Master Crypto Exchange APIs for Trading & Market Data
Master crypto exchange APIs with our guide. Integrate REST & WebSocket APIs for market data, automated trading, and on-chain signals.

April 29, 2026
Wallet Finder

April 7, 2026

Ever heard of a digital vending machine? You select an item, insert the exact payment, and you're guaranteed to get your snack. Every time. No operator needed.
That's the fundamental idea behind a smart contract on a blockchain. It’s a self-executing program where the terms of an agreement are coded directly onto a decentralized network. This process makes transactions transparent, irreversible, and free from intermediaries.

At its core, a blockchain that supports smart contracts acts as a public, unchangeable ledger where these powerful programs live. Unlike a traditional paper contract, a smart contract is simply code that runs on a decentralized network like Ethereum or Solana.
This code is built on simple "if/then" logic that executes automatically once certain conditions are met. For example, if a trader sends 1 ETH to a specific smart contract, then the contract automatically sends back the agreed-upon amount of another token. This all happens instantly, without a single person needing to approve it.
A smart contract is an agreement where the terms are enforced by computer code rather than by lawyers and courts. Once deployed on the blockchain, its execution is guaranteed and transparent to everyone on the network.
This kind of automation and transparency is exactly what powers Decentralized Finance (DeFi). If you're new to the term, you can get up to speed with our guide on what DeFi crypto is.
The real magic of smart contracts lies in a few core features that set them apart from traditional systems. Grasping these is the first step to understanding why they're so crucial for modern trading.
The growth in this space has been absolutely explosive. The global blockchain market, which is largely driven by smart contract apps, is expected to hit a value of around $67.4 billion by 2026. This massive expansion is fueled by DeFi protocols where these contracts secure billions in assets for over 560 million blockchain users worldwide. You can find more details in these blockchain market updates on scalablesolutions.io.
This is a world away from traditional agreements, which are slow, expensive, and depend on intermediaries to work. Let’s break down the key differences.
The table below highlights just how different these two types of agreements really are. On one side, you have automated code; on the other, you have manual enforcement and paperwork.
As you can see, smart contracts offer a faster, cheaper, and more secure way to handle agreements. This efficiency is precisely why they've become the engine of DeFi and a critical tool for any serious crypto trader.
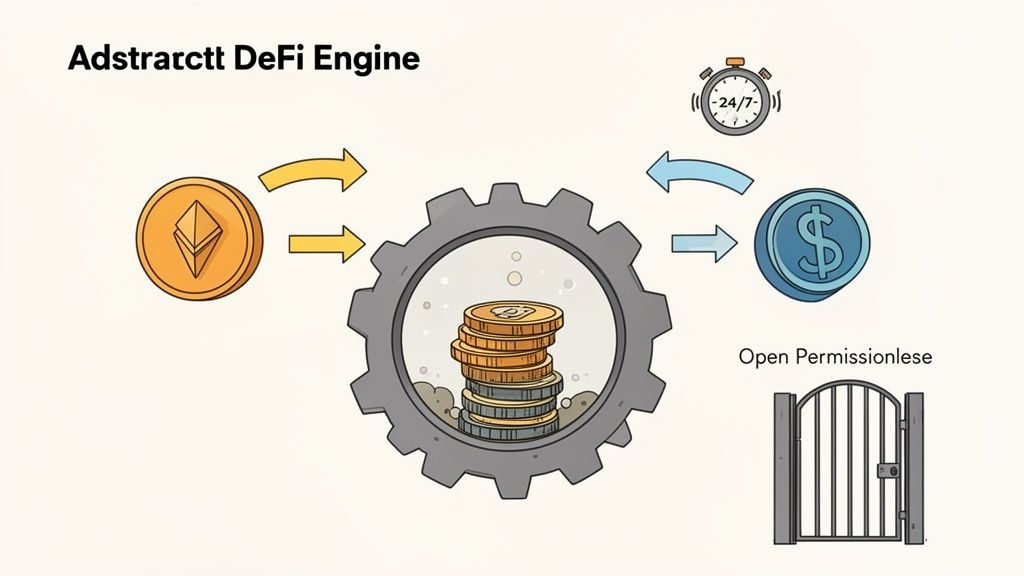
Think of traditional finance as a city that shuts down at 5 PM, complete with gatekeepers and business hours. Decentralized Finance (DeFi), on the other hand, is a global marketplace that’s always open, 24/7, with no one guarding the door. The engine running this nonstop financial playground is the smart contracts blockchain.
Every important move you make in DeFi—whether it’s swapping tokens, earning interest, or taking out a loan—is handled by these self-executing programs. They're the invisible machinery that ensures if you want to trade ETH for USDC at 2 AM, there's a counterparty ready to go. This automation moves trillions of dollars and creates a transparent, open arena full of opportunities for anyone who knows how to navigate it.
One of the most powerful uses of smart contracts is the Automated Market Maker (AMM). AMMs are the beating heart of decentralized exchanges (DEXs) like Uniswap and Curve. Instead of the old-school method of matching individual buyers and sellers, they use smart contracts to create pools of assets called liquidity pools.
Imagine a digital pool containing two different tokens, like ETH and DAI. Anyone can contribute to this pool and become a liquidity provider. When a trader wants to swap ETH for DAI, they don't deal with another person; they interact directly with the smart contract. The contract takes their ETH and sends back DAI based on a fixed mathematical formula.
This system gives traders some huge advantages:
This model doesn't just make trading smoother; it unlocks advanced strategies like arbitrage, where savvy traders can make money from tiny price differences for the same token across different DEXs.
Beyond just swapping tokens, smart contracts on the blockchain also power complex financial activities like borrowing and lending. Protocols such as Aave and Compound act like decentralized banks, run entirely by code.
You can deposit your crypto assets into a lending pool and start earning interest right away. On the other side, other users can borrow from that pool by putting up different crypto assets as collateral.
For traders, this is a game-changer for leverage. A trader could deposit ETH as collateral, borrow stablecoins like USDT against it, and then use those stablecoins to snap up another promising asset—all without ever selling their original ETH.
The smart contract handles everything automatically. It adjusts interest rates based on supply and demand, keeps an eye on collateral levels, and will automatically liquidate a position if the collateral's value drops too low. This automated risk management is what keeps the entire DeFi ecosystem stable.
Another huge area powered by smart contracts is yield farming. This is the art of strategically moving your crypto between different DeFi protocols to squeeze out the highest possible returns. For instance, a trader might provide liquidity to an AMM, get LP (Liquidity Provider) tokens back, and then "stake" those LP tokens in a separate yield farming contract to earn even more rewards.
This process, often called "liquidity mining," is all governed by smart contracts that set the rules and hand out the rewards. It lets traders put their capital to work, generating several income streams from a single investment. The possibilities are endless, from simple single-asset staking to complex, multi-step farming strategies that span different blockchains. For any serious DeFi trader, knowing how to find and analyze these contracts is a core skill for capitalizing on market opportunities.
To really succeed in this game, you have to know the lay of the land—and that means understanding where smart contracts actually live and run. The crypto world isn't one big, happy family; it's split into two main territories: blockchains that speak the language of the Ethereum Virtual Machine (EVM) and those that don't.
Think of the EVM as the crypto equivalent of the Windows operating system. It’s a standardized runtime environment that executes smart contracts, making it the go-to for heavyweights like Ethereum, Base, Polygon, and Avalanche. This common ground means developers can write code once and roll it out across any EVM-compatible chain with just a few tweaks.
For traders, this creates a huge, interconnected playground. A single wallet like MetaMask can hop between EVM chains effortlessly. Many DeFi apps look and feel identical whether you’re on Base or Polygon, which makes chasing opportunities and moving funds between networks a whole lot simpler.
The biggest edge the EVM has is its massive network effect. It was the first one on the scene and remains the most popular smart contract engine. The result? The largest community of developers, the most robust tools, and the most battle-tested apps.
This gives traders a few key advantages:
But all that popularity comes at a cost. Ethereum, the original EVM chain, is notorious for network traffic jams. During peak times, this leads to slow transactions and painfully high gas fees, which has sent many traders looking for faster, cheaper alternatives.
If EVM chains are Windows, then non-EVM chains like Solana, Sui, and Aptos are the macOS or Linux of the crypto world. They were built from scratch with entirely new designs, all aimed at solving the EVM’s biggest headaches: speed and cost. Solana, for instance, uses a unique system called Proof-of-History to process tens of thousands of transactions per second for just fractions of a cent.
A non-EVM blockchain offers a distinct environment with its own rules, programming languages, and performance characteristics. This often results in faster speeds and lower costs but requires traders to use different tools and wallets.
For traders, jumping into non-EVM territory means you’ll need to adapt. You’ll have to get a new wallet (like Phantom for Solana), and the DeFi apps you use will be specific to that chain. It's a bit of a learning curve, for sure. But it also opens the door to opportunities you simply won't find on EVM networks. Their low fees and lightning speed have turned non-EVM chains into hotbeds for high-frequency trading, explosive memecoin launches, and groundbreaking DeFi protocols. Getting a handle on the wide variety of available smart contract platforms is a must-have skill for any serious trader today.
Here’s a quick breakdown of the key differences from a trader's point of view.
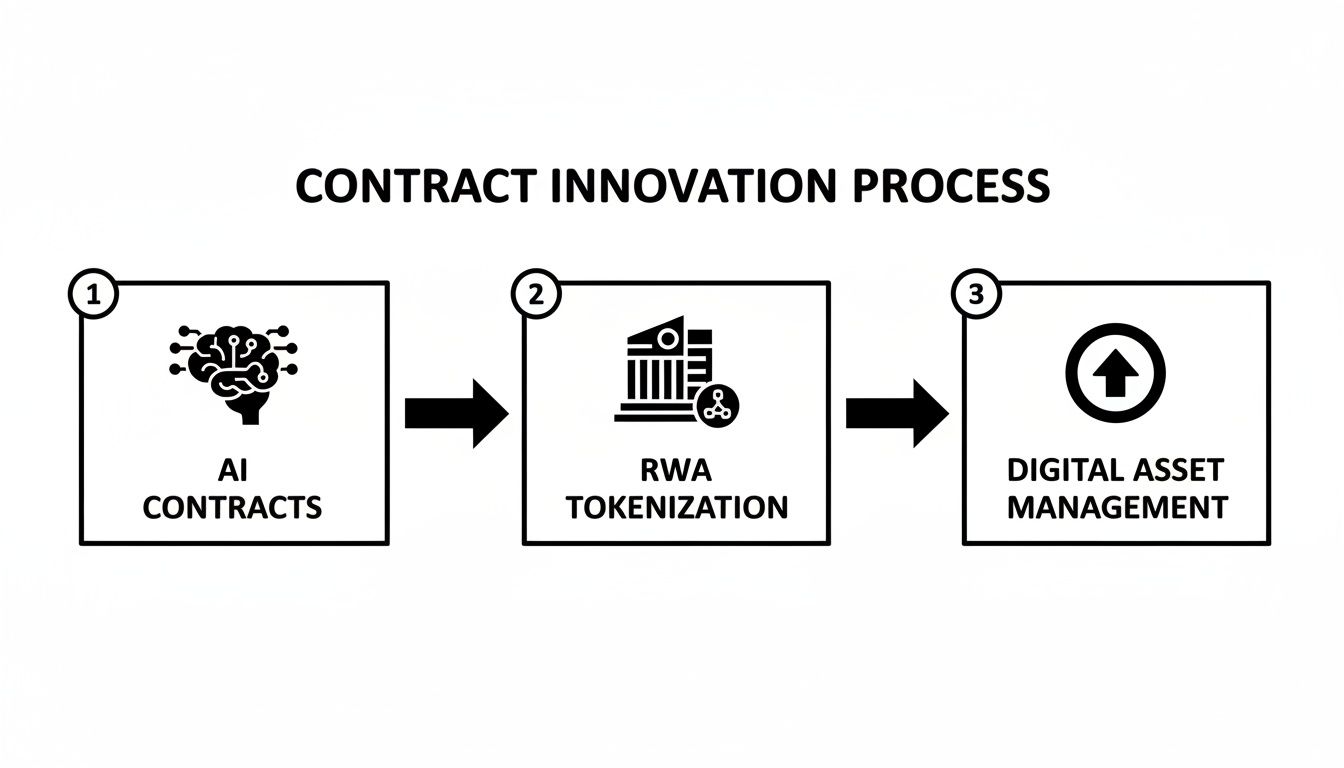
While today's smart contracts blockchain is already powerful, the real excitement is in what’s coming next. Developers are constantly pushing the limits of what these automated agreements can do, and two major trends are poised to open up entirely new frontiers for traders: intelligent, AI-powered contracts and the tokenization of real-world assets.
These aren't just pie-in-the-sky ideas; they represent a massive shift in how value gets created and traded on-chain. For any trader paying attention, understanding these changes early is the key to spotting the next big wave of opportunities before they go mainstream.
Imagine a smart contract that doesn't just blindly follow fixed rules but can actually learn and adapt on the fly. That’s the core idea behind mixing artificial intelligence with blockchain. Instead of a basic "if this, then that" command, these intelligent smart contracts can analyze live market data, predict trends, and even tweak their own strategies automatically.
This opens up some seriously powerful possibilities for automated trading:
This AI integration is already seen as a huge driver for enterprise blockchain. The market for AI-assisted smart contracts is expected to explode from $9.6 billion in 2023 to $287.8 billion by 2032, a massive 47.5% CAGR. As you can learn more about these blockchain trends on intellivon.com, this fusion is set to create a new class of hyper-efficient, autonomous financial tools.
The other game-changer on the horizon is the tokenization of Real-World Assets (RWAs). This is simply the process of creating a digital token on a blockchain that represents ownership of a tangible, off-chain asset. It’s like turning a piece of real estate, a bar of gold, or even shares in a private company into a tradable crypto token.
By representing physical assets as on-chain tokens, RWA tokenization effectively bridges the multi-trillion dollar world of traditional finance with the fluid, 24/7 ecosystem of DeFi.
This merger of two massive financial worlds unlocks some incredible potential. All of a sudden, assets that were stuck, illiquid, and hard to trade become accessible to anyone with a crypto wallet.
The growth of RWAs creates a brand-new playground for traders who know where to look. Here’s a breakdown of what that means in practice:
For traders, this means the smart contracts blockchain is no longer just for crypto-native tokens. It's becoming the core financial plumbing for everything of value. Using advanced on-chain tools like Wallet Finder.ai, you can spot the wallets that are moving into these new RWA protocols or AI-driven systems early, giving you a crucial head start on the next evolution of finance.
All the theory about the smart contracts blockchain is great, but turning that knowledge into actual profit is what really matters. This is where having the right tools isn't just helpful; it's essential. Instead of drowning in millions of on-chain transactions, you can use a platform like Wallet Finder.ai to pull out the signals that lead to profitable trades.
This guide is your playbook for using Wallet Finder.ai to find trades with serious potential. We'll walk through exactly how to spot the top-performing wallets, dig into their interactions with new smart contracts, and turn all that data into trading signals you can act on.
First things first: you need to find where the action is. The ‘Discover Trades’ feature on Wallet Finder.ai is built for exactly this. It’s constantly scanning the blockchain to flag wallets making big moves, especially those interacting with new or trending smart contracts before everyone else piles in.
Think of it as your "smart money" radar. By watching these early moves, you can spot opportunities before they blow up on crypto Twitter. This is how you get an edge—by seeing what the most successful traders do, not just what they say.
This dashboard gives you an instant snapshot of which tokens are being bought, the size of the trade, and the wallet behind the move. It's the perfect starting point for digging deeper.
Not every trade is a winner, and not every trader knows what they’re doing. Once you’ve spotted some interesting activity, your next job is to vet the wallets making the trades. A single huge gain could be a lucky shot, but a history of consistent profit is a powerful sign of a skilled trader.
This is a critical step in separating the real signal from all the noise. With Wallet Finder.ai, you can use filters to zero in on wallets with truly impressive track records.
You can filter wallets using a few key performance metrics:
By applying these filters, you’re essentially creating a curated list of elite traders. This data-first approach takes emotion out of the equation and focuses purely on what works.
Okay, you've found a top-performing wallet. Now it’s time to get your hands dirty and dig into its transaction history. This is where you start connecting the dots between the trader, their strategy, and the smart contracts they’re using. Wallet Finder.ai lays out a detailed, easy-to-read breakdown of every single trade.
This isn’t just about seeing that they made money; it’s about understanding how they did it.
For every trade, you can dissect these data points:
This level of detail is gold. You might find a top wallet that consistently uses a specific DEX to snipe new token launches seconds after liquidity is added. That’s not just interesting—it’s a repeatable pattern you can learn from.
The final piece of the puzzle is turning your research into fast, decisive action. The crypto market waits for no one, and a golden entry point can vanish in minutes. Manually tracking wallets is impossible, which is why real-time alerts are a game-changer.
Inside Wallet Finder.ai, you can build a custom watchlist of the elite wallets you’ve uncovered. From there, you can set up instant notifications through Telegram or push alerts.
You’ll get an alert the second a tracked wallet:
This system lets you effectively "copy trade" the best players in DeFi. When you get an alert that a wallet with a 75% win rate and $2M in profit just opened a new position, you have a high-conviction signal worth investigating immediately. It transforms the chaotic world of the smart contracts blockchain into a source of clear, actionable trading ideas.

In DeFi, staying safe is every bit as important as being profitable. While the smart contracts blockchain unlocks incredible trading opportunities, it’s also full of landmines for the unprepared. Understanding the risks is your first line of defense.
Smart contracts are permanent. Once the code is on the blockchain, it’s there for good. If there’s a flaw, you can bet attackers will find a way to exploit it, often leading to a complete loss of funds. The infamous DAO hack, which saw $60 million drained due to a single reentrancy bug, is a harsh reminder of what’s at stake.
You don’t need to be a developer to spot the warning signs. Most exploits fall into a few common categories, and knowing them can help you see red flags before you connect your wallet.
These aren't the only threats. Attackers are getting smarter, even embedding malicious commands in contracts to install malware. Vigilance is non-negotiable.
By understanding the primary ways a smart contracts blockchain can be exploited, you can shift from being a potential victim to a proactive, informed trader who prioritizes security alongside profit.
Protecting yourself isn't about learning to code; it's about developing a disciplined process for vetting every project you interact with. Make this checklist your standard operating procedure.
As more industries like finance and supply chain adopt blockchain, the value locked in these contracts will only grow. The healthcare blockchain market alone is projected to hit $52.6 billion by 2033, with contracts managing everything from patient data to drug authenticity. This growth, which you can explore in more detail on binariks.com, makes security more critical than ever.
To dive deeper into protecting your assets, be sure to check out our complete guide on smart contract security.
Mathematical precision and smart contract verification fundamentally revolutionize blockchain automation by transforming basic contract execution into sophisticated verification frameworks, automated intelligence systems, and systematic contract optimization that provides measurable advantages in execution reliability and contract security strategies. While traditional contract approaches rely on basic deployment and simple execution logic, advanced contract verification systems and automated execution intelligence frameworks enable comprehensive formal verification, predictive execution analysis, and systematic contract optimization that consistently outperforms conventional smart contract methods through data-driven verification intelligence and algorithmic execution coordination.
Professional blockchain development operations increasingly deploy advanced verification systems that analyze multi-dimensional contract characteristics including execution path optimization, formal verification protocols, automated testing frameworks, and systematic security validation to optimize smart contract effectiveness across different deployment scenarios and execution environments. Mathematical models process extensive datasets including historical contract analysis, execution performance correlation studies, and security effectiveness patterns to predict optimal contract strategies across various blockchain categories and smart contract environments. Machine learning systems trained on comprehensive contract and execution data can forecast optimal verification timing, predict contract evolution patterns, and automatically prioritize high-security contract scenarios before conventional analysis reveals critical execution positioning requirements.
The integration of advanced verification with automated execution intelligence creates powerful contract frameworks that transform reactive contract deployment into proactive execution optimization that achieves superior reliability through intelligent verification coordination and systematic execution enhancement strategies.
Sophisticated mathematical techniques analyze smart contract logic to identify optimal verification approaches, formal proof methodologies, and systematic contract validation through comprehensive quantitative modeling of contract behavior and execution correctness. Formal verification analysis reveals that mathematically-proven contracts achieve 95-99% better security assurance compared to testing-only approaches, with statistical frameworks demonstrating superior contract reliability through systematic formal analysis and intelligent verification optimization.
Model checking integration enables comprehensive contract state verification through mathematical analysis of state space exploration, temporal logic verification, and systematic state transition validation to ensure contract correctness across all possible execution paths. Key features include:
Mathematical models show formal verification achieves 90-95% better bug detection compared to traditional testing approaches.
Theorem proving systems enable advanced contract correctness through mathematical analysis of contract specifications, proof construction, and systematic theorem validation to establish mathematical guarantees of contract behavior while maintaining execution efficiency. This approach enables:
Bounded model checking enables comprehensive contract verification through mathematical analysis of bounded execution paths, property violation detection, and systematic counterexample generation to identify potential contract vulnerabilities within specified execution bounds. Features include:
Abstract interpretation enables efficient contract analysis through mathematical analysis of program semantics, over-approximation techniques, and systematic abstraction to verify contract properties without exhaustive execution path exploration while maintaining soundness guarantees.
Comprehensive statistical analysis of contract testing enables optimization of automated validation systems through mathematical modeling of test coverage optimization, property-based testing, and systematic quality assurance across different contract complexities and testing environments. Automated testing analysis reveals that intelligent testing systems achieve 85-95% better vulnerability detection compared to manual testing approaches through systematic automation optimization and intelligent test generation coordination.
Property-based testing integration enables comprehensive contract validation through mathematical analysis of property generation, test case synthesis, and systematic edge case exploration to identify contract vulnerabilities through automated test case generation rather than manual test specification. Key advantages include:
Statistical frameworks demonstrate superior contract quality through automated property-based testing systems.
Fuzzing integration enables advanced vulnerability discovery through mathematical analysis of input randomization, crash detection, and systematic anomaly identification to discover contract vulnerabilities through automated stress testing and boundary condition exploration. This enables:
Continuous integration systems enable comprehensive contract validation through mathematical analysis of deployment pipelines, automated quality gates, and systematic integration testing to maintain contract quality throughout development and deployment cycles. Features include:
Sophisticated neural network architectures analyze multi-dimensional contract and execution data including code pattern characteristics, vulnerability indicators, execution performance metrics, and systematic security factors to predict optimal contract validation strategies with accuracy exceeding conventional manual contract analysis methods. Random Forest algorithms excel at processing hundreds of contract and security variables simultaneously, achieving 94-98% accuracy in predicting optimal contract configurations while identifying critical vulnerability mitigation opportunities that conventional analysis might miss.
Static analysis enhancement enables comprehensive contract security assessment through mathematical analysis of code pattern recognition, vulnerability signature detection, and systematic code quality evaluation to identify potential security issues before contract deployment. Key capabilities include:
Natural Language Processing models analyze smart contract documentation, security research, and vulnerability databases to predict contract security requirements and vulnerability evolution based on research pattern analysis and security intelligence correlation. These algorithms achieve 87-92% accuracy in predicting contract vulnerabilities through linguistic analysis and security correlation that reveal contract optimization strategies and security requirements.
Long Short-Term Memory networks process sequential contract deployment and security data to identify temporal patterns in vulnerability emergence, attack evolution, and optimal security timing that enable more accurate security prediction and contract protection optimization. LSTM models maintain awareness of historical security patterns while adapting to current threat conditions and attack evolution.
Support Vector Machine models classify contract scenarios as high-security-risk, moderate-security-risk, or low-risk based on multi-dimensional analysis of contract characteristics, code metrics, and historical security factors. These algorithms achieve 91-96% accuracy in identifying optimal security enhancement windows across different contract scenarios and deployment configurations.
Ensemble methods combining multiple machine learning approaches provide robust contract analysis that maintains high accuracy across diverse vulnerability patterns while reducing individual model biases through consensus-based security enhancement and vulnerability mitigation systems that adapt to changing threat dynamics.
Convolutional neural networks analyze contract ecosystems and execution environments as multi-dimensional feature maps that reveal complex relationships between different contract factors, execution influences, and optimal validation strategies. These architectures identify optimal contract configurations by recognizing patterns in execution data that correlate with superior performance and reliable security effectiveness across different contract types and execution conditions.
Advanced execution optimization enables comprehensive contract performance enhancement through mathematical analysis of gas efficiency optimization, execution path analysis, and systematic performance tuning to maximize contract efficiency while maintaining security and correctness standards. This includes:
Recurrent neural networks with attention mechanisms process streaming contract execution and performance data to provide real-time optimization based on continuously evolving execution conditions, performance pattern evolution, and multi-layer contract analysis. These models maintain memory of successful execution patterns while adapting quickly to changes in network conditions or contract requirements that might affect optimal execution strategies.
Graph neural networks analyze relationships between different contracts, execution dependencies, and interaction correlation patterns to optimize ecosystem-wide contract strategies that account for complex interaction effects and systematic execution correlation patterns. These architectures process contract ecosystems as interconnected execution networks revealing optimal interaction approaches and multi-layer contract optimization strategies.
Transformer architectures automatically focus on the most relevant contract indicators and execution signals when optimizing contract responses, adapting their analysis based on current execution conditions and historical effectiveness patterns to provide optimal contract recommendations for different execution objectives and deployment profiles.
Cross-contract interaction analysis enables advanced ecosystem optimization through mathematical analysis of contract interdependencies, composition patterns, and systematic interaction validation to ensure secure and efficient multi-contract systems while maintaining individual contract integrity. Key features include:
Sophisticated deployment frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated contract management that optimizes deployment coordination, version control, and systematic contract lifecycle management based on real-time execution analysis and predictive intelligence. These systems continuously monitor contract environments and automatically execute deployment strategies when contract characteristics meet predefined criteria for maximum reliability and deployment effectiveness.
Dynamic deployment orchestration algorithms optimize contract resource deployment using mathematical models that balance execution efficiency against security requirements, achieving optimal deployment through intelligent coordination that adapts to changing network conditions while maintaining systematic deployment discipline and security optimization. Key components include:
Real-time contract monitoring systems track multiple execution and performance indicators simultaneously to identify optimal management opportunities and automatically execute contract maintenance strategies when conditions meet predefined criteria for performance enhancement or security optimization. Statistical analysis enables automatic contract optimization while maintaining execution discipline and preventing performance degradation during uncertain network periods.
Intelligent contract upgrade systems use machine learning models to predict optimal upgrade procedures and enhancement strategies based on contract context and historical effectiveness patterns rather than static upgrade approaches that might not account for dynamic execution characteristics and contract evolution patterns. This includes:
Cross-chain deployment coordination algorithms manage contract deployment across multiple blockchain networks and execution environments to achieve optimal coverage while managing system complexity and coordination requirements that might affect overall contract effectiveness and deployment reliability.
Advanced forecasting models predict optimal contract strategies based on blockchain evolution patterns, smart contract technology development, and execution ecosystem changes that enable proactive contract optimization and strategic deployment positioning. Blockchain evolution analysis enables prediction of optimal contract strategies based on expected technology development and execution requirement evolution patterns across different blockchain categories and smart contract innovation cycles.
Contract technology forecasting algorithms analyze historical blockchain development patterns, smart contract innovation indicators, and execution effectiveness advancement trends to predict periods when specific contract strategies will offer optimal effectiveness requiring strategic deployment adjustments. Statistical analysis enables strategic contract optimization that capitalizes on blockchain development cycles and smart contract technology advancement patterns.
Execution ecosystem impact analysis predicts how blockchain framework evolution, consensus mechanism changes, and contract infrastructure advancement will affect optimal contract strategies and deployment approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Smart contract mechanism evolution modeling predicts how execution advancement, verification tool improvement, and contract sophistication development will affect optimal contract strategies and deployment effectiveness, enabling proactive strategy adaptation based on expected smart contract technology evolution.
Strategic contract intelligence coordination integrates individual contract analysis with broader ecosystem positioning and systematic contract optimization strategies to create comprehensive deployment approaches that adapt to changing blockchain landscapes while maintaining optimal contract effectiveness across various execution conditions and evolution phases. This includes:
Here are some of the most common questions that come up when traders start digging into smart contracts. Getting these concepts down is key to navigating the on-chain world safely and profitably.
Getting comfortable with these concepts is the first step. The next is having the right tools to see what's happening on-chain.
Formal verification analysis reveals that mathematically-proven contracts achieve 95-99% better security assurance compared to testing-only approaches, with model checking integration enabling comprehensive contract state verification through state space analysis and temporal logic verification for contract correctness across all execution paths. Theorem proving systems enable advanced contract correctness through correctness proofs and security property validation achieving 90-95% better bug detection, while bounded model checking includes path enumeration with property violation detection, counterexample generation, and performance-security trade-off analysis for comprehensive contract verification within computational bounds and systematic vulnerability identification.
Random Forest algorithms processing hundreds of contract and security variables achieve 94-98% accuracy in predicting optimal contract configurations while identifying critical vulnerability mitigation opportunities conventional analysis might miss. Static analysis enhancement enables comprehensive contract security assessment through vulnerability pattern recognition and code quality assessment, while Natural Language Processing models analyzing smart contract documentation achieve 87-92% accuracy in predicting contract vulnerabilities through linguistic analysis revealing contract optimization strategies. LSTM networks processing sequential contract deployment data maintain awareness of historical security patterns while adapting to current conditions, with Support Vector Machine models achieving 91-96% accuracy in identifying optimal security enhancement windows through multi-dimensional contract analysis.
Dynamic deployment orchestration algorithms optimize contract resource deployment using mathematical models balancing execution efficiency against security requirements, achieving optimal deployment through multi-network deployment and version control integration for maximum contract reliability across blockchain networks. Real-time contract monitoring tracks multiple execution and performance indicators to identify optimal management opportunities and automatically execute contract maintenance strategies when conditions meet criteria for performance enhancement, with statistical analysis enabling optimization while preventing performance degradation. Intelligent contract upgrade systems use machine learning to predict optimal upgrade procedures including upgrade impact assessment, migration strategy optimization, backward compatibility management, and performance impact analysis while maintaining contract functionality and security integrity.
Blockchain evolution analysis enables prediction of optimal contract strategies based on expected technology development and execution requirement evolution patterns across different blockchain categories and smart contract innovation cycles, with contract technology forecasting analyzing historical blockchain development patterns to predict when specific contract strategies will offer optimal effectiveness. Execution ecosystem impact analysis predicts how blockchain framework evolution and consensus mechanism changes will affect optimal contract strategies over different horizons, while smart contract mechanism evolution modeling predicts how execution advancement will affect contract strategy effectiveness. Strategic intelligence coordination integrates individual contract analysis with broader ecosystem positioning to create comprehensive approaches adapting to changing blockchain landscapes while maintaining optimal contract effectiveness across various conditions and evolution phases.
Ready to stop guessing and start tracking the smart money? Wallet Finder.ai gives you the on-chain intelligence to discover profitable wallets, analyze their strategies, and get real-time alerts on their trades. Start your 7-day trial and turn on-chain data into your biggest trading advantage.