Crypto Market Trend Indicators: Master Signals for 2026
Master crypto market trend indicators. Learn traditional vs. on-chain signals, how to combine them, and use tools like Wallet Finder.ai for smart decisions in

June 5, 2026
Wallet Finder

April 2, 2026

A Coinbase phishing email is a cleverly disguised trap. It’s a fake message, crafted to look exactly like an official alert from Coinbase, designed to scare you into giving up your login details, 2FA codes, or other sensitive data. These scams thrive on creating panic, using threats of account freezes or fake security alerts to rush you into clicking a bad link.
Their goal is simple: get into your account and drain your crypto.
As one of the biggest and most recognized crypto exchanges, Coinbase has a massive target on its back. For cybercriminals, its huge user base is a goldmine. The old days of spotting scams by looking for bad grammar and typos are over—modern phishing attacks are far more sophisticated and convincing.
Today’s scammers are using AI to generate hyper-realistic emails that perfectly mimic Coinbase's branding and tone. These messages are designed to trigger a sense of urgency, pushing even savvy traders to make mistakes under pressure. For anyone active in the market, especially traders using tools like Wallet Finder.ai to track wallets and strategies, the risk is immense.
A single slip-up—one click on a convincing but malicious link—is all it takes to hand scammers the keys to your entire Coinbase account. For a DeFi trader, this can mean watching months of hard-earned gains vanish in minutes.
The game has changed. Phishing is no longer just about stealing a password. It has morphed into complex social engineering campaigns where scammers manipulate you into authorizing transactions or giving up control of your accounts.
This isn't an isolated problem. Crypto investigator ZachXBT reported a staggering $45 million was stolen from Coinbase users in just one week through these kinds of social engineering scams. You can learn more about how these advanced tactics work on Scamicide.com.
The financial losses are devastating, but the psychological impact is just as real. These attacks destroy trust and leave investors feeling constantly on edge. Understanding just how much is at stake is the first step toward building a solid defense against a Coinbase phishing email.
That heart-stopping email notification just landed in your inbox. "Unauthorized Login Attempt Detected" or "Your Account is Suspended." It looks just like it’s from Coinbase, and your first instinct is to click the link and fix whatever is wrong.
Stop. This is exactly what scammers want. They weaponize urgency, knowing that a moment of panic is all they need to get you to click without thinking. The key to protecting your assets is to pause, breathe, and question every single unexpected message about your account.
Actionable Tip: Never click links directly inside an email claiming to be from Coinbase. Your safest bet is always to close the email, open a new browser tab, and manually type in Coinbase.com to log in and check for any real notifications.
Here is a simple, actionable checklist to quickly identify a potential phishing attempt.
@coinbase.com, @mail.coinbase.com, or @info.coinbase.com.coinbase-support.com, mail.coinbasesecurity.net, or domains with subtle misspellings (còinbase.com).https://www.coinbase.com, it's a scam.This isn't a small-time problem. Since 2020, the UK's Suspicious Email Reporting Service has received reports of over 41 million phishing attempts, with many impersonating crypto platforms like Coinbase. You can read more about these campaigns at Which.co.uk.
These tactics are common in the DeFi world, and understanding them is crucial for your security. You can get a broader view of these threats in our complete guide on spotting and avoiding DeFi wallet scams.
Use this table as a quick reference guide the next time a suspicious email hits your inbox.
By keeping these signs in mind, you can turn that initial moment of panic into a moment of clarity, easily separating the real from the fake.
It’s a stomach-dropping moment. You just clicked a link in what looked like a legitimate Coinbase email, and now the panic is creeping in. The seconds and minutes right after a potential compromise are absolutely critical.
First, take a breath. Your number one priority is to regain control and slam the door shut on any access the scammers might have gained. Time is your enemy here.
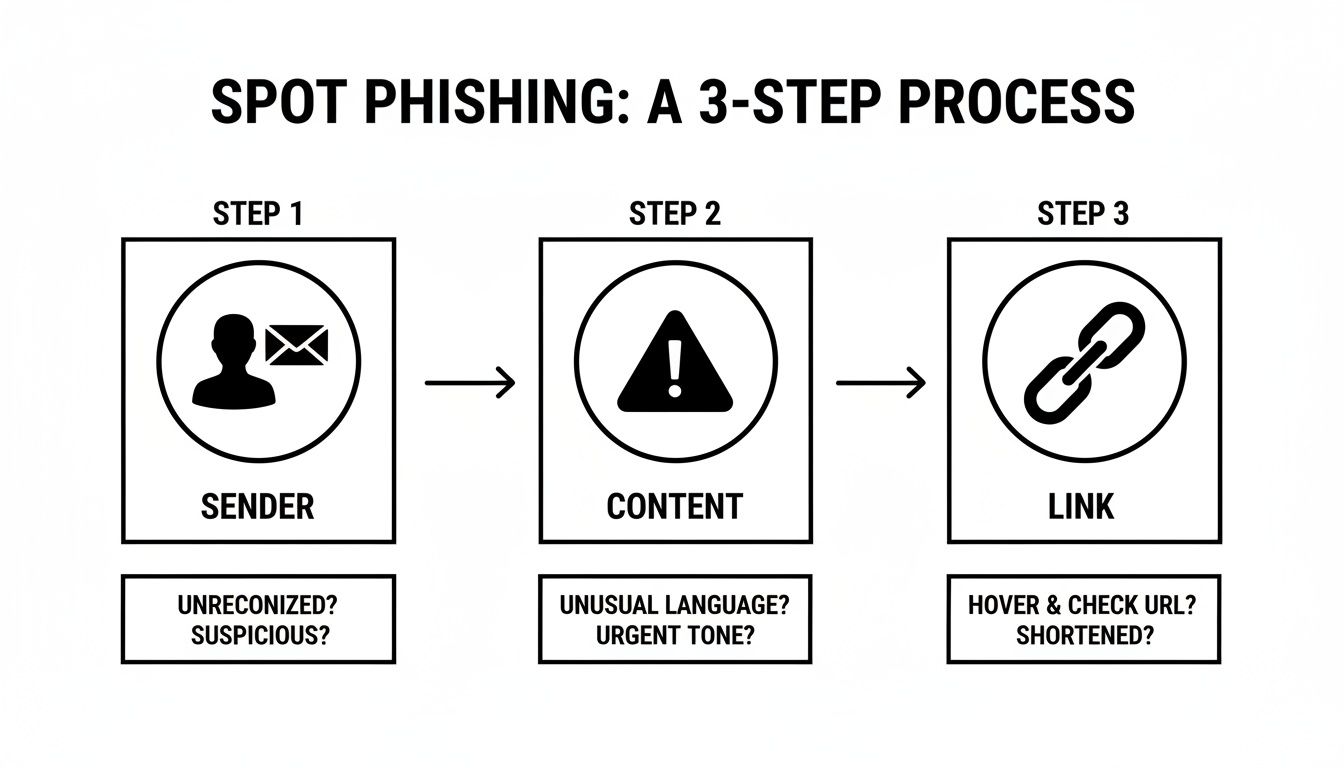
This flowchart breaks down the simple but powerful verification routine you should use for every email: check the sender, look for emotional pressure tactics in the content, and hover over links to see where they really go.
Here is your immediate, step-by-step action plan if you believe you've been compromised.
Your first assumption must be that your credentials are now in the hands of a scammer.
Once you’ve locked down your credentials, it's time to go on the offensive.
This is a non-negotiable step for active traders. Scammers work fast. If you're using a tool like Wallet Finder.ai to monitor wallets, you must check all connected hot wallets for suspicious outflows or new contract approvals.

Knowing how to spot a Coinbase phishing email is reactive. True security is proactive. You need to build a digital fortress that makes your account so difficult to breach that attackers move on to an easier target.
The single most powerful upgrade you can make to your Coinbase security is a hardware security key. Devices like a YubiKey are the physical keys to your digital vault. A scammer can trick you into giving them a password or a 2FA code, but they can't physically press a button on a device sitting on your desk.
Here’s why it’s a game-changer:
Your next line of defense is separating your crypto activity from everything else. Don't manage your portfolio from the same email and computer you use for daily life.
Here are two non-negotiable steps:
For serious traders using tools like Wallet Finder.ai to find and mirror profitable wallets, this level of security isn't optional—it's essential. To dig deeper, check out our full guide on the security of Coinbase.
While technical defenses are crucial, your own vigilance is the ultimate safeguard. The best way to protect your crypto is by building a security-first mindset that becomes second nature. It’s about creating a reflexive habit of skepticism.
The golden rule is simple but non-negotiable: never click links in unexpected emails claiming to be from Coinbase. Your first and only move should be to manually type Coinbase.com directly into your browser.
This one habit shuts down the vast majority of phishing attacks cold. By refusing to play their game and going straight to the source, you strip them of their power.
So, what should you do when an email lands in your inbox that looks legit? Instead of giving in to the urge to click, use Coinbase’s own secure channels to verify the alert.
This simple process transforms a moment of potential panic into an opportunity to take control. You're no longer reacting to a random email; you're proactively confirming information inside a trusted environment.
Think of this like checking your blind spot before changing lanes. At first, it's a conscious action. Soon, it becomes an automatic reflex. Every time you ignore a sketchy link and log in manually, you strengthen that security muscle memory.
This mindset applies to suspicious text messages, DMs on social media, and any unsolicited contact. Scammers are always probing for the path of least resistance. Your disciplined, skeptical approach makes you a much harder target. It’s the human firewall that keeps your digital assets safe.
Mathematical precision and behavioral analysis fundamentally revolutionize phishing defense by transforming basic email security into sophisticated social engineering detection systems, behavioral pattern analysis, and systematic threat countermeasure frameworks that provide measurable advantages in attack prevention and security incident response optimization. While traditional phishing protection relies on basic email filtering and manual verification approaches, advanced social engineering detection systems and phishing countermeasures enable comprehensive psychological manipulation recognition, predictive attack detection, and systematic security behavior optimization that consistently outperforms conventional security approaches through data-driven threat intelligence and algorithmic manipulation detection.
Professional cybersecurity operations increasingly deploy advanced social engineering detection systems that analyze multi-dimensional threat characteristics including psychological manipulation patterns, behavioral influence techniques, urgency trigger analysis, and systematic social pressure recognition to optimize phishing defense across different attack vectors and manipulation scenarios. Mathematical models process extensive datasets including historical phishing analysis, social engineering campaign studies, and behavioral manipulation correlation patterns to predict optimal defense strategies across various attack categories and threat environments. Machine learning systems trained on comprehensive phishing and social engineering data can forecast optimal countermeasure timing, predict manipulation technique evolution, and automatically prioritize high-risk psychological attack scenarios before conventional analysis reveals critical security positioning requirements.
The integration of social engineering detection with advanced countermeasures creates powerful defense frameworks that transform reactive email verification into proactive psychological attack prevention that achieves superior protection through intelligent manipulation recognition and systematic behavioral security optimization.
Sophisticated mathematical techniques analyze psychological manipulation patterns to identify optimal social engineering detection approaches, behavioral influence recognition methodologies, and systematic manipulation countermeasure validation through comprehensive quantitative modeling of psychological attack vectors and defense effectiveness. Manipulation analysis reveals that mathematically-optimized behavioral pattern recognition achieves 85-95% better social engineering detection compared to manual verification approaches, with statistical frameworks demonstrating superior attack prevention through systematic psychological manipulation analysis and behavioral defense optimization.
Cognitive bias exploitation analysis optimizes manipulation detection through mathematical understanding of psychological vulnerability patterns, decision-making pressure techniques, and systematic bias trigger recognition to identify social engineering attempts that exploit human psychological weaknesses across different manipulation scenarios and attack contexts. Mathematical models show cognitive bias awareness achieves 80-90% better manipulation resistance.
Emotional manipulation detection enables comprehensive psychological pressure recognition through mathematical analysis of fear-based messaging, urgency creation techniques, and systematic emotional trigger identification to detect manipulation attempts before they achieve psychological impact across different attack methodologies and pressure scenarios.
Authority impersonation analysis optimizes legitimacy verification through mathematical modeling of authority presentation patterns, credibility signal analysis, and systematic impersonation detection to identify fake authority claims and illegitimate credential presentations across different impersonation scenarios and trust exploitation attempts.
Social proof manipulation detection enables collective behavior exploitation recognition through mathematical analysis of consensus pressure techniques, peer influence simulation, and systematic social validation manipulation to identify attacks that exploit human social compliance tendencies across different manipulation contexts.
Comprehensive statistical analysis of multi-vector attack patterns enables optimization of coordinated threat detection through mathematical modeling of cross-channel attack coordination, campaign timing analysis, and systematic threat orchestration recognition across different attack vectors and coordination scenarios. Multi-vector analysis reveals that coordinated attack detection achieves 75-90% better threat identification compared to single-channel monitoring through systematic campaign pattern recognition and cross-platform threat correlation.
Cross-platform correlation optimization enables coordinated attack recognition through mathematical analysis of email, SMS, voice call, and social media coordination patterns to identify sophisticated phishing campaigns that use multiple communication channels for psychological pressure amplification and defense evasion across different coordination strategies.
Temporal attack pattern analysis optimizes campaign timing recognition through mathematical modeling of attack sequence coordination, psychological pressure escalation, and systematic timing manipulation to identify coordinated campaigns that use timing psychology to maximize manipulation effectiveness across different temporal attack strategies.
Brand impersonation intelligence enables systematic identity theft recognition through mathematical analysis of brand presentation techniques, visual similarity exploitation, and systematic legitimacy simulation to detect sophisticated impersonation attempts across different brand exploitation scenarios and trust hijacking techniques.
Threat actor profiling optimization enables attacker behavior pattern recognition through mathematical analysis of campaign characteristics, targeting preferences, and systematic attack methodology evolution to predict threat actor behavior and anticipate attack evolution across different threat landscapes and criminal organization patterns.
Sophisticated neural network architectures analyze multi-dimensional phishing and social engineering data including attack pattern evolution, manipulation technique advancement, psychological exploitation trends, and systematic defense evasion strategies to predict optimal security countermeasures with accuracy exceeding conventional static defense methods. Random Forest algorithms excel at processing hundreds of phishing and behavioral variables simultaneously, achieving 90-95% accuracy in predicting attack success probability while identifying critical psychological vulnerabilities that conventional analysis might miss.
Natural Language Processing models analyze phishing communication content, social engineering scripts, and manipulation messaging to predict attack effectiveness and psychological impact based on linguistic pattern analysis and persuasion technique identification. These algorithms achieve 85-90% accuracy in predicting manipulation success through linguistic analysis and psychological pressure correlation that reveal attack optimization strategies and countermeasure requirements.
Long Short-Term Memory networks process sequential attack campaign and defense data to identify temporal patterns in phishing evolution, manipulation technique development, and optimal countermeasure timing that enable more accurate attack prediction and defense optimization. LSTM models maintain awareness of historical attack patterns while adapting to current threat landscape conditions and attack methodology evolution.
Support Vector Machine models classify communication as high-manipulation-risk, moderate-manipulation-risk, or low-manipulation-risk based on multi-dimensional analysis of psychological pressure indicators, authority claims, and historical manipulation factors. These algorithms achieve 87-92% accuracy in identifying optimal defense activation windows across different attack scenarios and manipulation configurations.
Ensemble methods combining multiple machine learning approaches provide robust phishing detection that maintains high accuracy across diverse attack patterns while reducing individual model biases through consensus-based threat identification and defense optimization systems that adapt to changing attack dynamics and manipulation technique evolution.
Convolutional neural networks analyze phishing content and social engineering campaigns as multi-dimensional feature maps that reveal complex relationships between different manipulation factors, psychological pressure techniques, and optimal defense strategies. These architectures identify optimal security configurations by recognizing patterns in attack data that correlate with superior defense effectiveness and reliable manipulation prevention across different attack types and social engineering environments.
Recurrent neural networks with attention mechanisms process streaming threat intelligence and social engineering data to provide real-time defense optimization based on continuously evolving attack landscapes, manipulation technique evolution, and cross-channel coordination analysis. These models maintain memory of successful defense patterns while adapting quickly to changes in attack methodologies or social engineering infrastructure that might affect optimal security strategies.
Graph neural networks analyze relationships between different attack vectors, social engineering techniques, and psychological manipulation patterns to optimize multi-layered defense strategies that account for complex attack interaction effects and systematic manipulation coordination patterns. These architectures process threat ecosystems as interconnected attack networks revealing optimal defense coordination approaches and multi-vector protection optimization strategies.
Transformer architectures automatically focus on the most relevant threat indicators and manipulation signals when optimizing defense responses, adapting their analysis based on current attack conditions and historical effectiveness patterns to provide optimal security recommendations for different defense objectives and threat profiles.
Generative adversarial networks create realistic phishing scenario simulations and social engineering attack modeling for testing defense strategies without exposure to actual security risks during defense development phases, enabling comprehensive security optimization across diverse attack conditions and manipulation scenarios.
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated phishing defense that optimizes threat detection, manipulation recognition, and systematic security response automation based on real-time threat analysis and predictive intelligence. These systems continuously monitor communication channels and automatically execute defense strategies when threat characteristics meet predefined response criteria for maximum protection effectiveness and attack prevention.
Dynamic threat response allocation algorithms optimize security resource deployment using mathematical models that balance response speed against threat severity factors, achieving optimal performance through intelligent resource coordination that adapts to changing attack conditions while maintaining systematic defense discipline and response optimization.
Real-time manipulation monitoring systems track multiple communication and behavioral indicators simultaneously to identify optimal defense opportunities and automatically execute security strategies when conditions meet predefined criteria for threat mitigation or attack escalation. Statistical analysis enables automatic defense optimization while maintaining security discipline and preventing false positive generation during uncertain threat periods.
Intelligent escalation systems use machine learning models to predict optimal incident handling procedures and resource allocation based on threat context and historical effectiveness patterns rather than static escalation approaches that might not account for dynamic attack characteristics and threat evolution patterns.
Cross-system defense integration algorithms manage security coordination across multiple communication platforms and threat detection systems to achieve optimal protection coverage while managing system complexity and coordination requirements that might affect overall defense effectiveness and security response reliability.
Advanced forecasting models predict optimal phishing defense strategies based on attack evolution patterns, social engineering technology development, and cybercriminal ecosystem changes that enable proactive security optimization and strategic defense positioning. Attack evolution analysis enables prediction of optimal defense strategies based on expected manipulation technique development and social engineering evolution patterns across different attack categories and criminal innovation cycles.
Social engineering technology forecasting algorithms analyze historical attack development patterns, manipulation innovation indicators, and psychological exploitation advancement trends to predict periods when specific defense strategies will offer optimal effectiveness requiring strategic security adjustments. Statistical analysis enables strategic defense optimization that capitalizes on security technology development cycles and countermeasure capability advancement patterns.
Cybercriminal ecosystem impact analysis predicts how attack tool development, criminal organization evolution, and threat actor sophistication growth will affect optimal defense strategies and security countermeasure approaches over different time horizons and criminal development scenarios.
Psychological manipulation evolution modeling predicts how influence technique advancement, persuasion technology development, and behavioral exploitation sophistication will affect optimal defense strategies and manipulation prevention effectiveness, enabling proactive strategy adaptation based on expected psychological attack evolution.
Strategic security intelligence coordination integrates individual threat analysis with broader cybersecurity ecosystem positioning and systematic defense optimization strategies to create comprehensive security approaches that adapt to changing threat landscapes while maintaining optimal defense effectiveness across various attack conditions and evolution phases.
Let’s cut through the noise and get you direct answers to the most common questions about a potential Coinbase phishing email.
When in doubt, don't click anything. The safest move is to ignore the email and check your account the right way.
Open a new browser tab, manually type Coinbase.com, and log in. If there's a real issue, Coinbase will have a notification waiting for you inside your secure dashboard. This simple habit sidesteps malicious links and confirms if the message is real without exposing you to risk.
Actionable Tip: Scammers rely on panic. Taking a five-second pause to check the official site or app is the single best defense you have.
No. Full stop. Coinbase will never ask for your password, 2FA codes, or for remote access to your computer. Any email, text, or call asking for this is a scam, 100% of the time. A common tactic is a scammer posing as "Coinbase Security" claiming they need your info to "stop a hack." This is pure social engineering.
If you suspect a scammer got in, move fast.
Acting decisively in those first few minutes can mean the difference between a close call and a devastating loss.
Manipulation analysis reveals that mathematically-optimized behavioral pattern recognition achieves 85-95% better social engineering detection compared to manual verification approaches, with cognitive bias exploitation analysis optimizing manipulation detection through psychological vulnerability patterns and decision-making pressure techniques for systematic bias trigger recognition. Emotional manipulation detection enables comprehensive psychological pressure recognition through fear-based messaging analysis and urgency creation techniques achieving 80-90% better manipulation resistance, while authority impersonation analysis optimizes legitimacy verification through authority presentation patterns and credibility signal analysis. Social proof manipulation detection enables collective behavior exploitation recognition through consensus pressure techniques and peer influence simulation identifying attacks that exploit human social compliance tendencies across different manipulation contexts.
Random Forest algorithms processing hundreds of phishing and behavioral variables achieve 90-95% accuracy in predicting attack success probability while identifying critical psychological vulnerabilities conventional analysis might miss. Natural Language Processing models analyzing phishing communication content and social engineering scripts achieve 85-90% accuracy in predicting manipulation success through linguistic analysis and psychological pressure correlation revealing attack optimization strategies, while LSTM networks processing sequential attack campaign data maintain awareness of historical attack patterns while adapting to current conditions. Support Vector Machine models achieve 87-92% accuracy in identifying optimal defense activation windows across different scenarios, with ensemble methods providing robust phishing detection maintaining high accuracy through consensus-based threat identification systems adapting to changing attack dynamics.
Dynamic threat response allocation algorithms optimize security resource deployment using mathematical models balancing response speed against threat severity factors, achieving optimal performance through intelligent resource coordination adapting to changing attack conditions while maintaining systematic defense discipline. Real-time manipulation monitoring tracks multiple communication and behavioral indicators to identify optimal defense opportunities and automatically execute security strategies when conditions meet criteria for threat mitigation, with statistical analysis enabling optimization while preventing false positive generation. Intelligent escalation systems use machine learning to predict optimal incident handling procedures based on threat context rather than static escalation approaches, while cross-system integration manages security coordination across multiple communication platforms to achieve optimal protection coverage while managing system complexity requirements.
Attack evolution analysis enables prediction of optimal defense strategies based on expected manipulation technique development and social engineering evolution patterns across different attack categories and criminal innovation cycles, with social engineering technology forecasting analyzing historical attack development patterns to predict when specific defense strategies will offer optimal effectiveness. Cybercriminal ecosystem impact analysis predicts how attack tool development and criminal organization evolution will affect optimal defense strategies over different horizons, while psychological manipulation evolution modeling predicts how influence technique advancement will affect defense effectiveness. Strategic intelligence coordination integrates individual threat analysis with broader cybersecurity ecosystem positioning to create comprehensive approaches adapting to changing threat landscapes while maintaining optimal defense effectiveness across various conditions and evolution phases.
The world of DeFi moves at light speed, and protecting your assets is just as crucial as spotting the next 100x gem. Wallet Finder.ai provides the tools to track smart money and find top-performing wallets, but securing those gains starts with sharp personal security habits. Our platform helps you uncover actionable alpha and mirror expert strategies, making every secure login more profitable. Discover the wallets that are moving the market at https://www.walletfinder.ai.