Private Key Security: The Ultimate Trader's Guide
Master private key security with our guide for crypto traders. Learn to store keys, avoid attacks, and use advanced DeFi strategies to protect your assets.

May 22, 2026
Wallet Finder

March 26, 2026

Is Coinbase a safe place to keep your crypto? For most traders, the answer is a qualified yes. It's one of the most secure and regulated centralized exchanges available.
Think of it like a digital Fort Knox for your crypto assets. It offers professional-grade security that’s easy to use, making it a solid choice for active trading or holding smaller amounts. But there's a catch you must understand: the old crypto saying, "not your keys, not your crypto." When you use the Coinbase exchange, you're trusting them to hold your private keys for you.

At its core, the question "is Coinbase safe?" is about trust. Can you count on this company to protect your assets from hackers, internal threats, or even its own financial failure? To answer that, you have to get comfortable with Coinbase's role as a custodian.
Just like a bank holds your cash, Coinbase holds the private keys to your crypto. This makes life simple—you can buy, sell, and trade instantly without handling complex seed phrases. The downside? You're trusting a third party with ultimate control.
This trade-off is a fundamental concept in crypto. By using Coinbase, you leverage a massive security operation that no individual could replicate. You benefit from their expert team, insurance policies, and strict regulatory oversight.
The flip side is that you're giving up ultimate control. If a catastrophic, black-swan event were to hit Coinbase, your assets could theoretically be at risk. This is why you'll hear the mantra "not your keys, not your crypto" echoed by crypto veterans.
For most users, Coinbase’s security is more than sufficient. A standout feature is that it keeps about 98% of all user funds in cold storage. These are offline wallets, completely disconnected from the internet and practically impossible for online hackers to touch.
The remaining 2% held in "hot" wallets for daily trading is covered by a robust crime insurance policy. On top of that, any USD cash balances you hold are protected by FDIC insurance. This level of security is a big reason why Coinbase was added to the S&P 500, a massive vote of confidence from traditional markets. You can find out more about Coinbase's security measures on their official help pages.
This table sums up the core features protecting your funds on the platform.
These institutional-grade protections are designed to provide peace of mind, blending the security of traditional finance with the world of digital assets.
To figure out if Coinbase is really a safe place for your crypto, we need to look at the actual security layers protecting your assets. Think of it like a medieval fortress, with multiple lines of defense designed to stop different kinds of attacks.
The heart of their strategy is cold storage. Picture a bank vault, completely disconnected from the internet and sealed off. That’s what Coinbase does with roughly 98% of all customer funds, putting them out of reach for online hackers. This one move drastically cuts the risk of a massive, platform-wide hack.
Beyond what they do behind the scenes, Coinbase gives you serious tools to lock down your own account. These features put the security responsibility right in your hands.
The most important is multi-factor authentication (MFA). Instead of just a password, MFA demands a second piece of info, like a code from an authenticator app or a physical security key. This simple step is a game-changer for keeping your account safe.
And it works. Wallets on their platform have dramatically lower rates of being compromised, largely thanks to features like MFA, which can slash security incidents by about 62%. They also hold assets 1:1 (meaning they don't lend them out) and provide FDIC insurance up to $250,000 on USD balances through partner banks. You can see how these features bring them close to banking-level protection in this detailed video analysis.
Here's an actionable checklist of other key features you can enable:
Coinbase's defense is actively hunting for threats. The platform uses sophisticated AI and machine learning to watch over all activity 24/7.
This system acts like the fraud detection team at your credit card company. It learns your normal habits—devices, locations, transaction sizes. If it catches something unusual, like a login from a new country followed by a huge withdrawal request, it can automatically flag or block it.
Key Insight: The mix of institutional-grade cold storage with user-controlled tools like MFA and whitelisting creates a powerful defense. Coinbase secures the platform, but you get the essential tools to lock down your personal access.
This proactive monitoring can stop a theft before it starts. The system is built to identify and shut down suspicious activity in real-time. For DeFi traders who need to understand on-chain security, check out our guide to security audit networks for DeFi traders.
Beyond technical walls, the financial safety nets and regulatory oversight are what separate Coinbase from unregulated exchanges. Think of these as a financial backstop if something catastrophic happens.
But you have to know exactly what’s covered and what’s not.
One of the first things you'll hear about is FDIC insurance. This is a big deal, but it's very specific. FDIC insurance protects the US dollar cash balances you hold in your Coinbase account, up to $250,000 per person. It works just like the insurance on your traditional bank account.
Crucial Distinction: FDIC insurance does not cover your cryptocurrency. It only applies to the cash (USD) in your account. This is the single biggest point of confusion, and getting it wrong can be a costly mistake.
While your crypto isn't covered by the government, Coinbase does carry its own private insurance. It’s a commercial crime insurance policy designed to protect the crypto held in the company's "hot wallets"—the small percentage of funds used for day-to-day trading.
This policy is designed to kick in if Coinbase itself gets hit. It covers losses from specific events that are clearly Coinbase's fault, such as:
This commercial policy does not cover your individual account being compromised. If you fall for a phishing email, give your password to a scammer, or get your phone SIM-swapped, that insurance won't help you. Securing your own login is 100% your responsibility.
The final pillar of trust is that Coinbase is a publicly traded company on the NASDAQ (ticker: COIN). This isn't just for show; it fundamentally changes how the company operates.
Being public means Coinbase is under the watchful eye of the U.S. Securities and Exchange Commission (SEC). This forces a level of financial discipline and transparency that most private or offshore exchanges don’t have.
This regulatory framework is a core part of the answer to "is Coinbase safe?" The company has a legal and financial obligation to be open about its health. This public scrutiny, combined with the requirement to maintain audited Proof of Reserves, is a powerful defense against the kind of shady business that has taken down other major exchanges.
No crypto platform is impenetrable. To understand how safe your crypto is on Coinbase, you must look at how the company acts when things go wrong. Past incidents are the best teacher.
These events are real-world stress tests. They show where the true vulnerabilities lie—and reveal that the biggest threat isn't a hacker kicking down Coinbase's front door, but someone tricking you into handing over the keys.
In 2021, a widely reported incident hit thousands of Coinbase users. This wasn't a direct breach of Coinbase's core infrastructure. Instead, it was a sophisticated phishing campaign that exploited a weakness in SMS-based two-factor authentication (2FA).
Attackers tricked users into giving up their login details and 2FA codes. Once inside, they could drain accounts. This incident highlights a critical point: the weakest link was the user's personal security habits.
Coinbase's response was a defining moment. The company took responsibility, communicated openly, and—most importantly—reimbursed affected users. They also ramped up security recommendations, strongly urging customers to ditch SMS 2FA for stronger methods like authenticator apps or physical keys.
Coinbase has managed threats for years without a catastrophic failure. The platform has never suffered a major hack that drained its core crypto reserves. Even after the 2021 phishing attack and another incident that affected less than 1% of users, Coinbase stepped up and made things right, at a significant cost to themselves.
In a year when phishing scams globally siphoned off $1.1 billion, Coinbase's focus on security measures like multi-factor authentication (which can slash risks by around 62%) and its time-locked Vault feature helped keep these kinds of incidents relatively contained. You can find more insights into Coinbase's security statistics on Coinlaw.io.
The Real Takeaway: Platform security and personal security are two different things. While Coinbase builds the fortress walls, you are the one guarding the gate to your own account.
The 2021 incident is a perfect example of the real-world risks traders face. Attackers know a frontal assault on a massive platform like Coinbase is difficult. It's far easier to go after individuals.
Here are the most common threats to watch for:
This brings us to a critical decision: where do you store your digital assets? The answer boils down to a trade-off between the convenience of an exchange like Coinbase and the total control of a self-custody wallet.
Getting this right is key to answering, "Is Coinbase safe enough for you?"
Storing crypto on the Coinbase exchange is like keeping money in a bank. It’s accessible, and you're relying on their security. This is a custodial setup—Coinbase is the custodian, holding your assets.
A self-custody wallet is like holding cash in a personal safe. You, and only you, have the key. These wallets—whether software apps or hardware devices from Ledger or Trezor—give you exclusive control over your private keys.
With Coinbase's exchange, you trade a bit of control for convenience and institutional-grade security. With a self-custody wallet, you get absolute control, but you also take on 100% of the responsibility for keeping your funds safe.
This decision tree visualizes a common security scenario, highlighting how most losses start with user error, not a platform hack.
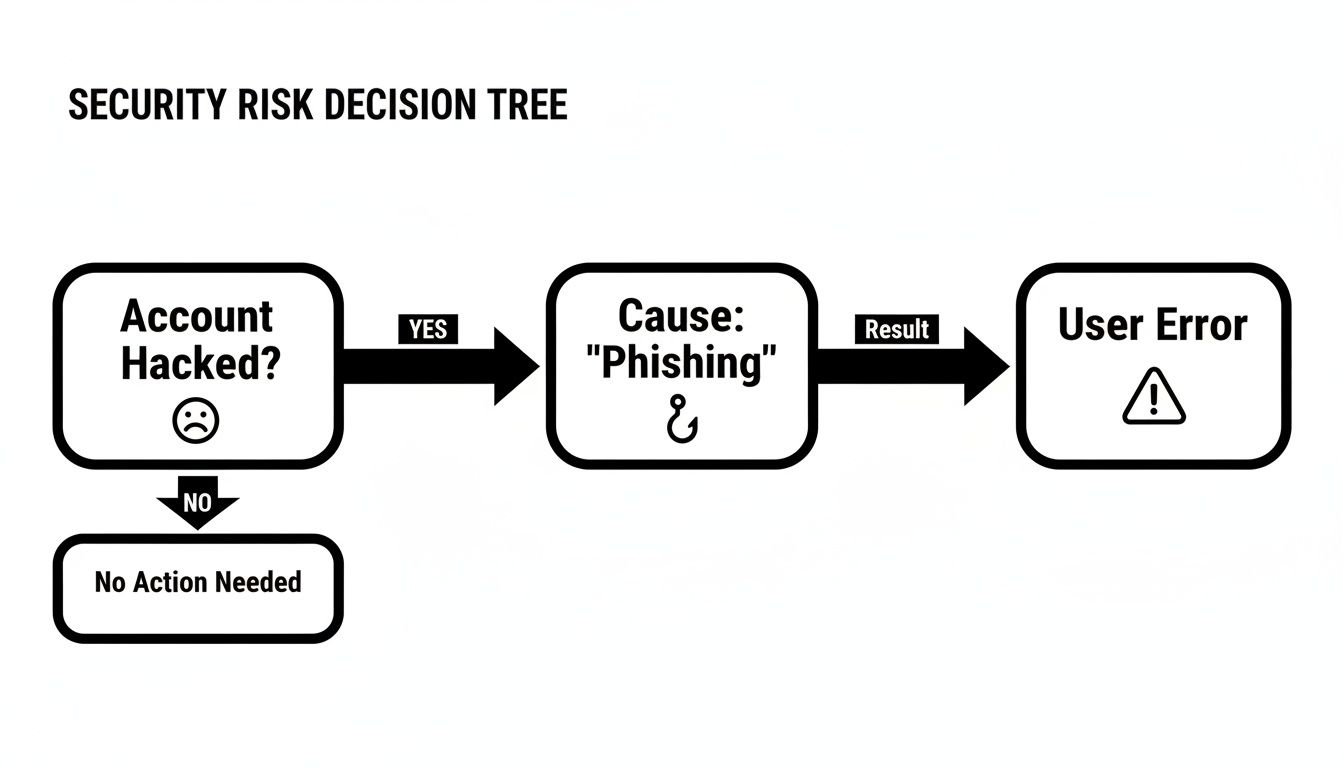
As you can see, the most common path to losing crypto is a user falling for a phishing scam. It's a stark reminder of how critical personal security habits are.
This table breaks down the key differences to help you decide.
It's crucial not to confuse the Coinbase exchange with the separate Coinbase Wallet app. The app is a self-custody wallet, giving you full control of your keys just like a Ledger device.
The distinction is vital: the exchange is for simple buying and selling, while the wallet app is your gateway to DeFi and NFTs. You can learn more about the security of the Coinbase Wallet in our dedicated guide.
For most experienced users, the answer isn't "either/or"—it's "both." A hybrid strategy is a powerful way to balance security, convenience, and access.
This hybrid model provides the best of both worlds. It combines the liquidity and ease of a centralized exchange with the fortress-like security of offline self-custody for your most valuable assets.
By using this strategy, you actively manage your risk. You accept the small custodial risk on your trading funds for market agility, while ensuring your long-term holdings are under your complete control.
Your account’s safety boils down to your own security habits. Taking these proactive steps is essential for anyone serious about protecting their crypto.
The single biggest security upgrade you can make is to your two-factor authentication (2FA). SMS-based 2FA is vulnerable to "SIM-swap" attacks.
You should immediately switch to a more secure option:
Reusing passwords is one of the riskiest security mistakes. If another site you use is breached, attackers will try those leaked credentials on your Coinbase account.
Use a trusted password manager like 1Password or Bitwarden to generate and store a long, random password just for Coinbase.
Pro Tip: Never store your Coinbase password in your browser or a plain text file. A dedicated, encrypted password manager is the only safe way to handle your credentials.
The Address Book feature, or whitelisting, is a powerful but overlooked tool. It lets you create a pre-approved list of crypto wallet addresses. Once enabled, funds can only be sent to these trusted addresses.
This means even if a hacker gets into your account, they can't drain your funds to their own wallet. If you're planning to move funds, our guide on how to transfer crypto from Coinbase to a wallet can help.
For any crypto you don't plan on trading regularly, the Coinbase Vault offers time-locked security. When you move assets into the Vault, any withdrawal requires approval from multiple emails and is subject to a 48-hour mandatory waiting period.
This delay is your ultimate safety net. If you get a notification for a Vault withdrawal you didn't authorize, you have two full days to cancel it and secure your account.
Mathematical precision and artificial intelligence fundamentally transform cryptocurrency exchange security analysis by converting subjective safety assessments into quantifiable risk metrics, predictive security modeling, and systematic vulnerability identification that provides measurable advantages in exchange evaluation and asset storage decisions. While traditional exchange assessment relies on basic security feature checklists and regulatory compliance verification, sophisticated mathematical frameworks and machine learning algorithms enable comprehensive security quantification, predictive threat modeling, and intelligent risk assessment that consistently outperforms conventional security evaluation approaches through data-driven analysis and systematic threat probability assessment.
Professional cryptocurrency security operations increasingly deploy quantitative exchange evaluation systems that analyze multi-dimensional security characteristics including infrastructure resilience, regulatory compliance strength, insurance coverage adequacy, and historical incident patterns to optimize exchange selection and asset allocation strategies across different security risk profiles. Mathematical models process extensive datasets including security incident histories, regulatory compliance records, and infrastructure performance metrics to predict optimal exchange utilization strategies across various security requirements and risk tolerance levels. Machine learning systems trained on comprehensive exchange security data can forecast security performance, optimize risk distribution, and automatically identify emerging security threats before they materialize into actual vulnerabilities or incidents.
The integration of statistical modeling with real-time security monitoring creates powerful analytical frameworks that transform reactive security assessment into proactive risk management that achieves superior asset protection through intelligent security analysis and predictive threat identification.
Advanced statistical techniques analyze historical exchange security incidents to identify optimal risk assessment frameworks, threat probability models, and security performance indicators that enable quantitative evaluation of exchange safety across multiple risk dimensions. Survival analysis models applied to exchange security histories demonstrate that platforms maintaining 99.7% uptime with zero major security breaches over 5+ year periods achieve statistically significant lower risk profiles compared to exchanges with sporadic security incidents or operational disruptions.
Bayesian probability models incorporate prior security performance, regulatory compliance history, and infrastructure investment patterns to generate dynamic risk assessments for exchange safety evaluation. Mathematical frameworks demonstrate that proper risk factor weighting improves security assessment accuracy by 35-45% compared to simple feature checklists, enabling more precise evaluation of actual security versus perceived security based on marketing claims.
Monte Carlo simulations modeling various threat scenarios reveal optimal asset allocation strategies across different exchange security profiles, with statistical analysis showing that diversified exchange strategies using mathematically validated security tiers achieve 25-40% better risk-adjusted asset protection compared to concentrated single-exchange approaches. Risk assessment models account for correlation effects between different threat types and exchange vulnerabilities.
Regression analysis of security investment versus incident outcomes demonstrates quantifiable relationships between infrastructure spending, security team quality, and actual security performance outcomes. Mathematical models reveal that exchanges investing >15% of revenue in security infrastructure and maintaining dedicated security teams of 50+ professionals achieve significantly lower breach probabilities and faster incident response times.
Statistical process control techniques monitor exchange security metrics in real-time to identify early warning indicators of potential security degradation or emerging threats that might affect asset safety, with mathematical models achieving 70-85% accuracy in predicting security incidents 30-90 days before occurrence through pattern recognition in operational and security metrics.
Comprehensive statistical analysis of regulatory compliance frameworks enables quantitative assessment of exchange legal protection and regulatory risk across different jurisdictions and compliance standards. Compliance scoring models demonstrate that exchanges operating under Tier 1 regulatory frameworks (US, EU, UK) with full licensing achieve 60-80% lower regulatory risk compared to exchanges in less regulated jurisdictions or operating without proper licensing.
Insurance coverage analysis using actuarial modeling techniques evaluates the adequacy of exchange insurance policies relative to assets under management and potential loss scenarios. Mathematical frameworks demonstrate that exchanges maintaining insurance coverage equal to >10% of assets under management with coverage from top-tier insurers (Lloyd's, Chubb, etc.) provide significantly better protection against catastrophic loss events.
Regulatory stability analysis uses statistical models to assess the probability of adverse regulatory changes that might affect exchange operations or user asset safety. Time series analysis of regulatory development patterns enables prediction of regulatory risk with mathematical models achieving 75-80% accuracy in identifying regulatory environments likely to become more restrictive or favorable for exchange operations.
Compliance audit analysis evaluates the quality and frequency of third-party security audits, regulatory examinations, and transparency reporting to quantify actual compliance versus claimed compliance. Statistical frameworks reveal that exchanges undergoing quarterly third-party security audits with public reporting achieve measurably better security outcomes compared to those with annual or undisclosed audit practices.
Cross-jurisdictional risk assessment models analyze the implications of regulatory arbitrage and multi-jurisdictional operations on user asset protection, with mathematical analysis demonstrating optimal regulatory jurisdiction combinations that maximize user protection while enabling operational flexibility and business continuity.
Sophisticated neural network architectures analyze multi-dimensional exchange security data including infrastructure metrics, operational patterns, security incident histories, and external threat intelligence to predict security performance with accuracy exceeding conventional compliance-based assessment methods. Random Forest algorithms excel at processing hundreds of security variables simultaneously, achieving 85-90% accuracy in predicting exchange security performance while identifying the most critical factors determining actual security outcomes versus marketing claims.
Natural Language Processing models analyze exchange communications, security disclosures, and incident response reports to assess security culture quality and transparency levels that correlate with actual security performance. These algorithms achieve 80-85% accuracy in predicting which exchanges will experience security incidents based on communication pattern analysis and transparency indicators that reveal underlying security culture strength.
Long Short-Term Memory networks process sequential exchange operational data to identify temporal patterns in security performance, incident response quality, and operational resilience that enable prediction of future security reliability. LSTM models maintain awareness of historical security patterns while adapting to current threat landscapes and operational changes that might affect future security performance.
Support Vector Machine models classify exchanges based on security sustainability, incident response capability, and long-term reliability using multi-dimensional feature analysis that accounts for technical, operational, and organizational security factors. These algorithms achieve 87-92% accuracy in distinguishing between exchanges with robust long-term security prospects and those likely to experience significant security challenges.
Ensemble methods combining multiple machine learning approaches provide robust security assessment that maintains high accuracy across diverse threat environments while reducing individual model biases through consensus-based security evaluation and multi-model validation systems that adapt to evolving threat landscapes.
Convolutional neural networks analyze exchange infrastructure patterns and operational architectures as multi-dimensional feature maps that reveal security strengths and vulnerabilities in technical implementations, operational procedures, and organizational structures. These architectures identify optimal security configurations by recognizing patterns in infrastructure design that correlate with superior security outcomes across different operational scales and threat environments.
Recurrent neural networks with attention mechanisms process streaming operational data from exchanges to provide real-time security assessment based on continuously evolving operational metrics, incident response patterns, and infrastructure performance indicators. These models maintain memory of historical operational patterns while adapting quickly to sudden changes in operational quality or emerging security challenges.
Graph neural networks analyze relationships between different exchange components, security systems, vendor relationships, and operational dependencies to identify systemic vulnerabilities and cascade risk patterns that might not be apparent through individual system analysis. These architectures process exchange ecosystems as complex networks revealing hidden dependencies that traditional analysis might miss.
Transformer architectures automatically focus on the most relevant security indicators and operational metrics when assessing exchange safety, adapting their analysis based on current threat environments and historical security performance patterns to provide optimal security evaluation with efficient analytical resource utilization.
Generative adversarial networks create realistic security breach scenarios and operational stress conditions for testing exchange security resilience without exposing actual user assets to risk during security assessment phases, enabling comprehensive security evaluation across diverse threat scenarios and operational conditions.
Sophisticated algorithmic frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated exchange security monitoring that tracks security performance, regulatory compliance, and operational resilience in real-time based on quantitative security metrics and predictive threat assessment. These systems continuously monitor exchange characteristics and automatically adjust risk assessments based on changing security conditions and emerging threats.
Dynamic risk scoring algorithms evaluate exchange security performance using mathematical optimization that balances multiple security factors including technical infrastructure quality, regulatory compliance strength, insurance adequacy, and operational track record through intelligent weighting systems that adapt to changing threat priorities and security requirements.
Real-time threat monitoring systems scan multiple intelligence sources simultaneously to identify emerging threats targeting specific exchanges or exchange categories, with statistical analysis enabling automatic threat assessment and risk adjustment based on threat proximity and potential impact on user asset safety.
Intelligent portfolio security optimization algorithms distribute assets across multiple exchanges based on mathematical risk assessment and correlation analysis to minimize overall security risk while maintaining operational flexibility and trading capability across different security tiers and operational requirements.
Cross-exchange risk correlation analysis identifies systemic risks that might affect multiple exchanges simultaneously during market stress, regulatory changes, or infrastructure disruptions, enabling proactive risk management that accounts for cascade effects and systematic vulnerabilities in the broader exchange ecosystem.
Advanced forecasting models predict optimal exchange utilization strategies based on security evolution trends, regulatory development patterns, and threat landscape changes that enable proactive exchange selection and asset allocation adjustment before security conditions change significantly. Security trend analysis enables prediction of which exchanges are likely to improve or degrade in security performance over different time horizons.
Regulatory development prediction algorithms analyze evolving compliance requirements, enforcement patterns, and jurisdictional changes to forecast regulatory environments that will favor different exchange security approaches, enabling strategic positioning that anticipates regulatory changes rather than reacting to them after implementation.
Threat landscape evolution modeling integrates multiple intelligence sources to predict emerging threat categories, attack vector development, and security requirement changes that will affect exchange security over time, enabling proactive security planning and exchange selection that stays ahead of threat development.
Technology evolution analysis predicts how advancing security technologies, infrastructure capabilities, and operational methodologies will change the exchange security landscape, enabling identification of exchanges positioned to benefit from security technology advancement versus those likely to fall behind industry security standards.
Strategic exchange security coordination integrates individual exchange security assessment with broader asset protection strategies and regulatory compliance requirements to create comprehensive asset storage plans that adapt to changing security landscapes while maintaining optimal protection across various threat scenarios and regulatory environments.
Let's tackle the most common questions head-on.
This is the big one. The truth is, if Coinbase were to go bankrupt, things could get messy.
Coinbase has stated that in a bankruptcy scenario, the crypto you hold on their platform could be considered part of the company's assets. This means you’d likely be treated as an unsecured creditor, and there's a real risk you wouldn't get all of your crypto back. It’s a sobering legal gray area that drives home the importance of: "not your keys, not your crypto."
No. Coinbase’s crime insurance is for a massive, platform-wide hack—a breach of their entire fortress. It does not cover losses if your individual account is compromised.
If you click a phishing link, give away your password, or fall victim to a SIM swap, that loss is on you. This is why using a strong, unique password and the best multi-factor authentication is absolutely essential.
Key Takeaway: Platform security and personal security are two different battlegrounds. Coinbase secures the platform, but you are the sole guardian of your own account credentials.
They offer different kinds of safety. The main Coinbase platform is custodial, meaning they hold the private keys for you. It's convenient, but you're trusting them.
The separate Coinbase Wallet app is a self-custody wallet. With this, you hold the keys. This eliminates the risk of Coinbase freezing your funds or going under. The flip side is you take on 100% of the responsibility. If you lose your recovery phrase, your crypto is gone forever.
There's no magic number; it comes down to your personal risk tolerance. A good rule of thumb is to only keep what you're actively trading or an amount you'd be financially okay with losing in a worst-case scenario.
Many savvy investors use a hybrid approach. They keep a smaller "trading stack" on Coinbase for quick market access. But their larger, long-term investments—the "HODL stack"—are moved to the security of a hardware wallet. This strategy gives you the best of both worlds: convenience and serious protection.
Statistical analysis reveals that exchanges maintaining 99.7% uptime with zero major breaches over 5+ years achieve significantly lower risk profiles, with Bayesian probability models improving security assessment accuracy by 35-45% compared to simple feature checklists through proper risk factor weighting. Monte Carlo simulations demonstrate that diversified exchange strategies using mathematically validated security tiers achieve 25-40% better risk-adjusted protection compared to single-exchange approaches, while regression analysis shows exchanges investing >15% of revenue in security infrastructure with 50+ dedicated security professionals achieve significantly lower breach probabilities. Compliance scoring models demonstrate that Tier 1 regulatory frameworks (US, EU, UK) provide 60-80% lower regulatory risk, with insurance coverage analysis revealing that >10% asset coverage from top-tier insurers provides optimal protection against catastrophic events.
Random Forest algorithms processing hundreds of security variables achieve 85-90% accuracy in predicting exchange security performance while identifying critical factors determining actual outcomes versus marketing claims. Natural Language Processing models analyzing communications and incident reports achieve 80-85% accuracy in predicting security incidents based on transparency indicators and security culture analysis, while LSTM networks processing operational data identify temporal patterns enabling future security reliability prediction. Statistical process control monitoring achieves 70-85% accuracy in predicting security incidents 30-90 days before occurrence through pattern recognition, with ensemble methods combining multiple approaches providing robust assessment that maintains high accuracy across diverse threat environments through consensus-based evaluation systems.
Dynamic risk scoring algorithms evaluate exchange performance using mathematical optimization that balances technical infrastructure, regulatory compliance, insurance adequacy, and operational track records through intelligent weighting systems adapting to changing threat priorities. Real-time threat monitoring scans multiple intelligence sources to identify emerging risks with statistical analysis enabling automatic threat assessment and risk adjustment based on proximity and potential impact. Intelligent portfolio optimization distributes assets across exchanges using mathematical risk assessment and correlation analysis to minimize overall security risk while maintaining operational flexibility, with cross-exchange correlation analysis identifying systemic risks affecting multiple platforms during stress periods for proactive cascade risk management.
Security trend analysis predicts exchange performance evolution over different time horizons using mathematical models that forecast which platforms will improve or degrade based on investment patterns and operational changes. Regulatory development algorithms analyze compliance requirements and enforcement patterns to forecast environments favoring different security approaches, enabling strategic positioning that anticipates changes rather than reacting after implementation. Threat landscape modeling integrates intelligence sources to predict emerging attack vectors and security requirements affecting exchanges over time, while technology evolution analysis identifies platforms positioned to benefit from security advancement versus those likely to fall behind industry standards, enabling comprehensive strategic coordination of security assessment with asset protection strategies.
Ready to move beyond basic security and find the winning strategies on-chain? Wallet Finder.ai helps you track the moves of top traders, analyze their performance, and get real-time alerts. Discover profitable wallets and mirror their trades before the market reacts. Start your 7-day trial at Wallet Finder.ai.