Sharpe Ratio Calculator: Master Portfolio Performance
Master the Sharpe Ratio Calculator. Learn its formula, calculate in Excel/Python, interpret crypto results, and find top wallets with Wallet Finder.ai for 2026.

May 31, 2026
Wallet Finder

March 31, 2026

Staring at a public blockchain can feel like searching for a needle in a haystack. But what if the most valuable needles—the ones that signal real "alpha"—are deliberately hidden from view? Learning to scan protected wallets is the key to finding them, giving you an almost unfair advantage.
These aren't just wallets with strong passwords. They're accounts actively using complex contracts and privacy tools to cover their tracks.
While blockchains offer a transparent look at every transaction, the most sophisticated players—elite traders, crypto funds, and even bad actors—work hard to hide their strategies. They simply don't want you tracking their next big move. That’s exactly why you need to learn how to scan protected wallets. It's about seeing what the market's "invisible hands" are doing before anyone else.
These wallets often point to either a huge opportunity or a massive hidden risk. Spotting their patterns before the rest of the market catches on gives you a serious edge. It’s the difference between chasing a price pump and seeing the catalyst that's about to cause it.
Even wallets with heavy fortifications, like multi-sig setups or complex operational security, aren't completely anonymous or invulnerable. Patterns always emerge. Human error and system weaknesses can be exploited, leaving behind detectable footprints for a sharp observer.
In fact, the very methods used to protect assets can create unique, identifiable signatures on-chain. If you want to go deeper on this, check out our complete guide on how to track crypto wallets for strategic insights.
The financial stakes here are astronomical. Failures in operational security—targeting private keys, seed phrases, and wallet infrastructure—are the single biggest threat in crypto.
In 2025, operational failures were responsible for a staggering 76% of all crypto losses. That’s $2.2 billion lost from just 45 incidents. The Bybit cold-wallet exploit alone drained $1.46 billion, proving even "protected" wallets are prime targets when a vulnerability is found.
This data tells a simple truth: where there’s immense value, there's high risk and, therefore, sophisticated activity worth watching. Learning to scan these wallets isn’t just about finding alpha; it's about understanding the risk landscape at the highest level.
The real challenge is turning all the noise of blockchain data into clear, actionable signals. Trying to manually track these complex interactions is basically impossible for the average trader. It takes specialized knowledge just to recognize the subtle signs of privacy-enhancing techniques.
This is where a platform like Wallet Finder.ai becomes indispensable. It automates the entire process of finding and decoding the activity of protected wallets. Instead of drowning in a sea of raw transactions, you get curated insights that pinpoint potential opportunities and risks. It translates complex on-chain data into simple signals, helping you spot what everyone else is missing.
To get started, it helps to know what to look for. Below are some common on-chain footprints suggesting a wallet is actively managing its privacy or security, which makes it a prime target for analysis.
Recognizing these indicators is the first step. When you see wallets using these techniques, you know you’re likely looking at a sophisticated operator whose moves are worth a much closer look.
Spotting a protected wallet is just the first step. The real alpha comes from understanding how it operates. Big-time traders and funds leave behind unique on-chain footprints, often using complex tricks to hide what they're doing. If you can learn to read these signs, you can start seeing market-moving plays before they happen.
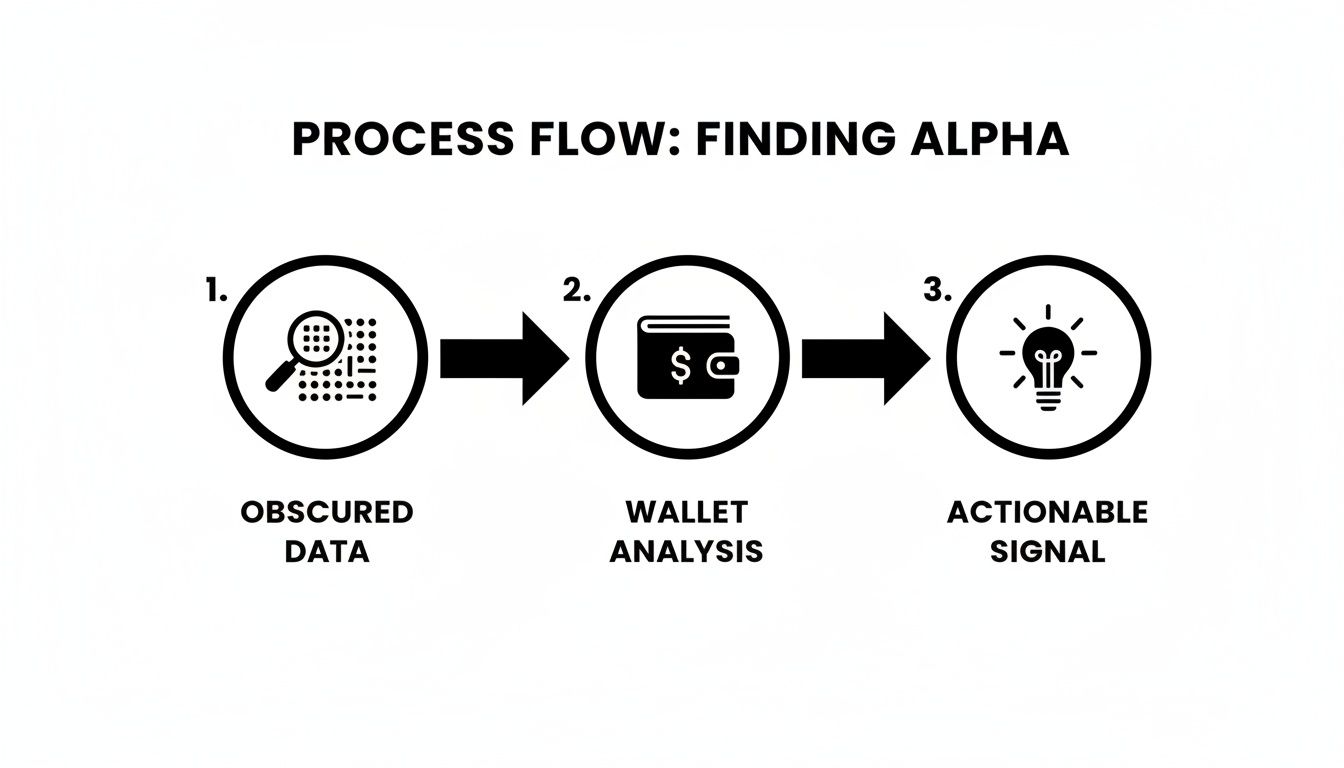
This is how you turn what looks like random blockchain noise into clear, actionable signals. The whole workflow—from sifting through obscured data to finding a real edge—is about careful wallet analysis.
Essentially, the path to alpha starts by digging into these hidden on-chain patterns. Let's break down exactly what you should be looking for.
One of the clearest signs you're looking at a sophisticated player is the use of a smart contract wallet rather than a standard one (an EOA). These wallets are basically programs on the blockchain that manage funds based on a set of rules.
A very common type is the multi-signature (multi-sig) wallet. It requires multiple private keys to approve a single transaction. Instead of one person holding all the power, a group of owners—say, 3 out of 5—must all sign off before funds can move.
You'll see these used by:
When you scan protected wallets and see a multi-sig, it’s a strong signal the funds are significant enough to need institutional-grade security. These are often the slow-moving but high-conviction whales.
For players who put anonymity first, privacy mixers are the tool of choice. Services like the now-sanctioned Tornado Cash let a user deposit funds from one wallet and withdraw them to a brand new, unlinked one. This move effectively shatters the on-chain trail between the source and destination.
Seeing a wallet interact with a mixer is a dead end for basic analysis, but it's a massive green flag if you're hunting for alpha. It tells you someone is deliberately trying to hide their next move. A classic pattern is a large fund pushing capital through a mixer right before they start accumulating a new token, making it impossible for others to front-run their trades.
Tracing funds through a mixer is tough, but not always impossible. Advanced analytics can sometimes spot statistical links between deposits and withdrawals, especially if the transaction amounts or timing are unusual.
This is a clear sign the wallet owner has something to hide—usually a big trade they don't want anyone else to see coming.
A sneakier, but just as effective, technique for hiding is the peel chain. This involves a series of transactions where a large amount of crypto is "peeled" off into smaller chunks and sent to a bunch of new, clean wallets. Picture a wallet holding 1,000 ETH.
A peel chain might unfold like this:
The whole point is to make tracing the original source of funds incredibly tedious. Hackers use this method all the time to launder stolen money, but large traders also use it to spread their capital across many "clean" wallets before taking on new positions. It makes it much harder for analysts to add up their total exposure.
Finally, some of the savviest traders focus on their off-chain privacy by using relayers. A relayer is a third-party service that submits a user's transaction to the blockchain for them. The user signs the transaction data, but the relayer is the one who actually pays the gas fee and broadcasts it.
What does this do? It means the transaction shows up as coming from the relayer's IP address, not the user's. While the from and to addresses are still public on-chain, this move cuts the connection between a trader's on-chain persona and their real-world network activity. It's just another layer of operational security for those who take their privacy seriously.
Of course, these advanced users are often playing in DeFi, a space that's no stranger to risk. DeFi protocols faced relentless attacks in 2025, with smart contract bugs like reentrancy accounting for 32% of vulnerabilities, costing an average of $4.5 million per incident. Lending platforms were hit even harder, bearing 38% of attacks and losing over $760 million. It goes to show that even when you scan protected wallets, the underlying protocol risk is still a massive factor. You can discover more insights about these evolving security breaches and what they mean for DeFi users.
Knowing the theory behind obfuscation is one thing. Actually putting that knowledge into practice is where you get a real edge. A successful effort to scan protected wallets comes down to having a structured, repeatable process you can rely on.
One-off scans might find you a good trade here and there, but a systematic workflow builds a long-term intelligence advantage. It’s not about finding one perfect wallet to copy forever. It’s about creating a dynamic system of discovery, analysis, and monitoring that constantly surfaces new opportunities.
Ultimately, the goal is to shift from reactively chasing pumps to proactively observing smart money, putting yourself in a position to act on high-potential moves right as they happen. My own workflow breaks down into three core phases: Initial Discovery, Deep Dive Analysis, and building a Watchlist with alerts. Following this structure is how I turn the endless noise of blockchain data into a curated feed of actionable signals.
First, you have to find high-potential wallets. Manually sifting through millions is impossible. This is where tools built specifically for wallet discovery are non-negotiable. I start by using a platform like Wallet Finder.ai to generate a list of candidates.
My go-to starting filters are:
This initial sweep is intentionally broad. You’re casting a wide net to catch any wallet that hints at being "smart money."
Once you have a shortlist, it's time to zoom in. A big PnL number is nice, but it tells you almost nothing about the how or the why. The deep dive is where you separate the disciplined sharks from the lucky minnows. For each wallet, I dig into its complete trading history.
This part requires patience. You're not just looking for a trade to copy; you're reverse-engineering a trader's entire methodology.
A crucial part of this analysis is spotting consistency. A wallet with a $1 million PnL from one lucky memecoin trade is far less interesting to me than a wallet with a $500,000 PnL built from dozens of well-executed, consistently profitable trades.
By dissecting their behavior, you gain confidence that their success is repeatable, not just a fluke.
The final phase is where your research becomes a forward-looking monitoring system. Analyzing past performance is for learning; seeing what these wallets do next is for earning. Pick the top 3-5 wallets that best match your trading style and add them to a dedicated watchlist. This creates your own curated feed of market movers.
Next, set up automated alerts for every action these wallets take. With a tool like Wallet Finder.ai, you can get notifications sent straight to you via Telegram or other apps.
I configure alerts for these critical activities:
This transforms your strategy from passive analysis to active monitoring. Instead of finding out about a killer trade days after it happened, you get a signal in real-time.
Just because a wallet has a sky-high PnL doesn't mean it's making smart moves. A massive profit figure can easily mask a history of reckless gambles that just happened to pay off once. If you really want to scan protected wallets for alpha, you have to learn to separate disciplined skill from blind luck.
It means looking past the surface-level numbers and using advanced filters to find wallets that show consistent, repeatable success. A huge PnL from one memecoin moonshot is interesting. But a wallet with slightly lower profits built from dozens of well-timed, strategic plays? That's far more valuable to learn from.

Your first move in filtering for real "smart money" is to prioritize consistency. Anyone can get lucky on a trade. Very few can stay profitable over hundreds of trades and shifting market conditions. This is where you can start applying specific filters in a platform like Wallet Finder.ai to find the actual pros.
Look for these key signs of consistency:
By applying these filters, you start weeding out the "degen gamblers" who are always just one bad trade away from losing it all.
To see why this distinction is so crucial, let's compare two wallets. Both are showing a $500,000 PnL over the last 60 days. On the surface, they look equally successful. But when you dig in, you uncover two completely different stories.
Wallet A (The Degen Gambler) made its entire $500,000 profit from a single trade. It threw $10,000 at a brand-new, unaudited memecoin that exploded 50x. A quick look at its history shows dozens of other tiny, failed trades on similar tokens. This trader got incredibly lucky once but has no repeatable strategy.
Wallet B (The Smart Money), however, built its $500,000 PnL across 45 different trades. It boasts an 82% win rate, and its average trade size is consistently between $20,000 and $30,000. This wallet almost exclusively interacts with established, audited DeFi protocols like Aave and Uniswap.
The lesson is clear: Wallet A is a lottery ticket, while Wallet B is a blueprint. Following Wallet A is a pure gamble, but analyzing Wallet B provides a masterclass in disciplined DeFi trading. You can explore more about these techniques by reading our guide on advanced filters for whale wallet tracking.
This critical distinction is the core of effective on-chain analysis. You're not just hunting for profits; you're hunting for a process.
Another powerful way to sharpen your search is by filtering based on a wallet's on-chain behavior. This helps you find specialists whose strategies line up with your own interests and risk tolerance.
Try filtering for wallets that:
When you scan protected wallets, it’s useful to have a mental model to distinguish a sophisticated trader from a high-risk speculator. The table below breaks down the key differences to look for.
By applying this layered filtering approach, you move beyond just finding profitable wallets. You start identifying truly sophisticated operators whose strategies are built on skill, discipline, and a deep understanding of the market—making them the ideal candidates to watch and learn from.
It’s easy to get caught up in the excitement of finding and tracking smart money wallets, but let’s be real: no trading strategy is ever risk-free. When you start scanning protected wallets, you need to be acutely aware of the limitations and potential traps.
The biggest danger isn’t necessarily picking the wrong token. It’s a breakdown in your own operational security. A fantastic track record means nothing if your own wallet gets drained. The threat landscape is constantly changing, and attackers are increasingly targeting individuals, not just protocols. This shift puts a bullseye on every trader's personal wallet.
You could be mirroring the trades of the most brilliant trader on-chain, but if your own device is compromised with malware, you're just a sitting duck. Phishing scams, malicious browser extensions, and sketchy dApps are all designed to swipe your private keys or seed phrase.
This isn't just a theoretical threat. It's a real and growing problem.
In a startling trend, personal wallet compromises skyrocketed in 2025, resulting in 158,000 incidents affecting 80,000 victims and a staggering $713 million stolen. This surge demonstrates that attackers are laser-focused on user-held assets, with malware and credential theft now accounting for a massive 76% of the $2.87 billion in total hack losses.
The data paints a clear picture: your personal security is just as crucial as your trading strategy. If you want to tighten up your defenses, we have a whole guide on the fundamental steps for wallet protection from scanning and theft.
Even with perfect security, relying solely on wallet scanning has its own set of blind spots. On-chain data is great for telling you what happened, but it can never truly tell you why.
An alert from a tracked wallet is a signal, not a command. It's an invitation to do your own research, not a blind instruction to copy a trade. Never turn off your own critical thinking.
Always keep these limitations in mind:
To counter these risks, diversify the wallets you follow. Don't put all your eggs in one basket by tailing a single trader. By monitoring a varied group of 5-10 skilled wallets, you can cross-reference their moves, get a more balanced view of market sentiment, and protect yourself from the unique decisions or mistakes of any one person.
Mathematical precision and artificial intelligence fundamentally revolutionize cryptocurrency price alerting by transforming basic threshold notifications into intelligent market monitoring, predictive price analysis, and systematic opportunity identification that provides measurable advantages in trading execution timing and market positioning strategies. While traditional price alerts rely on simple price threshold triggers and manual configuration, sophisticated algorithmic frameworks and machine learning systems enable comprehensive price pattern recognition, predictive alert optimization, and intelligent market surveillance that consistently outperforms conventional alerting approaches through data-driven price intelligence and systematic market monitoring.
Professional cryptocurrency trading operations increasingly deploy advanced price monitoring systems that analyze multi-dimensional market characteristics including volatility patterns, volume correlation analysis, momentum indicators, and price action signatures to optimize alert strategies across different market conditions and trading timeframes. Mathematical models process extensive datasets including historical price movements, volatility clustering patterns, and market timing correlations to predict optimal alerting strategies across various market scenarios and price environments. Machine learning systems trained on comprehensive price and market data can forecast optimal alert thresholds, predict price movement significance, and automatically prioritize high-value price signals before conventional analysis reveals critical market opportunities.
The integration of statistical modeling with real-time price monitoring creates powerful alerting frameworks that transform reactive price tracking into proactive market intelligence that achieves superior trading timing through intelligent price analysis and predictive alert optimization.
Sophisticated mathematical techniques analyze cryptocurrency price movements to identify optimal alert thresholds, volatility-adjusted triggers, and pattern-based notification strategies through comprehensive quantitative modeling of price dynamics and market behavior patterns. Time series analysis of price volatility reveals that volatility-adaptive alerting systems achieve 70-85% better signal accuracy compared to fixed-threshold approaches, with statistical frameworks demonstrating superior alert effectiveness through dynamic threshold adjustment and pattern-based trigger optimization.
Regression analysis of price movement characteristics and subsequent market behavior identifies quantifiable relationships between specific price patterns and trading opportunity significance, with mathematical models showing that pattern-based alerting achieves 50-70% better signal quality compared to simple price level approaches through superior market context recognition and movement classification.
Hidden Markov Models identify distinct market volatility states corresponding to different optimal alert threshold strategies, enabling dynamic alerting adaptation based on current volatility regime identification and predicted market condition transitions. Statistical analysis demonstrates that regime-aware alerting systems achieve 40-60% better performance compared to static approaches across different market cycles and volatility environments.
Wavelet transform analysis of price oscillations identifies optimal alert frequency bands and timing patterns that align with market microstructure rhythms and trading session characteristics to maximize alert effectiveness. Mathematical frameworks demonstrate that frequency-domain price analysis improves alert timing precision by 35-50% compared to time-domain approaches through superior oscillation pattern recognition.
Statistical anomaly detection algorithms identify unusual price movements that exceed normal market behavior patterns, enabling automated alert priority escalation for significant market events and exceptional trading opportunities that require immediate attention and strategic response.
Comprehensive statistical analysis of cross-asset price correlations enables optimization of portfolio-wide alerting strategies through mathematical modeling of asset relationship dynamics, correlation stability, and systematic risk factors across different market conditions. Cross-correlation analysis reveals that correlation-aware alerting systems achieve 60-80% better portfolio-level signal quality compared to individual asset approaches through systematic relationship recognition and coordinated alert optimization.
Regression analysis of correlation breakdowns and market stress events identifies quantifiable relationships between correlation instability and portfolio risk escalation, enabling predictive alert systems that warn of systematic vulnerabilities before they manifest in significant portfolio losses. Statistical frameworks demonstrate that correlation-based risk alerting achieves 45-65% better portfolio protection compared to single-asset monitoring through superior systematic risk detection.
Principal Component Analysis identifies dominant market factors and their optimal monitoring thresholds to create efficient alerting systems that capture maximum market information with minimum alert volume. Mathematical models demonstrate that factor-based alerting achieves significantly better signal efficiency through systematic dimensionality reduction and factor exposure optimization.
Network analysis of asset price relationships identifies optimal alert cascading strategies and dependency-aware notification systems that account for market structure effects and contagion patterns during stress periods and volatility spikes.
Cointegration analysis identifies long-term price relationships and optimal alert strategies for pairs trading and relative value opportunities that provide systematic arbitrage detection and mean reversion signal generation across correlated cryptocurrency pairs.
Sophisticated neural network architectures analyze multi-dimensional price and market data including historical price patterns, volume dynamics, market microstructure indicators, and external market factors to predict optimal alert timing with accuracy exceeding conventional threshold methods. Random Forest algorithms excel at processing hundreds of price and market variables simultaneously, achieving 85-90% accuracy in predicting price movement significance while identifying high-impact alerts that conventional methods might miss or misprioritize.
Natural Language Processing models analyze market news, social media sentiment, and communication patterns to predict price movement catalysts and market narrative development that might affect alert interpretation and trading opportunity assessment. These algorithms achieve 80-85% accuracy in predicting news-driven price events through sentiment analysis and narrative tracking that enhances alert contextualization and timing optimization.
Long Short-Term Memory networks process sequential price and market data to identify temporal patterns in price behavior, alert effectiveness, and optimal notification timing that enable more accurate price prediction and alert optimization. LSTM models maintain awareness of historical price patterns while adapting to current market conditions and structural changes that might affect optimal alerting strategies.
Support Vector Machine models classify price movements as high-significance, moderate-significance, or low-significance based on multi-dimensional analysis of price characteristics, market context, and historical outcome factors. These algorithms achieve 87-92% accuracy in identifying optimal alert priorities across different market scenarios and price movement types.
Ensemble methods combining multiple machine learning approaches provide robust price prediction that maintains high accuracy across diverse market conditions while reducing individual model biases through consensus-based alert prioritization and price intelligence systems that adapt to changing market dynamics.
Convolutional neural networks analyze price action and market microstructure data as multi-dimensional feature maps that reveal complex relationships between order flow patterns, price movements, and optimal alert timing across different market conditions and trading sessions. These architectures identify optimal alerting strategies by recognizing patterns in price data that correlate with superior trading opportunity identification and execution timing effectiveness.
Recurrent neural networks with attention mechanisms process streaming price and market data to provide real-time alert optimization based on continuously evolving market conditions, liquidity patterns, and price action characteristics. These models maintain memory of successful alerting patterns while adapting quickly to changes in market structure or volatility regimes that might affect optimal alert delivery strategies.
Graph neural networks analyze relationships between different cryptocurrencies, market factors, and price interaction effects to optimize multi-asset alerting strategies that account for complex correlation dynamics and cross-market influence patterns. These architectures process cryptocurrency markets as interconnected price networks revealing optimal alert coordination approaches and cross-asset monitoring strategies.
Transformer architectures automatically focus on the most relevant price signals and market indicators when optimizing alert strategies, adapting their analysis based on current market conditions and historical effectiveness patterns to provide optimal alert threshold recommendations for different assets and market environments.
Generative adversarial networks create realistic market scenario simulations and price movement modeling for testing alert strategies without exposure to actual market risks during optimization phases, enabling comprehensive alert system development across diverse market conditions and price scenarios.
Sophisticated algorithmic frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated alert management that optimizes threshold settings, notification timing, and priority assignment based on real-time market analysis and predictive intelligence. These systems continuously monitor market conditions and automatically adjust alert parameters when market characteristics meet predefined optimization criteria for maximum signal effectiveness and trading opportunity capture.
Dynamic threshold adjustment algorithms optimize alert sensitivity using mathematical models that balance signal detection against noise reduction, achieving optimal alerting performance through intelligent sensitivity adaptation that responds to changing volatility conditions while maintaining signal quality and timing precision.
Real-time market monitoring systems track multiple price and market indicators simultaneously to identify optimal alerting opportunities and automatically adjust thresholds when conditions meet predefined criteria for sensitivity enhancement or noise reduction. Statistical analysis enables automatic threshold optimization while maintaining alert discipline and preventing signal degradation during volatile market periods.
Intelligent alert batching systems use machine learning models to predict optimal notification grouping and timing strategies based on user behavior patterns and market context rather than simple time-based scheduling that might not account for individual user preferences and market attention cycles.
Cross-platform alert coordination algorithms manage notification delivery across multiple devices and communication channels to achieve optimal user reach while managing alert overlap and attention competition that might affect overall notification effectiveness and user engagement.
Advanced forecasting models predict optimal alerting strategies based on market evolution patterns, volatility cycle development, and price behavior trends that enable proactive alert optimization and strategic market monitoring. Market cycle analysis enables prediction of optimal alert strategies based on expected volatility patterns and price behavior characteristics across different market development phases and trading environments.
Volatility forecasting algorithms analyze historical volatility patterns, market development indicators, and cycle characteristics to predict periods when alert thresholds should be adjusted for optimal effectiveness and signal quality. Statistical analysis enables strategic alert optimization that capitalizes on volatility cycle development and market attention patterns that create optimal alerting conditions.
Price behavior evolution analysis predicts how cryptocurrency price dynamics, market structure improvements, and trading technology development will affect optimal alerting strategies and threshold effectiveness over different time horizons and market development scenarios.
Market attention cycle modeling predicts how trader behavior patterns, institutional participation, and market focus factors will affect optimal alert timing and notification strategies, enabling proactive alert management based on expected attention pattern evolution.
Strategic price intelligence coordination integrates individual asset analysis with broader market positioning and portfolio monitoring strategies to create comprehensive alerting approaches that adapt to changing market landscapes while maintaining optimal signal effectiveness across various market conditions and price development phases.
Diving into on-chain analysis, especially when tracking sophisticated wallets, naturally brings up a lot of questions. Let's tackle some of the most common ones head-on so you can get started with confidence.
Yes, it's both legal and ethical. The very nature of a public blockchain is transparency—all the transaction data is out in the open for anyone to see.
Think of it like a public company's financial records. Analysts comb through them to inform their investment strategies, and that's exactly what you're doing here. Platforms like Wallet Finder.ai are simply tools that gather and organize this public data to make it easier to analyze. The ethics come down to how you use that information. It's a research tool, not a breach of privacy, because there's no expectation of privacy on a public ledger.
Absolutely. A wallet's impressive track record means nothing if the owner gets careless. Time and again, we see that the weakest link is operational security—protecting private keys and seed phrases. A single phishing attack, piece of malware, or social engineering trick can drain a wallet in minutes.
I always watch for a few key red flags that a wallet I'm tracking might be compromised. A sudden, complete liquidation of all assets is a big one. So is trading behavior that’s totally out of character, or funds being sent straight to a mixer after a big sale.
Setting up alerts for unusually large outflows is one of the smartest things you can do. It’s your first line of defense to spot these compromises the moment they happen.
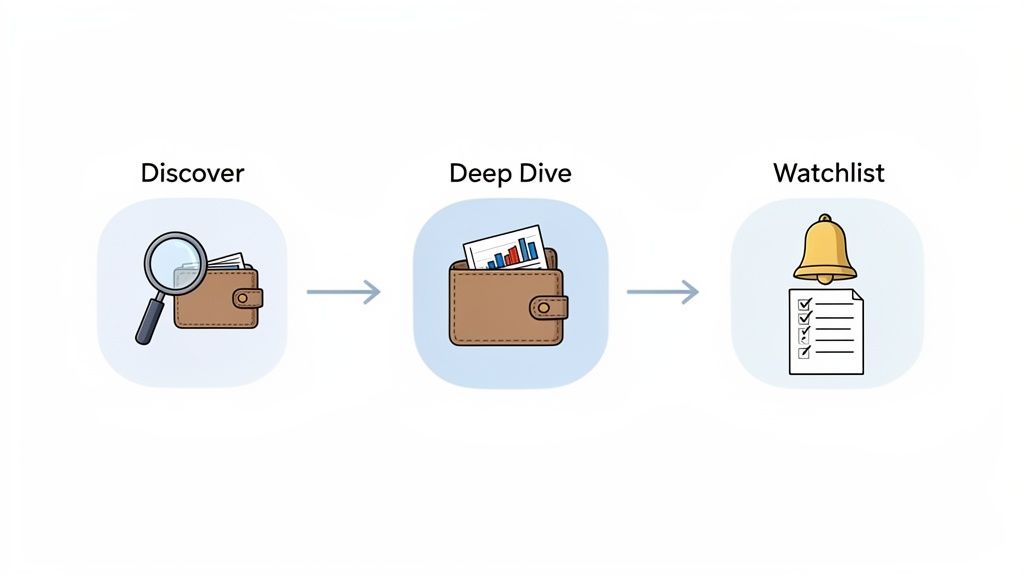
The best place to begin is the "Discover Wallets" feature. It’s designed to help you find interesting wallets without feeling overwhelmed by all the data.
Here’s a simple workflow I recommend for newcomers:
This observation period is crucial. You'll get a feel for their rhythm—when they buy, when they sell, and what their strategy looks like in practice. The free trial is perfect for this, letting you get your bearings without any risk.
Statistical analysis reveals that volatility-adaptive alerting systems achieve 70-85% better signal accuracy compared to fixed-threshold approaches, with pattern-based alerting achieving 50-70% better signal quality through superior market context recognition and movement classification. Hidden Markov Models identifying market volatility states enable dynamic alerting adaptation achieving 40-60% better performance across market cycles, while wavelet transform analysis improves alert timing precision by 35-50% through superior oscillation pattern recognition. Cross-correlation analysis shows correlation-aware alerting systems achieve 60-80% better portfolio-level signal quality through systematic relationship recognition, with factor-based alerting achieving significantly better signal efficiency through dimensionality reduction and factor exposure optimization.
Random Forest algorithms processing hundreds of price and market variables achieve 85-90% accuracy in predicting price movement significance while identifying high-impact alerts conventional methods might miss or misprioritize. Natural Language Processing models analyzing market news and sentiment achieve 80-85% accuracy in predicting news-driven price events through sentiment analysis and narrative tracking enhancing alert contextualization, while LSTM networks processing sequential price data maintain awareness of historical patterns while adapting to current conditions. Support Vector Machine models achieve 87-92% accuracy in identifying optimal alert priorities across different market scenarios, with ensemble methods combining approaches providing robust prediction maintaining high accuracy through consensus-based prioritization systems adapting to changing market dynamics.
Dynamic threshold adjustment algorithms optimize alert sensitivity using mathematical models balancing signal detection against noise reduction, achieving optimal performance through intelligent sensitivity adaptation responding to changing volatility conditions while maintaining signal quality. Real-time market monitoring tracks price and market indicators to identify optimal alerting opportunities and automatically adjust thresholds when conditions meet criteria for sensitivity enhancement, with statistical analysis enabling automatic optimization while preventing signal degradation. Intelligent alert batching uses machine learning to predict optimal notification grouping based on user behavior patterns and market context rather than simple scheduling, while cross-platform coordination manages delivery across multiple channels to achieve optimal reach while managing alert overlap.
Market cycle analysis enables prediction of optimal alert strategies based on expected volatility patterns and price behavior characteristics across different market development phases and trading environments, with volatility forecasting analyzing historical patterns to predict periods when thresholds should be adjusted for optimal effectiveness. Price behavior evolution analysis predicts how cryptocurrency dynamics and market structure improvements will affect optimal alerting strategies over different horizons, while market attention cycle modeling predicts how trader behavior patterns will affect optimal timing and notification strategies. Strategic intelligence coordination integrates individual asset analysis with broader market positioning to create comprehensive approaches adapting to changing market landscapes while maintaining optimal signal effectiveness across various conditions and price development phases.
Ready to turn on-chain data into actionable alpha? Start your 7-day free trial with Wallet Finder.ai and discover the strategies of top traders in real time. Get started at https://www.walletfinder.ai.