Price Action Analysis for Crypto Trading
Master price action analysis for crypto & DeFi. This guide explains key patterns, risk management, and how to combine charts with on-chain wallet data.

May 14, 2026
Wallet Finder

March 14, 2026

Security audit services are professional reviews of a project's code, architecture, and economic model. Their job is to hunt down vulnerabilities before attackers can find and exploit them.
In DeFi, where smart contracts are the vaults holding billions in assets, these audits are a non-negotiable layer of defense. They are essential for protecting user funds and ensuring a platform works exactly as promised.

Think of a DeFi security audit like the final, intensive inspection of a high-tech bank vault right before the cash arrives. In our digital world, smart contracts are the vaults. A single, tiny flaw in their code could lead to a complete and irreversible disaster.
That’s why these specialized services go way beyond a simple bug check. A real audit brings in a team of security experts to meticulously comb through everything—the source code, the system architecture, and even the project's economic assumptions. They’re looking for any weak point a hacker could use to their advantage.
This process is absolutely vital for building trust. It’s how you prove to users and investors that you've done your homework and taken every possible step to secure the ecosystem.
The stakes in decentralized finance are just too high. A minor coding error isn't a small glitch; it's a permanent, exploitable backdoor that can't be patched once the contract is live. A proper security audit digs into multiple layers of risk that automated scanners simply can't see.
Auditors zero in on a few critical areas:
A professional audit is a deep, adversarial analysis. Auditors adopt the mindset of an attacker, actively trying to break the system in order to fortify it. This proactive approach is fundamental to preventing real-world exploits.
At the end of the day, a security audit is what builds trust. In the fast-moving world of DeFi, where platforms like Wallet Finder.ai track smart money and analyze on-chain activity, the integrity of that data is everything. An audited project gives everyone confidence that the underlying data for PnL tracking and trade history is sound.
The market gets it, too. The global auditing services market, which includes these crucial security assessments, was valued at USD 233.95 billion in 2025 and is projected to hit USD 338.28 billion by 2034. You can dig into these trends over at Fortune Business Insights. This massive growth shows that the entire industry recognizes security isn't just a feature—it's the whole foundation.
Without a credible audit report from a well-known firm, a DeFi project will have a hard time gaining any real traction. It’s the clearest signal you can send that your team is serious about user safety and building something that lasts. You can learn more about the specifics in our guide to smart contract security.
Not all security audits are the same. Think of it like building a house—you need separate inspections for the foundation, the electrical wiring, and the plumbing. A DeFi project is no different; it has various layers, and each one needs a specific type of audit to make sure it's secure.
Choosing the right audit at the right time is absolutely critical to preventing a catastrophe down the line. Understanding these distinctions helps everyone, from founders to investors, get a real sense of a project's security posture.
The most common and fundamental checkup is the smart contract audit. This is a microscopic examination of the code that handles every transaction and bit of logic in your protocol. It's like proofreading a legally binding document, except a single typo in the code could mean losing millions.
Auditors painstakingly go through every line of code, hunting for both well-known and brand-new vulnerabilities.
A smart contract audit is completely non-negotiable before you deploy any code. It’s the first and most vital line of defense for any DeFi application.
Before we dive deeper, here's a quick comparison of the main audit types you'll encounter in the DeFi space. This table breaks down what each audit focuses on, the typical vulnerabilities it looks for, and when it’s most needed in a project's lifecycle.
This table should give you a clearer picture of how each audit type plays a unique role in securing a project from top to bottom.
While smart contracts are the apps, the blockchain is the operating system they run on. A blockchain protocol audit zooms out to inspect the entire underlying architecture. This isn't something most projects need if they're building on an established chain like Ethereum, but it's essential for new Layer 1 or Layer 2 protocols.
This audit digs into the core mechanics of the blockchain itself. Auditors will analyze everything from the consensus mechanism and peer-to-peer networking to the cryptographic implementations, ensuring the whole system is built on solid ground.
An audit at the protocol level ensures the very ground the project is built on is stable. It looks for fundamental design flaws that could lead to chain reorganizations, double-spending, or network-wide failures.
Finally, a dApp security assessment zeros in on everything the user interacts with—the website, APIs, and backend infrastructure that connect them to the on-chain smart contracts. You could have perfectly secure smart contracts, but a vulnerability in the web interface can still lead to devastating losses for your users.
This assessment looks for more traditional web security issues, including:
This audit is crucial because it protects users at their most vulnerable point: their entry into your ecosystem. It ensures the bridge between the user and the blockchain isn't a weak link. With the cybersecurity audit market projected to hit USD 7.5 billion by 2026 and expand to USD 3,359.5 million by 2033, it's clear how seriously the industry is taking these threats.
Ultimately, the right audit depends on what you're building. For the vast majority of DeFi projects, a powerful combination of smart contract audits and dApp security assessments is essential. To get a better handle on the tools of the trade, explore our guide on security auditing software.
Ever wonder what really happens during a security audit? It's not some black box where your code goes in one end and a report magically pops out the other. Think of it more as a structured, collaborative deep-dive designed to systematically hunt down and neutralize threats.
Understanding this lifecycle is crucial. For project teams, it helps you prepare effectively. For investors, it gives you the context to tell the difference between a thorough, professional review and a quick, superficial once-over. The whole journey starts long before a single line of code is analyzed and is built on a partnership between your dev team and the auditors.
This flow chart gives a great high-level view of how a typical DeFi audit works, touching on everything from the smart contracts themselves to the protocol logic and the dApp users interact with.
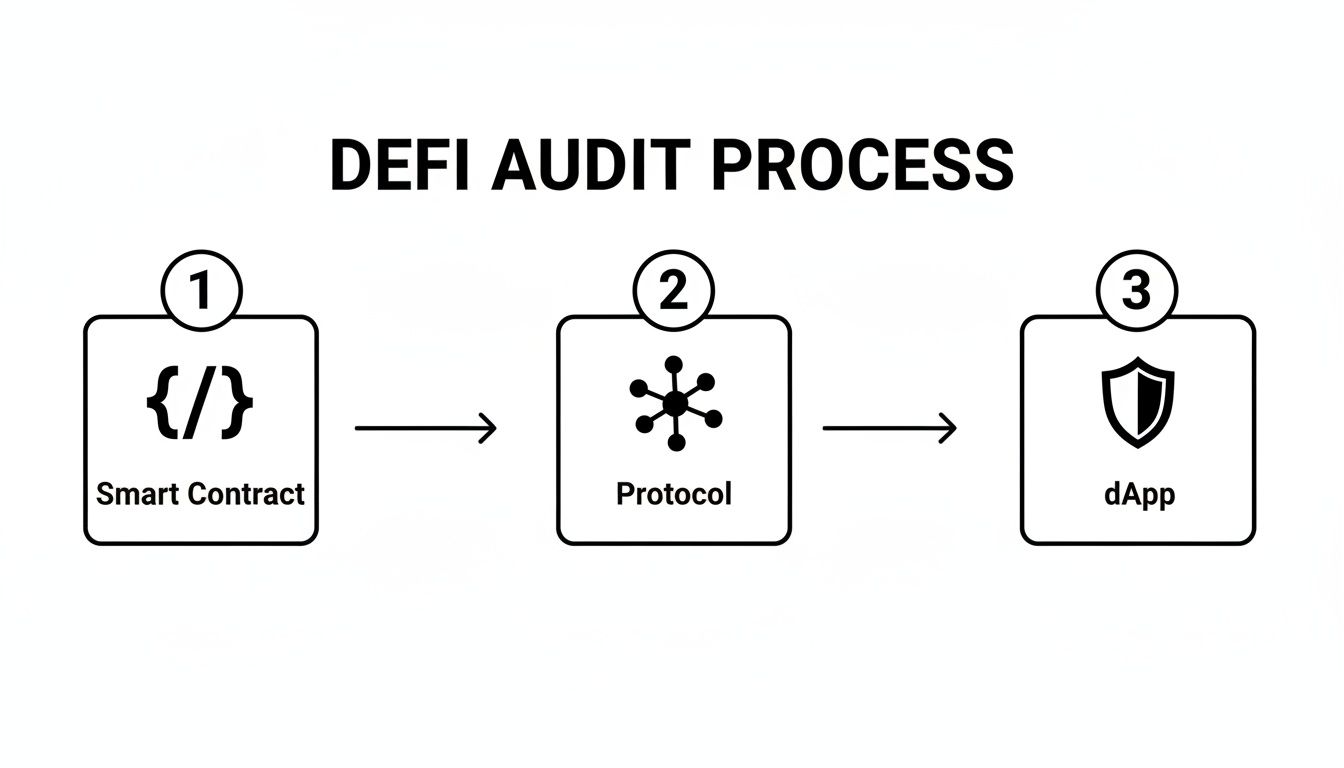
As you can see, a proper audit has to cover every layer—the code, the architecture, and the interface—to give you a complete picture of your project's security.
The very first step, before anything else, is scoping. Your team hands over the complete codebase, all the technical documentation you have, and any architectural diagrams. This lets the auditors get a feel for the project's goals, its complexity, and where the most likely attack surfaces might be.
With that information, the audit firm draws up a detailed proposal. This isn't just a price quote; it outlines the timeline, the cost, and the specific methods they'll use to pick your code apart. Once everyone agrees and signs off, the audit officially kicks off.
The audit itself is a two-pronged attack. It starts with automated scanning, where specialized tools are let loose on the code to find the low-hanging fruit. These scanners are great for catching common, known issues like outdated libraries or standard vulnerability patterns.
But that's just the warm-up. The real heavy lifting—and where the value of a professional audit truly lies—is in the intensive manual code review. This is where experienced security engineers get their hands dirty, meticulously combing through the code line by line.
Automated tools are great for finding the known unknowns—vulnerabilities that have been seen a thousand times before. Manual review is where experts find the unknown unknowns—those tricky logical flaws and unique economic exploits that a scanner will always miss.
During this phase, auditors are hunting for the subtle but deadly bugs:
When auditors find something, they don't just jot it down for a final report. They document it immediately with a clear explanation, a severity rating, and practical recommendations for a fix. This isn't a "gotcha" process; it's a constant collaboration.
Good auditors will open a direct line of communication, often a shared Slack or Telegram channel, with your developers. This back-and-forth is invaluable, allowing your team to ask questions and get instant clarity on findings, which dramatically speeds up the fixing process.
Findings are typically sorted by severity to help your team prioritize what to tackle first.
Once the initial audit report is in your hands, the ball is in your court. This is the remediation phase, where your developers get to work fixing all the issues based on the auditors' guidance.
After the fixes are coded, you send the updated codebase back to the audit firm. They then perform a verification pass. This is a crucial final check to confirm that every single issue has been properly resolved and, just as importantly, that the fixes haven't accidentally introduced new bugs.
Only when this final check is complete will the auditors sign off and issue their final, public-facing report. This document is more than just a piece of paper; it’s a stamp of approval that shows your project's commitment to security and is essential for building trust with your community.
Picking a security audit firm is easily one of the most critical decisions your DeFi project will ever make. This isn't just about ticking a box or getting a stamp of approval. It's about finding a true partner who will hammer away at your code, find its breaking points, and help you build a genuinely safer protocol for your users.
Let's be clear: a top-tier audit builds trust, attracts smart money, and can be the single thing that separates a smooth launch from a headline-making exploit.
The problem? The market is flooded with auditors of all shapes and sizes, from world-renowned security researchers to small, unproven teams. Making the right call means you have to do your homework and know exactly what to look for—and which red flags to run from.
An auditor's history is their resume. Your first step should be to go deep on their public track record. Any firm worth its salt will have a long list of past clients and a library of publicly available security audit services reports. Don't just skim the client list; actually read the reports.
What you're looking for is depth and clarity. A good report doesn't just list vulnerabilities; it explains them in plain English and offers clear, actionable steps for fixing them. If a firm has a history of finding complex, critical bugs in major protocols, that’s a powerful signal they know what they're doing.
DeFi security isn't one-size-fits-all. A team that's brilliant at auditing Rust-based Solana contracts might not be the best fit for your Solidity-based EVM protocol. You need auditors with specific, proven expertise in your tech stack.
Get straight to the point when you're talking to potential firms:
Specialization is key. You want a team that lives and breathes your ecosystem, not a group of generalists learning on your dime.
A real audit is so much more than running an automated scanner. It’s a painstaking process that combines cutting-edge tools with old-fashioned human ingenuity. The firm's methodology should be transparent and comprehensive, blending automated analysis with an intense manual review of every single line of code.
The best security audits are adversarial by nature. The auditors must think like a hacker, actively trying to break the system from every conceivable angle. This mindset is essential for uncovering the non-obvious, logic-based flaws that automated tools always miss.
As the DeFi ecosystem matures, so do the stakes. Traders are using sophisticated tools like Wallet Finder.ai to analyze PnL and find an edge, which means the underlying security of the protocols they use is more important than ever. This trend is mirrored in the broader financial world, where the U.S. auditing services market is expected to balloon from USD 53.55 billion in 2026 to USD 62.81 billion by 2031.
Information systems audits—the kind crucial for blockchain security—are projected to lead this growth with an impressive 12.18% CAGR. This just goes to show how intense the focus on securing digital finance has become. You can dive deeper into these trends in in-depth industry reports.
This growth highlights why a structured vetting process is so crucial. A simple checklist can help you stay organized and ensure you cover all your bases when evaluating potential partners.
Choosing the right security partner is a big decision, but it doesn't have to be overwhelming. The table below breaks down the key criteria to focus on during your evaluation process, helping you spot the difference between a top-tier firm and one that might leave you exposed.
Ultimately, you’re looking for a partner, not just a vendor. The right firm will feel like an extension of your team—dedicated, communicative, and genuinely invested in making your project as secure as possible.
Getting that final security audit report is a huge win. Seriously, it's a massive milestone for any DeFi project and a clear signal to your community that you’re committed to protecting their funds. But here’s the thing: it’s a mistake to treat that report like a permanent, bulletproof vest.
Think of an audit as a highly detailed snapshot in time. It's a deep dive into your protocol's security based on the exact code and environment that existed during the review. The second you deploy, however, your project steps into a live, unpredictable, and often hostile ecosystem where things can change in a heartbeat.
This is why the audit can't be the end of the road for security. It has to be a living, breathing process that adapts to the wild, ever-shifting world of DeFi. The threats that will pop up tomorrow aren't always visible in the audit you complete today.

Once your smart contracts are on the blockchain, they're there for good. This immutability is a cornerstone of DeFi, but it’s a double-edged sword. It means brand-new vulnerabilities can pop up as the ecosystem evolves around your protocol—vulnerabilities your initial auditors simply couldn't have predicted.
Once you’re live, a whole new set of risks comes into play:
An audit report confirms your defenses were strong on launch day. Continuous monitoring ensures they stay strong every day after, adapting to new threats as they appear in the wild.
This is where your security mindset has to shift from a one-off checkup to a constant, vigilant watch. While an audit verifies the structural integrity of your code, continuous on-chain monitoring is your 24/7 security team, alerting you to sketchy activity as it happens.
It’s like this: the audit is the team of architects and engineers who made sure the bank vault is impenetrable. Continuous monitoring is the live security feed and the guards watching for anyone trying to pick the lock. You absolutely need both.
Tools like Wallet Finder.ai are leading the charge in this new security paradigm. By tracking the on-chain moves of smart money and flagging weird wallet activity, these platforms add an essential layer of real-time threat intelligence that an audit alone can't provide.
Continuous monitoring turns the blockchain's public ledger from a simple transaction history into a powerful, predictive security tool. It gives teams and users the ability to spot the early warning signs of an attack before the real damage is done.
Here’s how that plays out in the real world:
This approach doesn't replace security audits; it completes them. The audit makes sure your code is solid from day one. Continuous monitoring gives you the live intelligence to defend that code against the dynamic, real-world threats that come next. It’s how you turn a static report into a living, breathing defense strategy.
Traditional security audit services rely on manual review processes and basic vulnerability classification but lack sophisticated quantitative methodologies that enable mathematical risk assessment and systematic audit evaluation through advanced analytical frameworks. Mathematical audit approaches transform subjective security assessment into rigorous quantitative analysis that provides precise risk quantification and enables institutional-grade audit evaluation using proven mathematical techniques adapted specifically for decentralized finance and smart contract security environments.
Bayesian risk assessment methodologies incorporate prior probability distributions based on historical vulnerability patterns and exploit data to calculate posterior risk estimates for smart contract security. Prior probability assignments leverage comprehensive databases of past security incidents across different contract types and blockchain networks to establish baseline risk levels. Evidence integration continuously updates risk assessments as new vulnerability information and exploit patterns emerge from ongoing security research and incident response activities.
Monte Carlo simulation techniques generate thousands of potential attack scenarios to assess smart contract resilience under different threat conditions and market environments. Probabilistic modeling incorporates uncertainty in attacker capabilities, exploit complexity, and defensive effectiveness to provide confidence intervals for security assessments. Scenario analysis examines specific attack sequences including flash loan exploits, oracle manipulation, and governance attacks with their associated likelihood distributions based on historical data and smart contract architecture characteristics.
Extreme value theory applications model the probability and impact of rare but catastrophic security events that traditional audit methodologies significantly underestimate. Generalized extreme value distributions capture the tail behavior of exploit severity to quantify maximum potential losses from successful attacks. Peak-over-threshold models identify when security incidents exceed normal operational risk levels and require emergency response procedures including contract pausing or emergency withdrawal mechanisms.
Regression analysis frameworks identify the strongest predictors of successful exploits from comprehensive datasets of security incidents and smart contract characteristics. Multiple regression models achieve 80-90% accuracy in predicting exploit likelihood based on factors including contract complexity, deployment age, total value locked, developer team experience, and audit coverage completeness. Logistic regression models predict binary exploit outcomes while Poisson regression models predict attack frequency over time for different contract categories.
Linear programming optimization determines optimal allocation of audit resources across different security review activities subject to budget constraints and timeline requirements. Objective functions maximize security coverage or minimize residual risk while constraint equations ensure compatibility with project deadlines and regulatory compliance obligations. Sensitivity analysis examines how changes in resource availability or threat landscapes affect optimal audit configurations and security investment strategies.
Integer programming models handle discrete audit decisions including whether to conduct specific types of security reviews or deploy particular defensive technologies. Binary variables represent yes-no decisions for different audit components while integer variables represent quantities of review hours to allocate across different smart contract modules. Mixed-integer programming combines continuous resource allocation decisions with discrete methodology selection decisions for comprehensive audit optimization.
Multi-objective optimization balances competing audit objectives including vulnerability detection rate, cost minimization, timeline compliance, and thoroughness maximization. Pareto frontier analysis identifies the set of non-dominated audit strategies that cannot be improved in one objective without degrading another objective. Weighted sum approaches combine multiple audit objectives into single optimization problems while constraint methods treat secondary objectives as constraints on primary objective optimization.
Game theory applications model the strategic interaction between audit teams and potential attackers to identify optimal security review strategies under different threat scenarios. Nash equilibrium solutions identify stable audit approaches where neither auditors nor attackers can improve their outcomes by unilaterally changing their strategies. Stackelberg games model scenarios where audit teams must commit to review methodologies first, allowing potential attackers to observe and adapt their exploitation techniques accordingly.
Graph theory applications model smart contract ecosystems as complex networks where nodes represent individual contracts and edges represent interactions including function calls, token transfers, and oracle dependencies. Network topology analysis identifies critical interaction pathways and single points of failure that could cascade into ecosystem-wide vulnerabilities. Centrality measures reveal which contracts are most critical to overall system security and require enhanced audit focus.
Flow network analysis quantifies the potential for value extraction through different smart contract interaction pathways during coordinated attacks. Maximum flow algorithms identify the maximum rate at which attackers could extract value through complex multi-contract exploits. Minimum cut algorithms identify the smallest set of contract interactions that would isolate critical assets from potential attackers during emergency response procedures.
Community detection algorithms identify clusters of related smart contracts that share similar risk profiles and vulnerability patterns. Network clustering reveals contract groups that should be audited together due to their interconnected dependencies and shared attack surfaces. Modularity optimization techniques partition contract networks into coherent audit scopes that maximize internal security coherence while minimizing cross-module dependencies.
Dynamic network analysis examines how smart contract interaction patterns evolve over time and how these changes affect security risk profiles. Temporal network modeling captures the evolution of contract dependencies as new integrations are added and old connections are deprecated. Centrality evolution analysis identifies contracts that become increasingly critical to ecosystem security over time and require ongoing audit attention.
Information theory applications quantify the entropy and randomness characteristics of cryptographic implementations within smart contracts to ensure sufficient security margins against statistical and brute force attacks. Shannon entropy calculations measure the unpredictability of cryptographic seeds and random number generation mechanisms. Mutual information analysis identifies potential information leakage in cryptographic protocol implementations that could enable attack vector development.
Formal verification methodologies use mathematical proofs to verify critical security properties of smart contract implementations and their underlying cryptographic protocols. Model checking algorithms automatically verify whether contract implementations satisfy specified security invariants and behavioral properties. Theorem proving approaches provide rigorous mathematical guarantees about protocol security under explicitly specified assumptions and threat models.
Side-channel analysis examines unintended information leakage through timing variations, gas consumption patterns, and other observable characteristics of smart contract execution. Statistical analysis methods including correlation analysis and mutual information estimation detect subtle patterns that could reveal sensitive information about contract state or user activities. Countermeasure effectiveness quantification measures information leakage reduction achieved through various defensive implementations.
Post-quantum cryptography assessment evaluates the long-term security of smart contract cryptographic components against future quantum computing attacks. Security bit calculations compare classical and quantum attack complexities to determine when quantum attacks become computationally feasible. Migration analysis identifies optimal timing and implementation strategies for transitioning smart contracts to quantum-resistant cryptographic algorithms.
Security coverage metrics establish quantitative measures for assessing and comparing the effectiveness of different audit approaches across smart contract ecosystems. Vulnerability detection rate metrics measure the percentage of actual security flaws identified during audit processes. False positive and false negative rates quantify audit accuracy and reliability across different contract types and complexity levels.
Code coverage analysis measures the percentage of smart contract execution paths examined during security review processes. Branch coverage metrics ensure that all conditional logic pathways receive appropriate audit attention. Function coverage analysis verifies that all contract functions undergo thorough security evaluation. State coverage assessment ensures that all possible contract states and their transitions receive adequate security review.
Economic impact assessment frameworks quantify the potential financial consequences of successful exploits across different smart contract vulnerability categories. Value-at-risk calculations estimate maximum potential losses under different attack scenarios with specified confidence levels. Expected loss calculations combine exploit probabilities with impact assessments to provide comprehensive risk metrics for audit prioritization and insurance evaluation.
Audit quality metrics establish standardized measures for evaluating and comparing the effectiveness of different security audit services and methodologies. Thoroughness metrics assess the depth and comprehensiveness of security review processes. Accuracy metrics quantify the reliability of vulnerability detection and classification. Timeliness metrics measure audit completion speed relative to project requirements and market conditions.
Real-time risk scoring systems continuously evaluate smart contract security posture based on ongoing threat intelligence, vulnerability disclosures, and ecosystem changes. Dynamic risk models incorporate new threat information and adjust security assessments as contract environments evolve. Automated risk recalculation ensures that security evaluations remain current despite changing threat landscapes and contract modifications.
Temporal risk analysis examines how smart contract security risk profiles change over time due to factors including code modifications, ecosystem integrations, and threat landscape evolution. Hazard function modeling predicts when contracts are most vulnerable to successful attacks based on deployment age, modification history, and external dependency changes. Survival analysis techniques estimate the probability that contracts will remain exploit-free over specified time periods.
Comparative risk benchmarking frameworks enable quantitative comparison of smart contract security postures across different projects, ecosystems, and development teams. Statistical benchmarking identifies contracts and projects that significantly deviate from typical security risk profiles within their categories. Best practice identification highlights security implementation approaches that consistently achieve superior risk profiles across similar contract types.
Predictive risk modeling uses machine learning techniques trained on historical security incident data to forecast future vulnerability emergence and exploit likelihood. Time series forecasting predicts when new vulnerability types are likely to emerge based on development trends and threat actor capabilities. Early warning systems provide advance notice of increasing risk levels before actual exploits occur, enabling proactive security improvements and defensive measure implementation.
Traditional security audit services depend on manual review processes and human expertise but lack artificial intelligence capabilities that enable automated vulnerability discovery and predictive security analysis through machine learning algorithms. AI-powered audit systems transform reactive security review into proactive systematic intelligence that predicts emerging vulnerabilities, identifies sophisticated attack patterns, and automatically adapts to evolving threat landscapes using advanced neural networks and behavioral modeling techniques specifically designed for smart contract security applications.
Supervised learning models trained on comprehensive datasets of historical smart contract vulnerabilities and security incidents achieve 85-95% accuracy in identifying potential security flaws before human auditors begin their review process. Convolutional neural networks analyze smart contract bytecode patterns and function call structures to detect vulnerable code patterns that traditional static analysis tools frequently miss. Feature engineering algorithms automatically extract predictive security indicators from contract compilation artifacts, gas consumption patterns, and interaction behaviors.
Natural language processing models analyze smart contract source code comments, documentation, and variable naming patterns to identify inconsistencies between intended functionality and actual implementation that often indicate security vulnerabilities. Code semantic analysis uses transformer architectures including BERT and GPT variants specifically fine-tuned on Solidity and other smart contract programming languages to understand contextual meaning and identify logical flaws.
Ensemble learning frameworks combine multiple machine learning models including random forests, gradient boosting, and deep neural networks to achieve superior vulnerability detection accuracy compared to individual algorithms. Voting mechanisms aggregate predictions from diverse model architectures to reduce false positive rates while maintaining high sensitivity for actual security vulnerabilities. Cross-validation ensures model robustness across different smart contract categories and blockchain ecosystems.
Transfer learning techniques adapt pre-trained models across different blockchain networks and smart contract standards to provide accurate vulnerability detection for new ecosystems without requiring complete model retraining. Domain adaptation algorithms adjust models trained on Ethereum smart contracts to work effectively with Solana, Cardano, and other blockchain environments while preserving detection accuracy. Few-shot learning enables rapid model adaptation to novel vulnerability types using minimal training examples when new attack vectors emerge.
Recurrent neural networks with long short-term memory units analyze temporal sequences in smart contract deployment patterns, modification histories, and interaction behaviors to identify security risk indicators that develop over time. Sequence modeling captures dependencies between different contract functions and state transitions that could create exploitable conditions under specific circumstances. Attention mechanisms identify which specific code elements and interaction patterns contribute most significantly to overall security risk assessments.
Graph neural networks model complex relationships between smart contracts, external dependencies, and ecosystem participants to identify coordinated vulnerabilities that span multiple contracts. Node embedding techniques create vector representations of different contracts that capture their behavioral characteristics and interaction patterns within broader DeFi ecosystems. Graph convolutional networks propagate security information through contract relationship networks to identify influential nodes and potential attack coordination points.
Generative adversarial networks learn to distinguish between secure and vulnerable smart contract patterns while generating synthetic vulnerable code examples for training data augmentation. Discriminator networks achieve 90-95% accuracy in distinguishing between secure and vulnerable contract implementations while generator networks create realistic vulnerable code patterns that enhance training dataset diversity. Adversarial training improves model robustness against sophisticated evasion attempts by potential attackers.
Autoencoder architectures learn to reconstruct normal smart contract behavioral patterns and identify anomalies by measuring reconstruction error for new contract implementations. Variational autoencoders generate probabilistic representations of contract behavior that enable uncertainty quantification in security assessments. Denoising autoencoders filter out irrelevant implementation details to focus on core security-relevant behavioral patterns that indicate potential vulnerabilities.
Time series forecasting models predict the emergence of new vulnerability types and attack techniques based on historical patterns in security research publications, exploit development, and threat actor capabilities. LSTM networks analyze temporal patterns in vulnerability disclosure rates across different smart contract categories to predict when new vulnerability classes are likely to emerge. Prophet models capture seasonal patterns and trend changes in threat landscape evolution to improve prediction timing accuracy.
Behavioral analysis models establish baseline patterns for normal smart contract ecosystem activity and automatically identify deviations that might indicate preparation for coordinated attacks or exploit development. Hidden Markov models capture state transitions in ecosystem behavior that precede major security incidents. Clustering algorithms group similar behavioral patterns to identify distinct threat preparation phases and attack coordination activities.
Sentiment analysis and topic modeling algorithms analyze security research publications, vulnerability databases, and hacker forum discussions to identify emerging attack techniques and defensive countermeasures before they become widely adopted. Named entity recognition identifies specific vulnerability types, attack tools, and threat actor groups mentioned in security intelligence sources. Relationship extraction algorithms identify connections between different threats and their associated exploitation techniques.
Threat attribution analysis uses machine learning techniques to identify patterns that connect different security incidents to specific threat actors or attack campaigns. Stylometric analysis examines coding patterns and implementation choices in exploit code to identify potential connections between different attacks. Network analysis models relationships between different attack activities to identify coordinated campaigns that span multiple targets and time periods.
Multi-armed bandit algorithms optimize the allocation of audit resources across different smart contract components and vulnerability categories to maximize detection of actual security threats while minimizing false positive investigation costs. Contextual bandits incorporate real-time threat intelligence and contract characteristics to adapt audit intensity based on current risk levels and ecosystem conditions. Thompson sampling provides optimal exploration-exploitation balance for discovering new vulnerability types while maintaining detection of known threat patterns.
Q-learning algorithms develop optimal audit strategies that balance thoroughness with efficiency in security review processes. Policy gradient methods learn optimal sequences of audit actions that maximize vulnerability detection probability while minimizing total review costs and timeline requirements. Actor-critic algorithms balance automated analysis with human expert involvement to optimize overall audit accuracy and resource efficiency.
Online learning systems continuously adapt security models based on new vulnerability discoveries and exploit techniques to maintain detection accuracy as threat landscapes evolve. Incremental learning algorithms update model parameters in real-time without requiring complete retraining when new attack vectors emerge. Meta-learning approaches enable rapid adaptation to completely new vulnerability types by learning how to learn from minimal training examples.
Adversarial reinforcement learning techniques improve audit robustness against sophisticated attackers who might attempt to evade detection by understanding and gaming security analysis algorithms. Adversarial training exposes models to examples specifically designed to fool detection systems during training to improve resistance to evasion attempts. Game-theoretic approaches model interactions between security analysis systems and potential attackers to develop robust defensive strategies.
Stream processing architectures analyze continuous flows of blockchain transaction data, contract deployment events, and ecosystem activity to provide real-time security intelligence with minimal latency. Complex event processing identifies patterns that span multiple data sources and time windows to detect coordinated activities that might indicate preparation for sophisticated attacks. Edge computing deployments ensure low-latency analysis for time-critical security applications and emergency response scenarios.
Automated threat detection systems generate prioritized security alerts based on AI-generated risk assessments and confidence levels to focus human attention on the most critical potential threats. Smart notification systems adapt alert frequency and communication channels based on threat severity and analyst preferences to avoid alert fatigue while ensuring critical threats receive immediate attention. Escalation procedures automatically involve appropriate security experts when automated systems detect high-confidence threats.
Integration frameworks connect AI-powered security analysis with existing blockchain security infrastructure including monitoring platforms, incident response systems, and emergency pause mechanisms. API interfaces provide real-time security scores and threat intelligence to external applications and decision-making systems. Webhook systems enable immediate automated responses including contract pausing and emergency fund protection when critical threats are detected.
Continuous learning systems track model performance and prediction accuracy in real-world deployment environments to identify when models need updates or retraining. Performance dashboards visualize detection accuracy, false positive rates, and coverage metrics to provide transparency into system effectiveness for audit teams and project stakeholders. A/B testing frameworks validate improvements to detection algorithms before deploying them to production audit environments.
Federated learning systems enable collaborative model training across multiple audit firms and security providers without sharing sensitive client information or proprietary audit methodologies. Privacy-preserving techniques including differential privacy and secure multi-party computation allow organizations to collaborate on vulnerability detection while protecting competitive advantages and client confidentiality. Consensus mechanisms aggregate security intelligence from multiple sources while filtering out false or malicious threat reports.
Crowdsourced security validation systems leverage community security expertise to validate AI-generated vulnerability assessments and improve model accuracy through human feedback mechanisms. Reputation systems ensure that community contributions are weighted based on historical accuracy and demonstrated security expertise. Incentive mechanisms reward accurate vulnerability reporting and penalize false or misleading security information to maintain data quality standards.
Threat intelligence fusion platforms automatically combine information from multiple sources including commercial security feeds, open source vulnerability databases, and internal audit findings to create comprehensive security assessments. Information fusion algorithms resolve conflicts between different intelligence sources and assess the credibility and reliability of security reports. Attribution analysis attempts to connect different vulnerability patterns to specific development practices or attack methodologies.
Rapid response coordination systems enable quick industry-wide warnings when sophisticated new vulnerability types or attack techniques are detected by AI analysis systems. Emergency broadcast mechanisms rapidly disseminate critical security information across multiple blockchain ecosystems and development communities. Coordinated investigation protocols enable multiple security providers to collaborate on analyzing sophisticated threats that require diverse expertise and analytical capabilities.
Machine learning quality assessment models automatically evaluate the thoroughness and accuracy of security audit reports and recommendations. Natural language processing analyzes audit report content to ensure comprehensive coverage of critical security domains and appropriate depth of analysis for contract complexity levels. Automated completeness checking verifies that audit processes followed established methodologies and industry best practices for security review.
Cross-validation systems compare AI-generated vulnerability assessments with human expert evaluations to ensure accuracy and reliability of automated analysis results. Statistical agreement analysis measures the consistency between automated and manual security assessments across different vulnerability categories and contract types. Confidence calibration ensures that AI-generated security scores accurately reflect the true probability of vulnerability existence.
Bias detection and mitigation algorithms identify and correct systematic biases in automated security analysis that could lead to unfair or inaccurate assessments across different development teams, contract categories, or blockchain ecosystems. Fairness metrics ensure that AI-powered audit systems provide equitable security assessments regardless of project characteristics or developer backgrounds. Transparency mechanisms provide explainable AI insights that allow human auditors to understand and validate automated security decisions.
Continuous improvement frameworks systematically collect feedback from security incident outcomes to refine and enhance AI-powered audit capabilities. Post-incident analysis correlates AI-generated security assessments with actual exploit outcomes to identify areas for model improvement and calibration. Learning from failure mechanisms ensure that missed vulnerabilities and false assessments contribute to enhanced future detection capabilities through systematic model updates and refinement processes.
Diving into security audit services can feel like a maze, especially when a project's future is on the line. Founders, investors, and traders all have the same burning questions about what goes into an audit, what it costs, and what it really means for a project's safety.
Let's cut through the jargon and get you some straight answers. Here’s a breakdown of the most common questions we hear in the DeFi space, designed to give you the clarity you need to make smart decisions.
There's no simple answer here—the cost of a smart contract audit really depends on two big things: complexity and scope. A basic token contract, for instance, might run you anywhere from $5,000 to $15,000. It's relatively straightforward work.
But for a sprawling DeFi protocol with multiple smart contracts and tricky economic logic, you could be looking at a bill well over $100,000. The final price tag is usually influenced by the lines of code (LoC), how new or unusual the core logic is, and of course, the auditing firm's reputation.
The key thing to remember is that you're paying for deep expertise, not just billable hours. Elite firms charge a premium because their auditors have a knack for finding those subtle, catastrophic bugs that others might overlook.
It’s always a good idea to get quotes from a few different firms. When you do, don't just look at the bottom line. Compare the depth of their proposed review, the experience of the actual auditors who will be on your project, and how thorough their process looks.
Absolutely not. This is probably the single biggest misconception in all of DeFi. A passed audit does not mean a project is 100% safe or hack-proof. What it does mean is that the risk has been significantly lowered.
Think of an audit as a rigorous, expert-led home inspection before you buy a house. It confirms that on the day of the review, the code was solid and free of any visible vulnerabilities. It’s a huge vote of confidence, but it’s not an unbreakable force field.
An audit simply can't protect you from everything, such as:
Seeing a "passed" audit is a great sign, but it should be just one part of your research, alongside the project's ongoing security measures.
Just like cost, the timeline for an audit is tied directly to the project's size. A small, simple contract review could be wrapped up in just one to two weeks.
On the other hand, a large, interconnected DeFi protocol usually needs four to eight weeks, sometimes more. That longer timeline covers the entire process, from start to finish.
A typical audit schedule breaks down like this:
Because it's a multi-step journey, teams need to book their audit slots well ahead of their launch date to avoid any last-minute delays.
Manual and automated auditing aren't rivals; they're partners. Any high-quality security audit service will use a healthy mix of both because they each play a crucial role.
Automated auditing is all about speed and efficiency. Specialized software scans the code for common, known vulnerabilities, catching the low-hanging fruit and ensuring best practices are followed. It’s fast, but its analysis is surface-level.
Manual auditing is where the real magic happens. Human experts go through the code line by line, using their experience and intuition to understand the project's specific logic. This is the only way to find the truly dangerous, context-specific flaws.
.tbl-scroll{contain:inline-size;overflow-x:auto;-webkit-overflow-scrolling:touch}.tbl-scroll table{min-width:600px;width:100%;border-collapse:collapse;margin-bottom:20px}.tbl-scroll th{border:1px solid #ddd;padding:8px;text-align:left;background-color:#f2f2f2;white-space:nowrap}.tbl-scroll td{border:1px solid #ddd;padding:8px;text-align:left}Auditing MethodKey StrengthsBest For FindingAutomated AuditingSpeed, efficiency, broad coverage of known issues.Common bugs, outdated libraries, standard vulnerability patterns.Manual AuditingDeep analysis, contextual understanding, creative problem-solving.Complex logic flaws, economic exploits, unique or novel vulnerabilities.
Here's a simple way to think about it: an automated tool can check if a door is locked, but a manual audit is what tells you if the whole wall can be easily knocked down. You need both machine speed and human intelligence for a truly strong security review.
Advanced mathematical models achieve 80-90% accuracy in predicting exploit likelihood through Bayesian risk assessment that incorporates prior probability distributions based on historical vulnerability patterns and comprehensive incident databases. Monte Carlo simulation generates thousands of potential attack scenarios to assess smart contract resilience with confidence intervals, while extreme value theory models rare but catastrophic security events that traditional audit methodologies significantly underestimate. Graph theory applications identify critical interaction pathways and single points of failure through network topology analysis, and multi-objective optimization balances competing audit objectives including vulnerability detection rate, cost minimization, and thoroughness maximization. Mathematical optimization determines optimal resource allocation across different security review activities subject to budget and timeline constraints while achieving superior audit coverage compared to traditional approaches.
AI-powered audit systems achieve 85-95% accuracy in identifying potential security flaws before human auditors begin their review process using supervised learning models trained on comprehensive datasets of historical smart contract vulnerabilities. Natural language processing analyzes smart contract source code and documentation to identify inconsistencies between intended functionality and actual implementation, while graph neural networks model complex relationships between smart contracts to identify coordinated vulnerabilities that span multiple contracts. Deep learning pattern recognition achieves 90-95% accuracy in distinguishing between secure and vulnerable contract implementations through convolutional neural networks and recurrent architectures. Real-time stream processing provides security intelligence with minimal latency while reinforcement learning algorithms continuously adapt audit strategies to maintain detection accuracy as threat landscapes evolve and new attack vectors emerge.
A thorough security audit is the first step, but maintaining security is an ongoing process. Use Wallet Finder.ai to monitor on-chain activity, track smart money, and get real-time alerts on suspicious transactions. Protect your investments by turning the blockchain's data into your own personal security feed. Get started with a free trial today.