AI Crypto Trading Signals: A Trader's Guide for 2026
Unlock the power of AI crypto trading signals. Learn to evaluate signal quality, avoid common pitfalls, and use on-chain data to make smarter DeFi trades.

June 3, 2026
Wallet Finder

February 16, 2026
A seed phrase wallet uses a unique 12 to 24-word phrase generated during setup. This isn't just a password; it's the master key to your entire crypto portfolio. Think of it as the ultimate backup—if your device is lost or broken, this phrase is all you need to restore your assets. It’s the very heart of self-custody.
Picture your crypto holdings not in a bank, but in a personal, invisible vault secured on the blockchain. A seed phrase is the one and only combination to that vault. This string of simple words, usually 12 or 24 long, is the absolute proof that you own your assets on networks like Ethereum or Solana.
This is a world away from a traditional bank, where they hold your money and can freeze your account at will. A seed phrase wallet puts you in complete and total control. This idea, called self-custody, is what makes decentralized finance (DeFi) possible. But with great power comes great responsibility.
When you hold your own seed phrase, you are your own bank. No one can touch, move, or freeze your funds without that exact sequence of words. This gives you a level of freedom and control over your digital assets that is unheard of in traditional finance. It’s a foundational concept for anyone serious about crypto.
The flip side? There’s no customer support line to call if you mess up. If your seed phrase is lost or stolen, your assets are gone forever. That's why mastering seed phrase security isn't just a good idea—it's the non-negotiable first step for any crypto user.
Your seed phrase isn't a password to an account; it is the account. Anyone who has it has full, unrestricted access to your funds, making its protection your highest priority.
Understanding how to manage a seed phrase is central to participating in the broader world of decentralized applications and trading. To see how these principles apply to the tools you'll use, check out our guide on what is a DeFi wallet. The concepts of security and self-sovereignty we've talked about here are the bedrock of that entire ecosystem.
It’s kind of wild to think that just 12 or 24 simple words can protect a whole portfolio of digital assets, especially when they’re scattered across different blockchains. But a seed phrase wallet does exactly this, using a clever and rock-solid mathematical process to turn your phrase into a nearly infinite supply of keys.
Think of your seed phrase as the master blueprint for your entire crypto identity. This blueprint gets plugged into a universal algorithm—basically, a standardized math recipe used by almost every modern wallet—to build every private key and public address you’ll ever need.
The whole process is deterministic, which is a crucial concept in crypto. All this means is that the same seed phrase will always generate the exact same set of keys, in the exact same order, every single time. It doesn't matter what compatible wallet software you use.
Your seed phrase isn't just one key; it's the root of a whole family tree of keys. The algorithm takes your unique phrase and creates a single "master" private key from it. From there, it can generate a virtually endless tree of individual private keys and their matching public addresses for all your different cryptocurrencies.
This diagram shows how it works—one seed phrase acting as the foundation for managing assets on completely different chains like Ethereum and Solana.
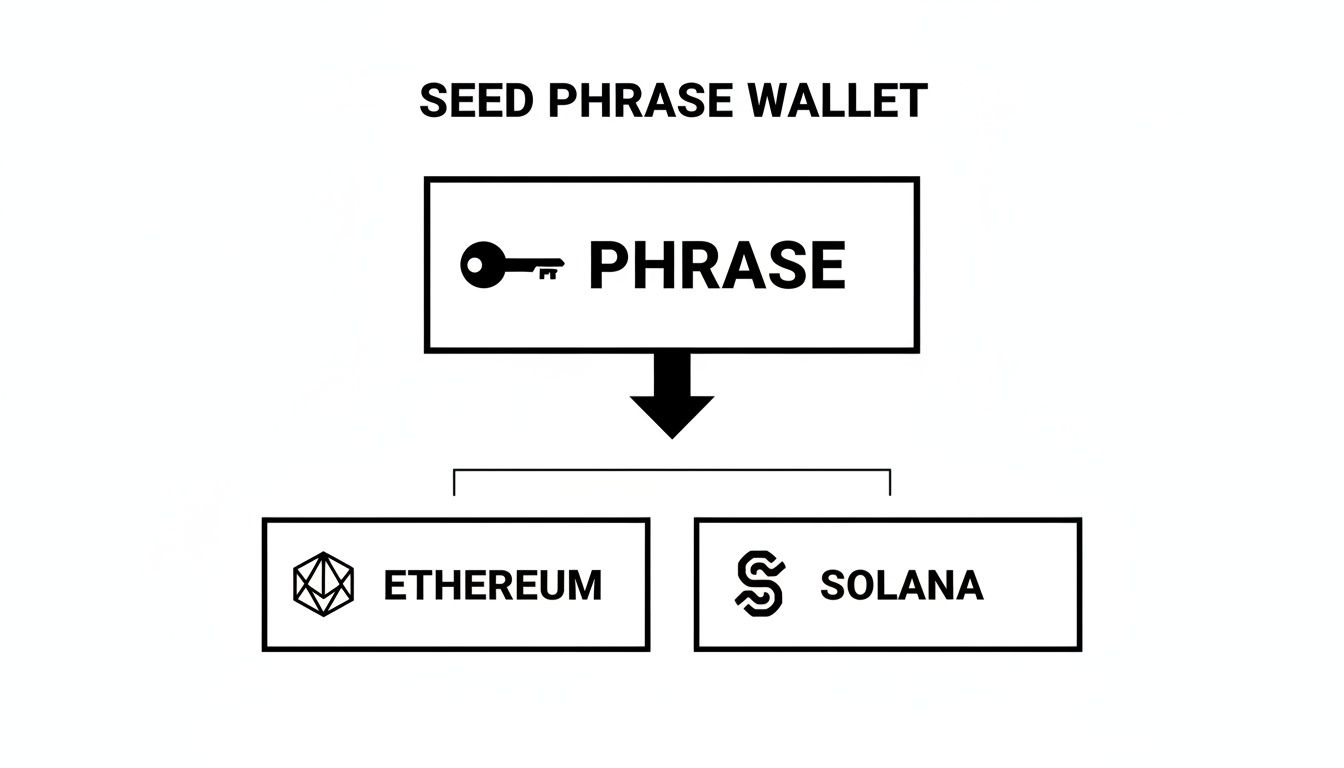
Because of this system, your wallet can give you a fresh, unused address for every transaction you receive. This is a huge plus for privacy, and you never have to create a new seed phrase to do it.
The real magic of this deterministic system shines when you need to recover your wallet. If you lose your phone or your hardware wallet breaks, you don't have to scramble to find individual private keys for your dozens or hundreds of assets. You only need one thing: your original seed phrase.
By simply typing that 12 or 24-word phrase into a new wallet, the algorithm gets to work and rebuilds your entire "building" of keys and addresses exactly as it was before. Your whole portfolio is back in your control, instantly.
This elegant solution is what makes self-custody not just possible, but practical. For an active DeFi trader juggling multiple assets, it means a single, securely stored backup is all you need to protect a complex and growing portfolio. It's security and control, simplified.
The BIP-39 standard that makes seed phrases compatible across wallets uses exactly 2,048 specific English words as its vocabulary. Every valid seed phrase is drawn exclusively from this published list — the list is public, documented, and freely downloadable by anyone. This creates a dictionary attack vulnerability when seed phrases are generated using weak entropy sources rather than true cryptographic randomness.
The attack math: a 12-word phrase selecting from 2,048 words has 2,048^12 possible combinations — approximately 2^132, which is mathematically unguessable by brute force. The vulnerability isn't the wordlist itself but the entropy source used to select from it. Compromised or low-quality random number generators narrow this search space dramatically. If a wallet's RNG produces only 2^40 unique seeds in practice (a discovered flaw), the entire 2^132 theoretical space collapses to 1 trillion guesses — potentially feasible for well-resourced attackers.
Several documented entropy failure modes have produced seed phrases that appear valid but are cryptographically weak:
The only reliable protection is using well-audited, hardware-based entropy sources. Hardware wallets like Ledger and Trezor use dedicated hardware random number generators (HRNGs) combined with user-provided entropy (physical button presses, accelerometer input) to generate seed phrases. This combination makes entropy starvation attacks essentially impossible.
For software wallets, generate seed phrases only in well-established, open-source applications with public code audits confirming their RNG implementation. Avoid generating seed phrases in:
If you have existing seed phrases generated by unknown or potentially compromised software, the safest action is migrating assets to a new wallet generated by verified hardware.
Once you've got your head around the power a seed phrase gives you, the next big question is: where do you actually use it? Choosing a wallet is one of the most important security decisions you'll make, and it all boils down to a classic trade-off between security and convenience.
Your choice here will completely shape how you interact with your crypto. There's no single "best" wallet—only the best one for what you need to do. The two main camps are hot wallets and cold wallets, and most serious crypto users end up using a mix of both.
A hot wallet is any crypto wallet that's connected to the internet. This includes browser extensions like MetaMask and mobile apps like Trust Wallet.
Their biggest advantage is pure convenience. Because they're always online, they’re perfect for daily use—making quick trades on a decentralized exchange (DEX), interacting with a DeFi protocol, or sending funds to a friend.
But that constant connection is also their greatest vulnerability. Being online makes them a potential target for hackers, phishing scams, and malware. It’s best to think of a hot wallet like the cash you carry in your physical wallet—only keep what you need for your day-to-day activity.
On the flip side, a cold wallet is a device that stays completely offline. These are usually hardware wallets, which are small physical gadgets like a Ledger or a Trezor.
These devices store your private keys inside a secure, isolated chip. When you need to approve a transaction, you sign it offline directly on the device. This means your precious seed phrase never, ever touches your internet-connected computer.
This offline approach offers the highest possible level of security against online threats, making cold wallets the undisputed champion for long-term storage. Think of it as your personal digital vault, perfect for locking away the bulk of your portfolio.
The core principle is simple: use hot wallets for frequent, small transactions and cold wallets for the secure, long-term storage of the majority of your portfolio.
Beyond hot and cold, there’s one more critical distinction: who actually controls the keys?
For anyone serious about DeFi, a non-custodial wallet isn't just an option; it's a must-have. It's the only way to achieve real financial autonomy on the blockchain.
Choosing the right wallet can feel overwhelming, but it gets easier when you see the options laid out. This table breaks down the four main categories to help you decide which setup matches your security needs and how often you plan to transact.
Wallet TypeSecurity LevelConvenienceWho Controls KeysBest ForHot (Non-Custodial)MediumHighYouDaily DeFi, trading, small balancesCold (Non-Custodial)Very HighLowYouLong-term holding, large amountsHot (Custodial)Low-MediumVery HighThird-PartyCentralized exchange trading, beginnersCold (Custodial)HighMediumThird-PartyInstitutional custody, crypto IRAs
Ultimately, a non-custodial wallet is the foundation for truly owning your assets. If you're diving into the world of DeFi, selecting the right one is your first major step. You can explore some of the top choices in our guide to the best Ethereum wallets for DeFi trading to find a good fit for your strategy.
In crypto, the biggest threat isn't a bear market—it's simple human error. The most brilliant trading strategy on the planet is worthless if a preventable mistake gets your wallet drained. The stakes couldn't be higher.
One simple slip-up with the master key to your non-custodial wallet on Ethereum, Solana, or any other chain can result in a total, irreversible loss. You can read more about these crypto wallet vulnerabilities to really get a sense of what’s at risk. To keep from becoming a statistic, you must adopt a mindset of extreme paranoia.

When it comes to your seed phrase, convenience is the enemy of security. Any digital copy of your seed phrase is a sitting duck for hackers, malware, and sophisticated phishing attacks.
Here are the absolute digital "don'ts" of seed phrase management:
Think of it this way: a digital copy of your seed phrase is like leaving your vault combination on a sticky note attached to your computer monitor. It’s a matter of when, not if, someone will find it.
Digital blunders are one thing, but simple human interactions can be just as dangerous. Scammers are masters of social engineering, playing on trust, greed, and fear to trick you out of your assets.
These final rules are the most important ones to remember:
Your seed phrase wallet gives you complete control over your crypto. The trade-off is that you—and you alone—are responsible for its security. By avoiding these common but catastrophic mistakes, you're building a fortress around your assets that no market crash could ever touch.
The seed phrase security framework described throughout this guide is mathematically unassailable. The 2^128 brute force protection of a 12-word phrase genuinely cannot be overcome by any computational attack. The guide correctly notes the real threat is theft or phishing — but understates the most direct and historically documented attack: physical coercion.
The "$5 wrench attack" is a security concept named for the simplest possible physical coercion tool. Mathematical security protects your wallet from digital attackers. It offers zero protection against someone who knows you hold significant crypto and threatens you or your family directly. Your BIP-39 entropy is irrelevant when someone is standing in your home.
This isn't theoretical. Documented cases of crypto holders being physically assaulted, kidnapped, or coerced into revealing seed phrases and transferring assets run into the hundreds globally. High-profile cases include home invasions against known crypto traders, armed robberies targeting people leaving crypto conferences, and extortion of family members to pressure wallet owners. Attackers identify targets through public social media flexing, blockchain analytics revealing large wallet balances linked to identifiable individuals, and data breaches from exchanges exposing holder identity and approximate wealth.
Operational security about your holdings is your primary protection:
Plausible deniability through decoy wallets: Maintain a decoy wallet using the same seed phrase but without the passphrase, holding a believable but non-catastrophic amount (1-3% of actual holdings). Under coercion, you reveal the seed phrase and the decoy wallet — the attacker sees real funds that seem plausible, transfers them, and leaves. Your actual wealth remains in the passphrase-protected path they don't know exists.
This decoy architecture works precisely because it's indistinguishable from reality to the attacker. The revealed seed phrase generates a real, functional wallet with real funds. The critical implementation requirement: the decoy must hold enough to be convincing. A wallet showing $200 when you're known to hold significant crypto will not satisfy an attacker who's done basic research.
Now that we've covered what not to do, let's build a proper fortress for your master key. Protecting your seed phrase wallet means getting serious about physical security. A layered, offline strategy is the only reliable way to guard your crypto against both digital hacks and real-world disasters.
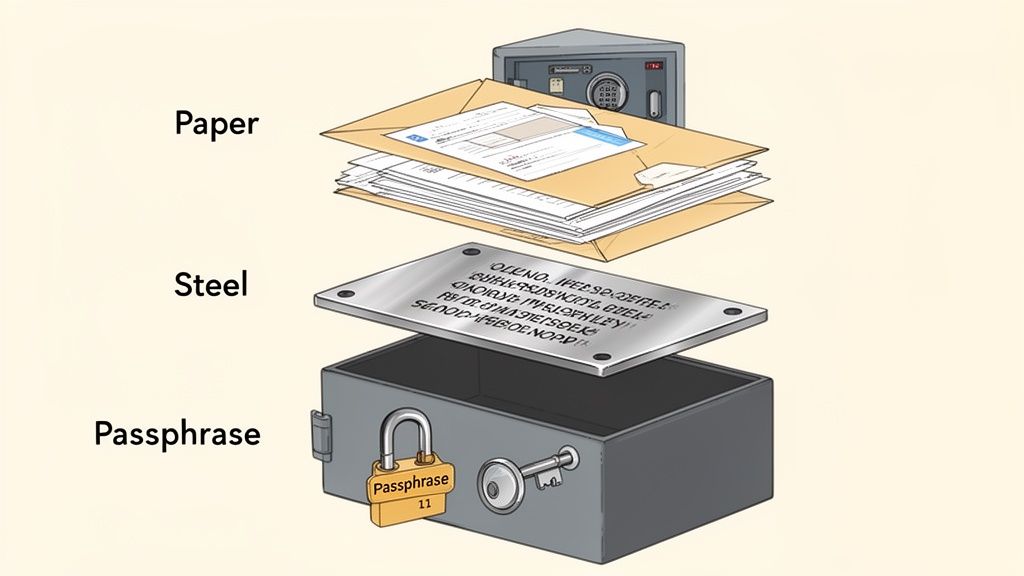
Follow these steps to create a resilient, multi-layered backup system.
Tier 1: Redundant Paper Backups
Tier 2: Fire and Flood Proofing
Tier 3: The Ultimate Security Layer (Passphrase)
This final layer transforms your backup from a simple key into a complex combination lock. If a thief steals your physical seed phrase, it's useless without the memorized passphrase. This is a key part of our broader checklist for assessing wallet risks, which you can use to harden your defenses even further.
The article correctly recommends enabling the passphrase (the optional 25th/13th word) as the ultimate security layer and crucially notes it must be memorized, never written down. This creates a catastrophic estate planning failure that destroys inherited crypto wealth at alarming rates. The security feature that protects you from thieves simultaneously protects your assets from your own heirs.
The inheritance math is brutal. You hold $500,000 in crypto secured by a hardware wallet with a strong memorized passphrase. Your seed phrase is physically secured across two locations per best practice — your heirs can find it. But without the memorized passphrase, those 24 words generate an empty wallet. The actual assets sit in the passphrase-protected derivation path, permanently inaccessible. Your estate lawyer can't help. The hardware wallet manufacturer can't help. No one can help — because the security design worked exactly as intended.
Even when you intend to pass the passphrase on, several failure modes destroy that plan:
The solution isn't abandoning the passphrase — it's designing an inheritance protocol that preserves both security and recoverability.
Option 1 — Shamir's Secret Sharing for the passphrase: Split the passphrase into three mathematical shares where any two can reconstruct it. Give Share A to your estate attorney, Share B to a trusted family member, Share C to a second trusted party. No single person has the passphrase, but two can reconstruct it after your death without exposing it to any individual beforehand.
Option 2 — Sealed estate envelope: Write the passphrase on paper, seal it in a tamper-evident envelope with your signature across the seal, deposit with your estate attorney under instructions to release only to named heirs upon death certificate presentation. Less elegant than Shamir but accessible to non-technical executors.
Option 3 — Hardware-locked secondary access: Configure a second hardware wallet using the same seed phrase but without the passphrase, holding only a small "inheritance signal" amount. Instructions in your will direct heirs to use this device first — confirming they have the seed phrase — then contact a named crypto-specialist attorney who holds the passphrase under attorney-client privilege.
The critical rule: document your security architecture, even if you don't document the passphrase itself. Your heirs should know a passphrase exists, that assets are in the passphrase-derived path rather than the standard path, and who to contact for recovery. Dying without disclosing that a passphrase exists leaves heirs with a correct seed phrase and an empty wallet — they'll assume the funds are gone rather than knowing to search for the passphrase.
A common fear holds a lot of traders back: if I use a tool to track a crypto wallet, can that tool somehow see its seed phrase?
Let’s clear this up right away: The answer is a hard no. Understanding why is crucial for using powerful platforms like Wallet Finder.ai with total confidence.
Think of these tools as specialized search engines for the blockchain. The blockchain itself is a giant public library of financial records, and anyone can walk in to read the books (transaction histories). But what they can't do is see the secret combination to the author's personal safe (your seed phrase).
On-chain analytics platforms only read and interpret the data that is already public for everyone to see.
Data TypeCan Trackers See It?Why?Transaction HistoryYesIt's public record on the blockchain.Token BalancesYesBalances are public data linked to wallet addresses.Trading PatternsYesDerived from analyzing public transaction history.Seed Phrase/Private KeysNoThis data is never broadcast or stored on the blockchain.
Your seed phrase is the master key used to authorize and sign new transactions. It’s not involved in recording old ones. This is a one-way street: the phrase creates a unique digital signature for a transaction, but that signature can never be reverse-engineered to reveal the phrase.
This fundamental separation is what makes the whole system work. You can safely use on-chain analytics to discover winning wallets, and then use the security best practices from this guide to protect the seed phrase for the wallet you use to act on those insights.
Even after you get the hang of seed phrases, a few practical questions always seem to pop up. Let's tackle the most common ones so you can handle these real-world situations like a pro.
If your hardware wallet gets lost, stolen, or just stops working, don't panic. Your crypto is completely safe—as long as you have your seed phrase tucked away securely. Remember, your assets are on the blockchain, not stored inside that little device.
All you need to do is get a new hardware wallet (it can be the same brand or another compatible one) and use your original seed phrase during setup. This will restore full access to all your funds, just like that.
Yes, you can. A standard BIP-39 seed phrase is designed to be compatible across most non-custodial wallets. This means you can import a phrase you got from one app into a completely different one and see the exact same accounts and funds.
But you need to be extremely careful here. Every single time you type your seed phrase into a device that's connected to the internet, you're opening the door to potential threats like malware or a clever phishing scam. Only ever import your phrase into software you absolutely trust and have verified is legitimate.
The statistical odds of someone guessing a 12-word seed phrase are astronomically low—we're talking less than one in 2^128. It’s far, far more likely for a phrase to be stolen through digital scams or physical theft than for it to be guessed by a computer.
Theoretically? Yes. Realistically? Absolutely not. A 12-word seed phrase has more possible combinations than there are estimated atoms in the known universe. Even the world's most powerful supercomputers would need billions of years to have a chance at guessing just one phrase.
The real danger isn't someone guessing it. The danger is you getting tricked into revealing it through a phishing attack, malware on your computer stealing it, or someone physically finding where you wrote it down. Your security focus should always be on protection, not obscurity.
Without explicit inheritance planning, it's permanently lost. Your heirs can find the seed phrase and correctly enter it into a wallet — but it opens the passphrase-free derivation path, which holds nothing. The actual assets live in the passphrase-protected path, inaccessible without the memorized word your heirs don't know.
Solutions: use Shamir's Secret Sharing to split the passphrase into three shares (any two reconstruct it), depositing shares with your estate attorney, a trusted family member, and a second trusted party. Alternatively, seal the passphrase in a tamper-evident envelope deposited with your estate attorney under death-release instructions. At minimum, document in your will that a passphrase exists and which path holds your actual assets — without this, heirs won't know to search for the passphrase.
Buy exclusively from manufacturer direct websites (ledger.com, trezor.io) or their verified official retail partners — never from Amazon third-party sellers or secondary markets. On receipt, verify packaging matches manufacturer-documented tamper-evident features exactly; any signs of resealing are disqualifying.
The definitive test: a legitimate hardware wallet never ships with a pre-written seed phrase. If a seed phrase card is in the box with instructions to use it, the device is compromised — discard it. Run the manufacturer's firmware verification tool before setup to confirm no unauthorized code modifications. Watch seed phrase generation happen on the device's own screen during setup, not through any software on your computer.
Yes — this is a real documented vulnerability. The BIP-39 wordlist is public, and if a wallet's random number generator (RNG) produces low-entropy outputs rather than true cryptographic randomness, the theoretical 2^132 search space of a 12-word phrase collapses to a much smaller practical search space.
Risk factors: generating seed phrases in browser extensions immediately after fresh installation, using unofficial or modified wallet software, running wallet software in virtual machines with limited hardware entropy access. Protection: generate seed phrases only on hardware wallets using dedicated hardware RNG chips combined with physical entropy (button presses, device movement). If you have phrases generated by unverified software, migrate assets to a new wallet generated by audited hardware.
Ready to turn on-chain data into actionable trading signals? Wallet Finder.ai helps you discover and track the most profitable wallets in DeFi. Start your 7-day trial and see what the smart money is doing. Find your edge at https://www.walletfinder.ai.