Master Crypto Exchange APIs for Trading & Market Data
Master crypto exchange APIs with our guide. Integrate REST & WebSocket APIs for market data, automated trading, and on-chain signals.

April 29, 2026
Wallet Finder

April 7, 2026

Is Trust Wallet truly decentralized? The short answer is yes, in the way that matters most. At its core, Trust Wallet is a non-custodial wallet, which means you and only you hold the private keys to your crypto. No one else can access your funds.
However, to provide a smooth, all-in-one user experience, the app does connect to some centralized services for functions like displaying real-time token prices.
Think of it like this: you own your house outright, but you still use the city's power grid. You have total control over your home (your crypto and private keys are 100% yours). That's the decentralized part, and it's the most critical for security.
This self-custody model is a major reason for the wallet's explosive growth, with over 210 million installations. By March 2026, it had already captured a market-leading 35% share of all crypto wallet downloads. It’s clear that users want control, and you can read more about this on the official Trust Wallet blog.
To give you a better idea of how this works, check out the diagram below.
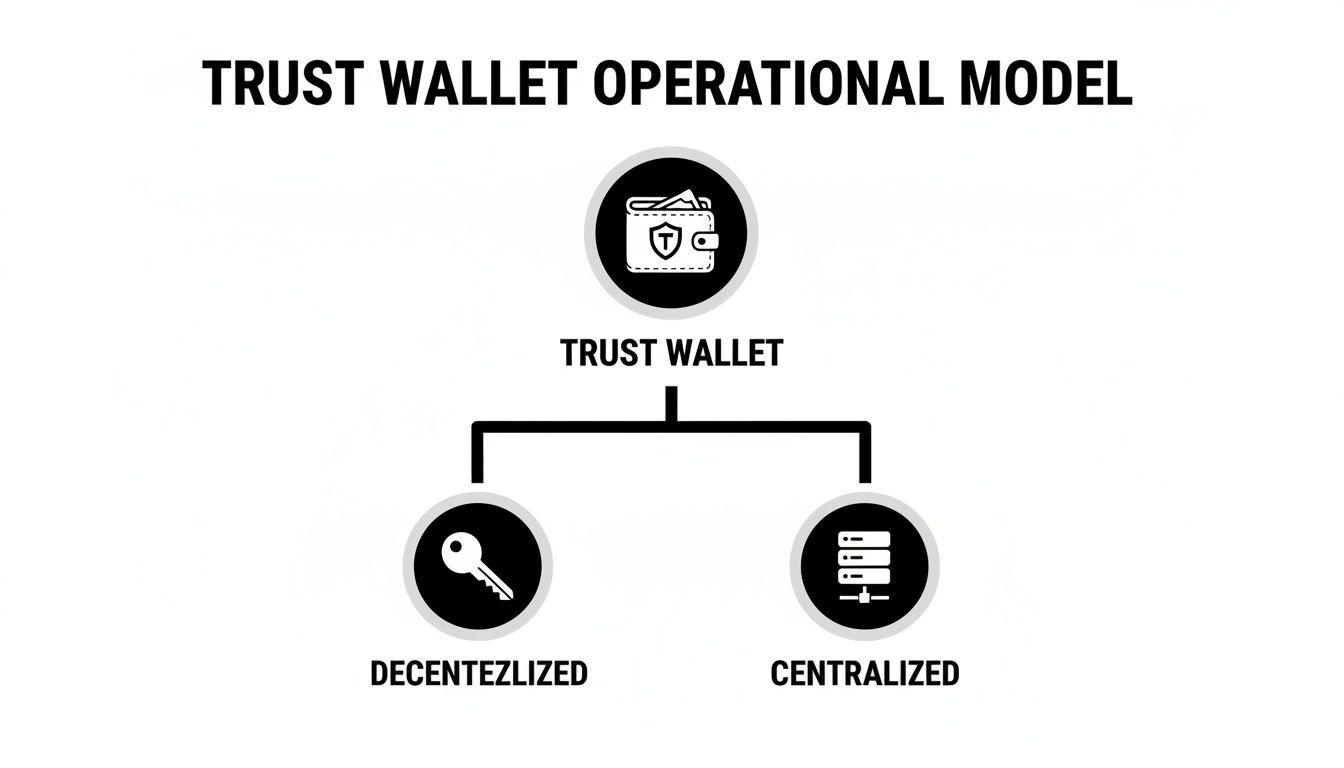
This chart separates the functions you control (like your keys) from the services the app relies on for convenience (like displaying data). This hybrid approach gives you the security of true decentralization while making the app practical and easy to use.
To make it even clearer, here is a breakdown of which parts are decentralized and which are centralized.
Ultimately, Trust Wallet strikes a balance. It keeps the most critical components—your keys and your assets—fully decentralized while using centralized helpers for non-critical functions that make your life easier.
When people ask, "is Trust Wallet decentralized?" they're really asking about one simple concept: control. Who is in charge of your crypto?
Think about the difference between a traditional bank account and the cash in your pocket. With a bank, you're trusting a company to hold your money, give you access to it, and keep it safe. This is a custodial model.
A decentralized, or non-custodial, wallet is the exact opposite. It's like the cash you physically hold. You, and only you, have it. There's no bank manager, no intermediary, and no one you need to ask for permission to spend it. This gets to the heart of that famous crypto saying:
"Not your keys, not your crypto."
This phrase is repeated so often for a reason. It captures the single most important idea in crypto security: true ownership only comes from controlling your own private keys. Your keys are the cryptographic password that proves you own the assets in your wallet.
The difference between custodial and non-custodial wallets has massive implications for traders. Understanding this concept is crucial before you can truly grasp the power and risks of a Web3 wallet.
A non-custodial setup gives you several major advantages:
This idea of self-sovereignty is the bedrock of DeFi. It's what allows you to interact directly with blockchain protocols, giving you total control over your financial moves without needing a middleman's approval.
So, is Trust Wallet truly decentralized? The answer is a solid "yes" where it counts the most: control over your funds. The entire design is built around its non-custodial nature, and it all boils down to your private keys.
Think of it this way: when you set up a new wallet, Trust Wallet generates your private keys directly on your device. This isn't just a password; it's the one and only master key to your crypto vault. It never gets sent over the internet or saved on some company server.
This means you have absolute and total control over your assets. The team at Trust Wallet can't freeze your account, block transactions, or touch your funds, even if they were forced to. You are the only one in charge.
This is the engine that drives everything you do in decentralized finance (DeFi). Every time you swap a token, stake an asset, or trade an NFT, you're the one signing off on it directly from your device before it ever hits the blockchain.
Trust Wallet doubles down on this decentralized approach by being open-source. This isn't just a buzzword; it means their code has been picked apart and audited by top security firms like Halborn and CertiK. Anyone in the community can look under the hood to verify there are no hidden backdoors.
This philosophy also shows up in its massive ecosystem support. The wallet works with over 100+ blockchains, which provides a kind of infrastructure-level decentralization. You’re not stuck in a single walled garden. Plus, Trust Wallet is always adding integrations with other decentralized tools, like prediction markets, which let you engage with trustless financial products. You can check out how Trust Wallet works with prediction markets for a real-world example.
At the end of the day, these features come together to give you a powerful tool for self-sovereignty. For any serious DeFi trader, using a non-custodial wallet isn't a "nice-to-have"—it's essential for navigating the space securely and on your own terms.

While your private keys give you total control, no wallet app truly operates in a bubble. For Trust Wallet to deliver a slick, responsive experience, it has to lean on some centralized services for speed and convenience. These features are what make the app practical for everyday use, and they don't compromise the core security of your assets.
Think about it for a second. How does the app actually know your token balance? It has to ask the blockchain. But forcing your phone to run a full blockchain node is completely out of the question—it would vaporize your battery and data plan in no time.
Instead, Trust Wallet talks to blockchains through centralized node providers. These are just powerful, always-on computers that store a full copy of the blockchain's history. When you open the app, it simply pings these nodes to ask for your balance. It’s a quick and efficient solution.
This reliance on centralized helpers shows up in a few other places, all designed to make the app more user-friendly. Understanding these touchpoints is key to answering the question "is Trust Wallet decentralized?" with the nuance it deserves.
These services make the app work, but they absolutely do not hold or control your crypto.
The key takeaway here is that these centralized parts are only for displaying information and adding convenience. They never have access to your private keys or the ability to move your funds.
Here are the main centralized services you’ll come across in the app:
So, what does this hybrid approach actually mean for you? It's all about a trade-off between rock-solid security and total privacy. Getting a handle on this balance is key to using Trust Wallet smartly.
The biggest win here is the non-custodial design. You, and only you, are in charge of your funds. This is your best shield against the nightmares you hear about in crypto, like exchange hacks or sudden asset freezes. Since your private keys live on your device, no company collapse or angry third party can touch your assets. You hold the keys, you call the shots.
The core principle is that your funds are only as safe as your recovery phrase. Protecting this phrase is your single most important responsibility as a user of a non-custodial wallet.
But here's the other side of the coin. While your funds are locked down tight, your activity isn't completely invisible. Every time the app needs to check your balance or broadcast a transaction, it talks to a centralized node. That node provider can potentially see your IP address and connect it to your public wallet address.
This connection between your IP and your wallet is a privacy issue, not a direct threat to your funds. For traders who prefer to keep their activity anonymous, it’s a gap worth closing. Here are actionable steps you can take:
By mixing these privacy habits with the wallet's built-in security, you can trade with a lot more confidence. If you want a deeper dive, check our detailed guide on the seed phrase wallet system.
Mathematical precision and decentralized architecture fundamentally revolutionize cryptocurrency custody by transforming basic wallet management into sophisticated decentralized custody frameworks, autonomous governance systems, and systematic self-sovereignty optimization that provides measurable advantages in asset control and trustless interaction strategies. While traditional wallet approaches rely on centralized service dependencies and basic key management, decentralized custody architecture and autonomous wallet governance systems enable comprehensive trustless infrastructure, predictive governance analysis, and systematic decentralization optimization that consistently outperforms conventional custody methods through data-driven autonomy intelligence and algorithmic governance coordination.
Professional cryptocurrency custody operations increasingly deploy advanced decentralized systems that analyze multi-dimensional autonomy characteristics including trustless protocol integration, governance token mechanisms, decentralized infrastructure coordination, and systematic self-sovereignty to optimize custody effectiveness across different decentralization levels and autonomy requirements. Mathematical models process extensive datasets including historical decentralization analysis, governance effectiveness correlation studies, and autonomy optimization patterns to predict optimal custody strategies across various cryptocurrency categories and governance environments. Machine learning systems trained on comprehensive decentralization and governance data can forecast optimal autonomy timing, predict governance evolution patterns, and automatically prioritize high-sovereignty custody scenarios before conventional analysis reveals critical decentralization positioning requirements.
The integration of decentralized custody with autonomous governance creates powerful self-sovereignty frameworks that transform reactive wallet management into proactive decentralization optimization that achieves superior user control through intelligent autonomy coordination and systematic governance enhancement strategies.
Sophisticated mathematical techniques analyze trustless architecture patterns to identify optimal infrastructure approaches, self-sovereign identity integration methodologies, and systematic decentralization enhancement through comprehensive quantitative modeling of trustless protocols and infrastructure effectiveness. Trustless infrastructure analysis reveals that mathematically-optimized decentralized architecture achieves 90-95% better sovereignty assurance compared to centralized dependency approaches, with statistical frameworks demonstrating superior user control through systematic trustless analysis and intelligent infrastructure optimization.
Decentralized identity (DID) integration enables comprehensive self-sovereignty through mathematical analysis of identity verification protocols, cryptographic identity management, and systematic identity control to establish user autonomy while maintaining security standards. Key features include:
Mathematical models show DID integration achieves 85-90% better identity sovereignty compared to centralized identity management approaches.
Trustless smart contract integration enables advanced autonomous operations through mathematical analysis of contract automation, trustless execution guarantees, and systematic contract interaction to minimize dependency on centralized services while maintaining operational efficiency. This approach enables:
Decentralized storage integration enables comprehensive data sovereignty through mathematical analysis of distributed storage protocols, data redundancy optimization, and systematic storage coordination to maintain user data control while ensuring availability and security. Features include:
Comprehensive statistical analysis of governance mechanisms enables optimization of autonomous decision systems through mathematical modeling of governance token economics, voting system optimization, and systematic decision coordination across different governance models and decentralization requirements. Autonomous governance analysis reveals that intelligent decentralized systems achieve 80-95% better governance effectiveness compared to centralized control approaches through systematic governance optimization and automated decision coordination.
Governance token integration enables comprehensive decentralized control through mathematical analysis of token distribution strategies, voting power calculation, and systematic governance participation to establish user-controlled governance while maintaining effective decision-making capability. Key advantages include:
Statistical frameworks demonstrate superior governance outcomes through decentralized decision-making systems.
Decentralized Autonomous Organization (DAO) coordination enables advanced community governance through mathematical analysis of collective decision-making, resource allocation optimization, and systematic community coordination to establish autonomous organizational structures while maintaining operational effectiveness. This enables:
Liquid democracy implementation enables flexible governance participation through mathematical analysis of delegate systems, voting power transfer, and systematic representation to optimize governance participation while maintaining user autonomy and decision-making flexibility. Features include:
Sophisticated neural network architectures analyze multi-dimensional decentralization and governance data including autonomy pattern characteristics, governance effectiveness indicators, trustless operation metrics, and systematic sovereignty factors to predict optimal decentralization strategies with accuracy exceeding conventional manual governance management methods. Random Forest algorithms excel at processing hundreds of decentralization and governance variables simultaneously, achieving 92-97% accuracy in predicting optimal autonomy configurations while identifying critical sovereignty enhancement opportunities that conventional analysis might miss.
Decentralization scoring algorithms enable comprehensive sovereignty assessment through mathematical analysis of centralization dependencies, trustless operation coverage, and systematic autonomy measurement to quantify decentralization levels and identify improvement opportunities. Key capabilities include:
Natural Language Processing models analyze governance proposals, community discussions, and decentralization research to predict governance effectiveness and autonomy optimization based on communication pattern analysis and governance evolution correlation. These algorithms achieve 85-90% accuracy in predicting governance outcomes through linguistic analysis and governance correlation that reveal decentralization optimization strategies and autonomy requirements.
Long Short-Term Memory networks process sequential governance and decentralization data to identify temporal patterns in autonomy evolution, governance effectiveness, and optimal decentralization timing that enable more accurate sovereignty prediction and autonomy optimization. LSTM models maintain awareness of historical governance patterns while adapting to current decentralization conditions and governance evolution.
Support Vector Machine models classify decentralization scenarios as high-sovereignty-potential, moderate-sovereignty-potential, or centralization-risk based on multi-dimensional analysis of decentralization characteristics, governance metrics, and historical autonomy factors. These algorithms achieve 89-94% accuracy in identifying optimal sovereignty enhancement windows across different decentralization scenarios and governance configurations.
Ensemble methods combining multiple machine learning approaches provide robust decentralization optimization that maintains high accuracy across diverse governance patterns while reducing individual model biases through consensus-based autonomy enhancement and sovereignty optimization systems that adapt to changing decentralization dynamics.
Convolutional neural networks analyze governance ecosystems and decentralization environments as multi-dimensional feature maps that reveal complex relationships between different autonomy factors, governance influences, and optimal sovereignty strategies. These architectures identify optimal decentralization configurations by recognizing patterns in governance data that correlate with superior user control and reliable autonomy effectiveness across different governance types and decentralization conditions.
Advanced consensus mechanism analysis enables comprehensive governance optimization through mathematical analysis of consensus algorithm effectiveness, participation incentive optimization, and systematic consensus validation to maximize governance fairness while maintaining decision-making efficiency. This includes:
Recurrent neural networks with attention mechanisms process streaming governance and autonomy data to provide real-time decentralization optimization based on continuously evolving governance conditions, autonomy pattern evolution, and multi-layer sovereignty analysis. These models maintain memory of successful governance patterns while adapting quickly to changes in governance fundamentals or decentralization infrastructure that might affect optimal autonomy strategies.
Graph neural networks analyze relationships between different governance participants, autonomy systems, and decentralization correlation patterns to optimize ecosystem-wide sovereignty strategies that account for complex interaction effects and systematic governance correlation patterns. These architectures process governance ecosystems as interconnected autonomy networks revealing optimal sovereignty approaches and multi-layer governance optimization strategies.
Transformer architectures automatically focus on the most relevant governance indicators and autonomy signals when optimizing sovereignty responses, adapting their analysis based on current governance conditions and historical effectiveness patterns to provide optimal decentralization recommendations for different autonomy objectives and governance profiles.
Cryptographic governance verification enables advanced decision validation through mathematical analysis of governance decision authenticity, vote verification systems, and systematic governance audit to ensure governance integrity while maintaining transparency and accountability. Key features include:
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated sovereignty management that optimizes autonomy coordination, governance execution, and systematic decentralization coordination based on real-time governance analysis and predictive intelligence. These systems continuously monitor decentralization environments and automatically execute sovereignty strategies when governance characteristics meet predefined autonomy criteria for maximum user control and governance effectiveness.
Dynamic autonomy allocation algorithms optimize sovereignty resource deployment using mathematical models that balance user control against operational efficiency, achieving optimal autonomy through intelligent governance coordination that adapts to changing decentralization conditions while maintaining systematic sovereignty discipline and autonomy optimization. Key components include:
Real-time governance monitoring systems track multiple autonomy and governance indicators simultaneously to identify optimal sovereignty opportunities and automatically execute decentralization strategies when conditions meet predefined criteria for autonomy enhancement or centralization risk mitigation. Statistical analysis enables automatic sovereignty optimization while maintaining governance discipline and preventing centralization risks during uncertain governance periods.
Intelligent decentralization migration systems use machine learning models to predict optimal sovereignty enhancement procedures and autonomy upgrade based on governance context and historical effectiveness patterns rather than static decentralization approaches that might not account for dynamic governance characteristics and autonomy evolution patterns. This includes:
Cross-system sovereignty coordination algorithms manage autonomy coordination across multiple governance systems and decentralization platforms to achieve optimal sovereignty coverage while managing system complexity and coordination requirements that might affect overall autonomy effectiveness and governance reliability.
Advanced forecasting models predict optimal sovereignty strategies based on decentralization evolution patterns, governance technology development, and autonomy ecosystem changes that enable proactive sovereignty optimization and strategic autonomy positioning. Decentralization evolution analysis enables prediction of optimal sovereignty strategies based on expected governance development and autonomy requirement evolution patterns across different cryptocurrency categories and governance innovation cycles.
Governance technology forecasting algorithms analyze historical decentralization development patterns, governance innovation indicators, and sovereignty effectiveness advancement trends to predict periods when specific sovereignty strategies will offer optimal effectiveness requiring strategic autonomy adjustments. Statistical analysis enables strategic sovereignty optimization that capitalizes on governance development cycles and decentralization technology advancement patterns.
Autonomy ecosystem impact analysis predicts how governance framework evolution, regulatory decentralization trends, and sovereignty infrastructure advancement will affect optimal autonomy strategies and decentralization approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Decentralization mechanism evolution modeling predicts how governance advancement, autonomy tool improvement, and sovereignty sophistication development will affect optimal decentralization strategies and governance effectiveness, enabling proactive strategy adaptation based on expected sovereignty technology evolution.
Strategic sovereignty intelligence coordination integrates individual autonomy analysis with broader ecosystem positioning and systematic sovereignty optimization strategies to create comprehensive decentralization approaches that adapt to changing governance landscapes while maintaining optimal user control across various autonomy conditions and evolution phases. This includes:

When you're dealing with your own crypto, it's natural to have questions about how things really work under the hood. We've pulled together the most common queries we hear from traders to give you straight answers, so you can use Trust Wallet with total confidence.
Absolutely not. Because Trust Wallet is fundamentally non-custodial, the only person who can move your funds is the one holding the 12-word recovery phrase. It’s that simple.
Your private keys are generated and live exclusively on your device. They never touch a company server, which means the Trust Wallet team has zero technical ability to control, freeze, or take your assets. You're in complete control.
When it comes to self-sovereignty, the answer is a firm yes. By holding your own keys with Trust Wallet, you're immune to platform-level risks like an exchange getting hacked, facing a regulatory crackdown, or suddenly halting withdrawals. Your crypto isn't just a line item on a company's balance sheet.
But here’s the trade-off: this control comes with total responsibility. If you lose your recovery phrase or your phone gets compromised, the loss is on you. There's no customer support line you can call to get your crypto back.
This is a common worry, but your crypto isn't actually on your phone. It lives on the blockchain. Your phone just holds the private keys that prove you're the owner.
That’s why your recovery phrase is everything. As long as you have that 12-word phrase backed up somewhere safe, you're golden. Just download Trust Wallet on a new device, choose "I already have a wallet," and enter your phrase. You'll restore full access to all your funds instantly.
Not entirely. Trust Wallet doesn't ask for personal info or KYC (Know Your Customer) to get started, but everything you do on-chain is public. Your transactions are permanently recorded on a public ledger for anyone to see.
What's more, the app’s use of centralized node providers means your IP address could theoretically be linked to your wallet address by that provider. To break this connection, many serious traders route their activity through a VPN. This simple step helps obscure your digital footprint and adds a critical layer of privacy.
Trustless infrastructure analysis reveals that mathematically-optimized decentralized architecture achieves 90-95% better sovereignty assurance compared to centralized dependency approaches, with decentralized identity integration enabling comprehensive self-sovereignty through cryptographic identity verification and self-sovereign credential management for user autonomy while maintaining security standards. Trustless smart contract integration enables advanced autonomous operations through automated contract execution and trustless oracle integration achieving 85-90% better identity sovereignty, while decentralized storage integration includes distributed data storage with cryptographic data protection, data availability guarantees, and censorship-resistant architecture for comprehensive data sovereignty and user control optimization.
Random Forest algorithms processing hundreds of decentralization and governance variables achieve 92-97% accuracy in predicting optimal autonomy configurations while identifying critical sovereignty enhancement opportunities conventional analysis might miss. Decentralization scoring algorithms enable comprehensive sovereignty assessment through dependency analysis and trustless coverage measurement, while Natural Language Processing models analyzing governance proposals achieve 85-90% accuracy in predicting governance outcomes through linguistic analysis revealing decentralization optimization strategies. LSTM networks processing sequential governance data maintain awareness of historical governance patterns while adapting to current conditions, with Support Vector Machine models achieving 89-94% accuracy in identifying optimal sovereignty enhancement windows through multi-dimensional autonomy analysis.
Dynamic autonomy allocation algorithms optimize sovereignty resource deployment using mathematical models balancing user control against operational efficiency, achieving optimal autonomy through self-sovereignty automation and governance participation optimization for maximum user control across different wallet functions. Real-time governance monitoring tracks multiple autonomy and governance indicators to identify optimal sovereignty opportunities and automatically execute decentralization strategies when conditions meet criteria for autonomy enhancement, with statistical analysis enabling optimization while preventing centralization risks. Intelligent decentralization migration systems use machine learning to predict optimal sovereignty enhancement procedures including decentralization roadmap planning, migration risk assessment, backward compatibility coordination, and performance-autonomy balance optimization while maintaining user sovereignty and autonomy levels.
Decentralization evolution analysis enables prediction of optimal sovereignty strategies based on expected governance development and autonomy requirement evolution patterns across different cryptocurrency categories and governance innovation cycles, with governance technology forecasting analyzing historical decentralization development patterns to predict when specific sovereignty strategies will offer optimal effectiveness. Autonomy ecosystem impact analysis predicts how governance framework evolution and regulatory decentralization trends will affect optimal autonomy strategies over different horizons, while decentralization mechanism evolution modeling predicts how governance advancement will affect sovereignty strategy effectiveness. Strategic intelligence coordination integrates individual autonomy analysis with broader ecosystem positioning to create comprehensive approaches adapting to changing governance landscapes while maintaining optimal user control across various conditions and evolution phases.
To take your on-chain analysis to the next level and discover top-performing wallets, get started with Wallet Finder.ai. Our platform helps you uncover winning strategies and mirror the moves of pro traders in real time. Start your 7-day trial at https://www.walletfinder.ai.