Private Key Security: The Ultimate Trader's Guide
Master private key security with our guide for crypto traders. Learn to store keys, avoid attacks, and use advanced DeFi strategies to protect your assets.

May 22, 2026
Wallet Finder

March 11, 2026
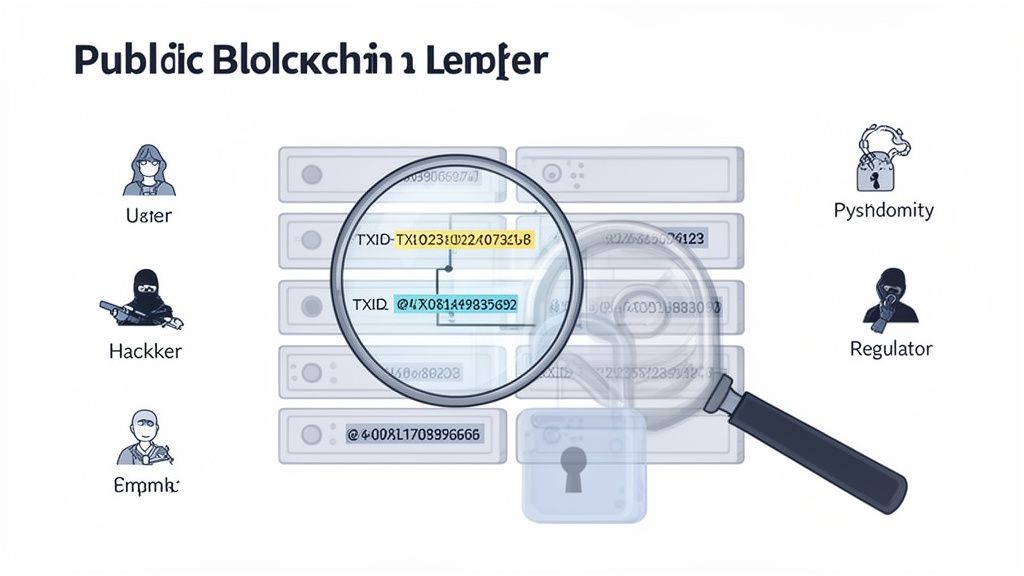
Crypto transaction tracking is the process of following digital currency as it moves across a public blockchain. Unlike the closed-off ledgers at your bank, blockchains are fundamentally transparent. This radical openness means anyone can view a permanent, unchangeable record of every transaction ever made, making it possible to trace the path of funds from one digital wallet to another.
Many newcomers get tripped up by the idea that crypto is completely anonymous. It's a common myth.
In reality, most major blockchains like Bitcoin and Ethereum are pseudonymous, not anonymous. This is a crucial distinction. While your real name isn't directly stamped onto your wallet, every single action you take leaves a permanent, public footprint on the ledger.
Think of the blockchain as a giant, public book of accounts that anyone in the world can open and read. Every transfer is a new line item, plain as day. This unlocks a massive opportunity to analyze financial flows, a practice we call on-chain analysis. If you want to go deeper, our guide on on-chain analysis breaks down how to read these market-moving signals.
The ability to follow digital money isn't just a neat technical trick; it's a critical skill in today's financial world. This transparency is a double-edged sword, creating privacy challenges while also offering huge benefits across several key areas:
The core challenge in crypto isn’t whether you can see the transactions—it’s about understanding what those transactions actually mean. By decoding the public ledger, we turn raw data into actionable intelligence.
To start tracking, you first need to understand the basic breadcrumbs every transaction leaves behind. These components are the building blocks of any investigation, allowing you to piece together the story of how and where the money moved.
This table breaks down the essential elements you'll encounter when analyzing a crypto transaction, helping you decode the data you see on any blockchain explorer.
Every crypto transaction leaves three essential pieces of information on the public ledger, and understanding what each one tells you is the foundation of any tracking or investigation work.
The transaction ID, commonly referred to as the TXID, is a unique alphanumeric string generated at the moment a transaction is broadcast to the network. It functions as an immutable receipt, permanently identifying that specific transfer and no other. The closest real-world equivalent is a package tracking number: just as a courier assigns a unique code to each shipment that allows anyone to look up its status and movement history, the TXID gives anyone the ability to pull up the complete details of a specific transaction at any time.
The wallet address is the public identifier that sends or receives funds in a transaction. It carries no personal information on its own, but it serves as the consistent anchor point that links all of a participant's on-chain activity together over time. The analogy is an email address: you can share it freely with anyone who needs to send you something, and anyone who knows it can see the messages sent to and from it, but the address itself does not reveal who you are in the physical world.
The blockchain explorer is the tool that makes the first two components accessible and interpretable. It is a publicly available website or application that indexes every transaction ever recorded on a specific blockchain, allowing anyone to search by TXID, wallet address, or block number and retrieve the associated data in a readable format. If the blockchain is the database, the explorer is the search engine that lets you query it without needing any technical infrastructure of your own.
Mastering crypto transaction tracking really just comes down to learning how to connect these pieces. You can start with a single transaction ID or wallet address and use a blockchain explorer to follow the money, uncovering a whole network of interconnected activity. This skill demystifies the blockchain and reveals the powerful stories hidden in its data.
Not all blockchains are built the same, which means the breadcrumb trails they leave behind look very different. If you want to get good at crypto transaction tracking, you first have to understand the unique accounting models of the major networks.
Each one demands a slightly different approach, kind of like a detective using different methods to track footprints in sand versus snow.
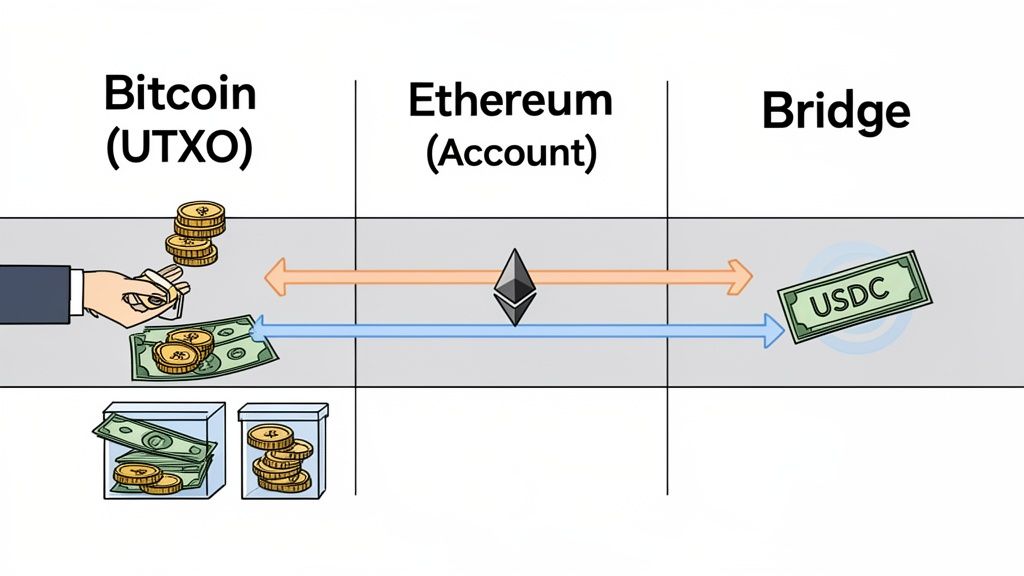
Let’s start with the original: Bitcoin. It runs on a system called the Unspent Transaction Output (UTXO) model. The easiest way to picture this is to think about physical cash.
When you use a $20 bill to buy a $5 coffee, you don’t get three-quarters of that same bill back. Instead, you get $15 in completely new bills and coins as change. Bitcoin works the exact same way. Every transaction consumes old UTXOs (the inputs) and creates brand new ones (the outputs)—one output goes to the person you're paying, and the other comes back to you as "change." This creates a complex, branching chain of transactions that analysts have to carefully piece together.
On the flip side, blockchains like Ethereum, Solana, and Base use a much more intuitive account-based model. This system works a lot more like a traditional bank account, making it far simpler to follow.
Instead of juggling inputs and outputs, every wallet just has a single balance. When you send funds, your balance goes down, and the recipient's balance goes up. Simple as that. This creates a direct, linear flow between addresses, which makes basic crypto transaction tracking much more straightforward than on Bitcoin.
This model is a game-changer when you’re tracking interactions with smart contracts—the automated programs that power DeFi. You can follow assets as they move from a user's wallet straight into a lending protocol and see exactly what happens next, whether they're being swapped, staked, or loaned out.
Within all these ecosystems, stablecoins like USDC and USDT have become the star players for anyone tracking funds. Because their value is pegged to a currency like the US dollar, they're used for everything from sending money across borders to trading in DeFi. All that activity creates a massive, clear, and easily traceable river of financial flow.
Their stability makes them a favorite for both legitimate businesses and shady actors trying to move money without worrying about price swings. This has caused their usage to absolutely explode.
In recent years, stablecoin transaction volumes have skyrocketed. They hit a record annual volume of over $4 trillion in just seven months, which is 30% of all on-chain crypto transaction volume. This explosion in trackable activity shows just how critical these dollar-pegged assets have become to the global flow of crypto. You can dive deeper into this trend in the full 2025 crypto adoption and stablecoin usage report from TRM Labs.
Things get really tricky when funds "jump" between different blockchains. This happens using tools called crypto bridges, which let someone lock an asset on one chain (like Ethereum) and get a "wrapped" version of it on another (like Solana).
This process completely breaks the trail you were following on a single ledger, creating a huge headache for analysts. An investigation that started on one blockchain suddenly hits a dead end, forcing you to pivot your entire strategy.
To connect the dots across chains, you have to:
This is a highly specialized skill that requires a deep understanding of how these bridges tick. If you're serious about mastering it, check out our dedicated guide on how to analyze cross-chain bridge transactions. By getting a handle on these different blockchain structures, you'll be able to follow the money no matter where it leads.
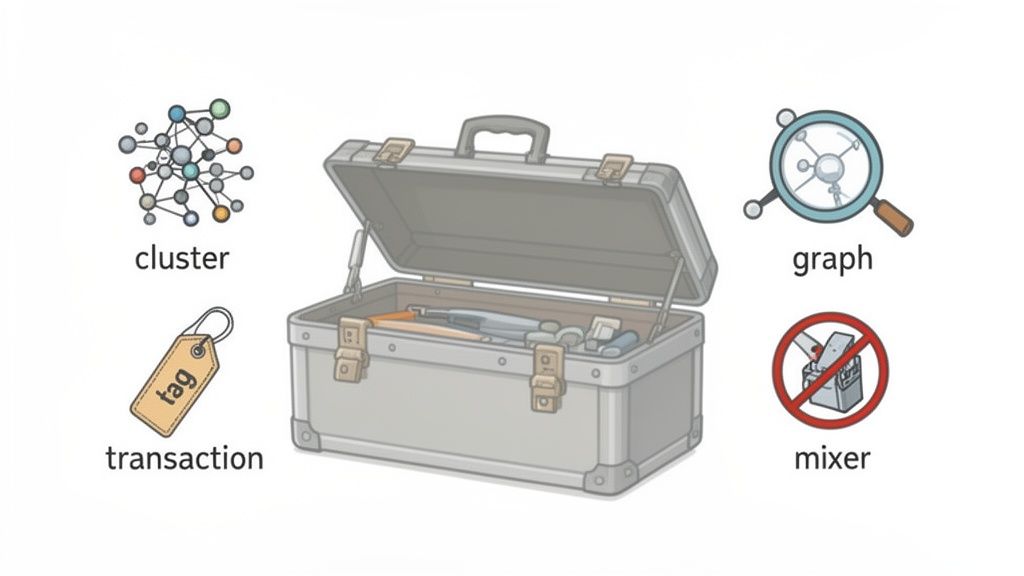
To make sense of the blockchain, analysts have a core set of techniques they turn to again and again. These are the clever rules of thumb—or heuristics—that help them connect the dots. Think of these methods as the fundamental tools in a blockchain detective's kit, turning raw, pseudonymous data into a story that reveals patterns you’d otherwise miss.
The most foundational technique is known as clustering. This is simply the process of grouping multiple blockchain addresses together with the assumption that they're all controlled by the same person or entity. It’s easily one of the most powerful concepts in crypto transaction tracking.
So, how do analysts know which addresses to group together? They use established heuristics based on common wallet behaviors. One of the most reliable is the co-spend heuristic, which assumes that if multiple addresses are used as inputs in a single transaction, they are probably controlled by the same wallet software—and by extension, the same owner.
Another key method is identifying common change address patterns. As we covered with Bitcoin's UTXO model, every transaction can create "change." A sharp analyst can often spot these change outputs, linking them back to the original sender and expanding their cluster of known addresses.
At its core, clustering transforms a chaotic sea of individual addresses into a manageable map of entities. Instead of tracking a hundred separate wallets, an analyst can now follow a single, consolidated actor across the blockchain.
Once a cluster starts taking shape, the next step is often address tagging. This is where analysts enrich the on-chain data with real-world intelligence. Blockchain analytics firms and the wider crypto community work to label, or "tag," addresses and clusters that are verifiably linked to known entities.
These tags provide crucial context, instantly clarifying what a transaction is all about.
This collaborative labeling effort turns a meaningless string of characters into a rich data point, dramatically speeding up any investigation.
With clusters identified and addresses tagged, analysts often turn to transaction graph analysis. This technique involves creating a visual map of how funds are moving between different entities. Instead of staring at a long list of transactions, a graph shows wallets as nodes and transactions as the lines connecting them.
This visual approach makes it much easier to spot complex money laundering patterns, such as:
Of course, bad actors are always trying to break the chain of custody using obfuscation tools. The most common are mixers (also called tumblers) and privacy coins. Mixers like Tornado Cash pool funds from tons of different users, jumble them all together, and then distribute them to new addresses, making direct tracing a nightmare.
However, advanced analytics can still pierce this veil. Analysts can use statistical analysis to calculate the probability that funds coming out of a mixer are linked to a specific deposit. For a detailed breakdown of these advanced methods, you can learn more by detecting crypto mixer transactions in our dedicated guide. Likewise, while privacy coins like Monero are designed for anonymity, tracing efforts focus on the on-ramps and off-ramps—where they are exchanged for more transparent assets.
Transaction timestamps are permanent blockchain records most analysts ignore for privacy analysis. But consistent activity patterns across thousands of transactions create geographic fingerprints that reveal wallet owners' locations with shocking precision. The blockchain timestamp isn't just when a transaction happened — it's a permanent record of when someone was awake and active.
Automated analysis tools plot transaction times for a target wallet over weeks or months. If activity consistently clusters between 14:00-22:00 UTC, the wallet owner is likely in US Eastern timezone. Activity clustering 21:00-05:00 UTC suggests Asia-Pacific. This geographic deanonymization works even when users attempt other privacy measures.
The analysis examines transaction density across twenty-four-hour periods. A wallet making trades at 03:00, 07:00, 14:00, and 22:00 UTC over months shows no pattern. But a wallet consistently trading 15:00-23:00 UTC reveals the owner operates during waking hours in a specific timezone.
Weekend and holiday patterns strengthen geographic inference. US-based wallets often show reduced activity on Thanksgiving, July 4th, Christmas. European wallets quiet down for different holiday periods. Asian wallets exhibit distinct Spring Festival or Golden Week patterns.
Even attempts at randomization fail against large datasets. A user trying to obscure their timezone by executing some transactions at "random" 03:00 hours still shows overall density clustering around their actual waking hours across hundreds of data points.
When analyzing multiple wallets suspected of common ownership, synchronized time zones provide powerful confirmation. If Wallet A, Wallet B, and Wallet C all show activity clustering 16:00-24:00 UTC across different days and weeks, they're likely controlled by someone operating in US Central/Mountain timezone.
Daylight Saving Time transitions create even stronger signatures. US wallets shift activity patterns by one hour twice yearly. European wallets shift on different dates. Wallets controlled by someone in Arizona (no DST) never shift. This annual pattern over multi-year analysis becomes definitive geographic proof.
Sophisticated actors aware of this vulnerability use bots executing transactions at randomized times across all twenty-four hours. But true randomization is expensive (requires always-on automation) and creates other suspicious patterns (why is a "human trader" executing swaps at 04:00 local time three times weekly?).
The only reliable defense is complete transaction time randomization via automated systems. Schedule transactions to execute across all hours with uniform distribution, eliminating any timezone clustering. This requires delegating all trading to bots rather than manual execution.
Alternatively, use transaction batching where multiple actions accumulate offline then execute simultaneously at randomized future times. Instead of trading when you decide to trade, queue actions throughout the day and have a bot execute them at algorithmically-selected random times.
For ultimate protection, route transactions through systems operating in different timezones. Use a VPS in Asia to execute trades even though you're in North America. This creates misleading timezone signatures, though sophisticated analysts can detect the VPS usage through other means.
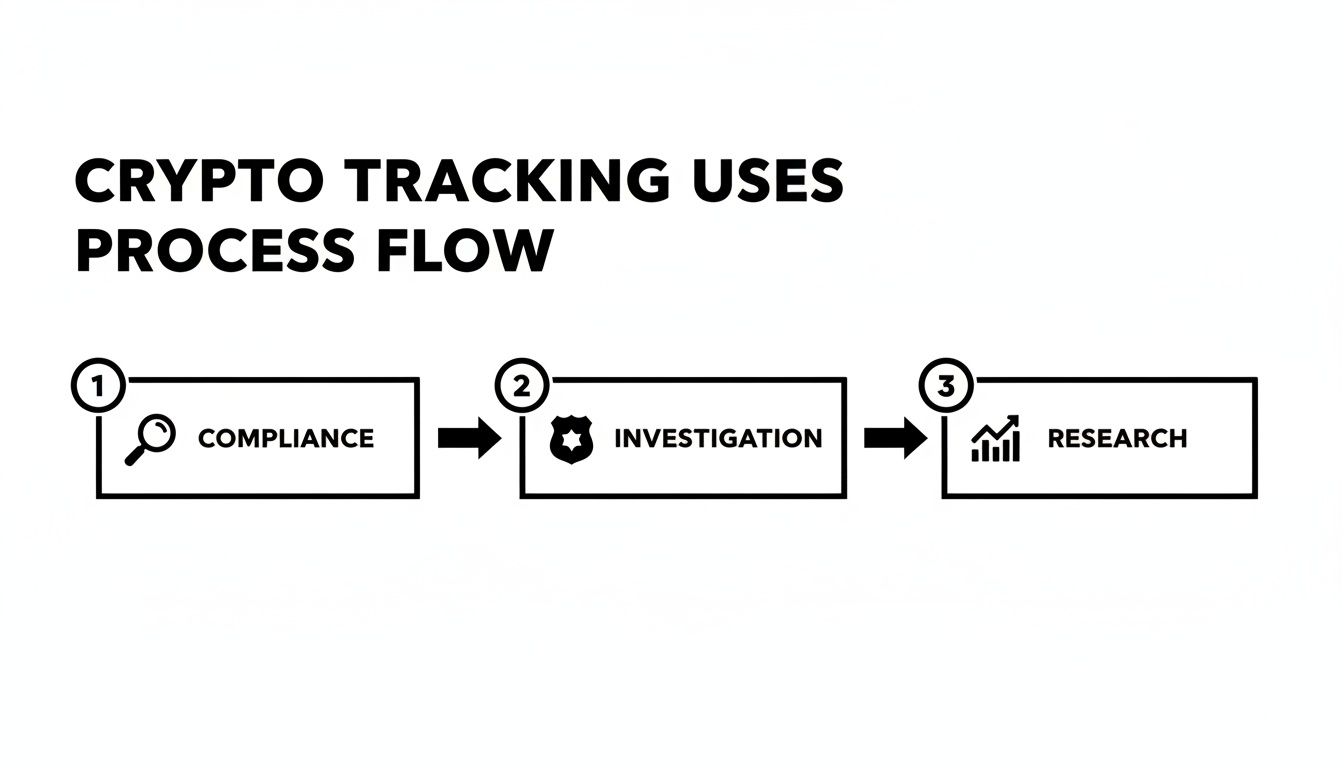
All the theory behind crypto transaction tracking is interesting, but where does the rubber meet the road? This is where abstract ideas like wallet clustering and heuristics turn into real-world results, impacting everything from billion-dollar investigations to your personal trading strategy.
These aren't just niche skills for on-chain detectives; they're fundamental to how the modern digital economy operates.
For any crypto exchange or business that wants to stay in business, a rock-solid Anti-Money Laundering (AML) program isn't just a nice-to-have—it's the law. Regulators demand that these platforms monitor transactions to stop criminals from using them to move dirty money. Transaction tracking is the engine that powers this entire effort.
Compliance teams use specialized software to automatically screen every single deposit. If someone tries to send in funds that came from a sanctioned address, a darknet market, or a known scammer's wallet, the system flags it in an instant. This lets the exchange freeze the funds, file a Suspicious Activity Report (SAR), and shut the door on bad actors.
Imagine an exchange gets an alert: a $50,000 deposit is just two "hops" away from a wallet tied to a ransomware crew. By tracing the money's path back, the compliance team can confirm the risk and act immediately, preventing those illicit funds from being laundered.
Transaction tracking is the critical bridge between what happens on the blockchain and what regulators require. It lets exchanges go beyond basic ID checks and actively police their platforms, which is essential for building trust across the entire crypto space.
When a big DeFi protocol gets hacked or a massive scam unravels, the first question everyone asks is, "Where did the money go?" Blockchain forensics is how we find the answer. Law enforcement and private investigators use transaction tracking to follow the digital breadcrumbs left by thieves in real-time.
Investigators build out detailed transaction graphs, creating a visual map of how the stolen assets are moving. They watch as hackers try to wash the funds through mixers, jump them across different blockchains using bridges, or swap them on decentralized exchanges. Even when criminals use incredibly complex methods to hide their tracks, they almost always slip up somewhere.
A typical forensic investigation looks something like this:
This exact process has been responsible for recovering billions of dollars in stolen crypto.
Dust attacks involve sending tiny amounts of crypto to many addresses to create transaction graph links. Most guides warn about receiving dust creating privacy risks. The deeper issue is how sophisticated analysts reverse this — using dust attacks to deanonymize the attackers themselves, not the victims.
When a dust attacker sends 0.0001 ETH to five thousand addresses, they create five thousand outbound transactions from their wallet. This spending pattern generates a massive, unique signature in the transaction graph. The attacker believes they're poisoning others' privacy. In reality, they've created the largest possible deanonymization surface for their own wallet.
Blockchain analysis identifies dust attacks by detecting: hundreds of identically-sized outbound transfers in rapid succession, tiny amounts (0.0001 ETH, 0.00001 BTC) sent to previously unrelated addresses, and funding source analysis showing the attacker's main wallet.
Once identified, the dust attacker's wallet becomes one of the most thoroughly documented addresses on the blockchain. Every transaction from that wallet before and after the attack is now connected to thousands of victim addresses, creating clustering opportunities the attacker never intended.
If any of those victim addresses were previously linked to exchanges, identified entities, or tagged wallets, those connections flow backward to the attacker. The attacker thought they were creating graph pollution. They actually created a massive dataset linking their wallet to thousands of previously unconnected graph nodes.
Analysts flip dust attack detection into attacker identification. They identify dust campaigns by signature pattern, trace back to the funding wallet, then analyze that wallet's entire transaction history. Where did the attacker's funding come from? Where do they send their non-dust transactions?
Many dust attackers fund their operations through privacy-conscious methods (mixers, peer-to-peer buys) but make mistakes elsewhere. They might send dust from a wallet that previously received exchange withdrawals. Or they consolidate dust wallets with their main operational wallet to reclaim gas fees. Each mistake creates deanonymization vectors.
The supreme irony: dust attacks attempting to pollute transaction graphs actually create some of the cleanest tracking datasets for identifying the attackers. A single dust campaign generates thousands of data points all tied to one source wallet, making that wallet trivial to analyze.
For would-be attackers (or anyone creating similar mass-distribution patterns like airdrops), never reuse distribution wallets for other purposes. Create a fresh wallet funded via mixer specifically for the distribution, execute once, then abandon.
Never consolidate dust or residual balances from distribution wallets back into main operational wallets. The consolidation transaction links the distribution wallet to your main wallet, connecting all those thousands of dust recipients to your real operations.
Use distinct gas funding sources for each distribution wallet. If you fund fifty distribution wallets from the same source, analysts cluster them instantly via common input heuristic. Each distribution should appear completely independent with no funding source overlap.
The smartest traders and investment funds use crypto transaction tracking to get a leg up on the competition. Because blockchains are public, the moves of the biggest players—the "whales"—are out there for anyone to see, if you know where to look.
By keeping an eye on the wallets of massive investors or venture capital firms, analysts can spot market-moving trends before they hit the headlines. For example, if a handful of major whale wallets all start scooping up a specific token, it might signal that good news is on the horizon or a big price move is coming. This strategy, often called "smart money tracking," helps traders see around the corner.
Transaction tracking also paints a clear picture of global crypto adoption, revealing which regions are growing fastest. According to a key index, India, the US, and Pakistan are leading the pack. We can also see institutional interest surging, with transfers over $1M in North America growing by a massive 49%. To see how on-chain data uncovers these global trends, check out the full 2025 Global Crypto Adoption Index from Chainalysis.
Before throwing money at a new crypto project, smart investors do their homework. A huge part of this due diligence involves digging into the project's on-chain financial records. By tracking the project's main treasury wallet, anyone can check if their actions match the promises made in their whitepaper.
Tracking can answer some very important questions:
This on-chain snooping offers a level of transparency you just can't get in traditional finance. It allows investors to verify a project's financial health right from the source of truth—the blockchain itself.
Centralized exchanges process withdrawals in batches to optimize gas costs. When an exchange executes a batch withdrawal, fifteen to fifty different users might receive their funds in a single transaction with multiple outputs. Users believe these separate addresses are anonymous. Blockchain analysis proves they all belong to customers of the same exchange — and often the same user.
The batching creates permanent on-chain evidence linking addresses that users thought were separate. If Address A and Address B appear together in an exchange withdrawal batch, they're both customers of that exchange. If they appear together in multiple batches over time, they're almost certainly the same user withdrawing to different wallets.
Analysts identify exchange batches by signature patterns: high output count (20-100 addresses receiving funds), specific output denominations favored by that exchange, gas price patterns matching the exchange's automated systems, and origination from known exchange hot wallets.
Once a batch is identified, all recipient addresses become associated. This creates clustering opportunities users never considered. They might use Address A for DeFi, Address B for trading, and Address C for HODL storage, believing these are separate. Appearing in the same withdrawal batch proves common ownership.
Repeated batch appearances strengthen clustering confidence. Address A and Address B receiving funds in the same Coinbase batch once might be coincidence. Both appearing in three different Coinbase batches over six months is definitive proof they're controlled by the same Coinbase account holder.
Sophisticated clustering extends across exchanges. If Address A appears in Coinbase batches and Address B appears in Binance batches, no direct link exists. But if both addresses later interact with the same DeFi protocol from the same IP address (via front-end analytics), they become clustered despite different exchange sources.
The clustering compounds when addresses bridge between exchanges. Address A withdraws from Coinbase, sends to Address B which deposits to Binance. Address B later withdraws from Binance to Address C. The batch appearance of A (from Coinbase) links to B's later batch appearance (from Binance), creating cross-exchange clustering chains.
The only protection is assuming all addresses appearing in the same exchange batch are permanently linked in analyst databases. If you need truly separate addresses, they must never receive funds from the same exchange in the same batch.
Spread withdrawals across time (days or weeks apart) to ensure they're processed in different batches. Same-day withdrawals from an exchange to multiple addresses will almost certainly batch together.
Use different exchanges for different wallets. Address A only ever withdraws from Coinbase. Address B only from Binance. Address C only from Kraken. This prevents batch-based clustering proving common ownership, though other behavioral patterns can still link them.
Alternatively, withdraw to a single address, then redistribute to final destination addresses in separate transactions hours or days later. This breaks the batch link because the redistribution isn't an exchange batch. However, it creates direct transaction graph links between the addresses, trading one deanonymization vector for another.
Most introductions to crypto transaction tracking focus on one-off investigations: find a wallet, trace a hack, follow a suspicious transfer. These are legitimate applications, but they represent only a fraction of what systematic tracking can do for an active investor or trader. The more powerful application is building a repeatable workflow that turns the blockchain's continuous data stream into ongoing market intelligence — a regular practice rather than a reactive investigation.
A tracking workflow is a structured routine for monitoring a defined set of wallet addresses and transaction patterns on a schedule, with clear criteria for what constitutes a signal worth acting on. The goal is not to watch everything all the time, which is neither practical nor productive, but to identify the specific on-chain behaviors that have historically preceded meaningful price moves and monitor for their recurrence.
The first step in building a workflow is selecting which wallets and entity types are worth tracking for your specific investment focus. Not all on-chain activity carries the same informational weight, and monitoring indiscriminately produces noise rather than signal.
For most investors, the highest-value addresses to monitor fall into three categories. The first is large individual wallets with a documented history of profitable positioning, sometimes called smart money wallets, whose transaction behavior has repeatedly preceded significant price moves in assets they accumulated. The second is protocol treasury wallets for projects you hold or are considering, whose spending patterns reveal genuine operational activity versus capital flight. The third is exchange deposit and withdrawal addresses for major centralized exchanges, whose net flow data reflects the aggregate behavior of large numbers of market participants and serves as a leading indicator of selling or accumulation pressure.
The practical starting point for most retail investors is a list of ten to twenty addresses across these three categories, narrow enough to monitor meaningfully but broad enough to generate useful signal diversity. As your familiarity with on-chain data grows, the list can expand and be refined based on which address categories have demonstrated the most consistent predictive value for the assets you trade.
The most common mistake in building a tracking workflow is starting to watch wallets before defining what you are watching for. Without pre-established signal criteria, you are not conducting analysis — you are pattern-matching after the fact, which reliably produces confirmation bias rather than actionable intelligence.
Signal criteria are the specific on-chain behaviors that, when observed in a monitored wallet, prompt you to investigate further or consider a position change. Useful criteria are precise and observable. Examples include a wallet that has been dormant for more than 60 days making its first significant outbound transfer, a cluster of previously unconnected smart money wallets simultaneously accumulating the same asset within a 48-hour window, or a protocol treasury wallet moving a large percentage of its stablecoin holdings to a centralized exchange deposit address.
Each of these criteria describes a specific, measurable on-chain event that is meaningful because of the behavior pattern it represents. Dormant wallet activation suggests a long-term holder has made a deliberate decision to act. Coordinated accumulation across unconnected wallets suggests independent convergence on the same thesis. Treasury-to-exchange transfers suggest an intent to liquidate. Defining these criteria in advance means that when you observe them, you have a clear basis for deciding what they imply rather than improvising an interpretation in the moment.
A tracking workflow produces value over time only if it is documented. Without records, you cannot evaluate whether your signal criteria are actually predictive, which ones generate false positives most frequently, or how your response to signals affected your outcomes. Documentation is what transforms a collection of observations into a learning system.
The minimum viable documentation for each signal event includes the wallet address that generated the signal, the specific transaction or pattern that triggered it, the date and the asset price at the time of observation, your interpretation of what the signal implied, any position you took in response, and the subsequent price outcome over a defined evaluation window. Reviewing this log quarterly gives you the data needed to improve your signal criteria iteratively, discarding those that have proven unreliable and refining those that have demonstrated consistent predictive value across multiple instances.
This discipline is what separates systematic on-chain analysis from anecdotal wallet-watching, and it is the foundation on which any durable trading edge built on transaction tracking must rest.
Blockchain explorers and basic transaction tracing reveal the mechanics of individual transfers. But the most valuable intelligence available from on-chain data is not found in single transactions — it is found in the behavioral patterns that emerge when you analyze a wallet's activity across time, asset types, and market conditions. Recognizing these patterns is the skill that distinguishes analysts who extract genuine edge from those who simply observe data without interpreting it.
Advanced pattern recognition requires familiarity with how sophisticated market participants typically behave at different stages of a market cycle, and the ability to identify deviations from baseline behavior that signal a meaningful change in positioning. Several patterns have proven consistently informative across multiple market cycles and are worth understanding in depth.
Accumulation fingerprinting is the process of identifying the specific transaction signatures that indicate a large wallet is building a position in an asset without wanting that accumulation to be obvious. Because large purchases made in a single transaction move the market and attract attention, sophisticated buyers typically spread their accumulation across many smaller transactions, multiple timeframes, and sometimes multiple wallet addresses.
The observable signature of deliberate accumulation differs from random buying in several ways. Transaction sizes tend to cluster in a narrow range rather than varying widely, because a systematic buyer is executing to a plan. Timing tends to show elevated activity during low-liquidity periods such as late-night hours in major trading time zones, when price impact is minimized. And the accumulation often occurs in tranches that correspond to identifiable support levels or after specific market events, rather than in a continuous stream that would reflect opportunistic buying without a structural thesis.
When you observe this pattern across multiple addresses that can be tentatively clustered as belonging to the same entity, the combined picture is substantially more informative than any individual transaction. A wallet making thirty small purchases of the same asset over two weeks is not engaging in routine activity. It is building a position, and understanding that distinction is the basis for one of the most reliable forms of on-chain alpha available to retail investors.
Exchange flow analysis is one of the most widely discussed on-chain metrics, but most interpretations focus on aggregate inflows and outflows without examining the behavior of specific wallet types within those flows. The more nuanced and informative observation is divergence: situations where the transaction behavior of high-value wallets moves in the opposite direction from the aggregate market flow.
When aggregate exchange inflows are rising, signaling that most market participants are preparing to sell, but large dormant wallets are simultaneously making outbound transfers to non-exchange addresses, that divergence suggests that sophisticated long-term holders are moving assets off exchanges and into self-custody, which is typically a behavior associated with confidence in holding rather than preparation for liquidation. The aggregate metric says sell pressure is building. The wallet-level behavior of the most experienced participants says the opposite. When these two signals diverge, the wallet-level behavior has historically been the more reliable leading indicator.
The reverse pattern is equally informative. When aggregate exchange outflows suggest broad accumulation but high-performance wallets are quietly moving assets toward exchange deposit addresses, the implication is that the apparent buying pressure may not be supported by the most informed segment of the market. Identifying this divergence early creates the opportunity to reassess a position before the broader market recognizes the shift.
Identifying accumulation fingerprints and exchange flow divergence manually requires tracking dozens of individual addresses across multiple explorers simultaneously, cross-referencing transaction timestamps and amounts, and maintaining a running model of what constitutes baseline versus anomalous behavior for each wallet. For a single address, this is time-intensive but feasible. Across a properly constructed monitoring universe of twenty or more addresses, it is practically impossible without tooling.
Alright, enough with the theory. Let's get our hands dirty and actually track some crypto.
Think of this as your first field assignment. We're going to walk through a basic investigation together, breaking down the entire process into five simple, actionable steps. By the end, you'll have a real skill that turns that mess of blockchain data into a clear story of where the money went.
Let's dive in.
Every investigation kicks off with a single clue—an anchor point that lets you unravel the rest of the story. In the world of crypto tracking, this is almost always one of two things: a transaction ID (TXID) or a wallet address.
Your first job is to lock down one of these pieces of information. It's the first thread you'll pull.
Once you have your starting clue, you need the right tool to look it up. This is where blockchain explorers come into play. These are basically free search engines for the blockchain, letting you plug in any TXID or address to see all the connected details.
For this guide, we'll stick with Etherscan since it's one of the most popular explorers out there.
This process isn't just for internet sleuths. As the graphic shows, these skills are fundamental for everything from regulatory compliance to deep-dive research and, of course, investigations.
With your explorer open, copy and paste your TXID or address into the search bar. The page that loads up is your initial crime scene, and it's packed with clues. Don't let it overwhelm you; just focus on the essentials for now.
You’ll see key details like the sender (From), the receiver (To), the exact amount transferred, and the transaction's timestamp. This first screen confirms the basic facts and, crucially, gives you the next set of addresses to investigate.
Now the real detective work begins. From that first transaction, you can start hopping both backward and forward in time. Click on the sender's address—where did their funds come from? Next, click on the receiver's address—where did the money go after this?
This process of jumping from one address to the next is the absolute core of crypto tracking. Each click peels back another layer of the onion, letting you map out the complete flow of funds. Make sure to document each address and transaction of interest as you build out your map.
Your goal is to follow the money until you hit either a dead end (like a privacy mixer) or an exit ramp, such as a deposit into a major crypto exchange. Finding an exchange deposit is often a huge win, as it links a pseudonymous address to a real-world entity that requires identity verification.
While manually clicking through a block explorer is powerful, it can get tedious and make it hard to see the forest for the trees. When you're ready to move past the basics, that's when specialized platforms like Wallet Finder.ai become indispensable.
These tools do the heavy lifting for you. They can automatically cluster addresses belonging to a single entity, visualize complex transaction flows, and tag wallets tied to known organizations. Instead of spending hours clicking, you get an entire network of activity laid out on a single screen. This helps you spot patterns, identify risky wallets, and turn your raw data into actionable intelligence—fast.
As you start peeling back the layers of on-chain analysis, it's totally normal to have questions. Let's be honest, some of these concepts can feel a bit abstract at first, and there's a lot of misinformation out there about how transparent blockchains really are.
This section is all about tackling those common questions directly. We'll cut through the noise and give you clear, straightforward answers to help you build a solid understanding and feel more confident as you dig deeper into on-chain data.
That's a great question, and the short answer is no—not all coins are created equal in terms of traceability. The big players you hear about all the time, like Bitcoin and Ethereum, operate on public ledgers. This means every single transaction is recorded and visible to anyone who wants to look, making them highly traceable.
But then you have a special class of cryptocurrencies known as privacy coins. Think of coins like Monero. They are specifically engineered to do the exact opposite. Using clever cryptography like ring signatures and stealth addresses, they deliberately hide the details of a transaction—who sent it, who received it, and how much was sent. While forensic tools are always getting smarter, these coins make a simple, A-to-B trace incredibly difficult by design.
On its own, tracking a crypto wallet just shows you the connections between different addresses, which are really just pseudonyms. An address is like a username on a forum; it doesn't have your name, photo, or home address attached to it.
The real key to connecting a wallet to a person is almost always at the on-ramps and off-ramps—the places where crypto meets traditional finance. We're talking about centralized exchanges like Coinbase or Binance. These platforms are legally required to conduct Know Your Customer (KYC) checks, which means they have to link a user's real-world identity to their accounts.
When funds you're tracking finally land in a deposit address at one of these regulated exchanges, that’s the golden link. At that point, law enforcement can use a subpoena or other legal processes to ask the exchange for the identity of the person who owns that account. Without that exchange connection, figuring out who's behind a wallet is a massive challenge.
If you're just getting started, the best free tools are, without a doubt, public blockchain explorers. They are incredibly powerful, free to use, and give you direct access to the raw data of the blockchain. Think of them as the Google for their specific network.
Here are the top three you should bookmark right away:
Getting comfortable with these explorers is the perfect way to build a strong foundation. You'll learn the core mechanics of transaction tracking before you ever need to think about paying for more advanced platforms.
Tracking funds across different blockchains is definitely a more advanced move, but it's a crucial skill. This usually happens when someone uses a crypto bridge to move an asset from one network to another (e.g., from Ethereum to Polygon).
Tracing this kind of move is a two-step dance:
Trying to connect these two dots manually can be a real headache. You have to meticulously compare timestamps, transaction amounts, and other data specific to the bridge. This is exactly why professional analysts often use specialized tools that can automatically spot these cross-chain jumps, turning a painful manual search into a single, clean visual line.
Yes. Consistent activity clustering during specific hours creates timezone fingerprints. If you trade primarily 15:00-23:00 UTC across months, analysts infer US Eastern timezone. Weekend/holiday patterns strengthen this (reduced US Thanksgiving activity, European Christmas quiet periods, Asian Spring Festival patterns).
Daylight Saving Time transitions provide definitive proof. US wallets shift activity by one hour twice yearly on US DST dates. European wallets shift on different dates. Arizona wallets never shift. Multi-year analysis makes geographic location undeniable.
Defend by using bots executing transactions at uniformly random times across all twenty-four hours. Alternatively, route through VPS in different timezones so transaction submission location differs from your actual location. Manual trading will always leak timezone information.
Exchanges process withdrawals in batches of 15-50 users in a single transaction to save gas. All recipient addresses in the batch are permanently linked as customers of that exchange. If Address A and Address B appear in three different exchange batches over six months, they're almost certainly the same user.
Analysts identify batches by high output count, specific denominations, gas patterns, and known exchange hot wallets. Once identified, all recipients become clustered. Users believing separate withdrawal addresses are private have instead created permanent on-chain proof of common ownership.
Defend by spacing withdrawals days/weeks apart so they process in different batches. Better yet, use different exchanges for different wallets (Address A only Coinbase, Address B only Binance). Same-exchange withdrawals to multiple addresses on the same day will almost certainly batch together.
Yes, via gas price fingerprinting. Wallet software like MetaMask, Trust Wallet, and Ledger Live each use distinct gas estimation algorithms. Using the same wallet software with the same settings (always "Fast") across multiple addresses creates identical gas bidding patterns identifiable as a signature.
Advanced users manually setting gas create stronger signatures. Consistently bidding exactly 5 gwei above base fee is unique across hundreds of transactions. Plotting (wallet_gas_price / network_base_fee) ratio reveals consistent bidding strategy even as absolute prices change.
Defend by deliberately randomizing gas across transactions (mix "Fast," "Medium," "Slow"). Use different wallet software for different addresses (MetaMask for one, Ledger for another). Implement custom scripts that bid randomly within 1.0x-1.5x base fee range to prevent pattern recognition.
The most reliable filter for distinguishing informative transactions from noise is behavioral context. A single large transaction from a wallet with no prior history of meaningful activity in that asset carries limited informational weight on its own. The same transaction from a wallet with a documented pattern of accumulating assets before significant price moves, in a timeframe and at a price level consistent with its historical behavior, is a meaningfully different data point. The practical way to apply this filter is to evaluate any transaction against three questions before treating it as a signal: does this wallet have a track record that justifies treating its behavior as informed? Is this transaction consistent with a pattern of deliberate positioning, or does it look like a one-off transfer with no broader context? And does the behavior align with or diverge from what other high-value wallets are doing simultaneously? A transaction that passes all three filters is worth investigating further. One that passes only the first is worth noting. One that passes none should be treated as noise regardless of its size.
The difference is primarily one of objective, which determines which behaviors and patterns are worth monitoring. Compliance-focused tracking is backward-looking and risk-oriented: its goal is to identify whether funds involved in a specific transaction have a historical connection to illicit activity, sanctioned addresses, or high-risk entities. The workflow starts with a known transaction and traces its history to assess risk exposure. Investment research-focused tracking is forward-looking and opportunity-oriented: its goal is to identify what high-performing wallets are doing right now in order to anticipate price movements before they are reflected in the market. The workflow starts with a curated set of monitored addresses and watches for behavioral signals that precede meaningful market moves. Both use the same underlying data and many of the same analytical techniques, including address clustering, transaction graph analysis, and entity tagging, but the direction of analysis and the criteria for what constitutes a relevant finding are almost entirely opposite. Understanding which objective you are pursuing before you begin an investigation prevents you from applying compliance-oriented skepticism to investment signals or treating investment-oriented pattern recognition as sufficient grounds for a compliance decision.
High-performance wallets are typically identified through retrospective analysis: an analyst observes that a specific address accumulated a position in an asset weeks or months before a significant price move, then traces that wallet's full transaction history to assess whether the early positioning was part of a consistent pattern or a single fortunate trade. Wallets that demonstrate consistent early positioning across multiple assets and market cycles are flagged as high-value monitoring targets. The question of whether following widely known wallets stops being useful is legitimate but somewhat overstated in practice. Sophisticated wallets that become aware they are being monitored can distribute activity across new addresses, which does reduce the signal quality from any single identified address. However, the behavioral patterns that made the original wallet worth following tend to persist across the new addresses, and on-chain clustering techniques can often identify the new addresses as belonging to the same entity based on co-spending patterns and transaction timing. More fundamentally, the informational value of on-chain smart money tracking derives not from any single wallet but from the convergence of behavior across multiple independent high-performance addresses simultaneously. When ten unconnected wallets with strong track records all begin accumulating the same asset within a short window, the signal remains informative regardless of whether any individual wallet is being deliberately watched, because the convergence itself is the signal.
Ready to move beyond manual tracking and see what the pros see? Wallet Finder.ai gives you the tools to automatically track smart money, discover winning trade strategies, and get real-time alerts on the wallets that matter. Start your 7-day trial and turn on-chain data into your competitive edge at https://www.walletfinder.ai.