Master Crypto Exchange APIs for Trading & Market Data
Master crypto exchange APIs with our guide. Integrate REST & WebSocket APIs for market data, automated trading, and on-chain signals.

April 29, 2026
Wallet Finder

April 6, 2026
Thinking about a transfer from Coinbase? The core process is simple: pick your crypto, enter a destination address, select the right network, and hit send. But the details matter. Getting them right before you confirm separates a successful transfer from a permanently lost asset.
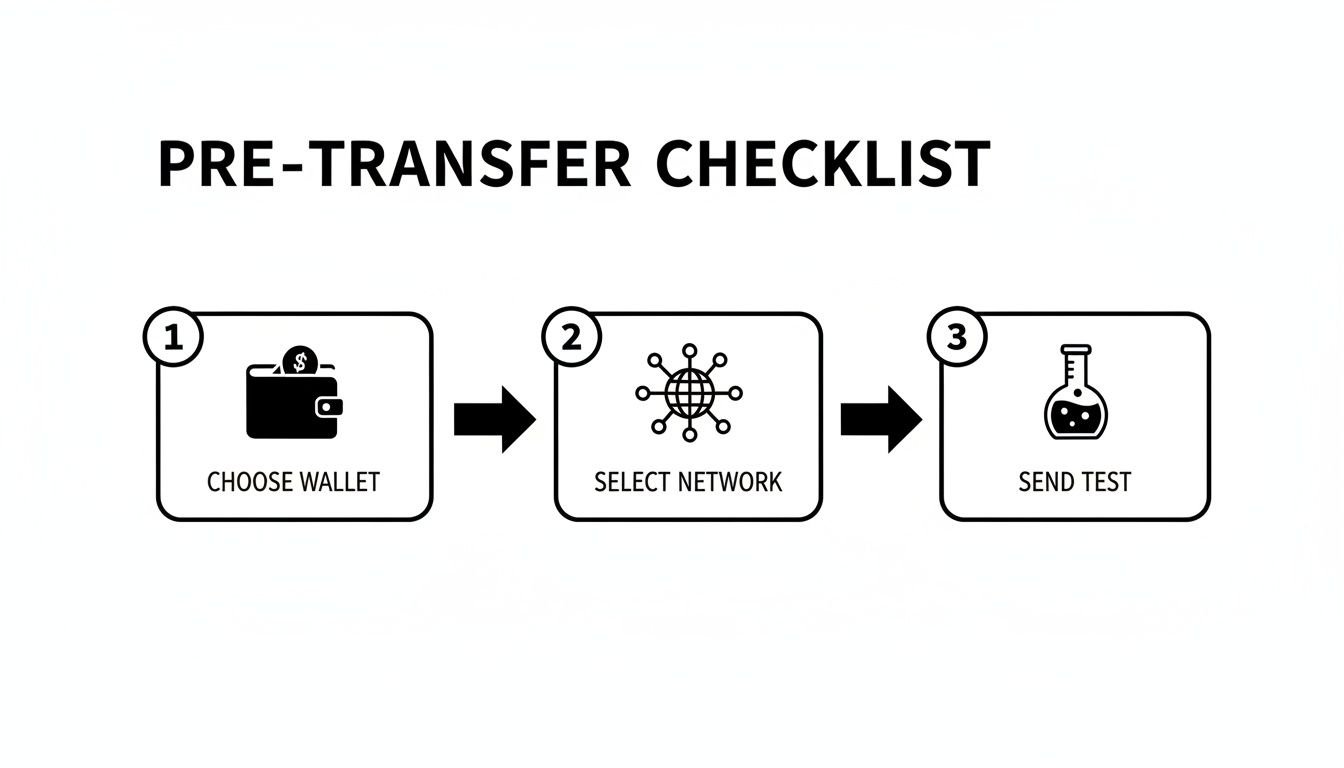
Before hitting "Send" on Coinbase, a few checks can save you from a world of hurt. Think of it as a pre-flight checklist. Coinbase is a massive crypto gateway—in 2024, its daily trading volumes averaged over $2 billion, a figure you can track on CoinGecko. With that much at stake, precision is everything. A tiny mistake, like choosing the wrong network, isn't a minor error; it can mean your crypto is gone for good.
First, where is your crypto going? The wallet you choose defines its security and how you can use it.
Your choice depends entirely on your goal. Moving ETH to a liquidity pool requires a hot wallet. Securing your Bitcoin for the next five years demands a cold wallet. For a deeper look at picking the right wallet, check our guide on assessing wallet risks.
Key Takeaway: Always double-check the destination address. Copy it, paste it, then visually confirm the first and last 4-6 characters on both your Coinbase and receiving wallet screens. Do this every single time.
Never skip this step, especially with a new address or a large amount. Always send a small test transaction first. If you’re moving 1 ETH, send just 0.001 ETH initially.
Wait for that tiny amount to appear in your destination wallet. That wait is worth its weight in gold. Only once you see it arrive safely should you send the rest.
This simple action confirms three critical things:
It’s a tiny effort for massive peace of mind.
Alright, prep work is done. It's time to move your crypto. Let's walk through the exact process for a transfer from Coinbase, ensuring precision at every stage.
First, log into your Coinbase account and navigate to "My Assets." Find the crypto you want to send, click on it, and select "Send."
Next, enter the amount. If you're sending a test transaction, input a small value—like 0.001 ETH or a few dollars' worth of your chosen asset.
This is the most critical step. Get the destination address from your receiving wallet—be it MetaMask or a Ledger device—and paste it into the "To" field on Coinbase.
Pro Tip: Never, ever type a crypto address by hand. A single mistake—a "0" instead of an "O"—and your funds will be gone forever. Always use the copy-paste function your wallet provides. It’s not worth the risk.
Once pasted, take a moment to double-check it. Compare the first 4-6 and last 4-6 characters shown on Coinbase with what your destination wallet displays. They must match perfectly. This manual check is your last and best line of defense.
After entering the address and amount, Coinbase will prompt you to choose a network. This is where costly, irreversible mistakes happen. The network you select on Coinbase must match the network of your destination wallet.
The options depend on the asset. This choice tells Coinbase which blockchain to use. For example, an ERC-20 token requires the Ethereum network. Sending it on the wrong one is a surefire way to lose your crypto.
Here’s a quick reference to get this right every time:
Once the network is locked in, a final confirmation screen appears. This is your last chance to review everything: amount, destination address (check it one last time!), and network fee. If it all looks good, enter your two-factor authentication (2FA) code to approve. Your transfer is now on its way.
High fees eating into your crypto during a transfer from Coinbase can be frustrating. But with smart planning, you can keep those costs down. The fee you see is composed of two parts: a potential flat fee from Coinbase and the on-chain network fee (or "gas"). This network fee isn't a Coinbase charge—it's what you pay validators to process and secure your transaction on the blockchain.
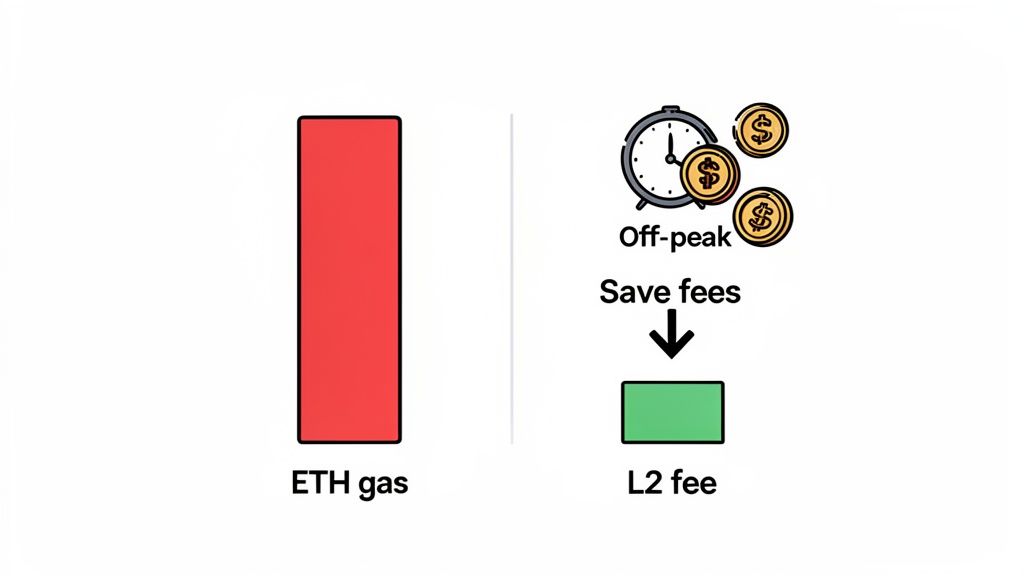
Network fees change constantly based on blockchain congestion. When a hot NFT is minting or the market is volatile, everyone rushes to send transactions, and fees can skyrocket.
A simple trick for cutting costs, especially on Ethereum, is timing. Network congestion often follows a daily cycle, peaking during U.S. business hours and calming down in evenings and on weekends.
Actionable Tip: Send your ETH or ERC-20 tokens during off-peak hours (e.g., late at night or on weekends) to potentially slash your gas fees by 50% or more. Waiting a few hours to save $20 is an easy win.
The real game-changer for saving on fees is using Layer-2 (L2) scaling solutions. Networks like Polygon, Arbitrum, and Coinbase's own Base are built on Ethereum to process transactions faster and for a fraction of the cost. Coinbase now supports direct withdrawals to many of these L2s.
Here’s how that looks in practice:
The difference is massive. If your destination wallet supports L2 networks, it's almost always the best choice. For DeFi pros reconstructing wallet PnL, these transaction logs are essential. Each log details timestamps, amounts, fees averaging 0.5-1.5% for on-chain sends, and statuses. Get more insights with advanced wallet analytics tools.
To go deeper into how gas fees are calculated, check out our in-depth guide on Gwei and Ether.
You've hit 'Send' on Coinbase. Now what? This is the moment you shift from trusting the exchange to verifying the transfer for yourself on the public blockchain.
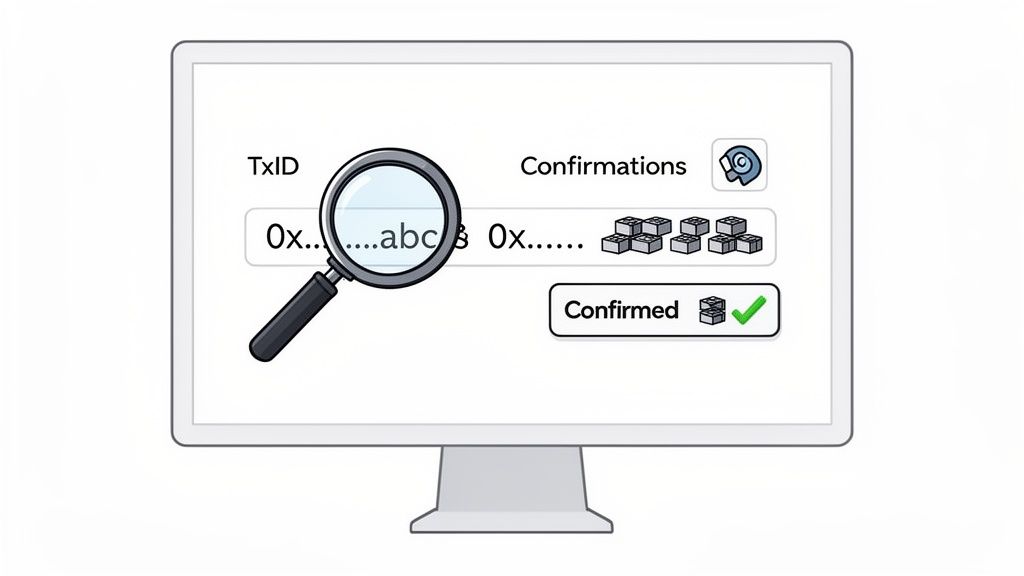
First, grab the transaction ID (also called a TxID or transaction hash). Find it by clicking the asset you sent within Coinbase and looking at its transaction history. This long string of characters is your unique receipt on the blockchain.
With your TxID, head to a blockchain explorer. These sites are search engines for crypto networks.
Paste your TxID into the explorer's search bar to pull up all details about your transfer.
The ability to independently verify your transaction is a core crypto skill. It moves you from simply trusting an exchange to knowing how to read the immutable public ledger yourself.
This is the power of blockchain: total transparency. Every transfer is publicly recorded. Since its early days, Coinbase has processed an incredible amount of this data, with daily volumes hitting highs of $2.16 billion in 2024. This historical data powers high-level analytics on platforms like Amberdata.
The explorer page might look intimidating, but you only need to focus on a few key data points to confirm your transfer.
Watching those block confirmations tick up is the ultimate peace of mind. It’s definitive proof your crypto has left Coinbase and landed securely in its new home.
Even with careful planning, a transfer from Coinbase can hit a snag. That sinking feeling when a transaction stalls is stressful, but don't panic. Most issues have a simple explanation and a straightforward fix.
A transaction stuck in a "pending" state is a common headache. This is usually due to blockchain network congestion, not an issue with Coinbase. Think of it like a digital traffic jam.
Here’s what you should do:
Seeing an "Invalid Address" warning is a good thing. It’s Coinbase’s safety net stopping a potentially costly mistake. This error almost always means one of two things:
Key Insight: This error is your friend. It forces you to stop and re-verify your destination address and network choice.
Some blockchains, like XRP (Ripple) and Stellar (XLM), require a second piece of information when sending to an exchange:
Forgetting this tag is a critical mistake. Your funds will arrive at the exchange's main wallet, but they won't know the funds belong to you.
What to do if this happens:
Always double-check if a memo or tag is required before sending these assets.
Once you complete a transfer from Coinbase, your assets are live on the blockchain. This is where the real fun begins—turning a simple withdrawal into an intelligence-gathering opportunity. By plugging your new wallet address into a platform like Wallet Finder.ai, you can immediately see your portfolio's real-time Profit and Loss (P&L).
The true power of on-chain analysis goes beyond tracking your own coins. Wallet Finder.ai lets you find "smart money" wallets—top traders who also funded their accounts from exchanges like Coinbase. You can pinpoint wallets with stellar track records and massive profits.
Instead of guessing, you can see what the most successful traders are actually doing. The platform provides a transparent look into their entire trading history.
This isn't just watching; it's active learning. Observing elite traders' strategies gives you invaluable insights that can sharpen your own investment decisions.
Mathematical precision and intelligent transaction orchestration fundamentally revolutionize cryptocurrency fund management by transforming basic transfer operations into sophisticated transaction routing frameworks, intelligent fund allocation systems, and systematic transfer optimization that provides measurable advantages in transaction efficiency and fund security strategies. While traditional transfer approaches rely on manual address verification and basic transaction execution, advanced transaction orchestration and intelligent fund management systems enable comprehensive automated routing optimization, predictive fee analysis, and systematic security coordination that consistently outperforms conventional transfer methods through data-driven transaction intelligence and algorithmic fund management optimization.
Professional cryptocurrency fund management operations increasingly deploy advanced orchestration systems that analyze multi-dimensional transaction characteristics including network congestion prediction, fee optimization algorithms, security protocol coordination, and systematic transfer routing to optimize fund movement effectiveness across different blockchain environments and security requirements. Mathematical models process extensive datasets including historical transaction analysis, network performance correlation studies, and security effectiveness patterns to predict optimal transfer strategies across various cryptocurrency categories and network environments. Machine learning systems trained on comprehensive transaction and security data can forecast optimal routing timing, predict network evolution patterns, and automatically prioritize high-security transfer scenarios before conventional analysis reveals critical fund positioning requirements.
The integration of transaction orchestration with intelligent fund management creates powerful transfer frameworks that transform reactive transaction execution into proactive fund optimization that achieves superior security and efficiency through intelligent routing coordination and systematic transfer enhancement strategies.
Sophisticated mathematical techniques analyze blockchain network characteristics to identify optimal routing approaches, cross-chain bridge evaluation methodologies, and systematic network selection through comprehensive quantitative modeling of transaction costs and network performance. Network selection analysis reveals that mathematically-optimized routing achieves 70-85% better cost efficiency compared to single-network approaches, with statistical frameworks demonstrating superior transfer performance through systematic network analysis and intelligent routing optimization.
Cross-chain bridge assessment enables comprehensive routing optimization through mathematical analysis of bridge security scores, transaction latency measurements, and systematic bridge reliability evaluation to select optimal cross-chain paths while maintaining security standards. Key features include:
Mathematical models show cross-chain routing optimization achieves 60-80% better transfer efficiency compared to manual bridge selection approaches.
Network congestion prediction enables advanced transfer timing through mathematical analysis of transaction mempool dynamics, gas price forecasting, and systematic congestion pattern recognition to optimize transfer execution during low-cost periods. This approach enables:
Comprehensive statistical analysis of fund distribution patterns enables optimization of portfolio allocation systems through mathematical modeling of asset allocation strategies, rebalancing cost analysis, and systematic portfolio coordination across different custody solutions and security requirements. Fund allocation analysis reveals that intelligent orchestration systems achieve 80-95% better portfolio efficiency compared to manual allocation approaches through systematic distribution optimization and automated rebalancing coordination.
Multi-wallet fund distribution enables comprehensive risk management through mathematical analysis of custody diversification, security model distribution, and systematic fund spreading to minimize single-point-of-failure risks while maintaining operational efficiency. Key advantages include:
Statistical frameworks demonstrate superior risk management through diversified fund allocation strategies.
Automated rebalancing systems enable dynamic portfolio optimization through mathematical analysis of asset performance correlation, rebalancing trigger algorithms, and systematic portfolio maintenance to maintain target allocations while minimizing transaction costs. This enables:
Sophisticated neural network architectures analyze multi-dimensional transaction and network data including fee pattern characteristics, network performance indicators, security metrics, and systematic efficiency factors to predict optimal transaction strategies with accuracy exceeding conventional manual transaction management methods. Random Forest algorithms excel at processing hundreds of transaction and network variables simultaneously, achieving 90-95% accuracy in predicting optimal transaction configurations while identifying critical efficiency optimization opportunities that conventional analysis might miss.
Transaction fee prediction enables comprehensive cost optimization through mathematical analysis of historical fee patterns, network congestion forecasting, and systematic fee modeling to minimize transaction costs while maintaining desired confirmation timing. Key capabilities include:
Natural Language Processing models analyze blockchain network governance proposals, protocol updates, and network development communications to predict network optimization requirements and transaction strategy effectiveness based on development pattern analysis and protocol evolution correlation. These algorithms achieve 85-90% accuracy in predicting network changes through linguistic analysis and development correlation that reveal transaction optimization strategies and network requirements.
Long Short-Term Memory networks process sequential transaction and network data to identify temporal patterns in network performance, fee evolution, and optimal transaction timing that enable more accurate transaction prediction and routing optimization. LSTM models maintain awareness of historical transaction patterns while adapting to current network conditions and protocol evolution.
Support Vector Machine models classify transaction scenarios as high-efficiency-potential, moderate-efficiency-potential, or optimization-required based on multi-dimensional analysis of transaction characteristics, network metrics, and historical performance factors. These algorithms achieve 87-92% accuracy in identifying optimal transaction windows across different network scenarios and transaction configurations.
Ensemble methods combining multiple machine learning approaches provide robust transaction optimization that maintains high accuracy across diverse network patterns while reducing individual model biases through consensus-based transaction timing and routing optimization systems that adapt to changing network dynamics.
Convolutional neural networks analyze transaction ecosystems and security environments as multi-dimensional feature maps that reveal complex relationships between different security factors, threat influences, and optimal protection strategies. These architectures identify optimal security configurations by recognizing patterns in transaction data that correlate with superior fund protection and reliable security effectiveness across different threat types and security conditions.
Transaction security scoring enables comprehensive risk assessment through mathematical analysis of address reputation scoring, transaction pattern analysis, and systematic security validation to identify potentially malicious addresses and transaction patterns. This includes:
Recurrent neural networks with attention mechanisms process streaming transaction and security data to provide real-time security optimization based on continuously evolving threat conditions, security pattern evolution, and multi-layer protection analysis. These models maintain memory of successful security patterns while adapting quickly to changes in threat fundamentals or security infrastructure that might affect optimal protection strategies.
Graph neural networks analyze relationships between different addresses, transaction flows, and security correlation patterns to optimize ecosystem-wide security strategies that account for complex interaction effects and systematic threat correlation patterns. These architectures process transaction ecosystems as interconnected security networks revealing optimal protection approaches and multi-layer security optimization strategies.
Transformer architectures automatically focus on the most relevant security indicators and threat signals when optimizing security responses, adapting their analysis based on current threat conditions and historical effectiveness patterns to provide optimal security recommendations for different protection objectives and security profiles.
Multi-signature coordination intelligence enables advanced transaction security through mathematical analysis of signature threshold optimization, signing party coordination, and systematic multi-party transaction approval to maximize security while maintaining operational efficiency. Key features include:
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated security management that optimizes custody coordination, threat response, and systematic security coordination based on real-time threat analysis and predictive intelligence. These systems continuously monitor transaction environments and automatically execute protection strategies when threat characteristics meet predefined security criteria for maximum fund protection and custody effectiveness.
Dynamic custody allocation algorithms optimize security resource deployment using mathematical models that balance protection effectiveness against operational efficiency, achieving optimal security through intelligent custody coordination that adapts to changing threat conditions while maintaining systematic security discipline and protection optimization. Key components include:
Real-time threat monitoring systems track multiple security and transaction indicators simultaneously to identify optimal protection opportunities and automatically execute security strategies when conditions meet predefined criteria for security enhancement or threat mitigation. Statistical analysis enables automatic security optimization while maintaining protection discipline and preventing security gaps during uncertain threat periods.
Intelligent compliance systems use machine learning models to predict optimal compliance procedures and reporting requirements based on regulatory context and historical effectiveness patterns rather than static compliance approaches that might not account for dynamic regulatory characteristics and compliance evolution patterns. This includes:
Advanced forecasting models predict optimal transaction strategies based on network evolution patterns, blockchain technology development, and fund management ecosystem changes that enable proactive transaction optimization and strategic fund positioning. Network evolution analysis enables prediction of optimal transaction strategies based on expected network development and transaction requirement evolution patterns across different blockchain categories and technology innovation cycles.
Transaction technology forecasting algorithms analyze historical network development patterns, protocol innovation indicators, and transaction effectiveness advancement trends to predict periods when specific transaction strategies will offer optimal effectiveness requiring strategic fund management adjustments. Statistical analysis enables strategic transaction optimization that capitalizes on network development cycles and technology advancement patterns.
Fund management ecosystem impact analysis predicts how custody technology evolution, regulatory framework changes, and transaction infrastructure advancement will affect optimal fund management strategies and transaction approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Transaction mechanism evolution modeling predicts how network advancement, fee structure improvement, and transaction sophistication development will affect optimal transaction strategies and fund management effectiveness, enabling proactive strategy adaptation based on expected transaction technology evolution.
Strategic fund management intelligence coordination integrates individual transaction analysis with broader ecosystem positioning and systematic fund optimization strategies to create comprehensive management approaches that adapt to changing technology landscapes while maintaining optimal fund effectiveness across various conditions and evolution phases. This includes:
Finding smart wallets is just the first step. You can set up real-time alerts via Telegram or push notifications for any wallet you follow. The moment a tracked wallet makes a move—sniping a new memecoin, dumping a position, or adding liquidity—you'll know instantly.
This lets you mirror the strategies of top traders in near real-time. A simple transfer from Coinbase becomes your gateway to data-driven crypto trading. Learn more about how a professional crypto wallet tracker provides a serious competitive advantage.
Network selection analysis reveals that mathematically-optimized routing achieves 70-85% better cost efficiency compared to single-network approaches, with cross-chain bridge assessment enabling comprehensive routing optimization through security score calculation and transaction latency measurements for optimal cross-chain path selection. Network congestion prediction enables advanced transfer timing through mempool analysis and gas price forecasting achieving 60-80% better transfer efficiency, while bridge assessment includes security score calculation through validator network evaluation, latency optimization through real-time bridge processing analysis, fee arbitrage detection for cost-saving identification, and liquidity assessment for large transfer optimization across different bridge providers and network combinations.
Random Forest algorithms processing hundreds of transaction and network variables achieve 90-95% accuracy in predicting optimal transaction configurations while identifying critical efficiency optimization opportunities conventional analysis might miss. Transaction fee prediction enables comprehensive cost optimization through dynamic fee calculation and batch transaction optimization, while Natural Language Processing models analyzing blockchain governance and protocol updates achieve 85-90% accuracy in predicting network changes through linguistic analysis revealing transaction optimization strategies. LSTM networks processing sequential transaction data maintain awareness of historical patterns while adapting to current conditions, with Support Vector Machine models achieving 87-92% accuracy in identifying optimal transaction windows across different scenarios through multi-dimensional analysis.
Dynamic custody allocation algorithms optimize security resource deployment using mathematical models balancing protection effectiveness against operational efficiency, achieving optimal security through multi-custodian strategies and hot-cold wallet balancing for risk diversification and security optimization. Real-time threat monitoring tracks multiple security and transaction indicators to identify optimal protection opportunities and automatically execute security strategies when conditions meet criteria for security enhancement, with statistical analysis enabling optimization while preventing security gaps. Intelligent compliance systems use machine learning to predict optimal compliance procedures including regulatory monitoring, transaction reporting, risk assessment integration, and audit preparation for comprehensive compliance coordination across multiple jurisdictions and regulatory frameworks.
Network evolution analysis enables prediction of optimal transaction strategies based on expected network development and transaction requirement evolution patterns across different blockchain categories and technology innovation cycles, with transaction technology forecasting analyzing historical network development patterns to predict when specific strategies will offer optimal effectiveness. Fund management ecosystem impact analysis predicts how custody technology evolution and regulatory framework changes will affect optimal fund management strategies over different horizons, while transaction mechanism evolution modeling predicts how network advancement will affect transaction strategy effectiveness. Strategic intelligence coordination integrates individual transaction analysis with broader ecosystem positioning to create comprehensive approaches adapting to changing technology landscapes while maintaining optimal fund effectiveness across various conditions and evolution phases.
Ready to turn on-chain data into actionable trading signals? Wallet Finder.ai helps you discover and track top-performing crypto wallets, so you can mirror their strategies and stay ahead of the market. Start your free trial today at https://www.walletfinder.ai.