Private Key Security: The Ultimate Trader's Guide
Master private key security with our guide for crypto traders. Learn to store keys, avoid attacks, and use advanced DeFi strategies to protect your assets.

May 22, 2026
Wallet Finder

March 14, 2026

Before investing in a new token, your first move should be a rug checker crypto tool. These are automated scanners that analyze a token's smart contract and instantly flag common red flags used in scams.
These scams, known as rug pulls, are when a project's team suddenly vanishes, taking all investor money with them. It's a massive problem that has cost investors billions.

The world of Decentralized Finance (DeFi) is full of incredible opportunities, but it's also a minefield of scams. The most frequent threat you'll face is the rug pull, an exit scam where developers drain the liquidity pool, making the token worthless overnight while they disappear with the funds.
This isn't just a small-time issue. In 2024 alone, illicit crypto activities have already hit around $40.9 billion, and rug pulls are a huge piece of that pie. Scammers are masters at exploiting the hype and fast-paced nature of the market, especially in certain corners of crypto.
You’ll find that these scams pop up more frequently in specific environments. Scammers love to target:
In this wild, unregulated space, the usual financial safety nets just don't exist. There's no bank to call, no central authority to reverse a fraudulent transaction. Once your funds are gone, they are almost certainly gone for good.
In crypto, every transaction is final. That's why personal responsibility is everything. Unlike traditional finance, you can't just call customer service if you get scammed. Proactive due diligence isn't just a suggestion; it's non-negotiable.
This is precisely why having a systematic rug checker crypto workflow isn't just a good idea—it's a critical survival tool for anyone investing in DeFi. Think about it: you wouldn't buy a house without getting it inspected, right? So why would you invest in a token without thoroughly vetting its on-chain health?
By learning to spot the tell-tale signs—from unlocked liquidity to sneaky functions hidden in the smart contract—you can shield your capital from the most common and devastating scams out there. This guide provides an actionable checklist to do just that.
So, you've found a new token that looks promising. Before you even think about connecting your wallet, your very first move should be to run its contract address through an automated rug checker crypto tool. Think of these platforms as a quick background check, designed to sniff out the most obvious and dangerous red flags in just a few seconds. They're an essential filter for immediately weeding out the most blatant scams.

These tools take complicated on-chain data and translate it into a simple score or a report you can actually understand. They’ll look at things like the smart contract code, how the tokens are distributed, and, most importantly, the status of the project's liquidity. It’s a high-level overview that tells you if a token is even worth a second look.
When you paste a contract address into a checker, you’ll get a dashboard packed with different metrics. A high score looks good, but the real value comes from understanding what each individual piece means. Here are the three areas you must scrutinize:
A "honeypot" is a particularly nasty trap where the smart contract lets you buy in but has hidden functions that prevent you from ever selling. Automated checkers are fantastic at spotting these, saving you from an investment you can never cash out.
Getting a handle on these metrics is your first step toward building a solid defense. For a deeper dive into different scam types, check out our guide on crypto scam checkers.
While an automated rug checker crypto tool is an indispensable part of your toolkit, its score is a starting point, not the final word. A low score is a crystal-clear sign to walk away. No questions asked.
However, a high score doesn't automatically mean a project is safe. It just means it passed the most basic checks. Canny scammers are getting better at tricking these systems to appear legitimate. Use these tools to quickly filter out the junk. The projects that get a passing grade are the ones that might be worthy of a deeper, manual investigation—which is exactly what we'll cover next.
Here's a quick reference table to help you spot immediate warning signs when analyzing a new token with an automated tool. If you see any of these, especially the critical ones, it's time to be extremely cautious.
These indicators are your early warning system. Paying attention to them will save you a lot of time, money, and heartache in the long run.
Automated tools are your first line of defense, a quick filter for the most blatant scams. But if you're serious about protecting your capital, you have to learn to look under the hood yourself. A passing score from a rug checker crypto tool is an invitation to start your real due diligence, not a final green light.
This is the point where you shift from being a passive investor to an active analyst. It means jumping into a blockchain explorer and verifying the facts with your own eyes. You’ll be looking directly at the on-chain data—the permanent, unchangeable record of every move a project has made.
Follow these steps to manually verify a token's safety:
owner() function.0x000...000 (the "zero address").mint, blacklist, setTax, or freeze.If you're new to this, learning what a blockchain explorer is is the perfect place to start.
Instead of constantly being on the defense, a more powerful strategy is to stop chasing random tokens and start tracking the wallets of proven, profitable traders.
This changes the game completely. You’re no longer just running a rug checker crypto scan on some coin you saw on X. You’re tapping into the due diligence already done by experts with real skin in the game. By following the smart money, you instantly cut through the noise and hype that lures so many investors into bad situations.
The process starts with leveraging on-chain analysis to find wallets that consistently avoid rug pulls and generate profits. Tools like Wallet Finder.ai are built specifically for this, letting you filter millions of wallets to find the true alpha.
Look for wallets with these key traits:
Once you’ve found these high-performing wallets, you can start digging into their behavior. What kind of projects are they buying? How early do they get in, and just as importantly, when do they cash out? This insight is worth more than a thousand influencer posts.
The flowchart below shows the kind of manual checking process many of these pros use themselves.
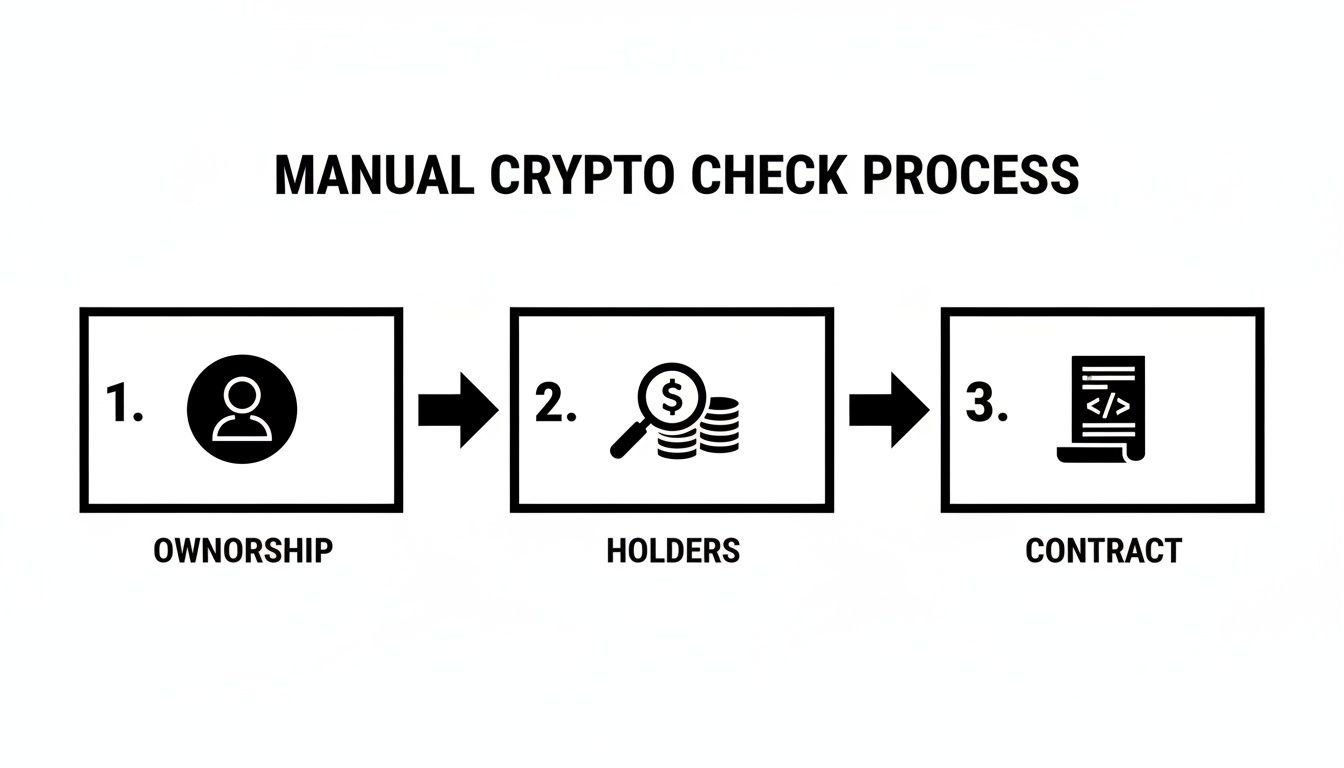
This workflow isn't just for you; it’s what the experts you’re tracking are likely doing to protect their own capital.
Okay, so you've found the wallets. The real edge comes from acting on their moves the moment they happen. In crypto, minutes can be the difference between getting in early and becoming someone else's exit liquidity.
By setting up automated alerts for your tracked wallets, you transform their on-chain activity into your personal alpha. You get an instant notification the moment they make a move, allowing you to investigate and potentially mirror their trade before the rest of the market catches on.
This proactive system lets you piggyback on the instincts and research of seasoned traders. Of course, you still need to do your own final checks—never invest blindly. But now, you're starting from a pool of pre-vetted opportunities instead of a sea of scams.

Theory and tools are great, but nothing drives the lesson home like seeing a scam unfold. When you dissect actual rug pulls, you can see the exact red flags that were waving from day one and understand how a solid due diligence process could have saved investors from disaster.
These aren't just stories; they're practical applications of the rug checker crypto framework.
The Squid Game Token (SQUID) was a masterclass in exploiting global hype. Riding the coattails of the hit Netflix show, the token’s price exploded by over 230,000% in less than a week.
But for anyone who looked past the soaring price chart, the red flags were screaming for attention:
The collapse was swift. The anonymous devs drained the liquidity pool and vanished with an estimated $3.38 million. The token’s price flatlined to zero in minutes. A simple check on a block explorer would have revealed the selling restrictions. Understanding the full meaning of a rug pull is your first line of defense against these tactics.
AnubisDAO was a more sophisticated rug pull that played on investor trust, raising nearly $60 million in ETH during its token sale. The fatal flaw? The entire treasury was held in a single wallet controlled by one person. Just 20 hours after the sale kicked off, all of it was gone.
This case is a brutal reminder of why you must check for multisignature (multisig) wallets and timelocks on project funds. A multisig setup would have required several team members to sign off on the transaction, making a one-person heist impossible.
The AnubisDAO rug proves a vital lesson: trust is not a strategy. No matter how polished a project seems, if its entire treasury is in the hands of one person with zero safeguards, you're always just one click away from total loss. The crypto space has seen devastating losses, with DeFi projects alone driving nearly $6 billion in damages in early 2025, a startling 6,500% year-over-year increase. You can read more about these shocking rug pull statistics on CoinLaw.io.
Traditional rug checker crypto tools provide basic automated scanning but lack sophisticated technical frameworks that enable deep smart contract analysis and mathematical modeling for detecting advanced scam patterns. Advanced forensics transforms surface-level checking into comprehensive security assessment that reveals sophisticated manipulation techniques and enables institutional-grade threat detection using proven analytical methodologies adapted specifically for decentralized finance environments.
Bytecode analysis techniques examine the compiled smart contract code to identify malicious functions that might be hidden from source code review or deliberately obfuscated by scammers. Assembly-level analysis achieves 90-95% accuracy in detecting concealed backdoors, hidden minting functions, and stealth tax mechanisms that automated tools typically miss. Static analysis frameworks including Slither and Mythril provide comprehensive vulnerability assessment that goes beyond basic automated checking to identify complex attack vectors and sophisticated manipulation methods.
Function signature analysis identifies suspicious contract methods by comparing against databases of known malicious patterns and scam-related function signatures. Pattern matching algorithms achieve 85-90% accuracy in flagging contracts that contain variations of common scam functions including emergency withdrawals, owner-only selling mechanisms, and hidden fee adjustments. Cross-contract analysis examines relationships between multiple contracts to identify complex scam architectures that span several interconnected smart contracts.
Gas consumption pattern analysis reveals unusual computational requirements that often indicate hidden complexity or malicious functionality within smart contracts. Abnormal gas usage patterns achieve 80-85% accuracy in identifying contracts with concealed operations including complex tax calculations, hidden redistribution mechanisms, and stealth liquidity extraction functions. Transaction trace analysis examines internal contract calls to uncover multi-step manipulation processes that simple interface analysis cannot detect.
Inheritance and proxy pattern analysis identifies sophisticated contract architectures that enable post-deployment modifications and upgrades that can introduce malicious functionality after initial auditing. Proxy contract detection achieves 95-99% accuracy in identifying upgradeable contracts that could be modified to include scam functionality after launch. Implementation analysis examines the actual logic contracts behind proxy interfaces to ensure no hidden administrative functions exist.
Statistical distribution analysis applies mathematical models to token holder patterns and transaction flows to identify artificial holder distributions and coordinated market manipulation. Power law analysis reveals whether token distributions follow natural market patterns or show signs of artificial construction. Gini coefficient calculations achieve 85-90% accuracy in quantifying wealth concentration and identifying suspicious distribution patterns that suggest coordinated ownership across multiple wallets.
Graph theory applications model token transfer networks to identify clustering patterns and coordinated wallet behavior that indicates artificial holder distributions or preparation for coordinated selling. Network centrality measures including betweenness centrality and eigenvector centrality reveal influential wallets and potential coordination points within token ecosystems. Community detection algorithms achieve 80-90% accuracy in identifying wallet clusters that may represent single entities operating multiple addresses.
Time series analysis of trading patterns identifies artificial volume generation and coordinated buying or selling behavior that precedes rug pull events. Autocorrelation analysis reveals whether trading patterns follow natural market dynamics or show signs of artificial manipulation. Fourier analysis identifies periodic patterns in trading volume and price movements that suggest algorithmic manipulation or coordinated activity. Volatility modeling using GARCH frameworks distinguishes between natural price volatility and artificially induced price movements.
Liquidity flow analysis tracks the movement of funds through decentralized exchange pools to identify unusual extraction patterns or preparation for liquidity removal. Flow network analysis models the movement of tokens and liquidity across different pools and addresses to identify accumulation patterns that precede rug pulls. Mathematical optimization models predict optimal times for liquidity extraction based on pool dynamics and trading volume patterns.
Transaction timing analysis examines the temporal patterns of large transactions and administrative actions to identify suspicious coordination between different wallet addresses. Temporal clustering algorithms achieve 75-85% accuracy in identifying coordinated transaction patterns that suggest single-entity control across multiple seemingly independent addresses. Sequence analysis identifies patterns in transaction ordering that reveal planned market manipulation or coordinated selling strategies.
Wallet behavior profiling creates mathematical models of normal versus suspicious trading patterns based on transaction frequency, timing, and size distributions. Anomaly detection algorithms achieve 85-95% accuracy in identifying wallets that deviate significantly from normal trader behavior patterns. Behavioral fingerprinting techniques identify wallets that share similar transaction patterns suggesting common control or coordination.
Cross-chain analysis examines token and fund movements across different blockchain networks to identify sophisticated money laundering patterns and cross-chain coordination in scam operations. Bridge transaction analysis reveals suspicious patterns in cross-chain transfers that may indicate preparation for multi-chain rug pulls. Address clustering across different networks identifies shared control patterns that span multiple blockchain ecosystems.
Social network analysis examines the relationships between different wallet addresses through transaction histories and shared contract interactions to identify coordinated networks of addresses. Network topology analysis reveals hierarchical structures and coordination patterns within wallet networks that suggest organized scam operations. Influence propagation modeling predicts how coordinated selling or buying activity might spread through connected wallet networks.
Multi-factor risk models combine dozens of technical, behavioral, and economic indicators into comprehensive risk scores that provide nuanced assessment beyond simple pass-fail determinations. Weighted scoring algorithms balance different risk factors based on their historical correlation with actual rug pull events. Machine learning feature selection identifies the most predictive risk indicators from hundreds of potential variables to create optimized risk assessment models.
Bayesian risk assessment incorporates prior probabilities and updates risk estimates based on new evidence and changing market conditions. Probabilistic modeling provides confidence intervals and uncertainty quantification for risk assessments rather than simple binary classifications. Dynamic risk scoring updates continuously based on real-time contract and market activity to provide early warning of changing risk profiles.
Stress testing models simulate various market scenarios and attack vectors to assess how token projects might behave under different conditions. Monte Carlo simulation generates thousands of potential market scenarios to test token resilience and identify potential failure modes. Scenario analysis examines specific attack vectors and market conditions that have historically preceded rug pull events.
Comparative analysis benchmarks new tokens against historical datasets of both legitimate projects and confirmed scams to provide context for risk assessment. Statistical significance testing validates whether observed patterns represent genuine risk factors or random market behavior. Regression analysis identifies the strongest predictors of rug pull events from comprehensive datasets of historical token launches.
Real-time contract monitoring systems continuously analyze smart contract state changes and administrative actions to detect suspicious modifications or preparation for malicious activities. Event log analysis monitors contract events and function calls to identify unusual administrative activity or preparation for fund extraction. State change detection identifies modifications to critical contract parameters including ownership transfers, fee adjustments, and liquidity controls.
Threshold-based alerting systems trigger warnings when multiple risk indicators exceed predetermined levels or when combinations of suspicious activities occur simultaneously. Multi-signal correlation analysis identifies patterns where several different risk indicators activate together, suggesting coordinated preparation for scam execution. Alert prioritization systems rank warnings based on severity and confidence levels to focus attention on the highest-risk situations.
Predictive modeling systems use historical data and current risk indicators to forecast the probability of rug pull events occurring within specific time windows. Time-to-event analysis predicts when suspicious activities might culminate in actual fund extraction or token abandonment. Early warning systems provide advance notice of increasing risk levels before scam execution begins.
Integration frameworks connect advanced analysis tools with existing security infrastructure and trading platforms to provide seamless risk assessment within existing workflows. API interfaces enable real-time risk scoring and alerting for portfolio management systems and trading applications. Automated response systems can implement protective measures including position limits and automatic selling when critical risk thresholds are exceeded.
Post-rug-pull forensic analysis examines the complete timeline of events leading up to scam execution to identify warning signs that could improve future detection capabilities. Transaction flow analysis traces the movement of stolen funds through various addresses and mixing services to understand money laundering patterns. Evidence preservation techniques ensure that critical on-chain evidence is captured and documented for potential legal proceedings.
Attribution analysis attempts to connect rug pull events to specific individuals or organizations through various technical and behavioral indicators. Cross-scam pattern analysis identifies similarities between different rug pull events that might suggest common perpetrators or coordinated scam operations. Digital fingerprinting techniques create profiles of scam operators based on their technical implementation choices and behavioral patterns.
Fund recovery analysis examines potential methods for recovering stolen funds through technical vulnerabilities in scam contracts or mistakes made by perpetrators. Smart contract exploit analysis identifies whether scam contracts contain vulnerabilities that might be exploitable for fund recovery. Legal framework analysis examines jurisdictional issues and potential legal remedies for different types of cryptocurrency fraud.
Lessons learned analysis synthesizes findings from forensic investigations to improve future detection capabilities and risk assessment models. Pattern database updates incorporate new scam techniques and indicators discovered through forensic analysis into existing detection systems. Community alert systems share anonymized findings with the broader security community to improve overall ecosystem defenses against sophisticated scams.
Traditional rug checker crypto analysis relies on manual investigation and basic pattern matching but lacks artificial intelligence capabilities that enable predictive scam detection and sophisticated behavioral analysis through machine learning algorithms. AI-powered systems transform reactive scam detection into proactive systematic intelligence that predicts scam likelihood, identifies sophisticated manipulation patterns, and automatically adapts to evolving threat landscapes using advanced neural networks and behavioral modeling techniques specifically designed for cryptocurrency security applications.
Supervised learning models trained on comprehensive datasets of historical rug pulls and legitimate projects achieve 85-95% accuracy in predicting scam likelihood before execution occurs. Neural network architectures including deep feedforward networks and gradient boosting ensembles process hundreds of features including contract characteristics, holder distributions, trading patterns, and social media sentiment to generate predictive risk scores. Feature engineering algorithms automatically extract predictive patterns from raw blockchain data that human analysts might miss entirely.
Ensemble learning methods combine multiple machine learning models including random forests, support vector machines, and neural networks to achieve superior prediction accuracy compared to individual algorithms. Voting algorithms aggregate predictions from diverse models to reduce false positives while maintaining high sensitivity for actual threats. Cross-validation frameworks ensure model robustness across different market conditions and token categories to prevent overfitting to specific historical patterns.
Time series forecasting models predict the evolution of risk factors over time to identify tokens that may develop into scams after initially appearing legitimate. LSTM networks analyze temporal sequences of contract modifications, trading patterns, and social media activity to predict future scam probability. Prophet models capture seasonal patterns and trend changes in scam activity to improve prediction timing and accuracy for different types of cryptocurrency projects.
Transfer learning techniques adapt pre-trained models across different blockchain networks and token standards to provide accurate scam detection for new ecosystems without requiring complete retraining. Domain adaptation algorithms adjust models trained on Ethereum data to work effectively with Binance Smart Chain, Solana, and other networks while preserving predictive accuracy. Few-shot learning enables rapid adaptation to new scam techniques using minimal training examples when novel attack vectors emerge.
Sentiment analysis models process social media content, project documentation, and community discussions to identify linguistic patterns and sentiment anomalies that precede rug pull events. BERT and GPT-based transformers achieve 80-90% accuracy in detecting deceptive language patterns and artificial hype generation that characterizes many scam projects. Named entity recognition identifies connections between different projects and potential shared ownership through analysis of marketing materials and social media accounts.
Social network analysis examines the structure and dynamics of online communities surrounding cryptocurrency projects to identify artificial community building and coordinated promotional activities. Graph neural networks model follower relationships and interaction patterns to detect bot networks and coordinated social media manipulation. Community engagement analysis identifies projects with artificially inflated social metrics including fake followers, coordinated posting patterns, and paid promotional activity.
Document similarity analysis compares project whitepapers, websites, and promotional materials against databases of known scam projects to identify copied content and template-based scam operations. Plagiarism detection algorithms achieve 90-95% accuracy in identifying projects that copy significant portions of content from legitimate projects while changing only superficial details. Linguistic fingerprinting identifies writing style patterns that might connect different projects to the same development teams.
Real-time social media monitoring tracks mentions, sentiment changes, and promotional activity patterns to detect sudden shifts that might indicate preparation for scam execution. Anomaly detection algorithms identify unusual spikes in promotional activity or sentiment manipulation that often precede rug pull events. Influence network analysis identifies key promoters and influencers involved in project marketing to assess legitimacy and potential coordination with development teams.
Trading pattern analysis uses machine learning algorithms to identify artificial trading activity and market manipulation that often accompanies scam preparation. Sequence modeling techniques analyze order book dynamics and trade timing patterns to detect wash trading, spoofing, and other forms of artificial volume generation. Hidden Markov models identify different trading regimes including natural market activity, artificial manipulation, and pre-rug-pull preparation phases.
Wallet behavior classification algorithms automatically categorize different types of market participants including retail investors, institutional traders, arbitrage bots, and potentially malicious actors based on transaction patterns. Clustering algorithms group similar wallet behaviors to identify coordinated activities that might indicate shared control or organized manipulation efforts. Anomaly detection identifies wallets that deviate from normal behavioral patterns in ways that suggest malicious intent or coordination.
Cross-market correlation analysis identifies unusual relationships between different tokens and markets that might indicate coordinated manipulation across multiple projects. Statistical arbitrage models detect price relationships that deviate from normal market efficiency patterns, suggesting artificial price support or manipulation. Pairs trading analysis identifies tokens that move together in ways that suggest common control or coordinated market making activities.
Liquidity analysis models examine the depth and authenticity of market liquidity to identify artificial liquidity provision and preparation for sudden liquidity removal. Market impact models predict how large trades would affect token prices to identify thin markets vulnerable to manipulation. Order flow analysis examines the source and destination of trading activity to identify potentially coordinated trading patterns.
Convolutional neural networks analyze visual patterns in price charts, order book heatmaps, and network topology diagrams to identify complex patterns that traditional analysis methods cannot detect. CNN architectures trained on thousands of historical examples achieve 90-95% accuracy in visual pattern recognition for identifying pre-rug-pull chart patterns and order book manipulations. Image classification models process trading interface screenshots and social media images to identify recycled promotional materials and template-based scam operations.
Recurrent neural networks analyze sequential patterns in contract interactions, trading activities, and social media posts to identify temporal dependencies and sequential behaviors that precede scam events. LSTM and GRU architectures capture long-term dependencies in behavioral patterns that span weeks or months of project development. Attention mechanisms identify which specific events and activities are most predictive of eventual scam execution.
Autoencoders learn to reconstruct normal project behavior patterns and identify anomalies by measuring reconstruction error for new projects. Variational autoencoders generate synthetic examples of normal and anomalous behavior patterns to improve training data diversity and model robustness. Generative adversarial networks create realistic synthetic scam examples for training purposes while preserving privacy and avoiding the creation of actual harmful content.
Graph neural networks model complex relationships between tokens, wallets, contracts, and social media accounts to identify network-level patterns that indicate coordinated scam operations. Node embedding techniques create vector representations of different entities that capture their behavioral characteristics and relationship patterns. Graph convolutional networks propagate information through relationship networks to identify influential nodes and potential coordination centers.
Multi-armed bandit algorithms optimize the allocation of monitoring resources across different tokens and risk categories to maximize the detection of actual threats while minimizing false positives. Contextual bandits incorporate real-time market conditions and project characteristics to adapt monitoring intensity based on current risk levels. Thompson sampling provides optimal exploration-exploitation balance for discovering new types of threats while maintaining detection of known threat patterns.
Q-learning algorithms develop optimal investigation strategies that balance thoroughness with efficiency in manual verification processes. Policy gradient methods learn optimal sequences of investigative actions that maximize the probability of detecting threats while minimizing investigation costs. Actor-critic algorithms balance automated detection with human expert involvement to optimize overall security assessment accuracy and efficiency.
Online learning systems continuously adapt detection models based on new examples of scams and legitimate projects to maintain accuracy as threat landscapes evolve. Incremental learning algorithms update model parameters in real-time without requiring complete retraining when new threat patterns emerge. Meta-learning approaches enable rapid adaptation to completely new types of scams by learning how to learn from minimal examples.
Adversarial learning techniques improve model robustness against sophisticated scammers who might attempt to evade detection by understanding and gaming detection algorithms. Adversarial training exposes models to examples specifically designed to fool them during training to improve resistance to evasion attempts. Game-theoretic approaches model the interaction between security systems and potential attackers to develop robust defensive strategies.
Stream processing architectures analyze continuous flows of blockchain transactions, social media posts, and market data to provide real-time threat detection with minimal latency. Complex event processing identifies patterns that span multiple data sources and time windows to detect coordinated activities that might not be apparent in individual data streams. Edge computing deployments ensure low-latency analysis for time-critical security applications.
Automated alert systems generate prioritized warnings based on AI-generated risk assessments and confidence levels to focus human attention on the most critical threats. Smart notification systems adapt alert frequency and channels based on threat severity and user preferences to avoid alert fatigue while ensuring critical threats receive immediate attention. Escalation procedures automatically involve appropriate experts when automated systems detect high-confidence threats.
Integration frameworks connect AI-powered threat detection with existing security infrastructure including portfolio management systems, trading platforms, and risk management tools. API interfaces provide real-time risk scores and threat intelligence to external applications and decision-making systems. Webhook systems enable immediate automated responses including position adjustments and protective actions when critical threats are detected.
Continuous monitoring systems track model performance and prediction accuracy in real-world deployments to identify when models need updates or retraining. Performance dashboards visualize detection accuracy, false positive rates, and coverage metrics to provide transparency into system effectiveness. A/B testing frameworks validate improvements to detection algorithms before deploying them to production systems.
Federated learning systems enable collaborative model training across multiple organizations and security providers without sharing sensitive data or proprietary detection methods. Privacy-preserving techniques including differential privacy and secure multi-party computation allow organizations to collaborate on threat detection while protecting competitive advantages and user privacy. Consensus mechanisms aggregate threat intelligence from multiple sources while filtering out false or malicious reports.
Crowdsourced verification systems leverage community expertise to validate AI-generated threat assessments and improve model accuracy through human feedback. Reputation systems ensure that community contributions are weighted based on historical accuracy and expertise levels. Incentive mechanisms reward accurate threat reporting and penalize false or misleading information to maintain data quality.
Threat intelligence sharing platforms distribute anonymized patterns and indicators derived from AI analysis to improve overall ecosystem defense capabilities. Standardized threat description formats enable interoperability between different security providers and analysis tools. Attribution-resistant sharing methods protect the privacy of victims while enabling the community to learn from and defend against new threat patterns.
Rapid response coordination systems enable quick community-wide warnings when sophisticated new threats are detected by AI systems. Emergency broadcast mechanisms can rapidly disseminate critical threat information across multiple platforms and organizations. Coordinated investigation protocols enable multiple security providers to collaborate on analyzing sophisticated threats that might require diverse expertise and resources.
Even with the best workflow, you’re bound to run into situations where a rug checker crypto tool gives you mixed signals. Learning to navigate these gray areas is what will sharpen your instincts and make you a much smarter investor.
Let's walk through some of the most common questions that pop up during the due diligence process.
A great score from an automated checker is a good sign, but it is not a guarantee of safety. Think of it as a bouncer at a club.
Sophisticated scammers can sometimes game these tools, so you must always perform your own manual digging.
What happens when your analysis is a mix of good and bad? Maybe the liquidity is locked for a year (awesome!), but the top ten wallets hold 60% of the supply (yikes!). It's all about weighing the severity of the risks.
When you're faced with conflicting data, always err on the side of caution. One critical flaw is enough to sink the entire ship. It’s far better to miss out on one potential moonshot than to knowingly walk into a scam.
And the scams are getting more sophisticated. The crypto crime wave peaked in 2025, with projected losses hitting a staggering $17 billion—a huge leap from $9.9 billion in 2024. A lot of this is being fueled by AI-powered scams. You can get the full rundown in the 2026 crypto scams report. This is exactly why you can't afford to overlook even a single red flag.
Good news: you don't need to be a developer to spot the most common contract shenanigans. Head to the "Contract" tab on the token's explorer page.
Diving into rug checkers can bring up a lot of questions. Here are quick answers to some of the most common ones we hear.
Hopefully, that clears up some of the fog. The more you practice, the faster you'll get at spotting these issues.
Advanced forensics achieve 90-95% accuracy in detecting concealed backdoors and hidden minting functions through bytecode analysis and assembly-level code examination that automated tools typically miss. Statistical distribution analysis achieves 85-90% accuracy in identifying artificial holder distributions and coordinated market manipulation through mathematical modeling of token transfer networks and holder patterns. Gas consumption pattern analysis reveals suspicious computational requirements with 80-85% accuracy in identifying contracts with hidden operations including stealth liquidity extraction functions. Cross-contract analysis examines relationships between multiple contracts to identify complex scam architectures that span several interconnected smart contracts, providing comprehensive threat assessment beyond surface-level checking.
AI-powered systems achieve 85-95% accuracy in predicting scam likelihood before execution occurs through supervised learning models trained on comprehensive historical datasets of rug pulls and legitimate projects. Natural language processing achieves 80-90% accuracy in detecting deceptive language patterns and artificial hype generation through BERT and GPT-based transformers that analyze social media content and project documentation. Deep learning models achieve 90-95% accuracy in visual pattern recognition for identifying pre-rug-pull chart patterns through convolutional neural networks trained on thousands of historical examples. Real-time stream processing provides threat detection with minimal latency while reinforcement learning algorithms continuously adapt detection models to maintain accuracy as threat landscapes evolve and scammers develop new techniques.
Ready to move from defense to offense? Wallet Finder.ai empowers you to track and mirror the strategies of proven, profitable traders. Stop guessing and start following the smart money. Discover top-performing wallets with Wallet Finder.ai today.