracy in predicting threat landscape evolution through linguistic analysis and threat correlation revealing security optimization strategies, while LSTM networks processing sequential security data maintain awareness of historical threat patterns while adapting to current conditions. Support Vector Machine models achieve 89-94% accuracy in identifying optimal security response windows across different scenarios, with ensemble methods providing robust threat detection maintaining high accuracy through consensus-based threat identification systems adapting to changing threat dynamics.
Dynamic security resource allocation algorithms optimize threat response deployment using mathematical models balancing security depth against operational efficiency factors, achieving optimal performance through intelligent security coordination adapting to changing threat conditions while maintaining systematic security discipline. Real-time threat monitoring tracks multiple security and threat indicators to identify optimal security opportunities and automatically execute response strategies when conditions meet criteria for threat mitigation, with statistical analysis enabling optimization while preventing false positive generation. Intelligent incident escalation systems use machine learning to predict optimal security procedures based on threat context rather than static response approaches, while cross-system integration manages security coordination across multiple platforms to achieve optimal security coverage while managing system complexity requirements.
Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and threat technique evolution patterns across different threat categories and attack innovation cycles, with cybersecurity technology forecasting analyzing historical threat development patterns to predict when specific security strategies will offer optimal effectiveness. Attack ecosystem impact analysis predicts how threat actor development and attack tool evolution will affect optimal security strategies over different horizons, while security mechanism evolution modeling predicts how protection advancement will affect security strategy effectiveness. Strategic intelligence coordination integrates individual threat analysis with broader security positioning to create comprehensive approaches adapting to changing threat landscapes while maintaining optimal security effectiveness across various conditions and evolution phases.
Ready to stop guessing and start tracking the smart money? Wallet Finder.ai gives you the on-chain intelligence to discover profitable wallets and act on opportunities before the rest of the market. Start your 7-day trial and turn blockchain data into a competitive edge today at https://www.walletfinder.ai.