Buy the Dip Crypto: Master Smart Entry Strategies
Buy the dip crypto - Master buy the dip crypto without getting burned. Learn step-by-step signals, optimal entry timing, risk management, & how to mirror smart

May 9, 2026
Wallet Finder

March 11, 2026

Relying on a single crypto wallet is like throwing your life savings, your weekly grocery money, and your high-risk stock picks into one big shoebox under your bed. It's a recipe for chaos and a massive security headache. For anyone serious about crypto, adopting a multiple crypto wallet strategy isn't just a good idea—it's absolutely essential.

The days of a "one-wallet-fits-all" approach are long gone. The crypto space has evolved, and so have the risks and opportunities. This shift is mirrored in the market itself; the global cryptocurrency wallet market was valued at $2,722.6 million back in 2021 and is on a trajectory to more than double by 2025.
With over 420 million crypto owners worldwide in 2024, the demand for smarter, more secure asset management has exploded. You can dig into more of these market insights on the growth of crypto wallets on cognitivemarketresearch.com.
This isn't just about more people piling in. It’s about investors getting smarter. They understand that different activities demand different tools and security levels. Funneling every transaction through a single wallet creates one giant bullseye for attackers. If that one wallet gets compromised, you could lose everything.
At its core, a multiple wallet strategy is all about managing risk. By splitting your funds into dedicated wallets, you're essentially building firewalls between your different piles of assets.
Think about it: you've found a new, unaudited DeFi protocol that promises insane yields. Are you really going to connect your main wallet—the one holding your long-term Bitcoin and Ethereum—to that contract? That's a huge, unnecessary gamble.
A seasoned pro would never do that. Instead, they’d use a dedicated "burner" wallet, funded with a small, expendable amount of crypto, just for these kinds of experiments. This simple act of separation shields the bulk of their portfolio from potential smart contract bugs or a clever phishing attack.
The core principle is simple but incredibly powerful: Isolate your risk. Never let your entire portfolio touch a single high-risk activity. Your HODL stash should live in a completely different universe from your daily degen trading funds.
Beyond the huge security upgrade, using multiple wallets brings much-needed organization to your crypto life. It lets you sort your assets by purpose, which makes tracking performance and making clear-headed decisions way easier. This organized approach is what separates the pros from the amateurs.
To give you a clearer picture, here’s a quick breakdown of why separating your wallets is a game-changer.
Long-term holding, often called HODLing, is the strategy that demands the highest security standard of any wallet use case. When you are storing core Bitcoin and Ethereum positions that you do not intend to touch for months or years, the primary benefit you are optimizing for is protection from online threats. A hardware wallet kept almost entirely offline and only connected to a device when an actual transaction is required is the correct tool for this purpose, because the private keys never enter an internet-connected environment during normal storage.
Active trading sits at the opposite end of the accessibility spectrum. When your strategy involves frequent trades on decentralized exchanges, speed matters and the friction of a hardware wallet becomes a liability. A hot software wallet holding only the stablecoins and volatile assets needed for your current trading activity gives you the quick access that execution requires, with the understanding that this convenience comes with meaningfully higher exposure to online threats compared to cold storage.
DeFi and staking activity introduces a specific risk that neither of the above wallets should absorb: smart contract interaction. Every time you connect to a lending protocol, liquidity pool, or yield farm, you are granting that contract permissions over your wallet's tokens. Isolating all of this activity in a dedicated wallet means that if a protocol is exploited or a malicious approval is granted, the damage is contained to that wallet alone and your long-term holdings and trading capital remain untouched.
NFT collecting adds an organizational dimension on top of the security argument. Keeping digital collectibles in their own wallet prevents them from becoming entangled with your fungible token activity, eliminates the risk of an accidental sale triggered by an approval granted in a different context, and makes portfolio management significantly cleaner since the full value and composition of your collection is visible in one place without being obscured by other asset types.
Here are some common, actionable setups:
This structure transforms a messy pile of digital assets into a well-oiled portfolio, where every component has a specific job and a defined risk level.
Creating multiple wallets provides zero privacy benefit if you fund them all from the same source. Every time you withdraw from Coinbase to three different "separate" wallets, you're creating permanent on-chain links that cluster those wallets together. Blockchain analysis tools can trivially identify they belong to the same person, defeating the entire purpose of wallet separation.
The clustering works through transaction graph analysis. If address A sends ETH to addresses B, C, and D in separate transactions, those addresses become linked. Even if B, C, and D never interact with each other afterward, their common funding source proves common ownership. Analysis tools score this relationship with extremely high confidence.
The problem compounds when you repeatedly fund wallets using similar patterns. Withdrawing 1 ETH from Coinbase to Wallet A on Monday, 1 ETH to Wallet B on Tuesday, and 1 ETH to Wallet C on Wednesday creates obvious patterns. The timing, amounts, and source create a signature linking all three.
More sophisticated users try to obscure this by varying amounts or adding delays. They might send 0.8 ETH, then 1.2 ETH, then 0.95 ETH with days between transactions. But if all three still originate from the same exchange account, the clustering algorithm still connects them with high probability.
The exchange deposit address acts as a permanent identifier. Every withdrawal from your Coinbase account carries metadata linking it to your KYC identity. When Wallet A, B, and C all trace back to the same deposit address, they're all linked to your real-world identity regardless of how you tried to obscure the transfers.
Even if you fund wallets separately, interactions between them destroy privacy. Sending tokens from Wallet A to Wallet B directly creates an obvious link. But even indirect interactions cluster wallets together.
If Wallet A interacts with a DeFi protocol, then Wallet B interacts with the same protocol minutes later from the same IP address, analysis tools flag them as likely related. The timing correlation plus behavioral similarity (using same protocols, same liquidity pools, same gas price strategies) creates probabilistic links.
Multi-input transactions are catastrophic for privacy. If you need to consolidate funds from three wallets to make a large purchase, combining UTXOs from all three in a single transaction permanently proves they're controlled by one entity. This single transaction undoes all previous separation efforts.
True wallet separation requires funding from independent sources. Buy crypto with cash through Bitcoin ATMs for one wallet. Use a different exchange for another. Accept peer-to-peer payments for a third. Each wallet needs a distinct origin story that doesn't trace back to a common source.
For Ethereum and other account-based chains, intermediate mixer/tumbler steps can break funding links. Send ETH from exchange to Tornado Cash, wait varying amounts of time (hours to days), then withdraw to your destination wallets. This breaks the direct transaction graph link between source and destinations.
Layer 2 solutions provide another separation method. Bridge from mainnet to Arbitrum, then from Arbitrum to Optimism, then withdraw to final wallet. Each bridge hop and chain transition complicates clustering because tools must track across multiple networks. Not perfect privacy, but significantly better than direct transfers.
The gold standard is mining or earning crypto directly to the wallet you want to keep separate. Run a validator or miner paying out directly to Wallet A. Earn freelance payments to Wallet B. These wallets have no funding transaction linking them to your exchange accounts or other addresses.
Building a personal wallet ecosystem isn't about becoming a tech wizard. It’s about smart, strategic planning. Think of it like organizing your regular finances—you wouldn't keep your life savings in the same checking account you use for daily coffee runs. The same logic applies here. You’re creating a tiered system to balance rock-solid security with everyday accessibility.
The goal is to separate your crypto assets into distinct buckets based on what you’re doing with them and how much risk you’re taking on. This isn't a rigid framework; it's a flexible model you can tweak for your own strategy. By creating these divisions, you build a resilient system where a screw-up in one area doesn’t sink your entire portfolio.
For most people, a three-tiered structure works best.
This is the bedrock of your setup, built for maximum security. It’s where you stash your core, long-term holdings—the assets you don't plan on touching for months, or even years.
Next up is your 'hot' wallet, designed for accessibility and frequent use. This is usually a software wallet—think a browser extension like MetaMask or a mobile app like Trust Wallet. This wallet should only hold the funds you need for regular trading, interacting with dApps you trust, or making quick payments.
A critical mistake new users make is using a single hot wallet for everything. By adopting a multiple crypto wallet approach, you're not just organizing—you're actively building layers of security that protect you from both hackers and your own simple mistakes.
The final tier is for specific, often higher-risk, activities. This is where you create separate 'burner' wallets for testing out new DeFi protocols, farming airdrops, or minting NFTs. Each of these wallets should be funded with only the amount of crypto you're fully prepared to lose.
This level of compartmentalization is a hallmark of sophisticated crypto management and is becoming standard for many of the 420 million people who owned crypto wallets by 2024. You can dive deeper into this trend in the 2025 Global Adoption Index from chainalysis.com.
Switching over to a multiple-wallet system is a huge security upgrade, but only if you nail the setup process. One small mistake can bring the whole structure crashing down. Your absolute number one priority is mastering seed phrase management.
Your seed phrase—that list of 12 or 24 words—is the master key to everything in that specific wallet. Let me be blunt: storing this digitally is a catastrophic mistake. A text file, a password manager, or a cloud drive can be compromised. If that happens, your crypto is gone. Forever.
The only truly safe way to store a seed phrase is offline. This means writing it down physically and keeping it safe from both prying eyes and physical damage. Here are actionable methods:
This entire process is about creating a clear flow from your most secure, long-term holdings to your more active, experimental funds.
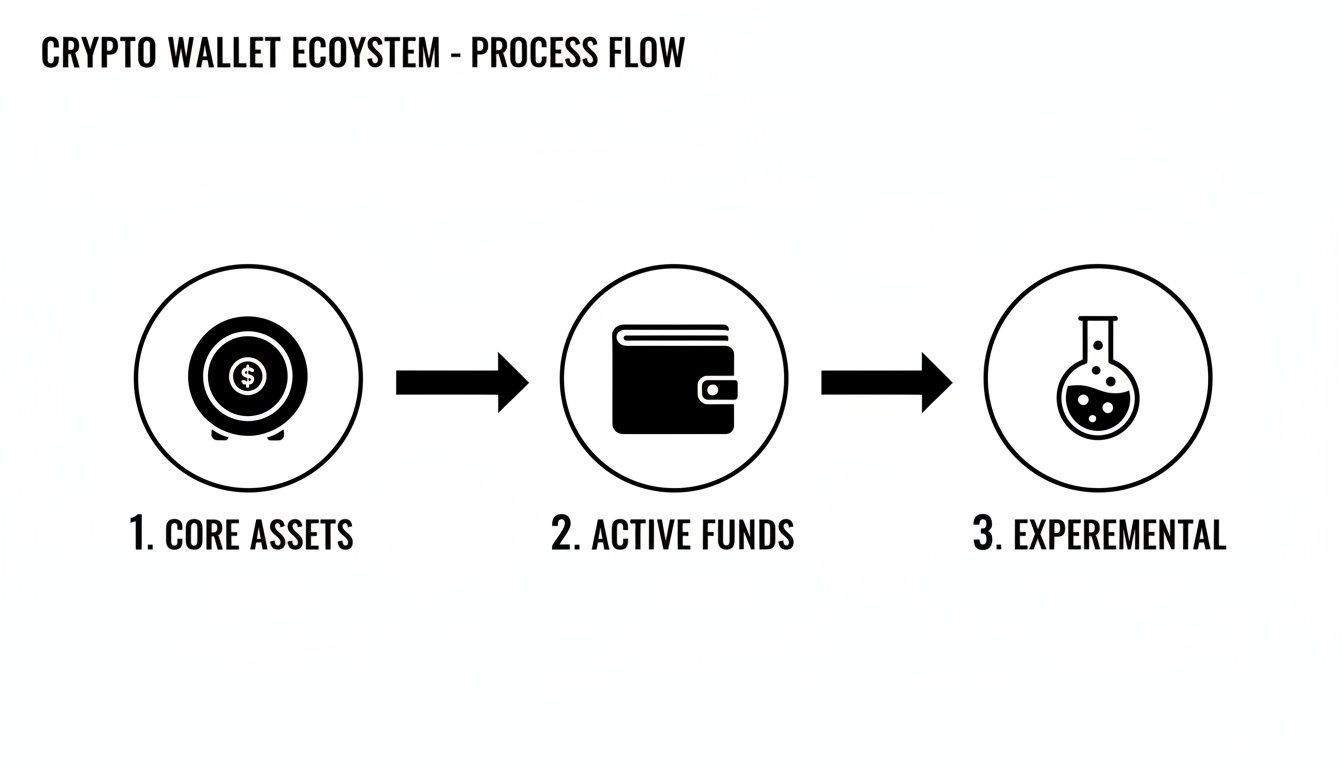
As you can see, the idea is to have a tiered approach, moving from your heavily protected "Core Assets" out towards more accessible "Active Funds" and finally your high-risk "Experimental" wallets.
Whenever you set up a new wallet, especially a hardware wallet, follow a strict protocol. Never create a wallet or initialize a device on a public Wi-Fi network like a coffee shop or airport. Always use a secure, private connection.
For hardware wallets like a Ledger or Trezor, the device itself is designed to generate your private keys completely offline. You then connect it to a software interface like MetaMask or Phantom to interact with dApps. This setup gives you the best of both worlds: the Fort Knox security of cold storage with the everyday convenience of a hot wallet, because your keys never actually leave the physical device.
Here's a pro-level tip: Use a dedicated, "clean" device—like a cheap laptop or an old phone that's used only for crypto. This creates an isolated environment, massively reducing your exposure to malware you might pick up from daily browsing or opening emails.
By putting these practices into place, you're building a real fortress around your digital assets. For an even deeper dive, run through this comprehensive checklist for assessing wallet risks to make sure all your bases are covered.
The standard advice is backing up seed phrases by writing them down and storing them securely. But when you have five wallets, storing all five seed phrases in the same location creates a catastrophic single point of failure worse than using one wallet. If someone finds your safe or your safe deposit box, they get everything instantly.
This defeats the entire risk isolation benefit of multiple wallets. The purpose was creating firewalls so a compromise of one wallet doesn't cascade. But if all seed phrases live in the same physical location, compromising that location gives the attacker simultaneous access to all wallets.
The more wallets you create, the more seed phrases you must secure. Each one is a critical secret requiring robust physical security. But you probably only have one or two truly secure storage locations — your home safe and maybe a bank safe deposit box.
Storing all seed phrases in your home safe means a home burglary or fire destroys access to every wallet simultaneously. The separation that protected you from smart contract exploits offers zero protection against physical threats. You've actually increased surface area (more seed phrases to secure) while concentrating vulnerability (all in one location).
Splitting seed phrases across multiple locations (home safe, bank box, trusted family member) improves physical redundancy but increases operational complexity. Now you need to visit three locations to recover your wallets after device loss. And you've tripled the number of people or institutions who could potentially access your funds.
Some users try memorizing seed phrases instead of writing them down. With one twelve-word phrase, this is marginally feasible (though still dangerous — memory fails). With five separate phrases totaling sixty words, it's completely unrealistic. You will forget them, especially under stress.
Attempting to memorize multiple phrases also increases the risk of confusing which phrase goes with which wallet. You remember the words but can't recall if "ability ... zebra" is your trading wallet or your HODL wallet. Testing each phrase to find the right one exposes them unnecessarily.
The secure approach is distributing seed phrases across independent physical locations with appropriate redundancy. Wallet 1 phrase in home safe. Wallet 2 phrase in bank safe deposit box. Wallet 3 phrase at trusted family member's secure location.
For critical high-value wallets, implement multi-signature or Shamir's Secret Sharing. Split the seed phrase into three shares where any two can recover it. Store Share A in home safe, Share B in bank box, Share C with trusted person. Compromising any single location reveals nothing. You need two locations to recover.
Metal backups distributed geographically protect against localized disasters. Home fire destroys the seed phrase stored there, but the bank box copy survives. Regional disaster (earthquake, flood) destroys both home and local bank, but the copy in a different state/country survives.
For wallets holding truly massive value, consider professional custody solutions that implement institutional-grade key management with geographic distribution, multi-signature controls, and disaster recovery procedures. This costs money but eliminates the single point of failure problem entirely.
Juggling multiple crypto wallets is smart for security, but it creates a new headache: keeping track of everything. Constantly jumping between different wallet apps and blockchain explorers just to get a clear picture of your net worth is exhausting and inefficient.
The solution is to pull everything together into a single, clean dashboard using a portfolio tracker. Just plug in your public wallet addresses, and these tools automatically fetch data from across different blockchains, giving you an instant, real-time snapshot of your entire portfolio.
Powerful platforms can bring order to your multi-wallet chaos. Tools like Zapper, Zerion, and DeBank are fantastic places to start. They connect to dozens of chains and hundreds of protocols, so you can be confident pretty much all of your assets will show up automatically.
The real magic happens when you organize that consolidated view. Here's how to make it actionable:
This level of organization turns a scattered mess of assets into a portfolio that actually makes sense. We’ve put together a detailed walkthrough in our guide on how to track DeFi portfolios across multiple wallets.
While standard portfolio trackers are great for keeping an eye on your own bags, the next-level tools can turn this data into a source of powerful market intelligence. Instead of just looking inward at your own performance, you can start analyzing the moves of other top-performing wallets to find new opportunities.
This is where a platform like Wallet Finder.ai changes the game entirely. It goes beyond simple tracking and dives deep into active discovery and analysis. You can pinpoint highly profitable traders, comb through their entire transaction history, and even get alerts the second they make a move.
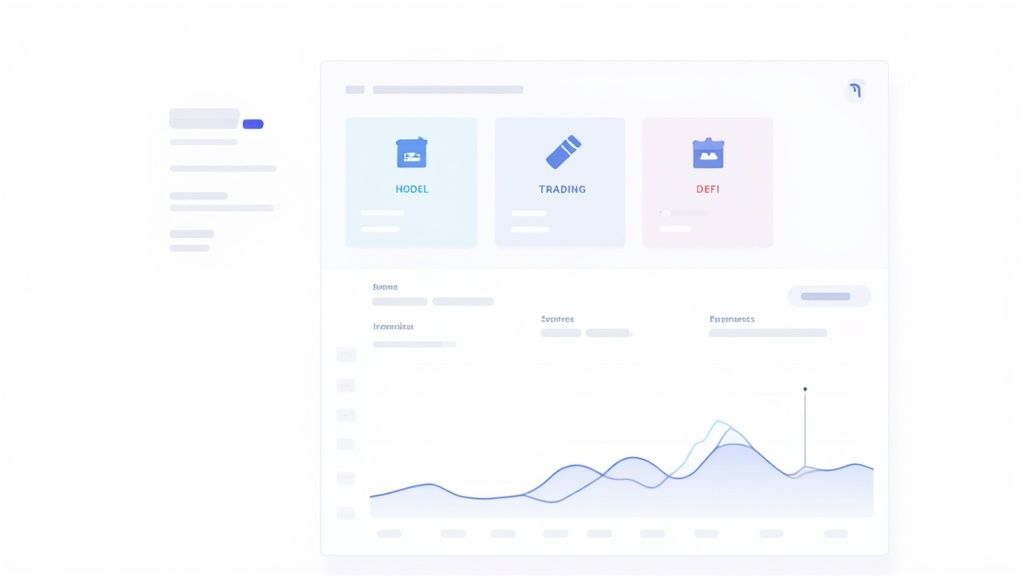
The dashboard above shows just how easy it is to filter for wallets with impressive PnL and high win rates, transforming raw on-chain data into signals you can actually use. This shifts you from being a passive observer of your portfolio to an active analyst of the market's smartest players.
By mirroring the strategies of consistently profitable wallets, you can uncover alpha that you would have otherwise missed. It’s like having a team of elite researchers working for you 24/7, with every move transparently recorded on the blockchain.
This approach combines the organizational power of a portfolio tracker with the strategic edge of on-chain intelligence, giving you a complete command center for your entire crypto strategy.
Every wallet on Ethereum requires ETH for gas fees. With one wallet, you maintain a single gas token balance covering all transactions. With five wallets, you need five separate ETH balances, fragmenting capital and creating constant rebalancing overhead.
The math is brutal. If you keep 0.5 ETH in your single wallet for gas, that covers months of transactions. Split across five wallets needing 0.5 ETH each, you're locking up 2.5 ETH total — five times the capital for the same transaction capacity. This idle capital could be deployed productively but instead sits fragmented across addresses waiting for gas usage.
Gas balances constantly drift as you use wallets unevenly. Wallet A used heavily for trading depletes its ETH. Wallet B barely touched accumulates excess ETH. You must periodically rebalance, sending ETH from overfunded wallets to underfunded ones.
Each rebalancing transfer costs gas, creating a tax on maintaining multiple wallets. If you rebalance monthly and each transfer costs $5 in gas, maintaining five wallets costs $20 per month in rebalancing overhead. That's $240 annually just moving gas tokens around — money that could be earning yield.
The rebalancing also creates transaction graph connections between wallets. Sending ETH from Wallet B to Wallet A links them on-chain. Repeated rebalancing over months creates obvious patterns that blockchain analysis tools use to cluster wallets.
Multi-chain strategies amplify the problem. You need ETH on Ethereum mainnet, ETH on Arbitrum, SOL on Solana, AVAX on Avalanche, MATIC on Polygon. With one wallet per chain, that's five gas token balances. With five wallets per chain, that's twenty-five separate balances to maintain.
Each chain has different gas token price volatility and transaction costs. ETH might pump 40% while your capital allocation to gas stays constant, meaning your gas balance is now excessive in dollar terms. SOL might dump 50%, meaning your gas balance is now insufficient. Constant cross-chain rebalancing becomes required.
One approach is designating a primary "hot" wallet on each chain that maintains most gas token holdings. Other wallets on that chain keep minimal gas balances (just enough for one transaction). When they need to transact, you first send gas from the primary wallet, then execute the transaction, then send any remaining gas back.
This centralizes gas capital in one wallet per chain but requires three transactions where one would have sufficed (send gas in, execute transaction, send gas out). If gas is expensive, the overhead negates the capital efficiency benefit.
Layer 2 solutions partially address this since gas costs are 10-100x lower. You can afford to keep fragmented gas balances because even 0.05 ETH per wallet on Arbitrum covers hundreds of transactions. But you still need mainnet ETH for bridging and L1 transactions.
Some wallets support "gas abstraction" where transactions can pay gas in the token being transferred rather than the native gas token. If you're selling 1000 USDC, the protocol takes 1005 USDC (1000 for you, 5 to swap for ETH gas). This eliminates the need to maintain separate gas balances but typically charges premium fees for the convenience.
The optimal strategy for high-value holders is accepting gas fragmentation as a cost of proper security. Lock up 2-3 ETH across wallets and treat it as infrastructure cost, not productive capital. For smaller holders where gas fragmentation represents 10%+ of portfolio value, consider reducing wallet count or concentrating activity on L2s where gas requirements are minimal.
Once you have your wallet system organized, the real fun begins. A multi-wallet system isn't just about defense; it's a launchpad for sophisticated plays that are clunky, or even impossible, with just one address. Each wallet becomes a specialized tool, letting you execute specific strategies with precision.
One of the smartest ways to use multiple wallets is to build a sandbox for your high-risk, high-reward ventures. Think about airdrop farming—it often means interacting with brand-new, unaudited smart contracts. Connecting your main wallet is a risk you shouldn't take.
By spinning up a dedicated "farming" wallet, you effectively quarantine any potential disaster. This same logic is a lifesaver for other degen activities:
Every move you make is etched onto the blockchain forever. Using one address for everything creates a public, easily searchable financial history for anyone to snoop on.
Segregating your activity across different wallets breaks this chain of data. It’s the on-chain equivalent of using different email addresses for different services, making it much harder for observers to connect all your financial dots.
Use one wallet for your CEX withdrawals, another for your DeFi adventures, and a third for private peer-to-peer deals. This simple act shatters your on-chain identity into disconnected pieces, dramatically improving your privacy.
Beyond risk management, a multi-wallet setup unlocks advanced financial maneuvers. A classic example is tax-loss harvesting. By keeping assets for this strategy in their own wallet, you can sell them to realize a loss for tax purposes without messing things up, like accidentally triggering a wash sale by repurchasing the same asset too soon in one of your other wallets.
This strategic separation is becoming more common as the market matures. Projections for the crypto wallet market show staggering growth, with software wallets leading the charge. This trend makes it easier for investors to use multiple wallets for distinct purposes—hot wallets for daily trading, cold storage for long-term holds, and specialized wallets for DeFi. It's just smart risk management.
Ultimately, mastering a multiple crypto wallet system turns you from a passive holder into an active strategist.
Setting up a multiple crypto wallet system is not a one-time task. The security architecture you build on day one degrades if it is not maintained, and the most common form of degradation is invisible: a slow accumulation of token approvals, stale connections, and dormant wallets that collectively represent a much larger attack surface than you realize. A multi-wallet system that is never audited offers significantly weaker protection than its structure implies.
A wallet audit is a scheduled review of every active wallet in your system to assess whether its current state matches its intended purpose, whether its approval history is clean, and whether the assets held in it are still appropriate for that wallet's risk tier. Most experienced crypto users conduct a full audit at least once per quarter, with lighter monthly checks on their most actively used hot wallets.
Every time you interact with a smart contract, you grant it a token approval — permission to move a specific token from your wallet on your behalf. Most users grant these approvals without reviewing the scope, and many protocols request unlimited approval by default because it saves users from re-approving on future transactions. The problem is that every active approval is an open door. If the protocol's contract is later exploited or upgraded maliciously, that approval remains valid and your funds remain accessible to it.
The practical solution is regular approval revocation using tools like Revoke.cash or the approval management features built into portfolio aggregators like DeBank. The audit workflow is straightforward: connect each wallet, review the full list of active approvals, and revoke any that belong to protocols you no longer use, protocols that have been deprecated or flagged for security issues, or any approval where the scope is unlimited and the protocol does not require it. Revoking an approval costs a small gas fee but eliminates a persistent vulnerability that most users never think about after the initial transaction.
For your Tier 3 experimental wallets, the cleanest approach is to revoke all approvals after each use and treat the wallet as functionally reset between experiments. This practice means that even if a contract you interacted with three months ago is later compromised, there is nothing left for it to access in that wallet.
A multi-wallet system is also a performance management tool. Because each wallet has a defined purpose, you can evaluate whether the capital allocated to it is being used effectively. Your active trading wallet's performance should be reviewed against a simple benchmark: did it outperform holding the same assets in your Tier 1 vault? If active trading is consistently underperforming passive holding after fees and gas costs, that is a signal to reduce the capital allocated to the trading wallet, not a reason to trade more frequently.
For DeFi and staking wallets, the review should include an assessment of whether the yield-to-risk ratio of current positions still justifies the capital commitment. Protocols that were offering attractive yields six months ago may now offer rates that do not compensate adequately for smart contract risk, particularly if their total value locked has declined significantly or their audit history has not kept pace with protocol upgrades.
Reassigning assets between tiers based on these performance reviews is part of managing the system rather than just maintaining it. Capital that has grown significantly in your trading wallet should be periodically transferred upward to your Tier 1 vault. Capital that is sitting idle in an experimental wallet without an active use case should be consolidated rather than left exposed in a wallet whose approvals may have accumulated without systematic review.
As the value of assets in your wallet system increases, the security standards for your seed phrase storage should scale proportionally. A laminated paper backup stored in a home safe may be adequate when a wallet holds a few hundred dollars worth of assets. As holdings grow into the tens of thousands, the standard should rise to include a second physical backup stored in a separate location, and potentially a metal backup for wallets holding significant long-term positions.
The key maintenance task here is verification. At each quarterly audit, physically confirm that your seed phrase backups are intact, legible, and stored exactly where you expect them to be. Hardware degrades, paper can be damaged, and physical storage locations can change. A seed phrase backup you cannot access when you need it is equivalent to no backup at all. Confirming the backup's integrity costs five minutes and protects everything held in that wallet indefinitely.
Once you start juggling multiple crypto wallets, a few questions are bound to pop up. It's totally normal to wonder about the practical side of things. Let's clear up some of the most common concerns so you can build out your system with confidence.
Yes, without a doubt. It’s significantly safer than putting all your eggs in one basket. Spreading your assets across different wallets is all about walling off risk. If a high-risk dApp drains your "burner" wallet, the damage is contained to that small amount. Your main stash, locked away in a separate hardware wallet, remains completely safe.
By separating your activities, you’re creating firewalls. A breach in one wallet doesn't cascade into a total portfolio wipeout, which is the nightmare scenario for anyone using a single-wallet setup for everything.
There isn't a single magic number, but for most active crypto users, a three-wallet system is the sweet spot. It strikes the perfect balance between security and usability.
Here’s a quick summary of the three-tier setup:
It definitely adds a layer, but modern crypto tax software is built for this situation. Platforms like Koinly or CoinTracker are lifesavers here. You just sync all your public wallet addresses and exchange accounts, and they pull everything together automatically. The software then crunches the numbers to calculate your capital gains and losses across your entire portfolio, saving you a massive headache.
Technically, you can import the same seed phrase into different wallet apps (like using your Ethereum seed in Phantom for Solana). But you absolutely should not. Doing this completely defeats the purpose of having separate wallets in the first place.
If that one seed phrase ever gets compromised, an attacker gets the keys to your entire kingdom. Every single wallet would be vulnerable. The only truly secure practice is to generate a unique, safely-stored seed phrase for each individual wallet you create. This keeps your security layers independent and robust.
Use independent funding sources for each wallet. Buy crypto with cash through Bitcoin ATMs for one wallet. Use different exchanges for others. Accept peer-to-peer payments for a third. Never fund multiple wallets from the same exchange account as this creates permanent transaction graph links.
For Ethereum, use intermediate privacy tools like Tornado Cash between source and destination. Send from exchange to Tornado, wait hours/days, withdraw to destination wallet. This breaks the direct on-chain link. Layer 2 bridges also help: mainnet → Arbitrum → Optimism → final wallet adds complexity to clustering.
Mining or earning crypto directly to each wallet provides the strongest separation. Validator rewards, freelance payments, or other direct-to-wallet sources have no funding transaction linking them to your other addresses or identity.
Distribute seed phrases across independent physical locations. Store Wallet 1 phrase in home safe, Wallet 2 phrase in bank safe deposit box, Wallet 3 phrase with trusted family member. Never store all phrases in one location — if someone finds that location, they get everything.
For high-value wallets, implement multi-signature or Shamir's Secret Sharing. Split seed phrase into three shares where any two recover it. Store shares in separate locations (home safe, bank box, trusted person). Compromising one location reveals nothing.
Use metal backups distributed geographically to protect against localized disasters. Home fire destroys the phrase stored there, but bank box copy survives. For truly massive holdings, consider professional custody solutions with institutional-grade key management.
Accept gas fragmentation as a cost of proper security. If you have five wallets, you need five separate gas token balances. With one wallet needing 0.5 ETH for gas, five wallets need 2.5 ETH total — five times the locked capital. This is the price of wallet separation.
For smaller portfolios where gas represents 10%+ of total value, concentrate activity on Layer 2s (Arbitrum, Optimism) where gas costs are 10-100x lower. 0.05 ETH per L2 wallet covers hundreds of transactions vs. 0.5 ETH on mainnet.
Consider gas abstraction protocols that let you pay fees in the token being transferred rather than native gas tokens (pay gas in USDC instead of ETH). This eliminates separate gas balances but charges premium fees. Revoke all approvals monthly on every wallet to prevent cross-contamination where malicious contracts exploit unlimited approvals across multiple wallets.
The safest transfer protocol between tiers follows a small test transfer first, full transfer second approach, regardless of how many times you have used the same addresses before. Before sending any meaningful amount between wallets, send a small test transaction and confirm it arrives at the correct address before initiating the full transfer. This protects against clipboard hijacking malware, which silently replaces a copied wallet address with an attacker-controlled address at the moment of pasting. Always verify the destination address on your hardware wallet's screen rather than relying solely on what is displayed in your browser or software interface, since screen-based verification confirms what the hardware device will actually sign rather than what the software interface is showing. For large transfers out of your Tier 1 cold storage wallet, treat every step as if the software environment on your computer may be compromised, because the hardware wallet's offline verification is specifically designed to protect you in exactly that scenario.
The immediate priority is containment, not investigation. As soon as you suspect a wallet has been compromised, move all assets out of it to a freshly generated wallet address that has never been used before and has no connection to the compromised wallet's transaction history. Do not transfer assets to another existing wallet in your system, because if the attacker has access to your seed phrase rather than just your private key, all wallets derived from the same seed phrase are potentially vulnerable. Generate the new wallet on a device that was not involved in any recent suspicious activity, use a new seed phrase, and record that seed phrase offline immediately before funding the new wallet. Once assets are secured, conduct a full audit of how the compromise occurred: review your recent approvals, check for any browser extensions that were installed near the time of the incident, and assess whether your seed phrase storage was physically or digitally accessible to anyone outside your control. The investigation matters for preventing a recurrence, but it is secondary to securing your remaining assets immediately.
The practical approach is to maintain a small but deliberate gas reserve in each active wallet calibrated to its expected transaction frequency rather than keeping large native token balances across all wallets simultaneously. For your active trading wallet on an EVM chain, a gas reserve of roughly 10 to 20 transactions worth of native token at current gas prices is a reasonable working balance. For your experimental wallets, fund them with gas immediately before each use and keep the residual balance minimal between sessions. For Tier 1 cold storage, gas management is nearly irrelevant because transaction frequency is by design very low. The more significant efficiency gain comes from timing transactions during low-congestion periods, which on most chains means weekends or off-peak hours in major time zones, and from using Layer 2 networks where gas costs are a fraction of mainnet fees for routine interactions. Tracking which of your wallets is running low on gas is one of the practical reasons to use a portfolio aggregator that displays native token balances across all your addresses simultaneously, so you can top up proactively rather than discovering an insufficient gas balance at the moment you need to execute a time-sensitive transaction.
Ready to turn on-chain data into actionable intelligence? Wallet Finder.ai helps you discover and mirror the moves of top-performing crypto wallets in real time. Start your 7-day trial and trade smarter by following the pros.