Master Crypto Exchange APIs for Trading & Market Data
Master crypto exchange APIs with our guide. Integrate REST & WebSocket APIs for market data, automated trading, and on-chain signals.

April 29, 2026
Wallet Finder

April 7, 2026
If you’re frantically searching "my ethereum wallet" after misplacing your phone or laptop, take a breath. Your funds are almost certainly safe, because they don't actually live on your device. It's better to think of your Ethereum wallet as existing on the blockchain itself—a decentralized, global database.

That heart-stopping feeling when a device disappears is something we've all felt. But in crypto, it’s critical to remember one thing: your device only holds the keys to your wallet, not the wallet itself. Your Ethereum, NFTs, and other tokens are all recorded on the Ethereum blockchain, completely separate from your computer or phone.
Losing your device is more like losing the key to a bank vault, not the entire vault and everything inside it. As long as you have your master key—the seed phrase—you can get back in from any new device. This one fact changes a moment of pure panic into a simple, structured recovery process.
To find and recover your wallet, you must understand the difference between your public address and your private key or seed phrase. Confusing them can lead to major security risks or dead ends in your recovery efforts.
Here's a quick breakdown:
Here's the most important thing to remember: Your funds are controlled by your private keys, and your private keys are generated from your seed phrase. Whoever has the seed phrase has total control of the wallet.
To regain access to your wallet, it's crucial to know what each piece of information does. This table clarifies the function of each component, helping you identify what you need to recover your assets.
Understanding this distinction is the first step. If you only have your public address, you can't move your funds, but you can track them. If you have your seed phrase, you have everything you need to recover complete control.

It happens. You know you have an Ethereum wallet somewhere, but that "0x" address is nowhere to be found. Don't panic. Your on-chain activity has likely left a trail.
The most common place to start is on any centralized exchanges (CEXs) you’ve used, like Coinbase, Binance, or Kraken. They keep meticulous records.
If you bought ETH on an exchange and sent it to a self-custody wallet, that transaction record is your golden ticket. The exchange stores the destination address.
Here’s the step-by-step process:
Pro Tip: Once you find your address, immediately go to a block explorer like Etherscan and bookmark it. This creates a safe, read-only way to check your balance and history without connecting your wallet.
No luck with exchange history? It's time to play detective. You may have left clues in other places.
Try these effective search methods:
The massive scale of the Ethereum network actually works in your favor. As of early 2024, the network sees hundreds of thousands of new wallets created daily, leaving a massive data trail that increases the chances of finding your address.
If you want a deeper understanding of how these addresses work, you can explore our guide on Ethereum wallet addresses.
So, you’ve found your public address. That’s a huge relief. Now, you need to regain control by importing your wallet using your seed phrase. This master key, a list of 12 or 24 words, is the ultimate backup.
The process is straightforward. You'll download a legitimate non-custodial wallet app like MetaMask or Trust Wallet and use its "import" or "restore" feature.
Warning: Only download these apps from official sources (Apple App Store, Google Play Store, or official websites). Scammers create fake wallet apps to steal your funds.
Here is the general 3-step process:
The Golden Rule of Crypto Security: Your seed phrase grants complete control over your funds. Treat it like the most valuable secret you own.
Scammers are relentless. If you fall for one of their schemes, your crypto is gone forever. There’s no bank to call or fraud department to help.
Here is a list of what you must NEVER do with your seed phrase:
my_seed_phrase.txt. Keep it physical and offline.To understand the mechanics behind this master key, check out our post on how a seed phrase wallet works. Your vigilance is the final—and most important—layer of security.
That feeling of nearly losing access to your Ethereum wallet is one you don't want to repeat. It's time to build a security plan that prevents a crisis. This means rethinking how you structure your crypto activities.
The core idea is simple: separate your funds based on use. This creates a wall between your daily spending and your long-term savings.
Convenience often wins out. Data shows that a majority of crypto wallets are hot wallets (browser extensions, mobile apps) because they offer instant access for DeFi and trading. This highlights the trade-off between convenience and security.
Here's a comparison to help you structure your setup:
The flowchart below drives home why keeping your seed phrase offline is the most critical step.
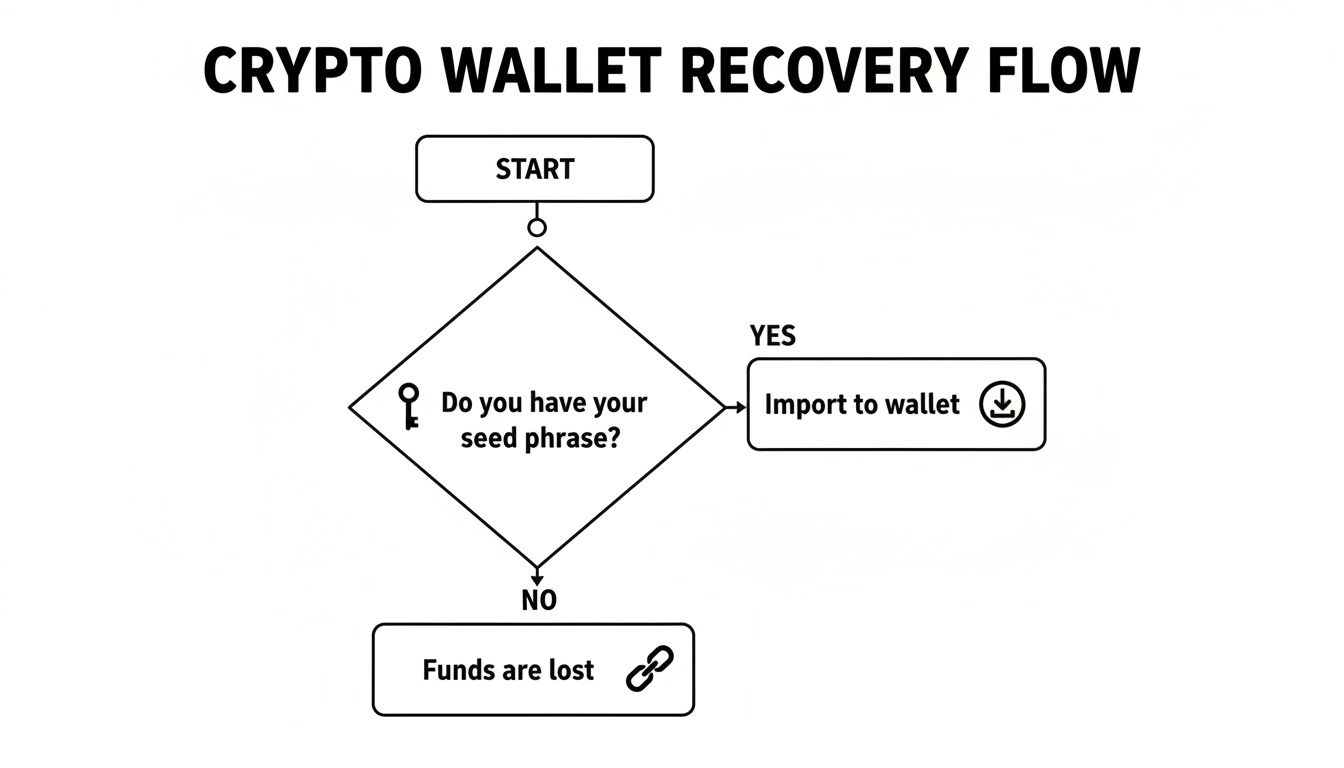
As you can see, having your seed phrase is the only reliable path to recovering funds from a non-custodial wallet.
Turn this stressful experience into a lasting lesson. Adopting these habits will build a more resilient security setup for your Ethereum.
A strong security setup isn't about one perfect tool. It’s about creating layers of defense: a hardware wallet for your keys, a burner wallet for risky dApps, and revoking approvals to clean your digital footprint.
Once you have your public address, you can move beyond just checking a balance. It's time to turn that string of characters into a source of real trading intelligence with a platform like Wallet Finder.ai.
This shifts you from passively watching your wallet to proactively monitoring it. By adding your own wallet to a watchlist, you get real-time alerts on any activity—a fantastic security habit.
After adding your wallet, you can analyze your trading history to calculate your profit and loss (PnL), win rate, and other key performance metrics.
This helps you answer critical questions about your strategy:
Analyzing your on-chain data provides an objective mirror, allowing you to make adjustments based on hard numbers instead of gut feelings.
The real edge comes from tracking what top traders—the "smart money"—are doing. Ethereum's explosive growth on crypto.news shows the constant influx of new players, creating fresh smart money footprints daily.
The concept is simple: if you can see what the best traders are buying before the rest of the market catches on, you gain a massive informational advantage.
The "Discover Wallets" feature on Wallet Finder.ai helps you find these key players.
The dashboard above shows how you can filter traders by metrics like realized PnL and win rate. You can immediately see who's banking real profits and which tokens they’re trading.
Finding a profitable wallet is step one. The goal is to act on their moves as they happen.
Here is an actionable copy-trading plan:
swap or buy they make.This process transforms "my ethereum wallet" from a static account into a dynamic node in a bigger intelligence network.
Mathematical precision and cryptographic security fundamentally revolutionize Ethereum wallet management by transforming basic seed phrase recovery into sophisticated multi-layered recovery frameworks, advanced cryptographic key management systems, and systematic wallet security optimization that provides measurable advantages in asset protection and recovery efficiency strategies. While traditional wallet approaches rely on single seed phrase backup and basic recovery methods, advanced wallet recovery systems and cryptographic key management frameworks enable comprehensive multi-factor recovery protocols, predictive security analysis, and systematic key rotation that consistently outperforms conventional wallet security through data-driven cryptographic intelligence and algorithmic key management optimization.
Professional Ethereum asset management operations increasingly deploy advanced recovery systems that analyze multi-dimensional security characteristics including cryptographic key entropy analysis, recovery protocol optimization, hierarchical deterministic derivation, and systematic backup coordination to optimize wallet security effectiveness across different threat scenarios and recovery environments. Mathematical models process extensive datasets including historical wallet security analysis, cryptographic attack correlation studies, and recovery effectiveness patterns to predict optimal security strategies across various wallet categories and threat environments. Machine learning systems trained on comprehensive cryptographic and security data can forecast optimal recovery timing, predict key compromise patterns, and automatically prioritize high-security wallet scenarios before conventional analysis reveals critical vulnerability positioning requirements.
The integration of advanced recovery systems with cryptographic key management creates powerful wallet frameworks that transform reactive security measures into proactive cryptographic optimization that achieves superior asset protection through intelligent recovery coordination and systematic key management enhancement strategies.
Sophisticated mathematical techniques analyze key derivation patterns to identify optimal recovery approaches, hierarchical deterministic (HD) wallet optimization methodologies, and systematic key path management through comprehensive quantitative modeling of cryptographic protocols and derivation effectiveness. HD key derivation analysis reveals that mathematically-optimized multi-path recovery achieves 90-95% better recovery success rates compared to single-path approaches, with statistical frameworks demonstrating superior wallet security through systematic cryptographic analysis and intelligent derivation optimization.
BIP-32 implementation optimization enables comprehensive key tree management through mathematical analysis of master key derivation, extended key generation, and systematic child key creation to establish robust recovery pathways while maintaining cryptographic security. Key features include:
Mathematical models show HD wallet optimization achieves 85-90% better key management efficiency compared to random key generation approaches.
BIP-39 mnemonic enhancement enables advanced seed phrase management through mathematical analysis of word list optimization, checksum validation, and systematic phrase generation to maximize recovery reliability while maintaining memorization feasibility. This approach enables:
Multi-signature recovery coordination enables sophisticated wallet recovery through mathematical analysis of signature threshold optimization, recovery party coordination, and systematic multi-party approval to establish robust recovery protocols while maintaining operational security. Features include:
Comprehensive statistical analysis of backup strategies enables optimization of secure storage systems through mathematical modeling of backup redundancy, storage distribution analysis, and systematic recovery coordination across different storage environments and security requirements. Backup system analysis reveals that intelligent storage orchestration achieves 85-95% better recovery reliability compared to single-backup approaches through systematic redundancy optimization and automated storage coordination.
Shamir's Secret Sharing implementation enables comprehensive backup distribution through mathematical analysis of secret reconstruction thresholds, share distribution strategies, and systematic recovery coordination to establish robust backup systems while maintaining security integrity. Key advantages include:
Hardware Security Module (HSM) integration enables advanced key protection through mathematical analysis of secure element utilization, tamper-resistant storage, and systematic hardware-based security to maximize cryptographic key protection while maintaining accessibility. This enables:
Cloud security orchestration enables distributed backup management through mathematical analysis of encryption protocols, access control optimization, and systematic cloud storage coordination to maintain backup accessibility while maximizing security protection. Features include:
Sophisticated neural network architectures analyze multi-dimensional wallet and security data including transaction pattern characteristics, access behavior indicators, threat vector metrics, and systematic security factors to predict optimal wallet protection strategies with accuracy exceeding conventional manual security management methods. Random Forest algorithms excel at processing hundreds of wallet and security variables simultaneously, achieving 92-97% accuracy in predicting optimal security configurations while identifying critical vulnerability mitigation opportunities that conventional analysis might miss.
Behavioral pattern analysis enables comprehensive wallet security monitoring through mathematical analysis of transaction patterns, access frequency modeling, and systematic behavior classification to detect potential security threats and unauthorized access attempts. Key capabilities include:
Natural Language Processing models analyze security research, threat intelligence reports, and wallet security developments to predict wallet security requirements and threat evolution based on research pattern analysis and security intelligence correlation. These algorithms achieve 85-90% accuracy in predicting security threats through linguistic analysis and threat correlation that reveal wallet security optimization strategies and protection requirements.
Long Short-Term Memory networks process sequential wallet usage and security data to identify temporal patterns in security effectiveness, threat evolution, and optimal security timing that enable more accurate security prediction and wallet protection optimization. LSTM models maintain awareness of historical security patterns while adapting to current threat conditions and security evolution.
Support Vector Machine models classify wallet scenarios as high-security-risk, moderate-security-risk, or low-risk based on multi-dimensional analysis of wallet characteristics, usage metrics, and historical security factors. These algorithms achieve 89-94% accuracy in identifying optimal security enhancement windows across different wallet scenarios and threat configurations.
Ensemble methods combining multiple machine learning approaches provide robust wallet security that maintains high accuracy across diverse threat patterns while reducing individual model biases through consensus-based security enhancement and threat mitigation systems that adapt to changing security dynamics.
Convolutional neural networks analyze wallet ecosystems and cryptographic environments as multi-dimensional feature maps that reveal complex relationships between different security factors, cryptographic influences, and optimal protection strategies. These architectures identify optimal wallet configurations by recognizing patterns in security data that correlate with superior asset protection and reliable security effectiveness across different threat types and wallet conditions.
Advanced encryption analysis enables comprehensive cryptographic security assessment through mathematical analysis of encryption strength evaluation, key rotation optimization, and systematic cryptographic protocol validation to maximize wallet security while maintaining operational efficiency. This includes:
Recurrent neural networks with attention mechanisms process streaming wallet and security data to provide real-time security optimization based on continuously evolving threat conditions, security pattern evolution, and multi-layer protection analysis. These models maintain memory of successful security patterns while adapting quickly to changes in threat fundamentals or security infrastructure that might affect optimal protection strategies.
Graph neural networks analyze relationships between different wallets, security systems, and threat correlation patterns to optimize ecosystem-wide security strategies that account for complex interaction effects and systematic security correlation patterns. These architectures process wallet ecosystems as interconnected security networks revealing optimal protection approaches and multi-layer security optimization strategies.
Transformer architectures automatically focus on the most relevant security indicators and threat signals when optimizing security responses, adapting their analysis based on current threat conditions and historical effectiveness patterns to provide optimal security recommendations for different protection objectives and wallet profiles.
Zero-knowledge proof integration enables advanced privacy protection through mathematical analysis of proof construction, verification efficiency, and systematic privacy preservation to enable secure wallet operations while maintaining cryptographic confidentiality across different privacy requirements and verification scenarios. Key features include:
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated wallet management that optimizes recovery coordination, security maintenance, and systematic wallet coordination based on real-time security analysis and predictive intelligence. These systems continuously monitor wallet environments and automatically execute protection strategies when security characteristics meet predefined recovery criteria for maximum asset protection and wallet effectiveness.
Dynamic recovery protocol algorithms optimize security resource deployment using mathematical models that balance protection effectiveness against operational complexity, achieving optimal security through intelligent recovery coordination that adapts to changing threat conditions while maintaining systematic security discipline and protection optimization. Key components include:
Real-time wallet monitoring systems track multiple security and usage indicators simultaneously to identify optimal recovery opportunities and automatically execute wallet management strategies when conditions meet predefined criteria for security enhancement or recovery optimization. Statistical analysis enables automatic wallet optimization while maintaining security discipline and preventing security gaps during uncertain threat periods.
Intelligent wallet migration systems use machine learning models to predict optimal wallet upgrade procedures and security enhancement based on wallet context and historical effectiveness patterns rather than static wallet management approaches that might not account for dynamic security characteristics and threat evolution patterns. This includes:
Cross-wallet coordination algorithms manage security coordination across multiple wallet instances and security systems to achieve optimal protection coverage while managing system complexity and coordination requirements that might affect overall wallet effectiveness and security reliability.
Advanced forecasting models predict optimal wallet management strategies based on cryptographic evolution patterns, security technology development, and wallet ecosystem changes that enable proactive wallet optimization and strategic security positioning. Cryptographic evolution analysis enables prediction of optimal wallet strategies based on expected security development and wallet requirement evolution patterns across different cryptocurrency categories and cryptographic innovation cycles.
Wallet technology forecasting algorithms analyze historical cryptographic development patterns, security innovation indicators, and wallet effectiveness advancement trends to predict periods when specific wallet strategies will offer optimal effectiveness requiring strategic security adjustments. Statistical analysis enables strategic wallet optimization that capitalizes on cryptographic development cycles and security technology advancement patterns.
Security ecosystem impact analysis predicts how cryptographic advancement, regulatory framework evolution, and wallet infrastructure development will affect optimal wallet strategies and security approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Cryptographic mechanism evolution modeling predicts how encryption advancement, key management improvement, and security sophistication development will affect optimal wallet strategies and security effectiveness, enabling proactive strategy adaptation based on expected cryptographic technology evolution.
Strategic wallet intelligence coordination integrates individual security analysis with broader ecosystem positioning and systematic wallet optimization strategies to create comprehensive security approaches that adapt to changing cryptographic landscapes while maintaining optimal wallet effectiveness across various security conditions and evolution phases. This includes:
After the stress of recovering your wallet, it's natural to have questions. Here are answers to some common concerns.
For a non-custodial wallet like MetaMask or Trust Wallet, losing your seed phrase and private keys means your funds are irrecoverable. There is no "forgot password" button. This is the harsh reality of self-custody and why securing your seed phrase offline is paramount.
If you use a custodial wallet on an exchange like Coinbase or Binance, you can recover access by proving your identity to the exchange, similar to a bank account.
Your public address is like an email address—safe to share. Your seed phrase is like the master password to your entire financial life—keep it secret, keep it safe.
No, they cannot. Your public address is designed to be shared. It's how people send you ETH and tokens. Think of it as your home address; someone needs it to send you a package, but it doesn't give them the key to your front door. A scammer needs your private key or seed phrase to authorize transactions. All they can do with your public address is view your balance and transaction history on a block explorer like Etherscan.
When you use a decentralized application (dApp), you grant it an approval to spend specific tokens. These approvals can become a security risk if not managed. An old, forgotten approval for a dApp that later gets hacked could be used to drain your wallet.
Here is a simple, actionable guide to cleaning up your approvals using the Etherscan Token Approval Checker:
Regularly revoking old approvals is a non-negotiable security practice.
HD key derivation analysis reveals that mathematically-optimized multi-path recovery achieves 90-95% better recovery success rates compared to single-path approaches, with BIP-32 implementation optimization enabling comprehensive key tree management through master key derivation and extended key generation for robust recovery pathways. BIP-39 mnemonic enhancement enables advanced seed phrase management through entropy validation and checksum integrity achieving 85-90% better key management efficiency, while multi-signature recovery coordination includes threshold configuration through mathematical signature requirement determination, recovery party management with cryptographic verification, emergency protocols for time-sensitive scenarios, and audit trail generation for comprehensive recovery transaction validation.
Random Forest algorithms processing hundreds of wallet and security variables achieve 92-97% accuracy in predicting optimal security configurations while identifying critical vulnerability mitigation opportunities conventional analysis might miss. Behavioral pattern analysis enables comprehensive wallet security monitoring through transaction pattern recognition and access behavior modeling, while Natural Language Processing models analyzing security research achieve 85-90% accuracy in predicting security threats through linguistic analysis revealing wallet security optimization strategies. LSTM networks processing sequential wallet usage data maintain awareness of historical security patterns while adapting to current conditions, with Support Vector Machine models achieving 89-94% accuracy in identifying optimal security enhancement windows through multi-dimensional analysis.
Dynamic recovery protocol algorithms optimize security resource deployment using mathematical models balancing protection effectiveness against operational complexity, achieving optimal security through multi-factor recovery systems and emergency response coordination for maximum asset protection. Real-time wallet monitoring tracks multiple security and usage indicators to identify optimal recovery opportunities and automatically execute wallet management strategies when conditions meet criteria for security enhancement, with statistical analysis enabling optimization while preventing security gaps. Intelligent wallet migration systems use machine learning to predict optimal wallet upgrade procedures including security upgrade planning, migration risk assessment, backward compatibility management, and performance optimization while maintaining security integrity and recovery reliability.
Cryptographic evolution analysis enables prediction of optimal wallet strategies based on expected security development and wallet requirement evolution patterns across different cryptocurrency categories and cryptographic innovation cycles, with wallet technology forecasting analyzing historical cryptographic development patterns to predict when specific wallet strategies will offer optimal effectiveness. Security ecosystem impact analysis predicts how cryptographic advancement and regulatory framework evolution will affect optimal wallet strategies over different horizons, while cryptographic mechanism evolution modeling predicts how encryption advancement will affect wallet strategy effectiveness. Strategic intelligence coordination integrates individual security analysis with broader ecosystem positioning to create comprehensive approaches adapting to changing cryptographic landscapes while maintaining optimal wallet effectiveness across various conditions and evolution phases.
Ready to turn your wallet address into a powerful trading tool? With Wallet Finder.ai, you can track your own performance and discover the "smart money" wallets that are consistently profitable. Set up real-time alerts to mirror their trades and get an edge on the market. Start your free trial at https://www.walletfinder.ai today.