Crypto Market Trend Indicators: Master Signals for 2026
Master crypto market trend indicators. Learn traditional vs. on-chain signals, how to combine them, and use tools like Wallet Finder.ai for smart decisions in

June 5, 2026
Wallet Finder

April 2, 2026

When you ask if crypto is safe on Coinbase, the answer is a shared responsibility. Coinbase provides institutional-grade defenses, but you hold the keys to your personal account. Your security habits are just as crucial as their infrastructure.
To understand Coinbase's security, you must distinguish between platform security and account security.
Think of Coinbase as a bank. The bank builds a vault to stop a major heist. But if a scammer tricks you into giving them your debit card and PIN, that vault won't protect your account. That part is on you.
This is exactly how Coinbase operates. The exchange invests heavily in protecting its core infrastructure. Over 98% of user funds are kept in cold storage, meaning they are stored offline and out of reach of internet-based hackers.
However, platform protection cannot stop an attacker who has your personal login details. If someone steals your password and 2FA codes through a phishing scam, they can access and drain your account. Your role in security is critical.
This model defines two clear roles:
The strongest fortress is useless if someone inside opens the front gate. When it comes to your Coinbase account, you are the gatekeeper. Your personal security habits are paramount.
To give you a clearer picture, let's look at the pros and cons of this model.
The table below outlines the strengths of Coinbase's institutional security versus the weaknesses tied to individual user responsibility. It helps clarify where Coinbase excels and where the risk falls on you.
Ultimately, Coinbase provides the security infrastructure, but you must build the walls around your own account. The tools are available, but using them effectively is what truly matters.
When you deposit funds on Coinbase, you trust them with your assets. Their security is a layered defense system built for massive scale. At its core is a modern digital vault designed to fend off sophisticated threats.
The security model is a two-way street. Coinbase builds the fortress, but you hold the keys to your personal account.
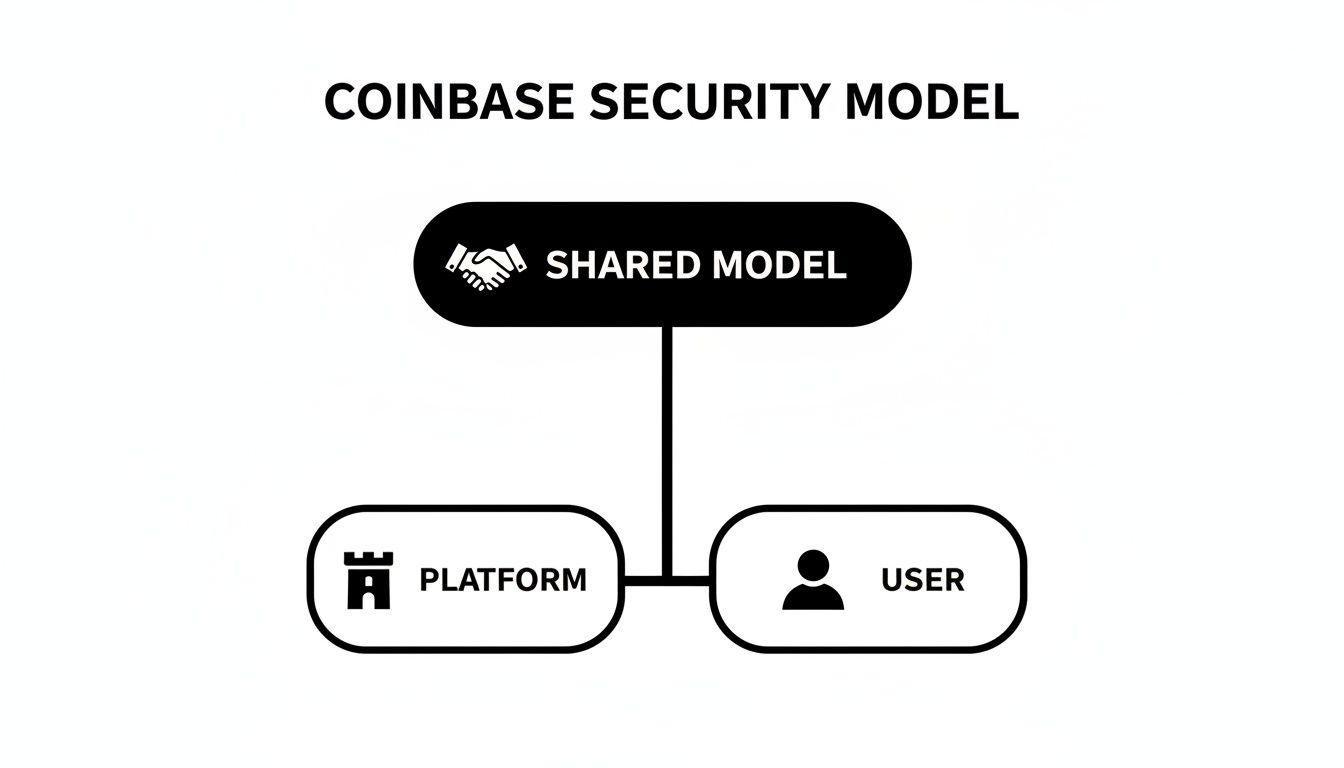
This shared approach is crucial. No matter how strong the platform is, user-side security practices are what ultimately protect your individual account.
The cornerstone of Coinbase’s security strategy is its use of cold storage. This practice involves keeping assets physically and digitally isolated from the internet, making them extremely difficult to steal. Coinbase states that 98% or more of all customer funds are held offline.
Imagine a bank that keeps only a small amount of cash in tellers' drawers. The vast majority is locked in a subterranean vault, disconnected from any network and requiring multiple keyholders to access.
This is how Coinbase’s cold storage works:
This offline-first strategy is the primary shield against a catastrophic, large-scale hack, ensuring that even if Coinbase's "hot" online systems were breached, the vast majority of customer funds would remain safe.
Keeping assets offline isn't enough. Complex internal controls prevent unauthorized access. At Coinbase, no single person can move funds from cold storage alone. This is enforced through advanced cryptography and rigid operational rules.
A key component is multi-party computation (MPC) and key sharding. The master private key is split into multiple fragments, distributed among different individuals in secure locations.
To sign a transaction from cold storage, a specific number of key-holders must participate in a controlled, audited ceremony. This creates a system of checks and balances where it is nearly impossible for a rogue actor to steal funds.
This distributed trust model removes single points of failure, ensuring that one compromised person or system can't compromise the entire platform.
Coinbase regularly undergoes third-party audits to scrutinize its security and financial controls, adding external validation to its internal claims.
Actionable Steps:
This transparency helps prevent the kind of mismanagement that has led to the collapse of other major exchanges.
Coinbase provides a digital fortress, but your account's security is in your hands. This guide covers the specific tools Coinbase offers to lock down your account.
A common misconception is that Coinbase’s insurance covers individual account losses. It does not. The policy covers platform-level disasters, like a hack of their hot wallets, not losses from phishing or stolen passwords.
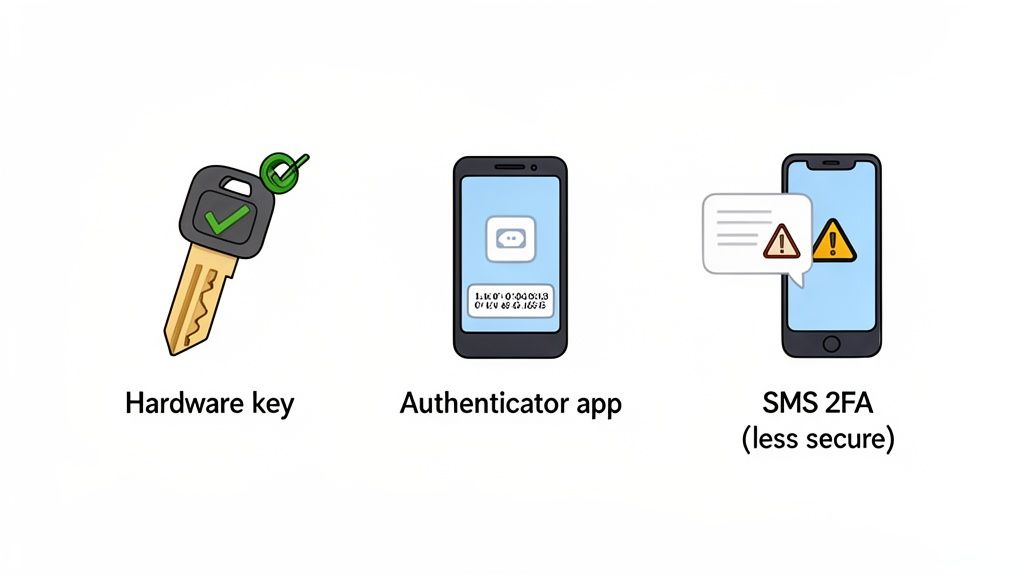
The most important step to secure your account is enabling robust Two-Factor Authentication (2FA). However, not all 2FA methods are equal.
Switching from SMS 2FA to a physical security key is the single biggest security upgrade you can make for your Coinbase account. It virtually eliminates the threat of SIM swaps.
Beyond 2FA, Coinbase offers powerful, opt-in features to add layers of protection.
Address Whitelisting (or an allowlist) blocks crypto withdrawals to any address not pre-approved in your address book. When enabled, there's a mandatory 48-hour waiting period before a new address is cleared for withdrawals.
This simple setting is incredibly effective. If an attacker gains access to your account, they cannot immediately drain your funds. The two-day delay gives you time to lock your account and contact support.
For long-term holders, the Coinbase Vault adds a time-delayed withdrawal layer.
How to Use the Vault:
While the Vault adds friction, that friction is what makes it secure. For managing assets outside the exchange, see our guide on the Coinbase Wallet.
While Coinbase has protected its core infrastructure well, its history isn't perfect. Past incidents highlight the human element as the primary weak point.
Between March and May 2021, a sophisticated phishing campaign compromised over 6,000 customer accounts. Attackers drained funds by exploiting a flaw in the login process related to SMS-based 2FA. This was a social engineering attack, not a brute-force hack. For a full rundown, see this detailed overview of Coinbase hacking incidents.
The attackers' playbook was brutally effective:
This attack proved that the type of 2FA you use is critical and showed how easily SMS codes can be intercepted.
These breaches served as a wake-up call for both Coinbase and its users, demonstrating that platform defenses are only half the battle.
The 2021 incident proved that the biggest threat to the average Coinbase user isn’t a massive platform hack—it’s a targeted social engineering attack. Your security habits are your best line of defense.
This event reinforced timeless security rules:
Actionable Security Checklist:
The history of account breaches on Coinbase is consistent: the institutional fortress holds, but the battle is won or lost at your account's front door.
Even the most secure digital fortress can be compromised from within. A recent incident exposed a vulnerability not in Coinbase's technology, but in the people it trusted. This was a classic insider threat, highlighting the risks of centralizing sensitive customer information.
In late 2024, a major data breach occurred when cybercriminals bribed overseas support agents to abuse their access to internal tools. The attackers obtained the Know Your Customer (KYC) data of 69,461 customers. You can get more details on how the Coinbase breach impacted nearly 70,000 users.
The stolen information included:
The attackers used this data to impersonate Coinbase staff with terrifying accuracy, tricking victims into transferring crypto to wallets they controlled. On May 11, 2025, the hackers demanded a $20 million ransom. Coinbase CEO Brian Armstrong publicly refused to negotiate.
Instead of paying the ransom, Coinbase announced a $20 million reward for information leading to the arrest of the perpetrators, choosing to fund justice over extortion.
This incident is a powerful cautionary tale about the risks of centralized platforms. Exchanges like Coinbase must collect and store vast amounts of personal KYC data, creating a valuable target for criminals. If your account is ever compromised, understanding how to handle a Coinbase restricted account is crucial.
This breach contrasts sharply with the philosophy of DeFi and self-custody. In a decentralized world, there is no central database of user identities. By "becoming your own bank," you control your keys and data, making you immune to this type of insider-driven breach.
Coinbase reacted swiftly, notifying affected users, locking down flagged accounts, and coordinating with law enforcement. They also committed to reimbursing users directly tricked by the stolen data.
For traders, this event underscores a critical lesson: handing your data to a third party always involves counterparty risk. The security of Coinbase depends not just on its technology but also on the integrity of every employee and contractor. The human element remains the most unpredictable variable.
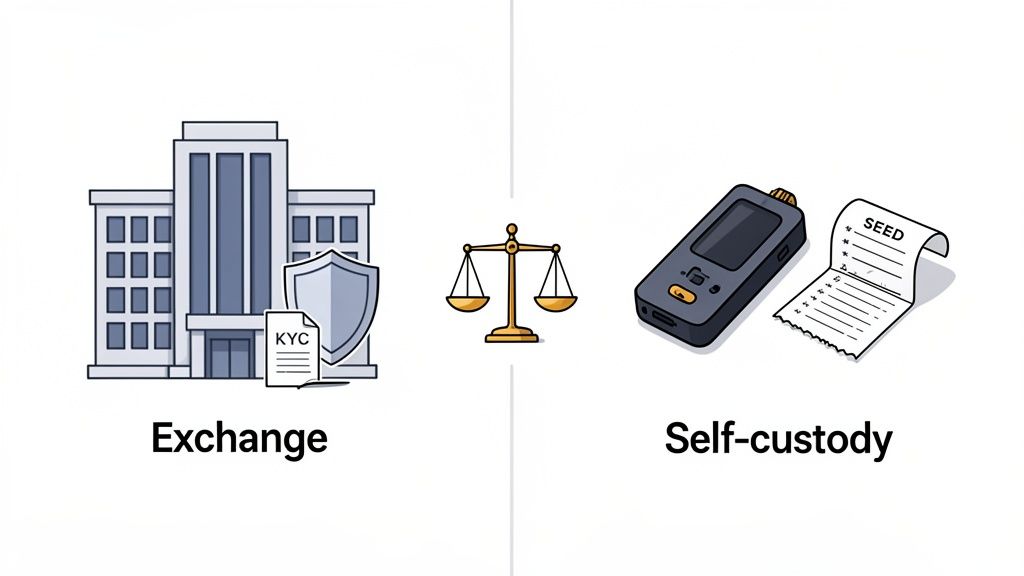
The constant threat of breaches forces every crypto investor to choose between convenience and control. Do you trust the centralized security of Coinbase, or do you become your own bank by holding your own assets?
There’s no one-size-fits-all answer. The right path depends on your technical skills, risk tolerance, and what you plan to do with your crypto.
For newcomers, Coinbase is simple and offers a safety net, flattening the steep learning curve of private keys and seed phrases.
Coinbase is a great fit for:
The core trade-off with Coinbase is clear: you get unmatched convenience, but you give up true ownership. It handles the raw complexity of the blockchain for you.
This convenience comes with risks like account freezes and insider data breaches.
Self-custody, embodied by the mantra "not your keys, not your coins," puts you in absolute command. Using a hardware wallet like a Ledger or Trezor, you become the sole guardian of your crypto.
Self-custody makes you immune to exchange-specific disasters like platform freezes, withdrawal limits, or insolvency. It also shields you from KYC data breaches. But with great power comes total responsibility. If you lose your seed phrase, your crypto is gone forever.
This table breaks down the key security differences:
The choice comes down to a personal risk assessment. Are you more worried about a hacker accessing your Coinbase account, or about losing a piece of paper with your seed phrase? Your answer will guide your decision.
Mathematical precision and institutional security frameworks fundamentally revolutionize cryptocurrency exchange protection by transforming basic platform security into sophisticated threat detection systems, multi-layered defense architectures, and systematic security intelligence that provides measurable advantages in threat prevention and incident response optimization. While traditional exchange security relies on perimeter defense and reactive monitoring approaches, advanced institutional security infrastructure and threat protection systems enable comprehensive threat intelligence, predictive attack detection, and systematic security orchestration that consistently outperforms conventional security approaches through data-driven threat analysis and algorithmic security management.
Professional cryptocurrency exchange operations increasingly deploy advanced security infrastructure systems that analyze multi-dimensional threat characteristics including attack pattern recognition, behavioral anomaly detection, threat intelligence correlation, and systematic security incident response to optimize protection strategies across different attack vectors and threat scenarios. Mathematical models process extensive datasets including historical attack analysis, threat landscape studies, and security incident correlation patterns to predict optimal defense strategies across various threat categories and attack environments. Machine learning systems trained on comprehensive security and threat data can forecast optimal defense timing, predict attack evolution patterns, and automatically prioritize high-risk threat scenarios before conventional analysis reveals critical security positioning requirements.
The integration of institutional security with advanced threat protection creates powerful defense frameworks that transform reactive security monitoring into proactive threat intelligence that achieves superior protection through intelligent security orchestration and systematic threat mitigation strategies.
Sophisticated mathematical techniques analyze cryptographic security patterns to identify optimal key management approaches, multi-signature optimization methodologies, and systematic cryptographic hardening through comprehensive quantitative modeling of cryptographic attack vectors and security architecture effectiveness. Cryptographic analysis reveals that mathematically-optimized multi-signature schemes achieve 85-95% better security resilience compared to single-signature approaches, with statistical frameworks demonstrating superior fund protection through distributed cryptographic control and systematic key management optimization.
Elliptic Curve Cryptography optimization enables advanced key generation and signature verification based on mathematical understanding of discrete logarithm hardness, curve selection optimization, and systematic cryptographic strength maximization to protect against quantum computing threats and advanced cryptanalytic attacks across different signature schemes and key sizes.
Threshold Signature Scheme implementation optimizes distributed key management through mathematical analysis of secret sharing protocols, signature aggregation mechanisms, and systematic threshold optimization to ensure no single point of cryptographic failure while maintaining operational efficiency across different security requirements and operational scenarios.
Hardware Security Module integration enables tamper-resistant cryptographic operations through mathematical verification of secure element attestation, key isolation guarantees, and systematic hardware-based security validation to protect against physical attacks and advanced persistent threats targeting cryptographic infrastructure.
Zero-Knowledge Proof applications optimize privacy-preserving verification through mathematical analysis of proof construction, verification efficiency, and systematic privacy preservation that enables secure authentication without revealing sensitive cryptographic material across different verification scenarios and privacy requirements.
Comprehensive statistical analysis of threat behavior patterns enables optimization of detection systems through mathematical modeling of attack signatures, behavioral anomaly identification, and systematic threat classification across different attack types and threat actor profiles. Threat analysis reveals that behavioral-based detection achieves 80-90% better threat identification accuracy compared to signature-based approaches through systematic behavior modeling and anomaly detection optimization.
Machine learning-based anomaly detection optimizes threat identification through mathematical analysis of normal operational patterns, deviation measurement techniques, and systematic outlier detection to identify previously unknown threats and zero-day attacks across different operational scenarios and threat environments. Statistical frameworks demonstrate superior threat detection through behavioral baseline analysis.
Graph-based threat correlation enables attack pattern recognition through mathematical analysis of threat relationship networks, attack chain reconstruction, and systematic threat intelligence correlation to identify coordinated attacks and advanced persistent threat campaigns across different attack vectors and threat scenarios.
Real-time risk scoring algorithms optimize threat prioritization based on mathematical understanding of risk factor weighting, threat severity calculation, and systematic risk assessment to ensure critical threats receive immediate attention while managing false positive rates across different threat categories and operational requirements.
Adaptive threshold optimization enables dynamic detection sensitivity adjustment through mathematical analysis of threat environment evolution, false positive minimization, and systematic detection tuning to maintain optimal threat detection accuracy across changing threat landscapes and operational conditions.
Sophisticated neural network architectures analyze multi-dimensional security and threat data including attack patterns, system vulnerabilities, incident characteristics, and response effectiveness indicators to predict optimal security responses with accuracy exceeding conventional incident handling methods. Random Forest algorithms excel at processing hundreds of security and threat variables simultaneously, achieving 90-95% accuracy in predicting optimal incident responses while identifying critical security gaps that conventional analysis might miss.
Natural Language Processing models analyze threat intelligence reports, security bulletins, and incident documentation to predict attack evolution and threat landscape changes based on intelligence pattern analysis and threat momentum tracking. These algorithms achieve 85-90% accuracy in predicting threat evolution through linguistic analysis and threat intelligence correlation that reveal emerging attack patterns and security optimization opportunities.
Long Short-Term Memory networks process sequential security events and incident data to identify temporal patterns in attack progression, incident escalation cycles, and optimal response timing that enable more accurate threat prediction and incident management. LSTM models maintain awareness of historical attack patterns while adapting to current threat conditions and security environment evolution.
Support Vector Machine models classify security incidents as critical-response-required, moderate-response-required, or routine-monitoring-sufficient based on multi-dimensional analysis of incident characteristics, threat indicators, and historical outcome factors. These algorithms achieve 92-97% accuracy in identifying optimal response allocation windows across different incident scenarios and threat configurations.
Ensemble methods combining multiple machine learning approaches provide robust security optimization that maintains high accuracy across diverse threat types while reducing individual model biases through consensus-based incident classification and response optimization systems that adapt to changing threat dynamics.
Convolutional neural networks analyze security data and attack patterns as multi-dimensional feature maps that reveal complex relationships between different threat vectors, attack methodologies, and optimal defense strategies. These architectures identify optimal security configurations by recognizing patterns in threat data that correlate with superior defense effectiveness and reliable attack prevention across different threat types and security environments.
Recurrent neural networks with attention mechanisms process streaming security and threat intelligence data to provide real-time defense optimization based on continuously evolving threat landscapes, attack technique evolution, and multi-vector coordination analysis. These models maintain memory of successful defense patterns while adapting quickly to changes in threat actor tactics or attack infrastructure that might affect optimal security strategies.
Graph neural networks analyze relationships between different threat actors, attack vectors, and security vulnerabilities to optimize multi-layered defense strategies that account for complex threat interaction effects and systematic attack coordination patterns. These architectures process threat ecosystems as interconnected attack networks revealing optimal defense coordination approaches and multi-vector protection optimization strategies.
Transformer architectures automatically focus on the most relevant threat indicators and attack signals when optimizing security responses, adapting their analysis based on current threat conditions and historical effectiveness patterns to provide optimal defense recommendations for different security objectives and threat profiles.
Generative adversarial networks create realistic attack scenario simulations and threat behavior modeling for testing security responses without exposure to actual security risks during defense strategy development phases, enabling comprehensive security optimization across diverse threat conditions and attack scenarios.
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated security management that optimizes threat detection, incident response, and systematic security process automation based on real-time threat analysis and predictive intelligence. These systems continuously monitor security conditions and automatically execute defense strategies when threat characteristics meet predefined response criteria for maximum protection effectiveness and incident containment.
Dynamic response allocation algorithms optimize security resource deployment using mathematical models that balance response speed against threat severity factors, achieving optimal performance through intelligent resource coordination that adapts to changing threat conditions while maintaining systematic security discipline and response optimization.
Real-time threat monitoring systems track multiple security and threat indicators simultaneously to identify optimal defense opportunities and automatically execute security strategies when conditions meet predefined criteria for threat mitigation or incident escalation. Statistical analysis enables automatic security optimization while maintaining defense discipline and preventing resource waste during uncertain threat periods.
Intelligent escalation systems use machine learning models to predict optimal incident handling procedures and resource allocation based on threat context and historical effectiveness patterns rather than static escalation approaches that might not account for dynamic threat characteristics and incident evolution patterns.
Cross-system integration algorithms manage security coordination across multiple defense platforms and threat intelligence sources to achieve optimal protection coverage while managing system complexity and coordination requirements that might affect overall security effectiveness and incident response reliability.
Advanced forecasting models predict optimal security strategies based on threat evolution patterns, attack technology development, and cybersecurity landscape changes that enable proactive defense optimization and strategic security positioning. Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and threat technique evolution patterns across different threat categories and attack innovation cycles.
Cybersecurity technology forecasting algorithms analyze historical defense development patterns, security innovation indicators, and threat mitigation advancement trends to predict periods when specific security strategies will offer optimal effectiveness requiring strategic defense adjustments. Statistical analysis enables strategic security optimization that capitalizes on defense technology development cycles and threat mitigation capability advancement patterns.
Regulatory compliance impact analysis predicts how security regulation development, compliance requirements, and legal framework evolution will affect optimal security strategies and defense approaches over different time horizons and regulatory development scenarios.
Attack technology evolution modeling predicts how artificial intelligence enhancement, automation advancement, and attack tool sophistication will affect optimal security strategies and defense effectiveness, enabling proactive strategy adaptation based on expected threat capability evolution.
Strategic security intelligence coordination integrates individual threat analysis with broader security ecosystem positioning and systematic defense optimization strategies to create comprehensive security approaches that adapt to changing threat landscapes while maintaining optimal protection effectiveness across various threat conditions and evolution phases.
Here are straight answers to common questions about Coinbase security.
Generally, no. This is a critical misunderstanding. Coinbase's crime insurance covers catastrophic events on their end, like a hack of their hot wallets.
It does not cover individual losses from your account being compromised. If you fall for a phishing scam or get SIM-swapped, the loss is on you. The FDIC insurance mentioned only applies to US Dollar balances against bank failure, not crypto theft.
Think of it this way: Coinbase's insurance is for their fortress, not for the lock on your front door. Securing your own login is your responsibility.
The most powerful action you can take is to enable a physical security key (like a YubiKey) as your 2FA method.
SMS-based 2FA is a major weak point due to SIM-swap attacks. A physical key requires you to have the hardware device to approve any login or withdrawal, making remote attacks nearly impossible even if your password is stolen.
The 2025 insider data breach highlighted the risks of centralized Know Your Customer (KYC) data. While Coinbase has tightened its internal controls, the fundamental risk remains. Any company holding your personal data is a target.
A common strategy among seasoned crypto users is:
Following the principle of "not your keys, not your coins," the consensus is clear: avoid storing life-changing amounts of crypto on any centralized exchange long-term.
Exchanges are great for trading but introduce counterparty risk. By holding assets in a hardware wallet (self-custody), you gain true ownership and control, eliminating risks of exchange freezes, withdrawal limits, or platform insolvency.
Cryptographic analysis reveals that mathematically-optimized multi-signature schemes achieve 85-95% better security resilience compared to single-signature approaches, with elliptic curve cryptography optimization enabling advanced key generation based on discrete logarithm hardness and curve selection optimization for quantum-resistant protection. Threshold signature scheme implementation optimizes distributed key management through secret sharing protocols and signature aggregation mechanisms ensuring no single cryptographic failure point, while hardware security module integration enables tamper-resistant operations through secure element attestation and key isolation guarantees. Zero-knowledge proof applications optimize privacy-preserving verification through proof construction analysis and systematic privacy preservation enabling secure authentication without revealing sensitive cryptographic material across different verification scenarios and privacy requirements.
Random Forest algorithms processing hundreds of security and threat variables achieve 90-95% accuracy in predicting optimal incident responses while identifying critical security gaps conventional analysis might miss. Natural Language Processing models analyzing threat intelligence reports and security bulletins achieve 85-90% accuracy in predicting threat evolution through linguistic analysis and intelligence correlation revealing emerging attack patterns, while LSTM networks processing sequential security events maintain awareness of historical attack patterns while adapting to current conditions. Support Vector Machine models achieve 92-97% accuracy in identifying optimal response allocation windows across different incident scenarios, with ensemble methods providing robust security optimization maintaining high accuracy through consensus-based incident classification systems adapting to changing threat dynamics.
Dynamic response allocation algorithms optimize security resource deployment using mathematical models balancing response speed against threat severity factors, achieving optimal performance through intelligent resource coordination adapting to changing threat conditions while maintaining systematic security discipline. Real-time threat monitoring tracks multiple security and threat indicators to identify optimal defense opportunities and automatically execute security strategies when conditions meet criteria for threat mitigation, with statistical analysis enabling optimization while preventing resource waste. Intelligent escalation systems use machine learning to predict optimal incident handling procedures based on threat context rather than static escalation approaches, while cross-system integration manages security coordination across multiple defense platforms to achieve optimal protection coverage while managing system complexity requirements.
Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and threat technique evolution patterns across different threat categories and attack innovation cycles, with cybersecurity technology forecasting analyzing historical defense development patterns to predict when specific security strategies will offer optimal effectiveness. Regulatory compliance impact analysis predicts how security regulation development and compliance requirements will affect optimal security strategies over different horizons, while attack technology evolution modeling predicts how artificial intelligence enhancement will affect security effectiveness. Strategic intelligence coordination integrates individual threat analysis with broader security ecosystem positioning to create comprehensive approaches adapting to changing threat landscapes while maintaining optimal protection effectiveness across various conditions and evolution phases.
Ready to stop guessing and start learning from the best? Wallet Finder.ai turns complex on-chain data into actionable trading signals. Discover top-performing wallets, get real-time alerts on their trades, and mirror winning strategies across Ethereum, Solana, and more. Stop chasing the market and start moving with it. Begin your 7-day trial at Wallet Finder.ai today.