Push Notification Alerts: Your DeFi Trading Edge
Learn how to use push notification alerts to master DeFi. This guide covers setup, best practices for traders, and how to get real-time copy trading signals.

May 8, 2026
Wallet Finder

March 24, 2026

Building a crypto wallet is more than just a technical exercise; it’s about creating a user's core gateway to the Web3 world. Before you even think about writing a single line of code, you need to make some critical decisions about security, custody, and features that will define your entire project.
The choices you make right now are everything. They will dictate your wallet's security model, shape the user experience, and even determine your legal and regulatory responsibilities. Get this wrong, and you'll be building on a shaky foundation.
The opportunity here is massive. The global crypto wallet market was valued anywhere from $12.20 to $15.54 billion in 2023. Forecasts predict it could explode to over $100 billion by 2033, growing at a compound annual rate of around 25%. This isn't just growth; it's a signal that there's huge demand for well-built, user-focused wallets.
So, where do you start? The first and most fundamental question to answer is: who holds the keys? Your answer splits the development path into two completely different directions.
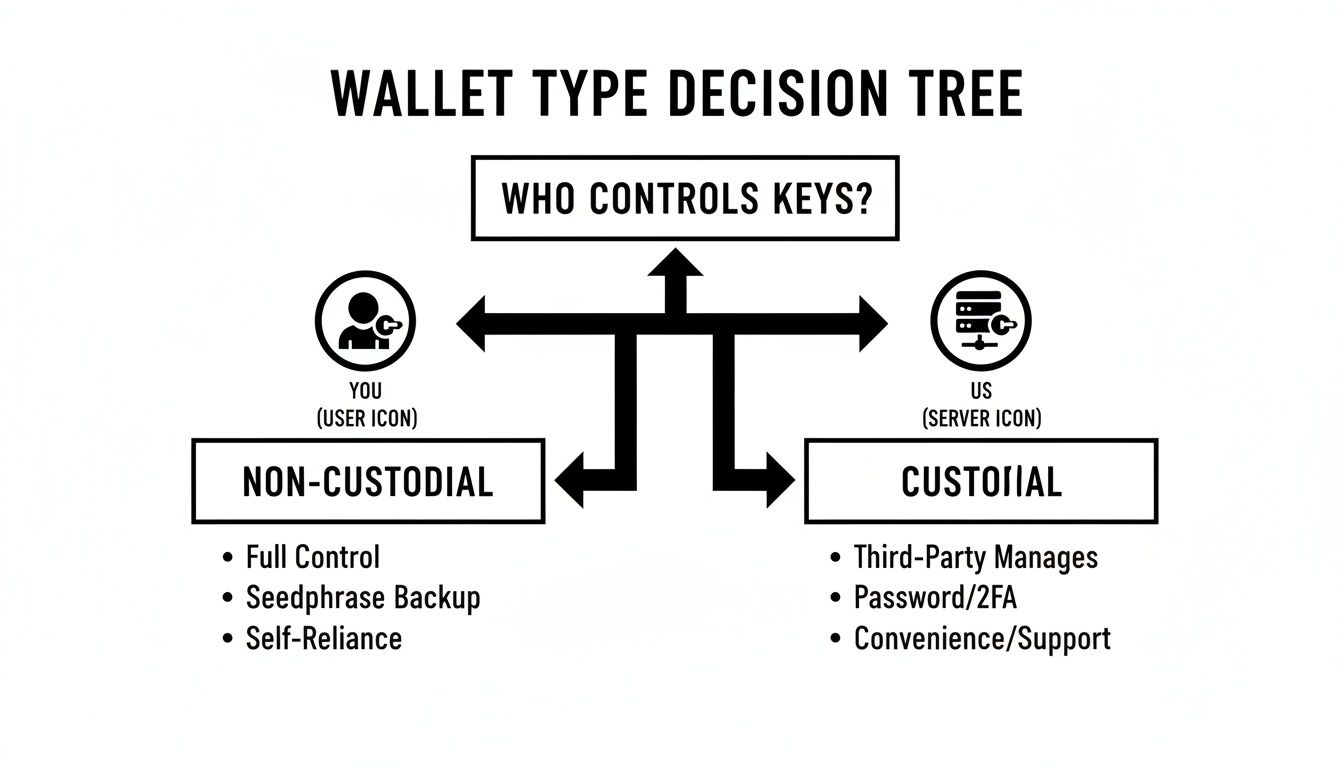
This decision tree nails the core difference. With a non-custodial wallet, you empower the user. With a custodial one, you take on that responsibility yourself.
Key Takeaway: Choosing a custody model is a philosophical decision, not just a technical one. Custodial wallets offer convenience by hiding complexity. Non-custodial wallets offer freedom and control. Your target audience's crypto-savviness and what they value most should be your guide.
The wallet game has evolved far beyond that initial custody choice. The first generation of wallets, what we call Externally Owned Accounts (EOAs), are essentially just a simple pair of public and private keys. They're controlled directly by that one private key and remain the most common wallet type you see today.
But a new, far more powerful paradigm is taking over: Smart Contract Wallets.
Also known as "smart accounts," these are actually smart contracts on the blockchain that function as a wallet. They aren't tied to a single private key. Instead, they're governed by programmable code. This simple shift unlocks a whole new world of features that are completely impossible for a standard EOA. You can dive deeper into the nuts and bolts of these next-gen wallets in our comprehensive guide on Web3 wallet architecture.
To make this choice clearer, we need to compare these architectures side-by-side. This table breaks down the fundamental differences between Custodial, Non-Custodial (EOA), and Smart Contract wallets, helping you map out your development path.
| Feature | Custodial Wallet | Non-Custodial (EOA) Wallet | Smart Contract Wallet |
|---|---|---|---|
| Key Control | Service Provider | User | Programmable (User-initiated) |
| Recovery Method | Password Reset | Seed Phrase | Social Recovery, Guardians |
| Security | Centralized server security | User's responsibility | On-chain logic, multisig |
| User Experience | Familiar (Web2-like) | Requires user education | Can be highly intuitive |
| Flexibility | Limited to platform features | Limited by protocol | Highly programmable, extensible |
Your decision here has real-world consequences. Building for DeFi newcomers who are terrified of losing a seed phrase? A smart contract wallet with social recovery is a brilliant solution. Targeting seasoned traders who demand absolute, unshakeable control? A classic non-custodial EOA is likely their preferred tool. You have to know your user inside and out before you commit.
Alright, you've got your strategy down. Now comes the really critical part: drafting the technical blueprint for your crypto wallet. Getting this architecture right from the beginning is everything. A solid plan here will save you from endless refactoring nightmares down the road.
Think of it this way—you're not just laying a foundation; you're designing the entire structure, from the plumbing to the security system, all at once.
The best-architected wallets are almost always modular. Building your wallet with independent, interconnected modules is the secret to making it maintainable and easy to upgrade later on.
Every crypto wallet, no matter how simple or complex, is built on a few fundamental components that have to work together perfectly. As you plan your development, make sure you account for each of these.
The golden rule of wallet architecture is to never let a private key leave the secure KMS. The signing engine should be the only part of your app that can even ask for a signature, and it should only get the signed transaction back—never the key itself.
The tech stack you pick will define the specific tools and libraries you’ll use to bring these components to life. This choice really depends on which blockchain ecosystems you're targeting.
For EVM-compatible chains like Ethereum, Base, and Polygon, the developer world is largely split between two giants:
If you’re building for Solana, your go-to is the official @solana/web3.js library. Be prepared for a different experience; its structure is built around Solana's unique account model and high-speed transaction processing.
One of the biggest forks in the road is deciding whether to build all your backend infrastructure yourself or to use a Wallet-as-a-Service (WaaS) provider. This is the classic "build vs. buy" debate, and your choice here has huge implications.
| Consideration | Building from Scratch | Using a WaaS Provider |
|---|---|---|
| Speed to Market | Slower; requires extensive backend development. | Much faster; focuses your team on the frontend. |
| Control & Customization | Total control over every aspect of the infrastructure. | Limited to the features offered by the provider. |
| Upfront Cost | Higher due to specialized backend engineering needs. | Lower; typically a usage-based subscription model. |
| Security Burden | You are 100% responsible for securing the key infrastructure. | The provider handles complex cryptography and security. |
| Team Skills | Requires deep expertise in cryptography and backend security. | Allows teams with strong frontend skills to get started. |
Going with a WaaS provider can be a brilliant move for teams trying to launch an MVP fast or for existing apps wanting to add wallet features without hiring a dedicated crypto security team.
But if your core product relies on a completely novel key management system or needs deep backend customization, building from scratch might be your only option. For those building their own backend, getting clean and reliable data is non-negotiable. You can learn more about this in our guide to the best crypto price APIs.
Of all the pieces in your crypto wallet puzzle, nothing is more critical than security. It isn't just a feature—it's the absolute bedrock of your application. One slip-up in how you handle cryptographic keys can lead to devastating and irreversible losses for your users.
Getting key management right is non-negotiable. This means looking at the entire journey of a private key, from its creation with true randomness to its encrypted storage and the methods you provide for users to back it up safely.
At its core, a private key is just a massive, random number. The entire security of a wallet hinges on just how "random" that number truly is. If a bad actor can figure out the pattern your wallet uses to generate keys, they can recreate them and start draining funds.
This is where cryptographically secure entropy comes into play. You can't just rely on simple math functions. Your wallet must use the operating system's built-in secure random number generator, which pulls unpredictable data from hardware-level sources like user input timing or electronic noise.
SecRandomCopyBytes on iOS or SecureRandom on Android.window.crypto.getRandomValues() method, the standard for generating cryptographically strong random values in browsers.Whatever you do, never attempt to roll your own "random" generation algorithm. This is a solved problem, and using battle-tested libraries is the only safe path forward.
Once that key is generated, it needs a safe place to live. Storing it in plain text, even for a split second in memory, is a rookie mistake with catastrophic potential. The baseline practice is to encrypt the key at rest, using a password or PIN from the user to unlock it.
But the gold standard is using the device's built-in secure enclaves. These are specialized hardware chips, completely isolated from the main operating system.
Think of a secure enclave, like Apple's Secure Enclave or Android's StrongBox Keystore, as a tiny vault inside a device's processor. It lets your app generate, store, and use keys without them ever touching the main OS—or any malware that might be on it.
This technique essentially turns the user's phone into a mini-hardware wallet. The private key never leaves the secure chip. Instead, the chip performs signing operations internally and just hands the final signature back to your app.
For a non-custodial wallet, "I lost my phone" can easily mean "I lost all my money." A clear, straightforward backup system is absolutely essential for user trust and adoption.
The industry standard is the mnemonic seed phrase (based on the BIP-39 standard), a simple list of 12 or 24 words that can be used to regenerate the master private key.
Your user interface has to walk the user through this critical process:
For more advanced products, especially smart contract wallets, you can also look into social recovery. This lets a user designate trusted "guardians" (like friends or other wallets they own) who can collectively approve a request to recover access to the account.
As a user's portfolio grows, their security needs become more serious. Building in native support for hardware wallets like Ledger or Trezor is a massive signal that you take security seriously.
The demand for this is undeniable. The Bitcoin and Cryptocurrency Hardware Wallets market was valued at USD 347 million in 2024 and is projected to explode to USD 2,667 million by 2034, growing at a blistering CAGR of 34.7%. This trend, detailed in recent hardware wallet market research, shows users are actively seeking top-tier security.
Technically, integration usually involves libraries like WebUSB or WebHID. These allow your web app to securely communicate with the connected hardware device. Your app builds the transaction, sends it to the hardware wallet, and the device signs it on its own secure chip before returning the signature.
Beyond just protecting the key itself, your wallet needs to protect the user from being tricked.
Let's be real: a single-chain wallet just doesn't cut it anymore. Today's crypto users are constantly jumping between ecosystems, and they expect to switch from Ethereum to Solana to a Layer 2 like Base without a second thought. If you're building a wallet, this isn't optional—it's a core requirement for being competitive.

This means your wallet’s architecture has to be built from the ground up to manage this complexity, all while keeping the user experience clean and simple.
Adding multi-chain support is much more than just sticking a network dropdown in your UI. You're dealing with entirely different cryptographic standards, address formats, and transaction types under one roof. The only sane way to manage this is through abstraction.
Your wallet will need a flexible communication layer that knows how to speak to various RPC (Remote Procedure Call) endpoints. Think of this as the gateway to each blockchain, allowing you to fetch balances and broadcast transactions.
I’ve found the best way to tackle this is by building modular ChainAdapter components for each ecosystem.
EVMAdapter would be your workhorse for Ethereum, Base, Arbitrum, and other EVM chains. Here, you’ll be using battle-tested libraries like Ethers.js or Viem.SolanaAdapter would use the @solana/web3.js library to handle the unique quirks of connecting to Solana RPC nodes.This approach keeps your chain-specific code neatly separated. When you’re ready to add a new network like Sui or Aptos down the road, you just build a new adapter instead of rewriting half your codebase.
Key Insight: The real challenge is managing key derivation paths. EVM chains almost always follow the BIP44 standard. But non-EVM chains like Solana have their own rules (like SLIP-0010). Your key management system absolutely must know how to derive the correct private key and public address for the active network, all from the user's single seed phrase.
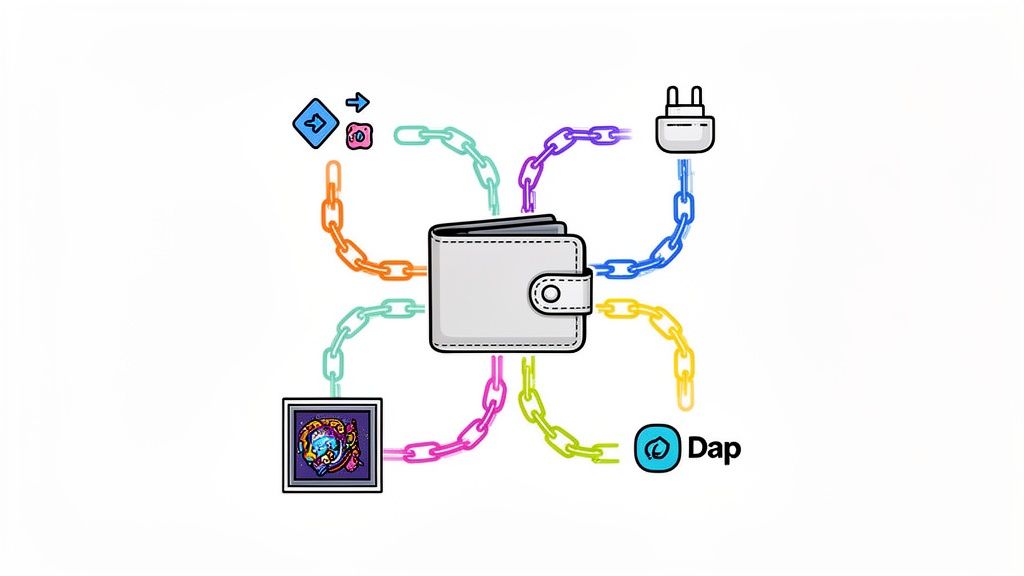
Once your multi-chain plumbing is in place, it’s time to build the features that will make people actually want to use your wallet. Sending and receiving tokens is just table stakes. Users are looking for advanced tools baked right into the app.
Here are three features you should prioritize on your roadmap:
With all this power under the hood, the biggest risk is creating a confusing and cluttered interface. Your goal should be to hide all the underlying complexity from the user.
| Feature Area | Best Practice for UX |
|---|---|
| Network Switching | Make it effortless, with clear visual indicators of the active chain. Automatically suggest switching if the user interacts with a dApp on a different network. |
| Asset Display | Group tokens by chain but present them in a single, unified portfolio view. Show a total portfolio value that combines assets from all supported networks. |
| Transaction Previews | Provide clear, human-readable transaction summaries. Decode what the user is signing, whether it's a simple token transfer or a complex smart contract interaction. |
Building a feature-rich, multi-chain wallet is a difficult but incredibly rewarding process. By focusing on smart architectural abstractions and a dead-simple user experience, you can create a product that becomes an essential tool for anyone navigating the decentralized world.
To build a wallet that traders can't live without, you need to think beyond the basics. Standard features like sending, receiving, and swapping are just table stakes. The real magic happens when your wallet becomes an intelligent command center, packed with tools that deliver actionable insights and help users make smarter, faster decisions.
This means shifting your wallet's UI from a simple balance sheet to a dynamic trading dashboard. It all starts with solid, real-time on-chain data. By plugging into live data providers, you can show users what they really need to see, right inside your app.
The biggest differentiator for a modern wallet is integrating signals that expose "smart money" movements. This is where you can connect to specialized services to surface genuine alpha. For instance, plugging into an API from a platform like Wallet Finder.ai lets you feed your users powerful copy-trading signals.
By integrating these kinds of analytics, your wallet can become the central hub of a user's entire trading ecosystem, connecting them to the data and applications they need to succeed.
An integration like this allows your wallet to display the P&L, win rates, and recent trades of top-performing traders, turning raw, noisy blockchain data into a clear competitive advantage.
From a technical standpoint, this involves making API calls to fetch the data. You might query an endpoint for a list of top wallets or subscribe to a webhook that pushes updates when a watched wallet makes a move. The key is to present this complex information in a simple, actionable format, like a push notification that screams opportunity: "Alert: Whale wallet 0x... just bought 10M PEPE."
Expert Insight: Let's be clear: these features are no longer a "nice-to-have." Active traders and DeFi natives expect their primary wallet to be their main interface for market analysis. By building these tools in-house, you stop users from bouncing to other platforms and dramatically boost your retention.
To truly build a trading command center, your development roadmap needs to prioritize features that give users an edge. The table below breaks down the essential components that turn a standard wallet into a powerful analytics tool that traders will actually use.
| Feature | Description | Primary User Benefit |
|---|---|---|
| Real-Time P&L Tracking | Automatically calculates and displays the profit or loss for each asset and the overall portfolio. | Provides immediate feedback on investment performance without manual calculations. |
| Smart Money Wallet Alerts | Pushes notifications when a tracked "smart money" or whale wallet makes a significant trade. | Enables users to act on market-moving trades in real-time. |
| On-Chain Signal Feeds | Integrates data feeds that highlight trending tokens, new liquidity pools, or unusual trading volume. | Helps users discover new opportunities before they become mainstream. |
| Wallet Profiling | Displays detailed statistics for any wallet address, including win rate, top tokens, and trading history. | Allows for deep due diligence on other traders to inform copy-trading decisions. |
By weaving these advanced analytics and trading tools directly into the core user experience, you're doing much more than basic crypto wallet development. You're building a product that doesn't just secure assets—it actively helps users grow them.
Launching a crypto wallet is a moment of truth. Unlike a standard app where you can push a quick fix for minor bugs, a single flaw in your wallet can mean irreversible financial losses for your users. There's simply no room for error.
The final stretch of development requires a hardcore, defense-in-depth mindset. It’s all about rigorous testing, independent auditing, and a well-planned deployment.
Before your wallet sees the light of day, it needs to be put through the wringer with exhaustive testing that mimics real-world scenarios. The goal is to move from testing the smallest pieces of code all the way up to verifying the entire system on live blockchain environments.
Your testing strategy should be built in layers:
Unit Tests: Every single function needs to be isolated and tested, especially those handling sensitive operations like cryptography or transaction formatting. For instance, a unit test must confirm your key generation function actually produces valid keys. Another should verify your transaction encoder structures data correctly for a specific network.
Integration Tests: This is where you check if all the different parts of your wallet play nicely together. Does the UI correctly call the signing engine? Does the signing engine get a signature from the Key Management System without accidentally exposing the private key?
End-to-End (E2E) Tests: Here’s where you simulate a full user journey from start to finish. You should automate tests that perform common actions like creating a new wallet, receiving funds, and sending a transaction. Run these on public testnets like Ethereum's Sepolia or Solana's Devnet to get as close to real conditions as possible.
Pro Tip: Use testnet faucets to grab free test assets. A good E2E test script automates the entire flow: check the initial balance (which should be zero), hit a faucet for funds, verify the balance updated, and then send a test transaction to another address.
Look, internal testing is critical, but it's never enough. You're too close to the project, and you will have blind spots. A third-party security audit isn't just a good idea—it's an absolute requirement before a single user's funds touch your wallet.
Independent auditors bring a fresh, adversarial perspective. Their job is to break your code in ways you never thought of.
During an audit, these experts will hammer your wallet, looking for:
Once you get that audit report, the work isn't over. You have to systematically fix every single issue, starting with anything marked as critical or high-severity. Publishing the audit results and your team’s fixes is a massive step toward building trust with your community. To get a better handle on what to expect, check out our guide on how to approach crypto security audit services.
With a clean audit report and a battle-tested codebase, you're finally ready to deploy. For mobile wallets, this means navigating the review processes for the Apple App Store and Google Play Store. Be ready for some back-and-forth, as they pay close attention to financial and crypto-related apps.
But launch day is just the beginning. From that moment on, you need rock-solid monitoring and logging to make sure your wallet stays secure and stable out in the wild.
Diving into crypto wallet development is an exciting journey, but it's bound to come with a few questions. We get it. Here are the most common things developers and entrepreneurs ask when they're just getting started.
The honest answer? It depends. The cost of building a crypto wallet can swing wildly based on what you're trying to achieve.
A lean, single-chain non-custodial wallet—think of it as your Minimum Viable Product (MVP)—could get off the ground for around $50,000. But if you're aiming for a feature-packed, multi-chain powerhouse with smart contract logic and top-tier security audits, you could easily be looking at a budget north of $500,000. The final number always comes down to your team's size, where they're located, and the plan for ongoing maintenance.
When it comes to wallet development, security isn't just a feature; it's everything. A few risks should be at the absolute top of your list.
A recent supply chain attack involved malicious npm packages impersonating Flashbots SDKs, designed to steal private keys and mnemonic seeds directly from developers' environments. This highlights the critical need to vet all dependencies during your crypto wallet development lifecycle.
Think of Wallet-as-a-Service (WaaS) as a shortcut. These platforms provide all the heavy-lifting infrastructure for key management and talking to the blockchain, which lets you pour all your energy into creating an amazing frontend user experience.
You should seriously consider WaaS if your main goal is getting to market fast or if your team doesn't have deep expertise in backend cryptography. It’s an excellent route for launching quickly while sidestepping a ton of initial complexity and security headaches.
Ready to turn on-chain data into your trading edge? Wallet Finder.ai helps you discover and track the smartest wallets in DeFi, providing real-time alerts and in-depth analytics. Start your 7-day free trial and copy-trade with confidence at https://www.walletfinder.ai.