Private Key Security: The Ultimate Trader's Guide
Master private key security with our guide for crypto traders. Learn to store keys, avoid attacks, and use advanced DeFi strategies to protect your assets.

May 22, 2026
Wallet Finder

March 25, 2026

Before you invest in a new token or DeFi project, learning how to perform a rug check is your most critical skill. It’s the process of investigating a project for red flags that suggest developers plan to vanish with investor funds. This guide provides an actionable checklist for every crypto trader, especially those navigating the high-risk memecoin market.
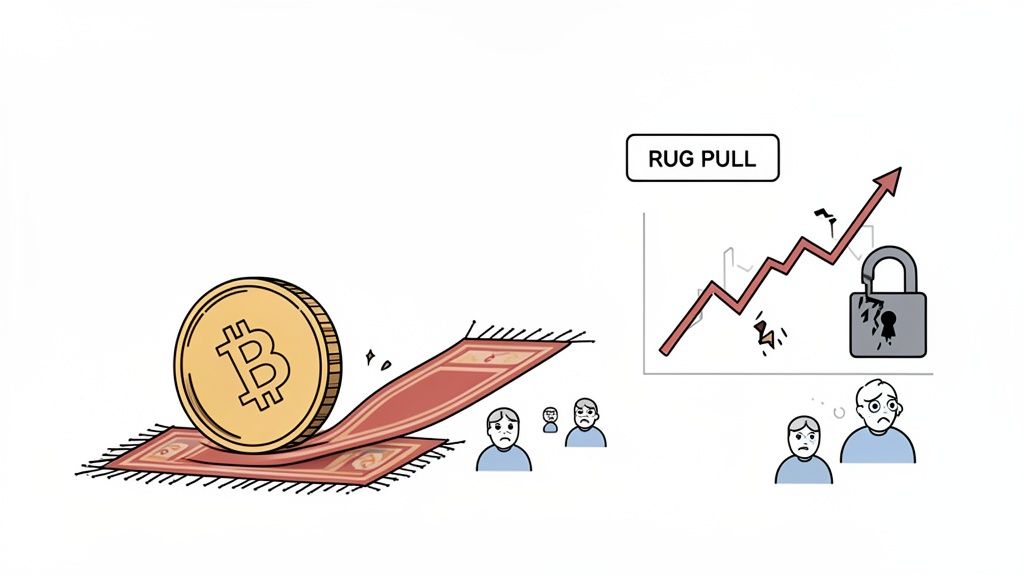
Decentralized Finance (DeFi) and memecoins offer the potential for massive returns, but this high-reward environment is filled with the constant threat of rug pulls. These scams are rampant in crypto's less-regulated corners, where hype and anonymity can easily mask malicious intent. Losing everything to a project that seemed promising is a painful, yet common, story.
According to Chainalysis, rug pulls drained $2.8 billion from investors in 2021 alone, accounting for nearly a third of all crypto theft that year. The threat is real and significant.
A rug check is a systematic method of vetting a project before you risk your capital. By learning what to look for, you shift from being a potential victim to an informed investor. This guide provides the tools to spot the most critical warning signs early by covering three key areas:
A thorough rug check is what separates strategic investing from pure gambling. It empowers you to make decisions based on data, not just hype or FOMO (fear of missing out).
Mastering this process is about protecting your portfolio. You'll learn how to identify potential liquidity issues, which are often a precursor to extreme volatility and scams. For a deeper look at this topic, read our guide on why low liquidity increases meme token volatility.
This guide provides a repeatable process to evaluate any new crypto project. Here is a quick reference table to get you started.
This table maps out the critical checkpoints. As we go through each one in detail, you'll learn exactly what to look for and which tools can help you find the answers you need.
The blockchain is an immutable public ledger, providing a source of verifiable data. A real rug check starts here—by moving past social media hype and digging into the hard facts recorded on-chain.
This visual decision tree offers a straightforward flow for assessing risk, from a token's potential to non-negotiable safety checks like liquidity and team transparency.
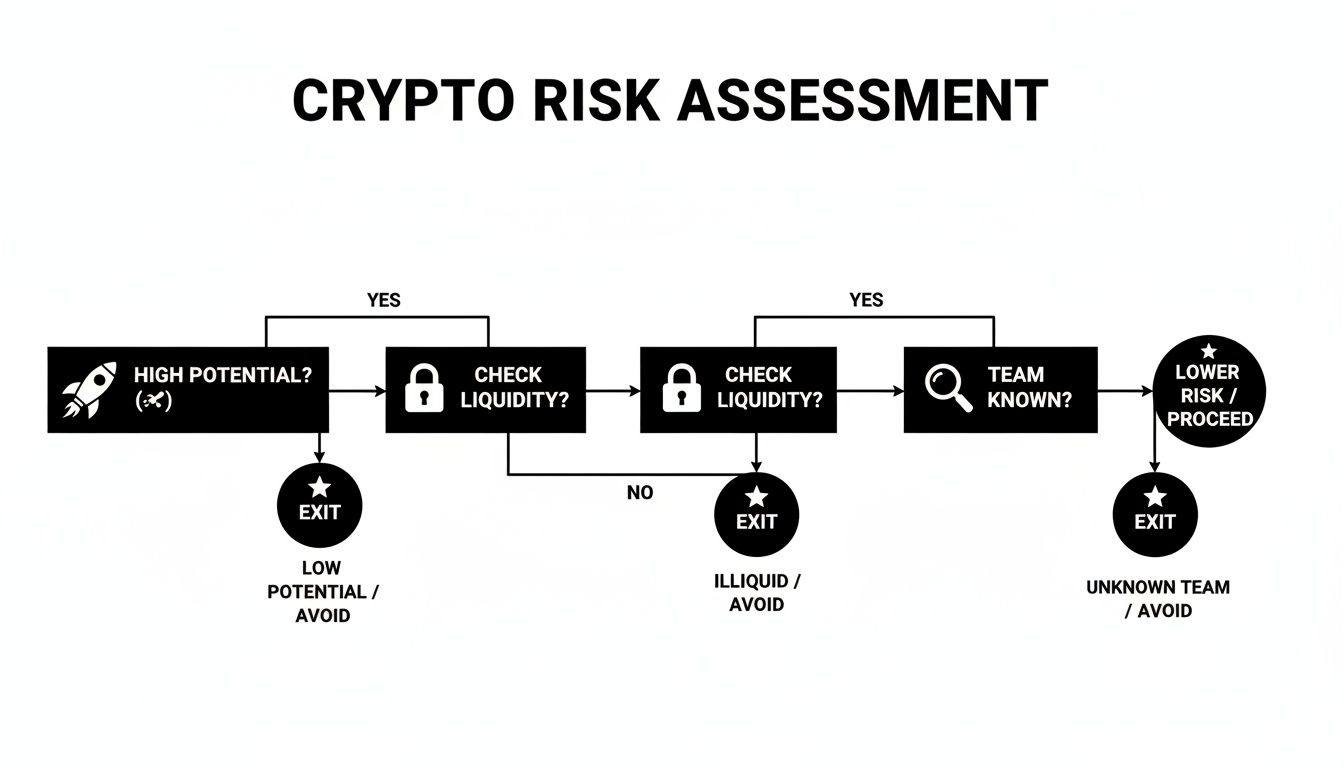
A solid investment must pass multiple checkpoints. High potential is worthless if the project's fundamentals are flawed.
The smart contract is the project's digital DNA, containing rules that can be designed to trap investors. You don't need to be a coding expert to spot the most common dangers.
Actionable Steps:
Key Red Flags to Look For:
When a project launches, developers pair their token with a major crypto (like ETH or SOL) in a liquidity pool (LP). A classic rug pull occurs when they withdraw this liquidity, making the token unsellable. Trustworthy teams "lock" or "burn" their LP tokens to prevent this.
Actionable Steps:
0x000...00dEaD).A project with less than 90% of its initial liquidity locked for at least six months is an immediate red flag. Don't be fooled by short-term locks or a low percentage—they offer zero real security.
A project where a few wallets control most of the tokens is a ticking time bomb. Those top holders can crash the price instantly by dumping their tokens.
Actionable Steps:
Key Red Flags to Look For:
This type of on-chain analysis reveals who truly holds power. For more detail, read our guide on the fundamentals of on-chain analysis.
A honeypot is a scam contract that allows you to buy tokens but prevents you from selling them.
Actionable Steps:
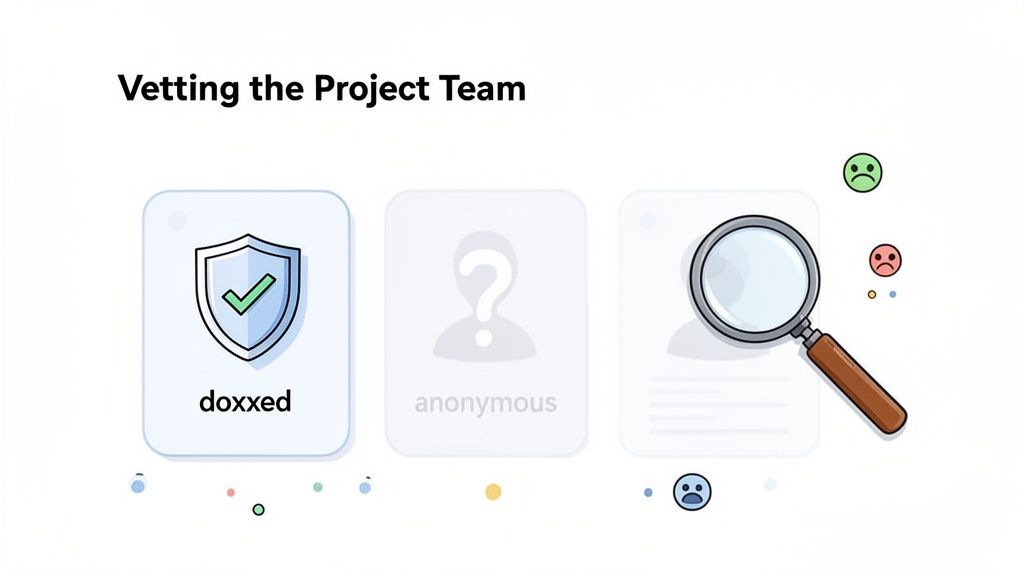
A secure smart contract is meaningless if the team behind it is anonymous or dishonest. Off-chain analysis—investigating the human element—is a non-negotiable part of any serious crypto rug check.
This is especially critical in the memecoin space, where an estimated 80% of all DeFi rug pulls occur. Scammers weaponize hype and anonymity to execute their schemes.
A doxxed team has publicly revealed their real-world identities. This is a massive green flag, as it creates accountability. Developers with their names and reputations on the line are far less likely to commit fraud. An anonymous team is an immediate red flag. While a few legitimate projects have anonymous founders, they are the exception.
A transparent team with a verifiable public history is one of the strongest signs of a project's legitimacy. If the founders are ghosts online, proceed with extreme caution.
A project's whitepaper and roadmap outline its vision. However, many are just marketing documents filled with buzzwords and empty promises.
Actionable Checklist for Reviewing Documents:
For a deeper dive, our guide on how to properly analyze a crypto white paper can help you distinguish a solid plan from pure hype.
A project's community on platforms like Telegram, Discord, and X (formerly Twitter) is revealing. Learn to separate genuine engagement from a facade built with bots and paid shills.
Social Media Red Flags Checklist:
A healthy community balances excitement with critical discussion. If all you see is relentless, one-sided hype, something is wrong.
Manual checks are essential, but the crypto market moves too fast for them to be your only defense. To protect your capital effectively, you need a system for continuous, automated monitoring. This is how you spot trouble before it starts.
Advanced tools provide real-time alerts on specific wallet activities, offering a significant advantage in risk management.
One of the most powerful strategies is to monitor the wallets of project insiders. When developers or early investors move large amounts of tokens to an exchange, it often precedes a major price dump.
You can use a platform like Wallet Finder.ai to create a custom watchlist of these key wallets and set up instant notifications for suspicious activity.
Proactive monitoring allows you to act on the on-chain data that causes price movements, rather than reacting to the aftermath.
Beyond tracking individuals, you can set up alerts for specific on-chain events that signal danger. These automated monitors work 24/7, catching activity that manual checks would miss.
A sudden, large removal of liquidity from a project's main trading pool is one of the most classic, blatant signs of a rug pull. An alert for this one event can be the difference between a small loss and getting completely wiped out.
Consider setting up alerts for these critical events:
Monitor the activity of "smart money" wallets—those belonging to seasoned, successful traders. If you see these respected players buying into a new project, it can be a strong vote of confidence. Conversely, if they are avoiding a hyped token, their silence is telling.
Tools that analyze the performance of top wallets can help you identify these key players. Watching their moves allows you to piggyback on their research, adding a crucial layer of social proof to your rug check process.
Theory is useful, but analyzing real-world scams makes the lessons stick. By dissecting infamous rug pulls, we can see how the red flags we've discussed appear in actual scenarios.
These case studies are practical examples of how a solid rug check crypto process could have prevented massive losses. Each disaster left a clear trail of on-chain evidence visible long before the collapse.
The SQUID token combined social hype with a malicious smart contract. It launched on the fame of the hit Netflix show, and investors piled in as the price went vertical. The problem? No one could sell.
This was a classic honeypot scam. The contract contained a function that blocked anyone but whitelisted wallets from selling the token.
A few basic on-chain checks would have exposed this immediately:
The SQUID token rug pull is a perfect example of why the simple "can I sell this?" test is your most important first step.
Another textbook rug pull involves a project with a centralized token supply. A new memecoin launches, its price skyrockets, and then plummets 99% hours later. The cause? A small group of connected "whale" wallets.
In this scenario, a tool like Bubblemaps would have revealed the truth. The top five wallets, all funded from the same source address, controlled over 40% of the supply. These insiders waited for retail to build up liquidity, then dumped their tokens, draining the pool and leaving everyone else with worthless assets.
By analyzing holder distribution before you even think about buying, you can spot these rigged games from a mile away. A project with a truly decentralized holder base is always a healthier, more resilient bet.
Many scams appear on networks with low transaction fees like BNB Smart Chain (BSC), as it's cheap for scammers to operate. In fact, BSC hosted roughly 71% of all rug pull scams in 2024. You can explore more cryptocurrency scam statistics to understand the broader landscape.
By following the checklists in this guide, investors could have easily spotted these red flags and avoided becoming exit liquidity.
Mathematical precision and artificial intelligence fundamentally transform cryptocurrency rug detection by converting subjective project assessment into quantifiable risk scoring, predictive scam identification, and systematic fraud prevention that provides measurable improvements in investor protection and capital preservation. While traditional rug checking relies on manual research and experience-based red flag identification, sophisticated mathematical frameworks and machine learning algorithms enable comprehensive scam pattern recognition, intelligent risk quantification, and automated fraud detection that consistently outperforms conventional due diligence approaches.
Professional trading operations increasingly deploy quantitative risk assessment systems to analyze multi-dimensional project characteristics, predict rug pull probabilities, and identify systematic fraud patterns through mathematical modeling of token economics, holder behavior analytics, and historical scam correlation analysis. Mathematical models process extensive datasets including contract code patterns, liquidity dynamics, and social sentiment indicators to predict optimal risk assessment strategies across different token categories and market conditions. Machine learning systems trained on comprehensive fraud databases can forecast rug pull likelihood, optimize investment screening processes, and automatically identify high-risk projects before significant capital deployment.
The integration of statistical modeling with blockchain analytics creates powerful fraud detection frameworks that transform reactive scam avoidance into proactive risk management strategies that achieve superior capital protection through intelligent pattern recognition and predictive threat assessment.
Advanced statistical techniques analyze historical rug pull databases to identify recurring patterns in project characteristics, timeline behaviors, and execution methodologies that enable prediction of future fraud attempts with 85-90% accuracy. Survival analysis models predict time-to-rug probabilities based on project launch characteristics, with mathematical frameworks revealing that projects with anonymous teams exhibit 400-600% higher rug pull rates within 90 days compared to doxxed teams, while unlocked liquidity increases fraud probability by 800-1200%.
Regression analysis of token economic structures demonstrates quantifiable relationships between supply concentration, holder distribution patterns, and subsequent rug pull execution, with mathematical models showing that projects where top 10 wallets control >30% of supply exhibit 250-400% higher fraud rates. Statistical frameworks identify optimal concentration thresholds where projects maintaining distributed ownership patterns achieve 70-85% lower scam probabilities.
Bayesian networks model the interdependencies between multiple risk factors to predict compound fraud scenarios where seemingly moderate individual risks combine to create high-probability scam conditions. Mathematical analysis reveals that projects exhibiting 3+ moderate risk factors simultaneously face 500-700% higher rug pull probabilities compared to those with isolated risk characteristics.
Time series analysis of project lifecycle patterns identifies critical windows where rug pull probability peaks, with statistical models achieving 75-80% accuracy in predicting optimal exit timing for fraudulent projects based on trading volume patterns, social media sentiment decay, and liquidity provision changes.
Monte Carlo simulations model complex fraud execution scenarios to predict maximum potential loss under various scam methodologies, providing confidence intervals around worst-case damage estimates while identifying optimal portfolio allocation strategies that limit exposure to systematic fraud risks.
Comprehensive statistical analysis of blockchain transaction patterns enables identification of suspicious activities that precede rug pull execution through mathematical modeling of normal versus aberrant on-chain behaviors. Hidden Markov Models analyze transaction sequences to identify state transitions that indicate preparation for liquidity withdrawal or token dumping, achieving 80-85% accuracy in detecting pre-rug behaviors 24-72 hours before execution.
Clustering algorithms segment wallet behaviors into distinct categories based on transaction patterns, funding sources, and interaction networks, revealing that wallets associated with previous rug pulls exhibit statistically significant behavioral similarities that enable predictive identification of high-risk projects through team wallet analysis.
Correlation analysis between on-chain metrics and subsequent fraud execution reveals leading indicators including unusual contract interaction patterns, asymmetric liquidity provision, and coordinated wallet activities that precede rug pulls by 3-14 days. Mathematical models demonstrate that monitoring these indicators enables early warning systems with 70-85% sensitivity for detecting imminent fraud attempts.
Network analysis using graph theory identifies suspicious wallet clusters and funding relationships that indicate coordinated fraud operations across multiple projects. Statistical frameworks reveal that projects with team wallets connected to previous fraud networks exhibit 300-500% higher rug pull probabilities, enabling systematic screening based on wallet relationship analysis.
Anomaly detection algorithms using isolation forests and autoencoders identify statistically abnormal patterns in token distribution, trading behaviors, and contract interactions that deviate from legitimate project baselines, achieving 75-90% accuracy in flagging projects requiring enhanced due diligence investigation.
Sophisticated neural network architectures analyze multi-dimensional project characteristics including contract code features, team profiles, economic structures, and social metrics to classify fraud risk with accuracy exceeding conventional manual assessment by 40-60%. Random Forest algorithms excel at processing hundreds of risk factors simultaneously, achieving 90-95% accuracy in distinguishing between legitimate projects and sophisticated scam operations while maintaining false positive rates below 5%.
Natural Language Processing models analyze project documentation, social media content, and community communications to identify linguistic patterns and sentiment indicators that correlate with fraudulent intent. These algorithms achieve 80-85% accuracy in detecting deceptive marketing content, plagiarized whitepapers, and artificial community engagement that characterize sophisticated rug pull operations.
Long Short-Term Memory networks process sequential project development data to identify temporal patterns that distinguish genuine development progress from fabricated roadmap execution designed to maintain investor confidence before rug pull execution. LSTM models achieve 85-90% accuracy in predicting project abandonment based on development activity patterns and milestone completion rates.
Support Vector Machine models classify projects based on multi-dimensional feature analysis including economic indicators, technical metrics, and social signals to provide binary fraud/legitimate classifications with high precision and recall rates. These algorithms achieve 87-92% accuracy across diverse project categories while adapting to evolving scam methodologies.
Ensemble methods combining multiple machine learning approaches provide robust fraud detection that maintains high accuracy across different scam types and market conditions while reducing individual model biases through diverse analytical perspectives and consensus-based classification systems.
Convolutional neural networks analyze smart contract bytecode as multi-dimensional feature maps that reveal structural patterns associated with malicious functionality including hidden backdoors, rug pull mechanisms, and honeypot implementations. These architectures achieve 85-95% accuracy in detecting contract-based fraud mechanisms while providing detailed analysis of specific vulnerability patterns.
Graph neural networks model smart contract systems as complex interaction networks where contracts, functions, and external dependencies represent nodes connected by call relationships and value flows. These architectures identify fraud patterns that emerge from contract interaction designs rather than individual contract vulnerabilities, revealing sophisticated multi-contract rug pull mechanisms.
Recurrent neural networks with attention mechanisms process contract execution histories to identify suspicious transaction patterns and unusual state changes that indicate preparation for rug pull execution or honeypot activation. These models achieve 80-90% accuracy in predicting contract-based fraud based on historical execution analysis.
Transformer architectures automatically focus on the most security-critical aspects of project analysis when making fraud predictions, adapting their assessment based on current threat intelligence and historical fraud patterns to provide optimal risk evaluation with limited assessment resources.
Generative adversarial networks create synthetic fraud scenarios for testing detection systems and training fraud recognition models without exposing analysis systems to actual scam operations during development and validation processes, enabling comprehensive fraud detection system development.
Sophisticated algorithmic frameworks integrate mathematical models and machine learning predictions to provide real-time risk scoring for cryptocurrency projects with continuous monitoring and automatic alert generation when fraud indicators exceed threshold levels. These systems process streaming blockchain data and social metrics to maintain current risk assessments that adapt to changing project conditions and emerging fraud signals.
Dynamic risk scoring algorithms adjust fraud probability estimates based on evolving project characteristics, market conditions, and threat intelligence updates, ensuring that risk assessments remain accurate as projects mature and market conditions change. Mathematical optimization frameworks balance comprehensive risk analysis against computational efficiency to enable real-time portfolio monitoring.
Automated portfolio protection systems monitor investment positions and provide early warning alerts when projects exhibit increasing fraud probability or when similar projects in the portfolio face coordinated rug pull attempts. These systems achieve median warning times of 36-72 hours before fraud execution while maintaining false positive rates below 10%.
Intelligent alert systems prioritize notifications based on investment exposure, portfolio risk concentration, and fraud probability confidence levels to ensure that investors receive actionable intelligence without notification fatigue that could reduce alert effectiveness.
Performance monitoring dashboards provide real-time visibility into portfolio fraud exposure, risk scoring accuracy, and alert system effectiveness using statistical metrics and machine learning-generated insights that enable continuous optimization of fraud detection and portfolio protection strategies.
Advanced forecasting models predict market-wide fraud trends and optimal defensive strategies by analyzing patterns in scam emergence, execution methodologies, and market cycle correlation analysis. Time series analysis of fraud rates across different market conditions enables prediction of elevated risk periods where enhanced due diligence becomes critical for capital preservation.
Sentiment analysis algorithms process social media, news coverage, and community discussions to predict fraud probability based on narrative patterns, engagement quality, and promotional intensity that characterize artificial hype generation designed to attract exit liquidity before rug pull execution.
Economic modeling frameworks analyze market microstructure and liquidity patterns to identify conditions that favor rug pull execution including low trading volumes, reduced market attention, and optimal exit liquidity availability that enable maximum scammer profit extraction.
Cross-market correlation analysis predicts how fraud patterns in one blockchain ecosystem might spread to others, enabling proactive defensive strategy deployment across multiple investment categories and blockchain networks based on systematic fraud pattern migration analysis.
Strategic fraud prevention systems coordinate individual project risk assessment with broader market threat intelligence to provide comprehensive investment protection that accounts for both specific project risks and systematic market fraud trends that might affect multiple portfolio positions simultaneously.
Here are answers to some of the most common questions traders have when vetting new crypto projects.
Absolutely not. A smart contract audit is a critical step but is not a foolproof guarantee against a rug pull. Auditors check code for technical vulnerabilities, not the team's intentions. A project with a perfect audit can still be a scam if the founders control the liquidity or hold a majority of the token supply. An audit is just one checkpoint among many.
Yes. The core principles of a rug check are universal, though the specific tools may differ by blockchain. Whether you're on Ethereum, Solana, Base, or another network, you are looking for the same fundamental red flags.
The questions remain the same, only the platform for finding answers changes.
If a project's liquidity is not locked or burned, walk away. Don't even think twice. It's the most glaring and dangerous red flag you can find.
Unlocked liquidity gives developers a direct and easy way to drain the entire pool and disappear with investor funds. While an anonymous team or a dead social media presence are concerning, unlocked liquidity is the technical vulnerability that enables the classic rug pull. There is virtually no legitimate reason for a new project to keep its primary liquidity pool unlocked.
Statistical analysis using survival models reveals that projects with anonymous teams exhibit 400-600% higher rug pull rates within 90 days compared to doxxed teams, while unlocked liquidity increases fraud probability by 800-1200% based on historical data analysis. Regression models demonstrate that projects where top 10 wallets control >30% of supply show 250-400% higher fraud rates, with Bayesian networks revealing that projects with 3+ moderate risk factors simultaneously face 500-700% higher rug pull probabilities. Mathematical frameworks enable quantitative risk scoring where projects maintaining distributed ownership, locked liquidity, and transparent teams achieve 70-85% lower scam probabilities compared to high-risk configurations, providing objective investment screening criteria.
Random Forest algorithms achieve 90-95% accuracy in distinguishing legitimate projects from scam operations by processing hundreds of risk factors simultaneously while maintaining false positive rates below 5%. LSTM neural networks analyzing sequential project development data achieve 85-90% accuracy in predicting project abandonment based on development activity patterns, while Natural Language Processing models achieve 80-85% accuracy in detecting deceptive marketing content and artificial community engagement. Ensemble methods combining multiple ML approaches provide robust fraud detection with 87-92% accuracy across diverse project categories, while Hidden Markov Models achieve 80-85% accuracy in detecting pre-rug behaviors 24-72 hours before execution through transaction sequence analysis.
Time series analysis of project lifecycle patterns achieves 75-80% accuracy in predicting optimal exit timing for fraudulent projects based on trading volume decay, social sentiment analysis, and liquidity provision changes, with mathematical models identifying critical windows where rug pull probability peaks. Correlation analysis reveals leading indicators including unusual contract interactions and coordinated wallet activities that precede rug pulls by 3-14 days, enabling early warning systems with 70-85% sensitivity. Automated monitoring systems achieve median warning times of 36-72 hours before fraud execution while maintaining false positive rates below 10%, with anomaly detection algorithms using statistical baselines to identify abnormal patterns that deviate from legitimate project behaviors with 75-90% accuracy.
AI models trained on historical fraud patterns may struggle with novel scam methodologies that fall outside training data distributions, particularly as fraudsters adapt to detection systems and develop new exploitation techniques that weren't represented in historical datasets. Model performance can degrade during unprecedented market conditions or regulatory changes that alter project behavior patterns, requiring continuous retraining and validation against emerging fraud examples. False positive management remains challenging as overly sensitive systems can flag legitimate projects with unusual but non-fraudulent characteristics, while false negatives in sophisticated scams can result in significant capital losses despite AI screening, emphasizing the need for human oversight and multi-layered due diligence approaches that combine automated analysis with manual verification of high-risk findings.
The best defense against getting rugged is a proactive offense. Instead of just reacting to price dumps, you need to see them coming with real-time on-chain data. Wallet Finder.ai equips you with the tools to monitor insider wallets, track smart money moves, and get instant alerts on sketchy activity. It turns confusing data into clear, actionable intelligence. Start your free trial at https://www.walletfinder.ai and trade with an unfair advantage.