Backtesting Framework A Guide for Crypto Traders
Build a backtesting framework that works for DeFi. Learn core components, on-chain challenges like gas and MEV, and how to test strategies before you trade.

May 20, 2026
Wallet Finder

March 11, 2026

When it comes to your crypto, "secure" means you're in control. Coinbase Wallet is built on a non-custodial foundation, which is a fancy way of saying you—and only you—hold the keys to your funds. While the app itself is packed with security features, the real strength of your wallet comes down to how you handle your secret recovery phrase.

Think of Coinbase Wallet like a high-tech safe you keep at home. Coinbase builds the reinforced steel door and installs the complex locking mechanism, but you're the only person who knows the combination.
This is a world away from how a typical crypto exchange works, where the company holds your assets for you, kind of like a bank. If you want to get into the weeds on this, our guide on a crypto exchange vs wallet breaks it down completely.
This "self-custody" approach is incredibly powerful. It means Coinbase can't touch, freeze, or lose your funds even if they wanted to. Your private keys are created and locked down directly on your device, using its built-in security hardware like the Secure Enclave on an iPhone.
But with great power comes great responsibility. While the wallet software is solid, it can't protect you from things happening outside the app, like getting tricked by a phishing scam or signing a malicious transaction. To truly answer "how secure is Coinbase wallet?", you have to look at both sides of the coin: the app's security and your own.
This is what we call a shared responsibility model. The table below clearly lays out what the wallet handles and what falls squarely on your shoulders.
The security architecture of Coinbase Wallet is best understood as four parallel layers, each one split between what the software handles automatically and what requires active engagement from you. Neither side of any layer is optional — the wallet's protections and your own behavior are complementary halves of a complete defense.
At the foundation is private key storage. The wallet encrypts your keys and holds them locally within your device's secure hardware, keeping them off Coinbase's servers and out of reach of remote attackers. Your corresponding responsibility is the recovery phrase that represents those keys: writing it down, storing it offline in a secure physical location, and never sharing it with anyone under any circumstances. The wallet's key storage is only as meaningful as the security of the phrase that can regenerate those keys from scratch.
The second layer is app access. Coinbase Wallet requires biometric authentication — Face ID or a fingerprint scan — along with a PIN before anyone can open the app, creating a barrier against unauthorized access if your device is lost or stolen. Your side of this layer is setting a PIN that is genuinely strong and unique rather than something guessable, and keeping the physical device itself secure so that the authentication requirement cannot be bypassed through direct hardware access.
The third layer is transaction signing. The wallet requires your explicit approval for every outbound transaction, which prevents any external party from moving funds without your active consent. This protection is only as strong as the attention you bring to the confirmation screen. Reviewing the full details of every transaction — the destination address, the amount, and the specific contract permissions being granted — before signing is the behavior that makes the signing requirement meaningful rather than a rubber stamp you click through quickly.
The fourth layer is scam prevention. The wallet maintains warnings for known malicious DApps and filters out spam tokens to reduce your exposure to common attack vectors. Your role here is to treat these warnings as a starting point rather than a complete solution: avoiding suspicious links, manually verifying URLs before connecting your wallet, and approaching unsolicited offers or airdrop claims with skepticism regardless of how legitimate they appear.
Ultimately, Coinbase provides the secure vault, but you're the security guard at the door. Your diligence is the final, most crucial layer of defense for your crypto.
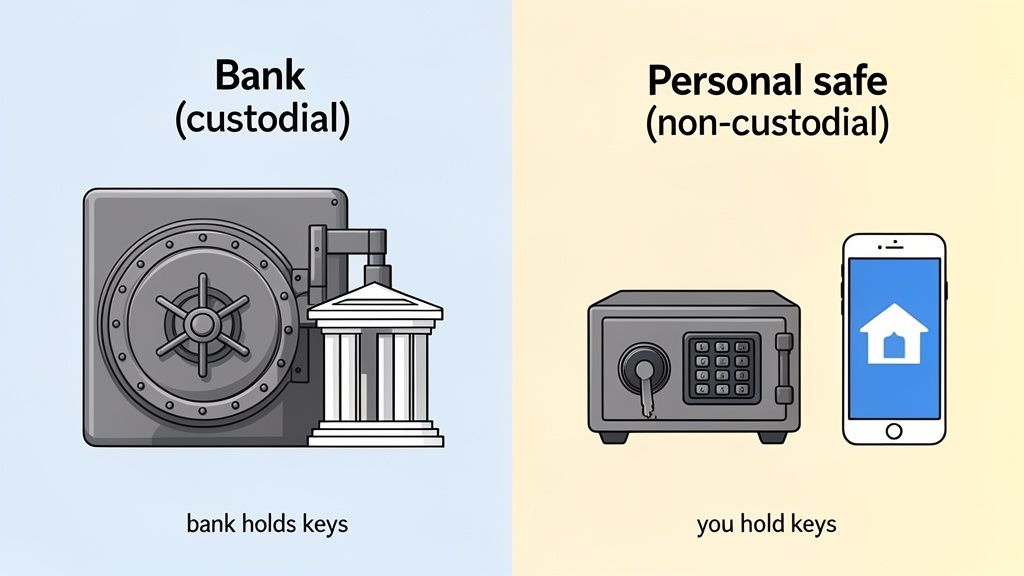
To really get a handle on Coinbase Wallet's security, we have to start with one core idea: it's "non-custodial." This isn't just jargon; it's a fundamental concept that completely changes who's in charge of your crypto.
Think of it like the difference between a traditional bank and a personal safe you keep at home. The bank is a custodian. They hold your money in their vault, and while you can access it, they have the ultimate control. They can freeze your account, and their security is what stands between a thief and your cash.
Coinbase Wallet is your personal safe. You, and only you, hold the key. In the world of crypto, that "key" is your set of private keys, which are protected by your 12-word recovery phrase. This isn't just a small detail—it's the entire foundation of the wallet's security design.
When you first set up your Coinbase Wallet, it generates your unique private keys right then and there. These keys are never sent to Coinbase's servers or stored in some online database. Instead, they’re encrypted and kept directly on your phone or computer, taking advantage of the device's own security hardware.
For instance, modern iPhones have a specialized chip called the Secure Enclave. It’s a hardware-based key manager that’s totally walled off from the main processor and the rest of the operating system.
This on-device approach means even Coinbase can't touch, see, or move your funds. They build the app—the interface you use—but they never hold the keys to the vault. This design choice eliminates a massive central point of failure.
This model is a game-changer. An incident involving rogue overseas support agents at Coinbase actually proved the strength of this system. While some customer data was compromised, not a single dollar of wallet funds was at risk because the private keys were never accessible to Coinbase or its staff in the first place.
This kind of personal control is non-negotiable for active traders. If you're copy trading or diving into decentralized finance (DeFi), you need 24/7, unrestricted access to your capital. You simply can't risk getting locked out because an exchange is down for maintenance or has decided to freeze withdrawals. Our guide on what is a DeFi wallet goes deeper into why this control is so critical.
Breaking down the practical differences between these two models makes it crystal clear where the security responsibility falls. It’s not about one being better than the other, but about picking the right tool for the job.
The most fundamental difference between a custodial platform and a non-custodial wallet is who holds the private keys. On a custodial exchange like Coinbase.com, the exchange holds the keys on your behalf. You have an account with a balance, but the actual cryptographic ownership of those assets belongs to the platform. A non-custodial wallet like Coinbase Wallet inverts this entirely: the keys are generated on your device and stay there, meaning you hold direct, unmediated ownership of everything in the wallet.
That key custody difference determines everything else. Because a custodial exchange controls the keys, it also controls access. It can freeze your account, limit withdrawals, or restrict activity in response to regulatory pressure, a compliance flag, or its own operational decisions. A non-custodial wallet has no equivalent mechanism. No company, regulator, or third party can freeze funds that are controlled by keys stored on your own device, because there is no intermediary with the authority or the technical ability to do so.
Recovery works differently under each model as a direct consequence of where custody sits. A custodial platform can restore your access through identity verification and a password reset because it holds the keys independently of your login credentials. If you lose access to your account, the platform can verify who you are and let you back in. A non-custodial wallet has no such fallback. The 12-word recovery phrase is the one and only mechanism for restoring access, because it is the only representation of the keys themselves. Lose the phrase with no backup, and the funds are permanently inaccessible to everyone including you.
The risk profiles follow naturally from these structural differences. Custodial platforms concentrate risk at the platform level: an exchange hack, an insolvency event, or a regulatory freeze affects every user simultaneously regardless of individual behavior. Non-custodial wallets shift risk entirely to the individual: the platform cannot be hacked for your keys because it does not hold them, but losing your recovery phrase, falling for a phishing attack, or having your device compromised are risks that only your own diligence can prevent.
This complete ownership is precisely why the answer to "how secure is Coinbase Wallet?" always comes back to you, the user. The wallet gives you a fortress, but you're the one holding the keys. Its ultimate security depends on how well you protect your device and, most importantly, that sacred recovery phrase.
Beyond its core non-custodial design, Coinbase Wallet isn't just a passive vault; it's an active security system with multiple layers of defense. These aren't just checkbox features. They’re practical tools designed to shield you from both sophisticated external threats and simple, costly human errors.
Think of it like the safety system in a modern car. The non-custodial architecture is the high-strength steel frame, but you also get airbags, seatbelts, and automatic braking. All these components work together to keep you safe on the road. Coinbase Wallet brings this same layered philosophy to protecting your crypto.
These features are engineered to create just enough friction at critical moments, forcing you to pause and double-check what you're doing before you commit to an irreversible on-chain transaction.
The very first security layer you'll bump into is the one protecting the app itself. Before you can even peek at your balances or think about sending funds, the wallet demands you prove it's really you.
This is a non-negotiable security gate. It ensures that if someone gets their hands on your unlocked phone, they can't just open your wallet and go on a spending spree. For this, the wallet cleverly uses your device's own built-in security.
This initial barrier is absolutely crucial. It creates a clear separation between your phone's general security and your wallet's security, adding a vital layer of protection against physical theft.
Coinbase Wallet doesn't just sit back and wait for an attack; it actively tries to steer you away from common crypto scams and traps. It has several built-in mechanisms that act as an early warning system, helping you spot danger before you sign a malicious transaction.
These features are a lifesaver for DeFi traders who are constantly interacting with new DApps and contracts. One wrong signature on a sketchy site can wipe you out, which makes these proactive alerts a massive part of the wallet's value proposition.
A core tenet of crypto security is "don't trust, verify." Coinbase Wallet’s built-in alerts and previews help automate parts of that verification process. It’s like having a digital co-pilot that points out potential hazards before you fly into them.
The wallet uses a few specific tools to make your journey through the on-chain world safer:
These features work together to create a much safer experience, dramatically lowering the odds that a simple mistake will lead to a catastrophic loss.
One of the wallet’s most debated features is the optional encrypted cloud backup for your recovery phrase. This tool lets you save your 12-word phrase to your personal Google Drive or iCloud account, locked behind a password that only you set.
The convenience factor is huge—it gives you a way to get your wallet back if you lose the piece of paper with your phrase on it. At the same time, it introduces a potential online attack vector that simply doesn't exist if your backup is purely offline.
Here’s a look at the trade-offs:
The convenience case for cloud backup is straightforward. If you lose the physical copy of your recovery phrase, a cloud backup gives you a way to restore access to your wallet on a new device without that backup being permanently lost. For users who are genuinely at risk of misplacing a paper backup or who lack a secure physical storage option, this digital failsafe has real practical value.
The security trade-off is equally straightforward. Enabling cloud backup means your recovery phrase exists in an online environment, even in encrypted form. The encryption itself relies on a password only you set, which is a meaningful protection layer — but it introduces a compound vulnerability that does not exist with a purely offline backup. An attacker who gains access to both your cloud account and your backup password has everything needed to take your funds. Neither breach alone is sufficient, but both are achievable through phishing, credential stuffing, or social engineering, which means the combined risk is not negligible.
The recovery dimension cuts both ways in a less obvious way. The cloud backup solves one recovery problem — physical loss or destruction of your phrase — while creating a new one. If you forget the specific password you used to encrypt the backup, the phrase is inaccessible regardless of whether the file itself is intact. A strong, unique password that you do not write down anywhere is difficult to remember over a long period; a password you do write down reintroduces a physical exposure point. This means the cloud backup option effectively trades one category of recovery risk for another rather than eliminating the problem entirely.
The bottom line is that cloud backup is a convenience feature with a defined security cost, not a security upgrade. For users who understand that trade-off and accept it, it functions as a reasonable secondary failsafe. It should never replace an offline physical backup, and ideally it exists alongside one rather than instead of it.
For maximum security, the gold standard is—and always will be—to store your recovery phrase completely offline in multiple secure physical locations. But for users who understand and accept the risk, the cloud backup can be a handy, though less secure, fallback. If you do enable it, the key is to use an incredibly strong, unique password for the encryption.
While Coinbase Wallet gives you a solid, non-custodial foundation, its security features can only protect what happens inside the app. The wild world of DeFi is an open frontier, and that freedom exposes active traders to a whole different class of threats—ones that target your behavior, not the wallet software itself.
Think of it this way: a secure wallet is your shield, but understanding these attack vectors is your sword. Scammers are always cooking up new ways to trick you into willingly signing away your funds. Let's break down their most common tactics.
Phishing is one of the oldest tricks in the book, but it's brutally effective. Forget clunky emails with typos. Scammers now create pixel-perfect clones of popular DeFi apps, NFT marketplaces, and airdrop claim pages. They look and feel exactly like the real deal.
You'll usually find links to these fake sites shared on social media, in a Discord server, or even promoted in search results. When you connect your wallet, the site will hit you with one of two requests: it will either ask for your 12-word recovery phrase (which you should never, ever share) or prompt you to sign what looks like a harmless transaction.
Phishing attacks thrive on urgency and FOMO. A surprise airdrop for a hot new token is a classic lure. Always triple-check URLs and be deeply skeptical of any site asking for your recovery phrase or pushing you toward a "wallet migration" or "security upgrade."
The moment you enter your phrase or sign their malicious transaction, the game is over. The scammer gets full control and will drain your wallet in seconds.
A much sneakier threat is the malicious token approval. When you use a new decentralized exchange (DEX), it asks you to "approve" spending for a certain token, like USDC. This is a normal, necessary step that lets the DEX's smart contract execute your trades.
But scammers have weaponized this mechanism. They'll build a malicious smart contract disguised as a new trading tool, a high-yield staking pool, or an exclusive NFT mint. When you interact with their site, your wallet pops up with an approval request. If you're rushing and not paying close attention, you might accidentally sign an unlimited approval.
This gives the scammer's contract permission to withdraw all of that specific token from your wallet, whenever they want, without needing you to sign anything ever again. It’s like giving a complete stranger a signed blank check.
This is exactly why the transaction previews and approval alerts inside Coinbase Wallet are so critical. They are your last line of defense, showing you precisely what permissions you’re about to grant before you commit.
The beauty of DeFi is that anyone can deploy a smart contract. The danger is... well, that anyone can deploy a smart contract. A flood of new projects launch without getting a formal security audit from a reputable firm.
Interacting with these unaudited contracts is like walking into a building before the safety inspector has signed off on it. It might be fine. Or it might have a critical flaw that an attacker can exploit to drain funds from everyone who deposited assets into it.
Before you jump into a new protocol or liquidity pool, always look for a public security audit. Legitimate projects are proud to share their audit reports from firms like CertiK, Trail of Bits, or OpenZeppelin. No audit? That's a massive red flag.
Finally, never underestimate good old-fashioned social engineering. Scammers haunt community forums like Discord, Telegram, and X (formerly Twitter), often impersonating project developers or support staff.
These fakers will slide into your DMs with "helpful" advice, offer to troubleshoot a problem, or announce a "special giveaway" just for you. Their goal is always the same: to trick you into revealing your recovery phrase, sending them crypto, or clicking a link to their phishing site.
Burn these golden rules into your brain:
By understanding how these scams work, you can shift from being a potential target to a vigilant defender. Your Coinbase Wallet gives you the secure tools, but your awareness is what truly keeps you safe in the DeFi wild west.
Knowing the threats is one thing; doing something about them is another. Fortifying your Coinbase Wallet isn’t about complex technical wizardry. It’s about building a few disciplined habits that can turn a standard digital wallet into a personal financial fortress and dramatically cut down your risk.
This decision tree gives you a simple mental framework for navigating common—and often tricky—DeFi interactions.
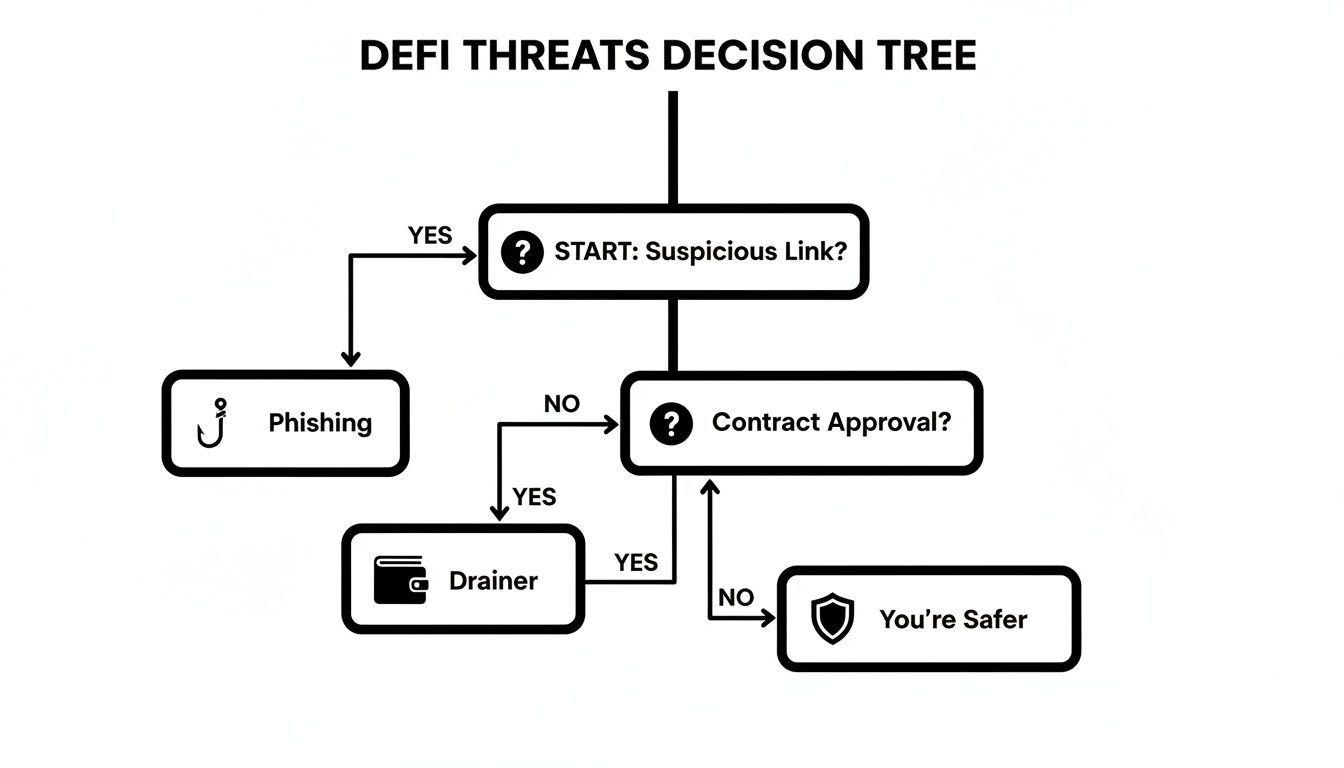
As you can see, the path to safety boils down to being extra cautious about two main attack vectors: sketchy phishing links and malicious contract approvals.
The best security comes from layering the wallet's built-in features with your own vigilant practices. When you create multiple layers of defense, a single mistake is far less likely to result in a total wipeout. Let's walk through the most impactful strategies you can put in place today.
If you do only one thing on this list, make it this one. Pairing your Coinbase Wallet with a hardware wallet like a Ledger or Trezor is the single most effective security upgrade you can make. It immediately elevates your setup by keeping your private keys completely offline, even when you’re interacting with online DApps.
Think of it like this: your Coinbase Wallet app becomes the secure "browser" you use to explore DeFi, but the hardware wallet acts as the physical key and signature pad. Every single transaction, no matter how small, has to be physically approved on the hardware device itself.
This simple step neutralizes the most common remote attacks:
Setting this up is easy. You simply import your hardware wallet's public address into Coinbase Wallet. This creates a "watch-only" view, letting you see your balances and initiate transactions. But to actually sign and send anything, you'll need to physically plug in and approve it on your Ledger or Trezor.
Not all of your crypto needs to be on the front lines, exposed to the daily risks of active trading. A time-tested security strategy is to split your funds between a "hot" wallet for daily use and a "cold" wallet for long-term storage.
Your hot wallet is your Coinbase Wallet mobile app, holding only what you need for immediate trading or DeFi activity. Your cold wallet is your hardware wallet, safely storing the rest of your assets for the long haul.
This strategy is all about damage control. If your hot wallet ever gets compromised, the attacker only makes off with your "spending money." Your real savings remain untouched and secure in offline cold storage.
Unlimited token approvals are a ticking time bomb. They're convenient, sure, but they grant smart contracts permanent permission to move your funds. It’s absolutely critical to manage these permissions proactively.
Cleaning up your approvals is like changing the locks on your digital doors. It ensures old, forgotten permissions can't be exploited down the line. For a more detailed guide on what to look for, our checklist for assessing wallet risks can help direct your review.
Finally, the best defense you have is your own diligence. Cultivating a habit of meticulously verifying everything before you click "approve" is your strongest shield against scams.
Recent data shows just how crucial this is. Coinbase Wallet is a self-custody solution, which is exactly what DeFi traders need—not even Coinbase can touch your funds. While the industry saw $2.17 billion stolen in 2023 hacks, personal wallet compromises made up 23.35% of those thefts. This underscores that user-side security is paramount.
Understanding how secure Coinbase Wallet is in absolute terms only tells part of the story. The more actionable question for any serious DeFi participant is how it compares to the other self-custody options available, and whether the security trade-offs of each option match the specific way you use crypto. Not every wallet is built for the same user, and choosing the wrong architecture for your activity level and risk profile creates security gaps that no amount of individual diligence can fully close.
The comparison across self-custody options breaks down across four meaningful dimensions: where private keys are stored, what attack surface each architecture exposes, how the wallet handles multi-chain and DeFi interactions, and what the recovery path looks like if something goes wrong. Coinbase Wallet performs differently on each dimension relative to its main alternatives, and understanding those differences determines whether it is the right primary wallet for your needs or whether it should serve as one layer within a broader multi-wallet architecture.
A hardware wallet like a Ledger or Trezor stores private keys on a dedicated physical device that never connects to the internet directly. This is structurally more secure than any software wallet for long-term storage of significant holdings, because the attack surface for remote exploitation is essentially zero. Malware on your computer or phone cannot reach keys that live on an air-gapped device that only signs transactions when physically connected and manually confirmed.
The trade-off is friction. Hardware wallets require a physical device to approve every transaction, which is appropriate and desirable for a cold storage vault but impractical for a trader executing multiple DeFi interactions per session. Coinbase Wallet's on-device key storage within the Secure Enclave is a meaningful security architecture, but it is connected to an internet-facing device, which means sophisticated malware capable of exploiting the operating system represents a theoretical attack vector that hardware wallets eliminate by design.
The practical resolution for most active traders is to use both: hardware wallet for long-term holdings and large capital reserves, Coinbase Wallet as the active trading interface funded with only the capital needed for current positions. This combination captures the security ceiling of cold storage where it matters most while preserving the speed and accessibility that DeFi participation requires.
The most common alternative to Coinbase Wallet among DeFi traders is MetaMask, which uses a similar browser extension and mobile app architecture. Both are non-custodial and store private keys locally with encryption. The meaningful security differences between them are narrow at the architecture level but more significant at the feature level.
Coinbase Wallet's transaction preview and simulation feature, which shows the expected outcome of a transaction before you confirm it, is one of the more practically valuable security features in any consumer-facing wallet. MetaMask has introduced similar functionality, but Coinbase Wallet's implementation is more consistently surfaced during the confirmation flow rather than requiring users to opt into a simulation. For traders who interact frequently with new or unfamiliar contracts, this difference in default behavior reduces the probability of accidentally approving a malicious transaction.
The more significant difference is that Coinbase Wallet is developed and maintained by a publicly regulated company with significant reputational stakes in the wallet's security record. This creates a meaningful organizational incentive for rapid vulnerability disclosure and patch deployment that smaller independent wallet teams may not match. For users who weight the ongoing security maintenance of the software heavily in their evaluation, this institutional backing represents a genuine advantage over community-developed alternatives.
Coinbase Wallet's multi-chain support covers Ethereum and EVM-compatible networks as well as Solana, which addresses the majority of active DeFi trading volume. For traders whose activity is concentrated on these chains, the wallet's architecture fits the use case well. The token approval alerts and DApp blocklist features that make Coinbase Wallet's security posture strong on Ethereum apply consistently across the supported chains, which means the security layer does not degrade as you move activity from mainnet to Layer 2 networks or to Solana.
The limitation worth noting is that Coinbase Wallet's security features are primarily designed for the chains it officially supports. Traders who regularly interact with newer or less established chains may find that the DApp blocklist coverage is thinner for those ecosystems, and transaction simulations may be less reliable for contract types that the simulation engine has less historical data on. In these cases, the user-side diligence practices described earlier in this guide become proportionally more important as the wallet's proactive protection layer becomes less comprehensive.
Security is typically discussed in terms of what can go wrong: how to prevent hacks, how to avoid scams, how to protect a seed phrase. This is the right frame for protecting existing assets. But for active traders, the security of a wallet is only meaningful in the context of how the wallet is being used, and how it is used determines whether security measures are sufficient or whether they are being systematically undermined by the nature of the activity.
The most common way that technically secure wallets get drained is not through software exploits but through the trading behavior of their owners. Interacting with unvetted contracts, chasing high-yield protocols without understanding their risk profile, and making impulsive decisions based on social media signals rather than on-chain data are behaviors that no wallet security feature can protect against. The security of your Coinbase Wallet in practice is therefore inseparable from the quality of the decisions you make about what to connect it to.
A practical discipline that many experienced DeFi traders adopt is maintaining a strict separation between the wallet used for research and exploration and the wallet used for meaningful capital deployment. The research wallet, typically funded with a small amount that represents an acceptable total loss, is used to interact with new protocols, test unfamiliar contract interfaces, and verify that a DApp behaves as described before any significant funds are committed. The execution wallet, which holds the capital you are actually trading with, never touches a protocol that has not been validated through the research wallet first.
This separation means that any malicious contract interaction, unexpected token approval, or phishing-adjacent connection event affects only the research wallet. The execution wallet's attack surface is limited to protocols with a demonstrated track record in your own testing, which is a meaningfully smaller and better-characterized risk universe than the full landscape of DeFi contracts available at any given time.
Coinbase Wallet's architecture supports this separation cleanly. You can manage multiple wallets within the same app interface, each with its own seed phrase, without needing separate devices or separate installations. The friction of switching between wallets is low enough that the discipline is practically sustainable rather than theoretical.
The final layer of a complete security and trading practice is using on-chain intelligence to inform which protocols and assets your execution wallet interacts with in the first place. A wallet that only touches assets and protocols that high-performing, experienced market participants are also using is exposed to a fundamentally different risk profile than one that chases every new launch based on social media attention.
High-performance wallets tracked through on-chain intelligence platforms have typically already conducted the due diligence that a retail trader would struggle to replicate independently. Their presence in a protocol's user base is not a guarantee of safety, but it is a meaningful signal that the protocol has been evaluated by participants with both the analytical capability and the financial incentive to identify serious risks before committing capital. Following their activity into established protocols rather than racing into unvetted new launches is one of the most practical ways to reduce the frequency of high-risk contract interactions that represent the primary user-side security threat to any self-custody wallet.
Jumping into self-custody can bring up some valid questions. It's totally normal. Getting clear on how everything works is the best way to feel confident about keeping your crypto safe.
Here are some straightforward answers to the questions we hear most often from users trying to get a handle on their wallet's security.
This is a big point of confusion, so let's clear it up. The simple answer is no, Coinbase cannot freeze, access, or move the funds in your Coinbase Wallet. This is true even if your account on the Coinbase.com exchange gets locked for some reason.
Think of them as two completely separate products, because that's what they are. Your Coinbase Wallet is non-custodial, which means the private keys—the actual ownership of your crypto—are stored right on your phone or device, not with Coinbase. This design choice gives you total control over your assets, completely independent of what happens with your exchange account.
Coinbase Wallet has an optional feature that lets you back up your encrypted recovery phrase to your personal iCloud or Google Drive. It’s convenient, for sure, but it's a feature that you need to think about carefully.
It's definitely safer than just saving your phrase in a plain text file on your computer, since it's encrypted with a password only you should know. However, it does open up an online attack vector that simply doesn't exist if you keep your backup completely offline. If a hacker managed to get into both your cloud account and figure out your backup password, your funds would be at risk.
The gold standard for security hasn't changed: write down your 12-word recovery phrase on paper and store it in multiple, secure, offline locations. This classic method completely removes online hackers from the equation.
Losing your phone when it has your wallet on it feels awful, but you need to act fast. Don't panic, but don't delay either.
Your one and only goal is to get control of your assets before anyone else can.
This last step is absolutely critical. It drains the wallet that was on your lost phone, making it completely useless. That way, even if someone eventually breaks through your phone's lock screen, they’ll find nothing but an empty wallet.
The Secure Enclave is a dedicated hardware security module built into modern Apple devices that operates as a completely isolated processor with its own encrypted memory, separate from the main application processor. When Coinbase Wallet generates your private keys, they are stored inside the Secure Enclave rather than in the device's general storage, which means that even if malware gains significant access to your phone's operating system, it cannot read or export the keys because the Secure Enclave enforces hardware-level access controls that the operating system itself cannot override. The keys never leave the Secure Enclave in unencrypted form. When a transaction needs to be signed, the signing operation happens inside the Secure Enclave and only the signed transaction output is returned to the application, not the key that was used to sign it. This architecture means that a remote attacker who fully compromises your phone's software environment still cannot steal your private keys, because the keys are in a hardware partition that software access cannot reach. The practical implication is that the most common category of mobile malware, which works by reading application data from device storage, is neutralized by this design. The threat vectors that the Secure Enclave does not protect against are physical device compromise by a sophisticated actor with hardware extraction capabilities, and the social engineering attacks that bypass key theft entirely by tricking you into authorizing transactions yourself.
The tension between security against digital theft and resilience against physical loss is the central challenge of recovery phrase management, and the optimal solution involves redundancy across physical media and locations rather than any single storage method. The most secure baseline is to write your 12-word phrase on paper in permanent ink, laminate it to protect against moisture and handling damage, and store it in a fireproof, waterproof safe at your primary residence. This provides strong protection against the most common physical threats. The vulnerability is that a single physical location can be compromised by a sufficiently severe event such as fire, flood, or forced access. The appropriate response to this vulnerability is a second physical backup stored in a geographically separate location — a trusted family member's secure location or a bank safe deposit box — rather than any form of digital backup, which reintroduces online attack vectors. For holdings above a threshold where you want even stronger physical durability, stamping your phrase onto a metal plate made of steel or titanium eliminates the fire and water vulnerability of paper entirely. The key principle across all of these approaches is that each additional backup location increases recovery resilience but also increases the number of physical points that must remain secure, so the number of backup locations should be proportional to the value being protected rather than maximized arbitrarily.
Yes, completely and indefinitely. This is one of the most important practical implications of the non-custodial architecture and one of the most misunderstood aspects of self-custody wallets. Your funds exist on the blockchain, not inside Coinbase's systems, and your private keys are stored on your device, not on Coinbase's servers. Coinbase's role is to provide the application interface that makes interacting with the blockchain accessible, but the underlying keys and the assets they control are independent of the company's continued operation. If Coinbase ceased to exist tomorrow, you would restore access to your funds by importing your 12-word recovery phrase into any compatible non-custodial wallet application. Because Coinbase Wallet uses the industry-standard BIP-39 seed phrase specification, your recovery phrase is compatible with a wide range of alternative wallets including MetaMask, Trust Wallet, and others. The recovery phrase is the portable, universal key to your assets, and as long as you have it stored safely, no business failure, regulatory action, or technical shutdown affecting Coinbase can prevent you from accessing what is yours. This is the foundational promise of self-custody, and it is precisely why maintaining a secure, accessible offline backup of your recovery phrase is the single most important security practice for any non-custodial wallet user.
Ready to turn on-chain data into actionable trading signals? Wallet Finder.ai helps you discover and mirror the strategies of top-performing crypto traders in real time. Start your free 7-day trial and trade smarter, not harder. https://www.walletfinder.ai