Dogen Crypto Price: A Trader's Analysis & Guide
Get a complete analysis of the Dogen crypto price. Understand key indicators, track smart money, and learn actionable strategies for monitoring this memecoin.

May 16, 2026
Wallet Finder

February 20, 2026
Smart contract security is the practice of designing, building, and deploying blockchain contracts that are resilient to exploits. It's an absolutely critical field because once a smart contract is live on the blockchain, its code is immutable—it cannot be changed. This means any tiny flaw becomes a permanent, exploitable backdoor that could lead to catastrophic financial loss.
Welcome to the high-stakes world of decentralized applications, where a single coding mistake can lead to millions of dollars vanishing in minutes. Think of a smart contract as a digital vault that runs on automated, unbreakable rules. If there's a flaw in those rules, the vault is effectively left wide open for anyone on the internet to raid.
This isn't just a "what if" scenario. We've seen billions of dollars drained from DeFi protocols, NFT projects, and DAOs because of security failures. These hacks don't just cause devastating financial losses; they shatter the user trust that the entire Web3 ecosystem is built on. Because blockchain transactions are irreversible, once the funds are gone, they're almost always gone for good.
The fallout from weak smart contract security hits every corner of the decentralized world. Whether you're building, investing in, or just using dApps, a proactive security mindset is non-negotiable.
Here’s a breakdown of how different sectors are impacted:
A smart contract is only as secure as its weakest line of code. In an environment where transactions are irreversible, 'good enough' security is never good enough. It has to be airtight.
Ultimately, building resilient and trustworthy systems isn't just a technical best practice—it's essential for the long-term survival of Web3. This guide is here to show you not just what can go wrong, but how to get it right from the very beginning.
To build secure smart contracts, you first have to think like an attacker. Vulnerabilities aren't just lines of buggy code; they're unlocked doors inviting hackers to drain funds, rig outcomes, and shatter trust in a project. Let's move past the dense technical jargon and break down the most common threats with simple analogies to see how they really work.
The financial stakes here are astronomical. The entire blockchain world has seen staggering losses from these exploits, with over $2.2 billion stolen from crypto platforms in a single year—a 20% jump from the year before. This isn't random; it's driven by a pattern of known vulnerabilities like reentrancy, broken access control, and oracle manipulation. In fact, one detailed security report analyzing 149 major hacks found that these specific flaws led directly to more than $1.42 billion in losses across DeFi, NFTs, and other dApps.
This infographic really drives home the point: smart contracts are the digital vaults at the heart of everything we do in Web3, from DeFi and NFTs to DAOs.
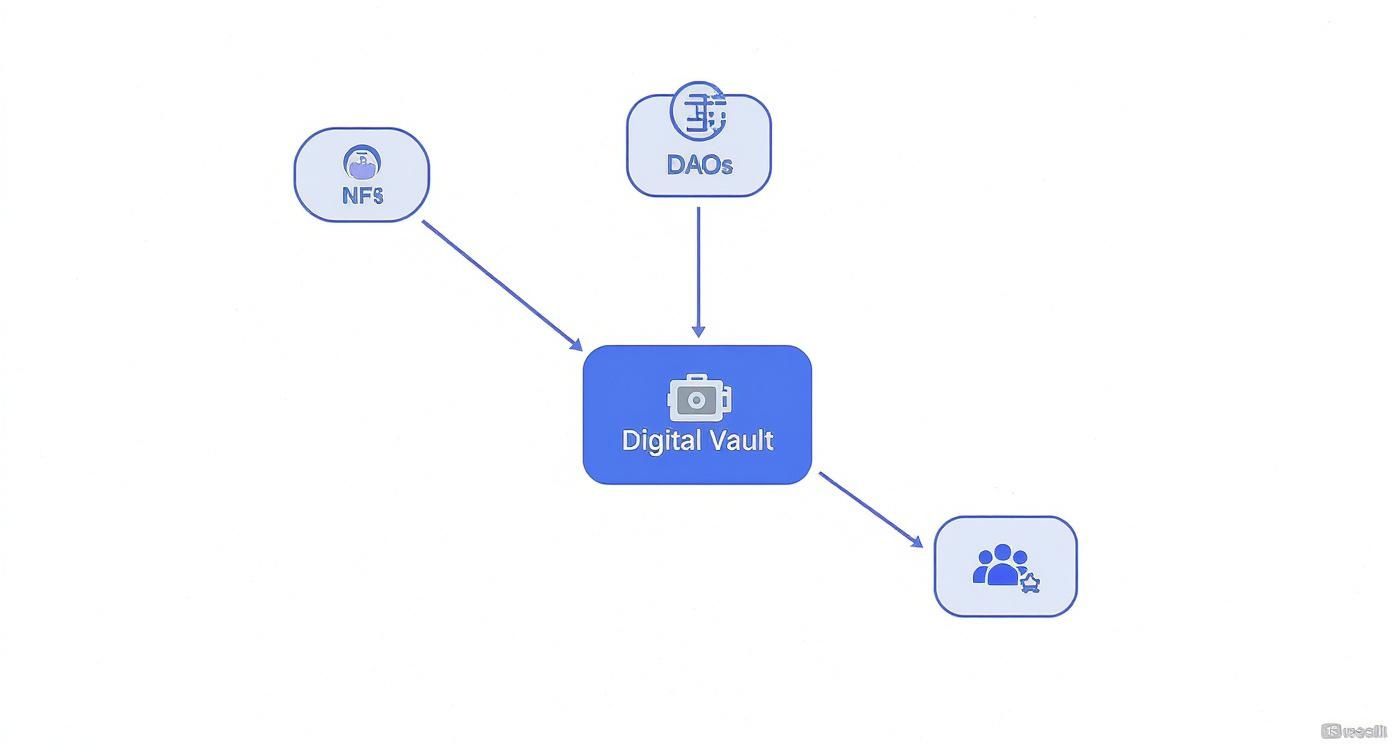
Because these vaults secure such a diverse range of high-value applications, a single weakness in one contract can send shockwaves across the entire ecosystem.
Picture a bank teller who’s having a bad day. They hand you cash from your account but forget to update the balance on their computer right away. A reentrancy attack is the smart contract version of this blunder.
Here’s how it works: an attacker’s malicious contract calls a function like withdraw(). The victim contract sends the funds but—crucially—before it updates the attacker's balance. The malicious contract is designed to immediately call that same withdraw() function again, and again, and again, all before the first transaction has a chance to finish. This loop drains the contract dry until there’s nothing left.
Actionable Prevention Steps:
ReentrancyGuard is the industry standard.transfer() or send() over call(): For simple ETH transfers, transfer() and send() have a built-in gas limit that prevents reentrancy, though call() is necessary for more complex interactions.If you want to dive deeper into the technical nuts and bolts, we have an in-depth guide on detecting reentrancy attacks that covers mitigation strategies.
Poor access control is one of the simplest yet most devastating flaws you’ll find. It’s the digital equivalent of leaving the admin keys hanging on the front door of your vault. This happens when a function that should be restricted—like one only the contract owner can use—is left open for anyone to call.
For instance, imagine a function that lets the owner change withdrawal fees or upgrade the contract's entire logic. If it’s missing the proper security checks, an attacker can just waltz in, call the function, and make themselves the new owner. From there, they can drain the treasury or even self-destruct the contract.
Actionable Prevention Steps:
onlyOwner Modifiers: Apply modifiers to restrict critical functions to authorized addresses.admin, minter, pauser) rather than a single owner.tx.origin for Authorization: Never use tx.origin for authentication, as it can be easily exploited by intermediary malicious contracts. Use msg.sender instead.internal or private: This prevents anyone from re-initializing the contract's state after deployment.Many DeFi protocols need to know what’s happening in the real world, like the current price of ETH or BTC. They get this information from oracles, which act as a bridge for external data. Oracle manipulation is when an attacker finds a way to feed the smart contract bad data to trick it.
Think of it like this: a lending protocol uses a price oracle to value collateral. An attacker takes out a huge flash loan and uses it to momentarily crash the price of an asset on the specific decentralized exchange the oracle is watching. With the price now artificially tanked, the attacker can liquidate other users' positions at a massive discount, pocketing a tidy profit before the market corrects itself moments later.
To give you a clearer picture, the table below summarizes some of the most frequent exploits, how they work, and the real-world consequences. Recognizing these patterns is the first step toward building stronger defenses.
Vulnerability TypeHow It WorksReal-World ConsequenceHow to Prevent ItInteger Overflow/UnderflowForcing a number variable to wrap around its maximum or minimum value (e.g., 255 + 1 = 0 for a uint8).Can be used to mint infinite tokens, bypass payment checks, or drain contract funds.Use SafeMath libraries (like OpenZeppelin's) or Solidity version 0.8.0+, which has built-in checks.Front-RunningAn attacker sees a profitable transaction in the mempool and pays a higher gas fee to get their own transaction processed first.Steals profitable trades, arbitrages, or NFT mints from legitimate users.Implement a commit-reveal scheme or use a submarine-send service to hide transaction details until after execution.Timestamp DependenceA contract uses block.timestamp for critical logic, which miners can slightly manipulate.Allows miners to unfairly influence outcomes in time-sensitive applications like lotteries or games.Avoid using block.timestamp as a primary source of entropy or for critical decision-making. Use oracles or commit-reveal schemes instead.Unchecked External CallsA contract calls an external contract but doesn't handle potential failures, assuming the call will always succeed.Can lead to the contract getting stuck in an invalid state, freezing funds, or creating denial-of-service vulnerabilities.Always check the return value of external calls and handle both success and failure cases appropriately.
These are just a few of the creative ways attackers try to break things. By anticipating these vectors and designing code that is resilient by default, we can build a much safer ecosystem for everyone.
Solid smart contract security isn't something you just tack on at the end. That’s like trying to add a foundation to a skyscraper that’s already been built—it’s clumsy, inefficient, and usually too late. Instead, security needs to be woven into every single stage of the development process.
Think of a Secure Development Lifecycle (SDLC) as the architectural blueprint for a digital fortress. You wouldn't just start laying bricks without first figuring out where the walls, gates, and watchtowers need to go. It's the exact same idea here. Building security in from day one is far more effective than scrambling to patch holes in a live, immutable contract.
This proactive approach helps teams spot flaws when they're still easy and cheap to fix, reducing the risk of a catastrophic exploit down the line and building a much more trustworthy app for your users.
Before you write a single line of code, you need to think like an attacker. This is where threat modeling comes in. It’s the process of mapping out potential security risks and planning your defenses while you're still in the design phase.
Actionable Threat Modeling Checklist:
The point of threat modeling isn't to squash every single potential bug. It's to build a system that is secure by design. You're shifting from reactive bug-fixing to proactive risk management.
Once your secure design is locked in, it’s time to build. Writing secure code means sticking to battle-tested standards and patterns that help you sidestep the most common traps.
Actionable Secure Coding Best Practices:
require(msg.sender == owner)).No amount of careful design or coding can replace a truly hardcore testing strategy. In Web3, testing is more than just making sure functions return the right values. You have to actively simulate hostile environments and adversarial attacks.
Your testing strategy should include this actionable checklist:
The final piece of the puzzle is getting your contract onto the blockchain securely and managing its lifecycle.
Secure Deployment Checklist:
If your contract is upgradeable, check out our guide on smart contract upgrades and their security risks to ensure your upgrade mechanism is rock-solid.
The article discusses traditional testing approaches but lacks sophisticated mathematical frameworks that can provide absolute certainty about smart contract security properties through formal verification methods. Formal verification transforms probabilistic security assessment into mathematical proof that contracts cannot be exploited under specified conditions.
Theorem proving systems like Coq, Isabelle/HOL, and Lean enable developers to write mathematical proofs that smart contracts satisfy specific security properties. Theorem provers verify that contracts cannot violate invariants like "user balances never decrease without explicit authorization" or "total supply remains constant across all operations." Interactive proof development guides developers through logical reasoning while automated tactics handle routine verification tasks.
Model checking algorithms systematically explore all possible execution paths to verify that smart contracts satisfy temporal logic specifications under every conceivable scenario. Model checkers like TLA+, SPIN, and NuSMV can analyze contracts with millions of states to ensure security properties hold universally. Unlike testing that samples execution paths, model checking provides mathematical proof of correctness across infinite execution possibilities.
Specification languages enable precise mathematical description of smart contract behavior and security requirements. Languages like Dafny, Why3, and K Framework provide formal notation for expressing function preconditions, postconditions, and invariants that prevent vulnerability classes. Specifications serve as mathematical contracts between developers and verification tools while enabling automated proof generation.
Contract invariants define mathematical properties that must hold throughout contract execution, providing systematic protection against entire vulnerability classes. Invariants can specify that reentrancy guards remain locked during external calls or that access control permissions follow specific hierarchies. Automated verification tools check that invariants are preserved under all possible execution scenarios.
Temporal logic specifications express security properties that involve time-dependent behavior using Linear Temporal Logic (LTL) and Computation Tree Logic (CTL). Temporal properties can specify that "after initiating a withdrawal, user balance decreases before the function returns" or "privileged functions are never callable by unauthorized addresses." Temporal verification provides guarantees about execution ordering and timing relationships.
Sophisticated verification techniques enable formal analysis of complex security properties through mathematical modeling and automated proof generation.
Abstract interpretation provides mathematical frameworks for analyzing smart contract behavior through lattice theory and fixed-point analysis. Abstract domains capture security-relevant properties while abstracting away implementation details irrelevant to security verification. Lattice-based analysis enables systematic abstraction that preserves critical security properties while enabling efficient verification.
Symbolic execution with formal constraints uses mathematical logic to represent all possible program states and execution paths simultaneously. Constraint solvers like Z3 and CVC4 determine whether security violations are possible by solving mathematical equations representing contract execution. Symbolic approaches achieve completeness guarantees that testing approaches cannot provide.
Refinement verification establishes mathematical relationships between abstract security specifications and concrete implementations to ensure security properties are preserved during development. Refinement relations prove that implementations cannot introduce vulnerabilities not present in verified specifications. Stepwise refinement enables verification of complex contracts through systematic decomposition.
Program synthesis automatically generates provably secure smart contract implementations from formal security specifications. Synthesis tools produce code guaranteed to satisfy security properties while meeting functional requirements. Automated synthesis eliminates implementation errors that introduce vulnerabilities while ensuring generated code meets mathematical specifications.
Compositional verification techniques enable formal analysis of complex DeFi systems by verifying individual contracts and their interactions separately while maintaining mathematical guarantees about overall system security. Assume-guarantee reasoning allows modular verification where each component's security proof depends only on interface specifications rather than implementation details.
Deployment of formal verification requires systematic integration with development workflows and careful balance between verification completeness and practical constraints.
Specification-driven development integrates formal specification writing with code development to ensure security properties are designed into contracts from inception. Early specification development guides implementation while incremental verification catches security issues before they compound. Specification-first approaches achieve higher verification coverage with lower overall effort.
Verification condition generation automatically translates smart contracts and security specifications into mathematical formulas suitable for automated theorem proving. VC generation handles the mechanical aspects of formal verification while enabling developers to focus on security properties and specifications. Automated translation ensures consistency between code and verification conditions.
Proof automation reduces manual verification effort through automated theorem proving, proof search strategies, and tactic development. Modern proof assistants provide high-level proof languages and automated decision procedures for routine verification tasks. Automation enables focus on high-level security properties rather than low-level proof mechanics.
Counterexample-guided refinement provides concrete attack scenarios when formal verification identifies potential vulnerabilities. Counterexamples enable developers to understand precisely how security properties can be violated while guiding specification and implementation refinement. Concrete examples bridge the gap between abstract mathematical proofs and practical security understanding.
Tool integration frameworks combine formal verification with existing development environments, testing frameworks, and continuous integration systems. Integration tools handle the complexity of verification tool chains while providing familiar development experiences. Seamless integration encourages formal verification adoption without disrupting established workflows.
Formal verification provides mathematical certainty about security properties but requires significant mathematical expertise and verification infrastructure. The investment in formal methods is often justified for high-value protocols where security failures can result in substantial losses, providing the highest possible assurance level for critical smart contract systems.
Even with the most buttoned-up Secure Development Lifecycle, every project needs a fresh set of eyes. Your team can be the best in the business, but blind spots are just human nature. This is where professional audits and public bug bounties come in, acting as the ultimate stress test before your code is trusted with a single dollar of user funds.
These external reviews aren't just a box-ticking exercise for catching bugs; they're about building rock-solid trust. A clean audit report from a reputable firm tells the world you're serious about security. A bug bounty program shows you're committed to keeping the protocol safe for the long haul.
So, what exactly is a smart contract audit? Think of it as hiring a team of professional ethical hackers to try and crack open your digital vault before the real criminals get a chance. It’s a deep-dive analysis of your entire codebase by third-party security experts.
An Actionable Guide to a Successful Audit:
A good audit doesn't just point out problems; it helps you understand the why behind them. It's a collaborative process that strengthens both your code and your team's security mindset for future projects.
An audit gives you a fantastic point-in-time snapshot of your code's health. But for continuous, ongoing security, you need a bug bounty program. This is like crowdsourcing your security to a global army of white-hat hackers, all financially motivated to find and responsibly report vulnerabilities.
Platforms like Immunefi or HackerOne are the marketplaces where projects connect with thousands of these security researchers. By offering a cash reward (a "bounty"), you incentivize the best in the world to poke, prod, and pressure-test your live contracts.
According to the Top 100 DeFi Hacks Report, a jaw-dropping 44% of all attacks are now off-chain, and an even more alarming 47% of total losses come from something as simple as compromised private keys. This proves that audits must be paired with strong operational security and continuous vigilance.
Putting together a successful bug bounty program boils down to a few key ingredients:
ComponentDescriptionActionable TipClear ScopeDefines exactly which contracts and assets are fair game.Be explicit about what's in and out of scope to focus researchers' efforts on your most critical assets.Tiered RewardsOffers different payout amounts based on a vulnerability's severity (e.g., Low, Medium, High, Critical).Set a significant reward for critical findings (often 5-10% of funds at risk) to attract top-tier security talent.Responsive CommunicationHaving a dedicated person to quickly acknowledge reports and work with researchers.Establish a clear Service Level Agreement (SLA) for response times to build a strong reputation within the security community.
By layering professional audits with a well-managed bug bounty program, you build a security model that's truly battle-tested. It’s the best way to protect your project and its users from threats, both on-chain and off.
Getting your smart contract audited and deployed isn't the finish line. That's actually where the real work begins. The most battle-hardened protocols treat security not as a one-off task, but as a constant, active defense.
Real-time on-chain monitoring acts as your dApp's dedicated Security Operations Center (SOC), watching the blockchain 24/7 for any hint of trouble. It's about shifting from a passive, pre-launch checklist to an active, around-the-clock guard. You want to catch exploits as they're happening, not read about them in a post-mortem report.
Specialized platforms sift through mempool chaos and transaction data in real time, hunting for the digital fingerprints of an attack. This could be a brand-new wallet suddenly firing off complex, multi-step transactions or a transaction with a ridiculously high gas fee—a classic sign of someone trying to front-run legitimate users.
Audits are absolutely essential, but they're static. Monitoring, on the other hand, is dynamic. It’s the live intelligence feed that helps you fight back against threats that pop up after deployment. A good monitoring tool establishes a baseline of your protocol's normal activity and then flags anything that deviates from it.
Here is an actionable list of red flags that often signal an attack in progress:
On-chain monitoring transforms security from a historical analysis into a real-time defense mechanism. It’s the difference between locking the vault door and having guards who watch it around the clock.
This dashboard from Wallet Finder.ai is a perfect example of how a monitoring tool visualizes suspicious activity, giving teams an instant, at-a-glance view of potential threats.
What makes this so powerful is the ability to connect the dots. A single high-gas transaction might be nothing, but when you see it comes from a brand new wallet that's also making strange function calls, you've got a clear picture of an unfolding attack.
Let’s make this real. Imagine a DeFi lending protocol that uses a price oracle to value collateral. An attacker's goal is to fool the protocol into thinking the collateral is worthless, letting them liquidate positions unfairly.
Here’s how a real-time defense would play out:
This is what modern security looks like. The monitoring system turned an abstract threat into a concrete, actionable alert that saved the protocol from a catastrophic failure.
The article covers traditional monitoring but lacks sophisticated AI systems that can learn from attack patterns, predict novel threats, and automatically discover vulnerabilities through machine learning techniques. AI-powered security analysis represents the cutting edge of smart contract protection through adaptive threat detection and predictive vulnerability assessment.
Deep learning neural networks trained on vulnerability datasets achieve 85-95% accuracy in identifying security flaws through pattern recognition that surpasses human auditors for common vulnerability classes. Convolutional Neural Networks adapted for code analysis learn abstract representations of vulnerable code patterns while Recurrent Neural Networks analyze sequential aspects of smart contract execution. Graph Neural Networks model contract interaction patterns and control flow structures to identify complex vulnerabilities.
Anomaly detection algorithms identify unusual behavior patterns in smart contract execution that may indicate zero-day exploits or novel attack techniques. Machine learning models trained on normal execution patterns flag deviations that suggest malicious activity including unusual gas consumption, unexpected state changes, or abnormal transaction patterns. Unsupervised learning approaches detect attacks without requiring labeled examples of attack types.
Natural Language Processing techniques analyze smart contract comments, documentation, and variable names to identify semantic indicators of security issues. NLP models can flag contracts with inconsistent documentation, misleading comments, or variable names that suggest dangerous functionality. Semantic analysis helps identify developer intent that may not align with actual implementation security.
Behavioral pattern recognition systems learn from historical attack data to identify emerging threat patterns and predict future attack vectors. Machine learning models trained on thousands of historical exploits can recognize attack signatures and predict likely targets based on contract characteristics. Predictive models enable proactive security measures before attacks occur.
Automated vulnerability discovery uses machine learning to generate and test potential exploit scenarios against smart contracts. AI systems can systematically explore attack possibilities while learning from successful and unsuccessful exploitation attempts. Automated discovery scales vulnerability research beyond human capacity while identifying novel attack vectors.
Sophisticated AI systems provide comprehensive security analysis through integration of multiple machine learning techniques and real-time threat intelligence.
Ensemble learning methods combine multiple AI models to achieve superior detection accuracy and robustness compared to individual approaches. Random Forest algorithms, gradient boosting models, and neural network ensembles provide complementary perspectives on security threats. Model fusion techniques integrate different AI approaches while uncertainty quantification provides confidence estimates for security assessments.
Reinforcement Learning agents develop optimal strategies for security testing and vulnerability discovery through interaction with smart contract environments. RL agents learn to identify effective attack strategies while adapting to defensive countermeasures. Policy optimization enables automated security testing that improves over time through experience.
Transfer learning techniques adapt AI models trained on one blockchain or programming language to analyze contracts in different environments. Pre-trained models leverage knowledge from Ethereum Solidity contracts to analyze Binance Smart Chain or other platforms. Cross-domain transfer learning reduces training requirements while improving detection accuracy across diverse blockchain ecosystems.
Adversarial training improves AI model robustness against evasion attacks where malicious actors attempt to hide vulnerabilities from automated analysis. Adversarial examples expose models to intentionally obfuscated vulnerable code that helps models learn to identify disguised security flaws. Robust models maintain effectiveness despite attempts to game automated security analysis.
Online learning systems continuously update AI models as new vulnerability data becomes available without requiring complete retraining. Streaming machine learning algorithms adapt to evolving threat landscapes while maintaining detection accuracy. Incremental learning enables real-time model improvement as new attack techniques emerge.
AI systems provide forward-looking security capabilities that predict threats before they manifest and enable proactive protective measures.
Threat prediction models forecast likely attack targets and timing based on analysis of contract characteristics, market conditions, and historical attack patterns. Predictive systems consider factors like total value locked, contract complexity, and recent vulnerability disclosures to assess attack probability. Risk scoring enables prioritized security focus on highest-risk protocols.
Attack simulation engines use AI to generate realistic attack scenarios for testing contract defenses under various threat conditions. Simulation systems create synthetic attacks that test security measures while providing training data for detection systems. Automated simulation enables comprehensive security testing across numerous attack possibilities.
Early warning systems detect precursor activities that often precede major attacks including unusual contract deployments, suspicious wallet activity, and coordination patterns among potential attackers. Machine learning models identify leading indicators that suggest attack preparation while providing time for defensive measures.
Vulnerability trend analysis uses machine learning to identify evolving patterns in smart contract vulnerabilities and predict future security challenges. Trend analysis reveals how attack techniques evolve over time while predicting likely directions for future threat development. Proactive trend analysis guides security research priorities.
Adaptive defense systems automatically adjust security measures based on AI-assessed threat levels and attack patterns. Dynamic systems can modify monitoring sensitivity, adjust access controls, or implement additional protective measures based on machine learning risk assessment. Adaptive responses provide proportional security that scales with threat levels.
Practical implementation of AI-powered security requires careful system design, data management, and integration with existing security infrastructure.
Data pipeline architecture handles the massive data volumes required for effective machine learning including blockchain transaction data, contract source code, and vulnerability databases. Pipeline systems manage data collection, preprocessing, feature extraction, and model training while maintaining data quality and consistency. Efficient pipelines enable real-time AI analysis at blockchain scale.
Model deployment infrastructure enables real-time AI analysis of smart contract activity through scalable cloud computing and edge deployment strategies. Deployment systems handle model serving, load balancing, and failover procedures while maintaining low latency for time-critical security applications. Production deployment requires robust infrastructure for continuous AI operation.
Explainable AI techniques provide insights into model decision-making to help security teams understand why specific threats were flagged or vulnerabilities identified. Model interpretability is crucial for security applications where users need to understand and trust automated findings. Explainable systems facilitate debugging and improvement of AI security tools.
Human-AI collaboration frameworks integrate machine learning insights with human expertise to optimize security analysis and decision-making. Collaborative systems leverage both artificial intelligence pattern recognition and human understanding of attack motivation and context. Hybrid approaches achieve better results than purely automated or manual security analysis.
Continuous validation systems ensure AI models maintain accuracy and reliability over time through automated testing, performance monitoring, and model drift detection. Validation frameworks identify when models require retraining or adjustment while ensuring consistent security analysis quality. Continuous monitoring prevents security tool degradation over time.
AI-powered security analysis requires significant technical infrastructure and machine learning expertise but provides capabilities for threat detection and vulnerability discovery that traditional approaches cannot match, enabling proactive security measures and automated analysis at the scale and speed required for comprehensive smart contract protection.
We've covered a lot of ground, from identifying common vulnerabilities to building a full-blown security lifecycle. Think of it as a defense-in-depth strategy for your smart contracts. Real security isn't a one-and-done checklist; it’s an ongoing commitment that starts the moment you write your first line of code.
Here is an actionable summary of the layers of a robust security strategy:
Security LayerKey ActionWhy It's Crucial1. Secure DesignConduct thorough threat modeling before coding.Prevents vulnerabilities from being built into the core logic.2. Secure CodingFollow best practices like Checks-Effects-Interactions and use standard libraries.Minimizes common bugs and exploits at the source code level.3. Rigorous TestingImplement unit, integration, and fuzz testing.Catches bugs and edge cases before they can be exploited.4. External AuditsHire reputable third-party firms to review your entire codebase.Provides an unbiased, expert opinion to uncover blind spots.5. Bug BountiesLaunch a public program to incentivize ethical hackers to find flaws.Offers continuous security testing by a global pool of talent.6. Real-Time MonitoringUse on-chain monitoring tools to detect threats 24/7 post-deployment.Enables active defense and rapid response to attacks as they happen.
Smart contract security is not about writing perfect code once; it's about creating a durable system that can anticipate, detect, and respond to threats in a constantly evolving environment.
When you adopt this mindset, you’re doing more than just shipping code. You're building trust with your users, protecting their funds, and proving your protocol can be relied on. Use these principles as a lens to examine your own practices and find where you can make them stronger. This is how you build applications that last and contribute to a safer, more dependable decentralized world for everyone.
Got questions about smart contract security? You're in the right place. Here are some straightforward answers to the things developers and investors ask most.
If I had to pick just one, it’s embracing a "defense-in-depth" mindset. It's a strategy where you never, ever rely on a single security measure. Think of it like securing a castle: you need a moat, high walls, guards, and a locked keep. One layer alone won't cut it.
The process starts with clean, simple code, leaning on battle-tested libraries like OpenZeppelin. From there, you layer on a comprehensive test suite and get at least one professional third-party audit before you even think about deploying. And once you're live? Real-time on-chain monitoring is your final line of defense. Just getting an audit and calling it a day is one of the biggest mistakes teams make; smart contract security is a continuous process, not a one-time task.
Security isn't a product you buy; it's a process you live. In the world of unchangeable contracts, this thinking is everything. An audit gives you a snapshot in time, but continuous monitoring is the live video feed you need.
Figuring out if a project is safe as a user or investor takes a bit of digging, but there are some clear signs that a team is serious about protecting its users.
Actionable Due Diligence Checklist for Users:
Honestly, security is less about the blockchain itself and more about the quality of the code running on it. Sure, a mature blockchain like Ethereum has fantastic developer tools and a huge community of security researchers, but vulnerabilities almost always come down to bad logic in the code.
A poorly written Solidity contract is going to be a ticking time bomb on any EVM-compatible chain, whether that's Ethereum, Polygon, or BSC. The fundamental rules of secure coding, intense testing, and professional audits are universal. They apply everywhere, making the diligence of the developer the real factor that determines a contract's safety.
Formal verification transforms probabilistic security assessment into mathematical proof through sophisticated theorem proving and model checking techniques that provide absolute certainty about security properties. Theorem proving systems like Coq, Isabelle/HOL, and Lean enable developers to write mathematical proofs that smart contracts satisfy invariants like "user balances never decrease without authorization" or "total supply remains constant across operations." Interactive proof development guides logical reasoning while automated tactics handle routine verification tasks. Model checking algorithms systematically explore all possible execution paths using tools like TLA+, SPIN, and NuSMV to verify temporal logic specifications hold under every conceivable scenario, providing mathematical proof across infinite execution possibilities rather than sampling-based testing. Specification languages like Dafny and Why3 provide formal notation for expressing function preconditions, postconditions, and invariants that prevent entire vulnerability classes. Contract invariants define mathematical properties preserved throughout execution while temporal logic specifications express time-dependent security properties using Linear Temporal Logic and Computation Tree Logic. Abstract interpretation uses lattice theory and fixed-point analysis to capture security properties while symbolic execution with constraint solvers determines whether security violations are mathematically possible. Refinement verification establishes mathematical relationships between abstract specifications and concrete implementations, ensuring security properties are preserved during development. Program synthesis automatically generates provably secure implementations from formal specifications, eliminating implementation errors while guaranteeing mathematical security compliance.
AI-powered security analysis achieves 85-95% accuracy in vulnerability identification through deep learning neural networks trained on extensive vulnerability datasets that surpass human auditor capabilities for common vulnerability classes. Convolutional Neural Networks adapted for code analysis learn abstract representations of vulnerable patterns while Recurrent Neural Networks analyze sequential contract execution aspects and Graph Neural Networks model interaction patterns to identify complex vulnerabilities. Anomaly detection algorithms identify zero-day exploits through machine learning models trained on normal execution patterns that flag deviations suggesting malicious activity including unusual gas consumption, unexpected state changes, or abnormal transaction patterns. Natural Language Processing analyzes contract documentation and variable names to identify semantic security indicators while behavioral pattern recognition learns from historical attack data to predict emerging threats and likely targets. Automated vulnerability discovery uses machine learning to systematically generate and test exploit scenarios while learning from successful attempts. Ensemble learning combines Random Forest algorithms, gradient boosting models, and neural networks for superior detection accuracy while reinforcement learning agents develop optimal security testing strategies through environment interaction. Transfer learning adapts models across blockchain platforms while adversarial training improves robustness against evasion attacks where malicious actors attempt to hide vulnerabilities. Threat prediction models forecast attack targets and timing based on contract characteristics and historical patterns while attack simulation engines generate realistic scenarios for defense testing. Early warning systems detect precursor activities preceding major attacks while adaptive defense systems automatically adjust security measures based on AI threat assessment.
Decentralized security infrastructure eliminates single points of trust through blockchain-based audit verification that records findings and security assessments on immutable ledgers, providing transparent and tamper-proof documentation that enables public verification while preventing audit manipulation. Decentralized autonomous audit networks coordinate multiple independent security researchers through DAO-based systems that incentivize quality analysis via token rewards and consensus mechanisms for finding validation, reducing bias and improving coverage compared to single-firm approaches. Trustless bug bounty protocols automate vulnerability reporting, verification, and reward distribution through smart contracts that ensure automatic payment upon confirmation while providing transparent tracking without intermediary platforms. Cryptographic proof systems enable verifiable security claims where protocols prove specific properties without revealing implementation details through zero-knowledge proofs that demonstrate compliance while protecting intellectual property. Community-driven validation leverages collective intelligence through prediction markets, reputation systems, and crowd-sourced analysis that combines diverse expertise using market mechanisms for security assessment aggregation. Multi-party computation enables collaborative vulnerability analysis without revealing sensitive code while homomorphic encryption allows security analysis of encrypted contracts. Decentralized identity systems provide reputation tracking and credential verification for security researchers without centralized authority while consensus-based vulnerability assessment uses distributed voting to validate findings. Token economic models create appropriate incentive structures through staking mechanisms and reward distribution while governance protocols coordinate decision-making through decentralized autonomous organization structures. Quality assurance mechanisms maintain high standards through peer review and cross-validation while interoperability standards enable cross-chain security assessment consistency.
Economic security modeling provides systematic frameworks for understanding rational adversary behavior and designing incentive-compatible security mechanisms through game-theoretic analysis that considers participant payoffs and strategic interactions. Mechanism design principles create systems where rational participants have incentives for honest behavior even when acting in self-interest, aligning individual incentives with security objectives through careful analysis of information asymmetries and strategic behavior. Game-theoretic attack modeling analyzes vulnerabilities from profit-maximizing adversary perspectives that weigh attack costs including gas fees, opportunity costs, and detection risks against expected returns, enabling realistic threat assessment and security prioritization. Cost-benefit analysis evaluates attack economic rationality by comparing required resources against expected profits while considering technical expertise requirements, capital costs, and legal risks to understand attack economics for defense prioritization. Nash equilibrium analysis identifies stable strategic configurations where no participant has deviation incentives, predicting likely outcomes in multi-participant security scenarios while revealing whether mechanisms create stability or incentivize disruption. Security bonding mechanisms require economic stakes that can be slashed for violations, creating strong financial incentives for honest behavior through optimal stake requirements and slashing conditions. Prediction market security assessment uses market mechanisms for continuous protocol evaluation through crowd-sourced intelligence and financial stakes that aggregate security risk information. Progressive security mechanisms automatically increase protection measures based on total value at risk, creating proportional protection that scales with economic attack incentives through adaptive confirmation requirements and consensus thresholds. Economic voting systems resist manipulation through analysis of voting costs, coalition formation, and strategic behavior while preventing vote buying and coordination attacks. Market-based security mechanisms including insurance markets and security bonds create self-regulating systems that harness collective intelligence and economic incentives for scalable security solutions without centralized control.
Ready to turn on-chain data into actionable trading signals? Wallet Finder.ai helps you discover profitable wallets and mirror their strategies in real time. Start your 7-day trial today and trade ahead of the market.