Price Action Analysis for Crypto Trading
Master price action analysis for crypto & DeFi. This guide explains key patterns, risk management, and how to combine charts with on-chain wallet data.

May 14, 2026
Wallet Finder

March 30, 2026

The most common Coinbase Wallet scams all boil down to one thing: tricking you into handing over your assets or your secret recovery phrase. It's a tough lesson to learn, but with Coinbase Wallet, you are in complete control of your security. This freedom is exactly what thieves bank on.
To keep your crypto safe, you first have to grasp the huge difference between using the Coinbase exchange (Coinbase.com) and the Coinbase Wallet app.
Think of Coinbase.com as your bank. The institution holds your funds, and they’re responsible for securing them behind the scenes. Coinbase Wallet, on the other hand, is like having physical cash in your own personal safe. You have total control, but you also have total responsibility for keeping it locked down. Scammers thrive on this distinction.
This shift from a custodial service (the exchange) to self-custody (the wallet) is where the real danger lies. Scammers know Coinbase can’t reverse a transaction or get your funds back from your personal wallet. Their entire strategy is to con you—the sole guardian of your crypto—into making a fatal mistake.
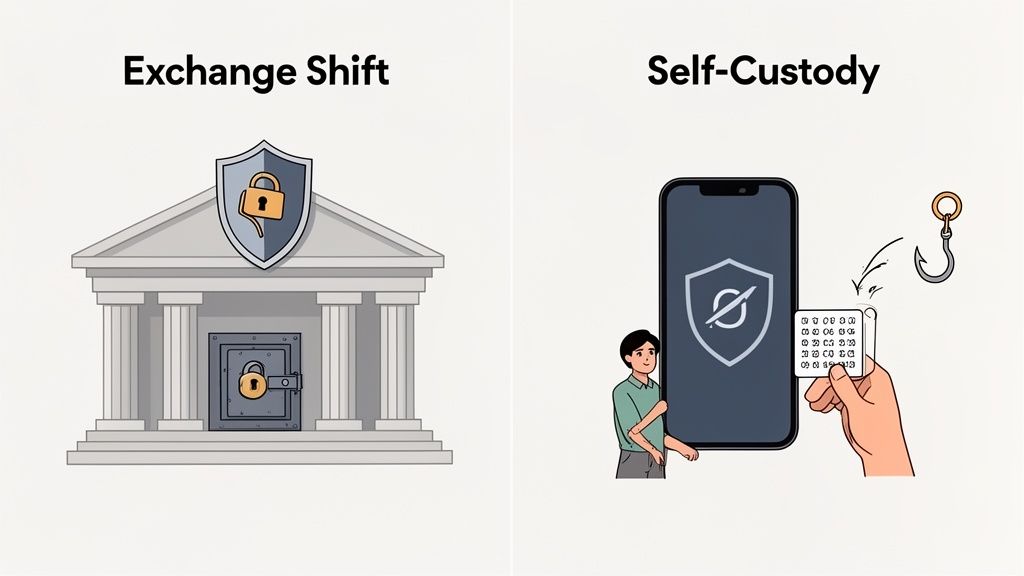
Because the security models are worlds apart, so are the risks. On Coinbase.com, the company has massive, platform-wide security systems in place. With Coinbase Wallet, the security is all on you.
This means your biggest vulnerabilities aren't hackers breaking into Coinbase's servers, but rather:
Once your recovery phrase is compromised, it’s game over. An attacker gains irreversible control of your funds. Understanding this is the single most important step in protecting yourself. For a more detailed breakdown, check out our guide on how secure the Coinbase Wallet is.
Let's put this side-by-side to make it crystal clear. This table contrasts where the security responsibilities and common threats lie for the exchange versus your personal wallet.
| Feature | Coinbase.com (Custodial Exchange) | Coinbase Wallet (Non-Custodial) |
|---|---|---|
| Who Holds the Keys? | Coinbase secures your private keys. | You hold your own private keys and recovery phrase. |
| Recovery Method | Password reset and identity verification. | Your 12-word recovery phrase is the ONLY way. |
| Primary Scam Vector | Account takeover through stolen passwords and SIM swaps. | Tricking you into signing malicious transactions or giving up your recovery phrase. |
| Fund Recovery | Possible in some cases, as Coinbase controls the accounts. | Impossible. Once funds are gone, they cannot be recovered by Coinbase. |
This table shows exactly why scammers target Wallet users so aggressively—the power is entirely in your hands, and so is the potential for error.
The critical takeaway is this: With Coinbase Wallet, you are the bank. Any successful scam relies on tricking you, not on hacking Coinbase's systems. Adopting this mindset is your single strongest defense.
Scammers are creative, persistent, and always sharpening their tactics. They’re laser-focused on exploiting human psychology, not complex code. Knowing their playbook is your first—and best—line of defense against a potential Coinbase Wallet scam.
They operate on a simple principle: in self-custody, tricking you is the only thing standing between them and your funds. Let's break down the most common traps.
Phishing is one of the oldest tricks, but it’s still dangerously effective. Criminals build a pixel-perfect copy of a legitimate website—like the Coinbase login page or a dApp connection prompt—to fool you into handing over your sensitive info.
How it works:
These attacks work because they manufacture panic. The urgency is a tool to make you act before you think. To get better at spotting these fakes, check out our detailed guide on identifying a Coinbase phishing email.
Decentralized applications (dApps) are the heart of Web3, but this is also where scammers build malicious apps to steal your crypto. When you connect your wallet to a dApp, you sign a "permission" or "approval." A legitimate dApp asks for limited permissions, but a malicious one tricks you into signing a transaction with dangerously broad ones, such as an unlimited spending approval for a token like ETH or USDC.
Signing a malicious smart contract is like handing a thief a signed blank check. You've given them pre-authorization to take whatever they want from your wallet at any time, without needing your approval again.
Common Lures for Malicious DApps:
Always be extremely skeptical of any dApp you are not 100% certain is legitimate.
This is arguably the most insidious Coinbase Wallet scam because it preys on people who are already stressed and looking for help. It works by having scammers impersonate official support staff to manipulate you.
How it plays out:
Coinbase has been crystal clear: they will never ask for your recovery phrase, password, or remote access to your computer. They will also never slide into your DMs on social media to offer support. If someone does, it is a scam—every single time.
These three methods—phishing, malicious dApps, and fake support—are the foundation for nearly every attack. Recognizing these patterns is the key to keeping your crypto safe.
To really get how a modern Coinbase Wallet scam works, you have to forget about simple fake emails. We're talking about coordinated criminal operations now. These aren't lone wolves; they’re organized groups that mix technical skills with sharp psychological manipulation to build trust, create panic, and walk you step-by-step toward emptying your wallet.
By looking at a real-world case, you can see their playbook in action. Once you know the pattern, the red flags are much easier to spot.
As crypto has grown, so have the criminals. What used to be basic phishing emails has turned into multi-stage attacks. A chilling example is the case of Ronald Spektor, a 23-year-old who orchestrated a scheme that drained nearly $16 million from his victims.
Spektor’s crew didn't just guess passwords. They ran a professional operation, first bribing insiders to get customer data. Then, they used that info to impersonate Coinbase support with terrifying accuracy. You can dive deeper into how these rings operate in this 2026 crypto crime analysis from Chainalysis.
This case shines a light on the single biggest vulnerability: the human element. The scam wasn't just about code; it was a masterclass in social engineering.
The Spektor case proves that the most dangerous scams aren't random. They are well-planned campaigns that use insider information and psychological pressure to make an impersonation feel completely real.
Let’s walk through the typical flow of one of these impersonation scams. It’s a methodical process designed to break down your defenses one piece at a time.
This timeline shows how scammers have evolved their tactics, often blending them together for a more effective attack.
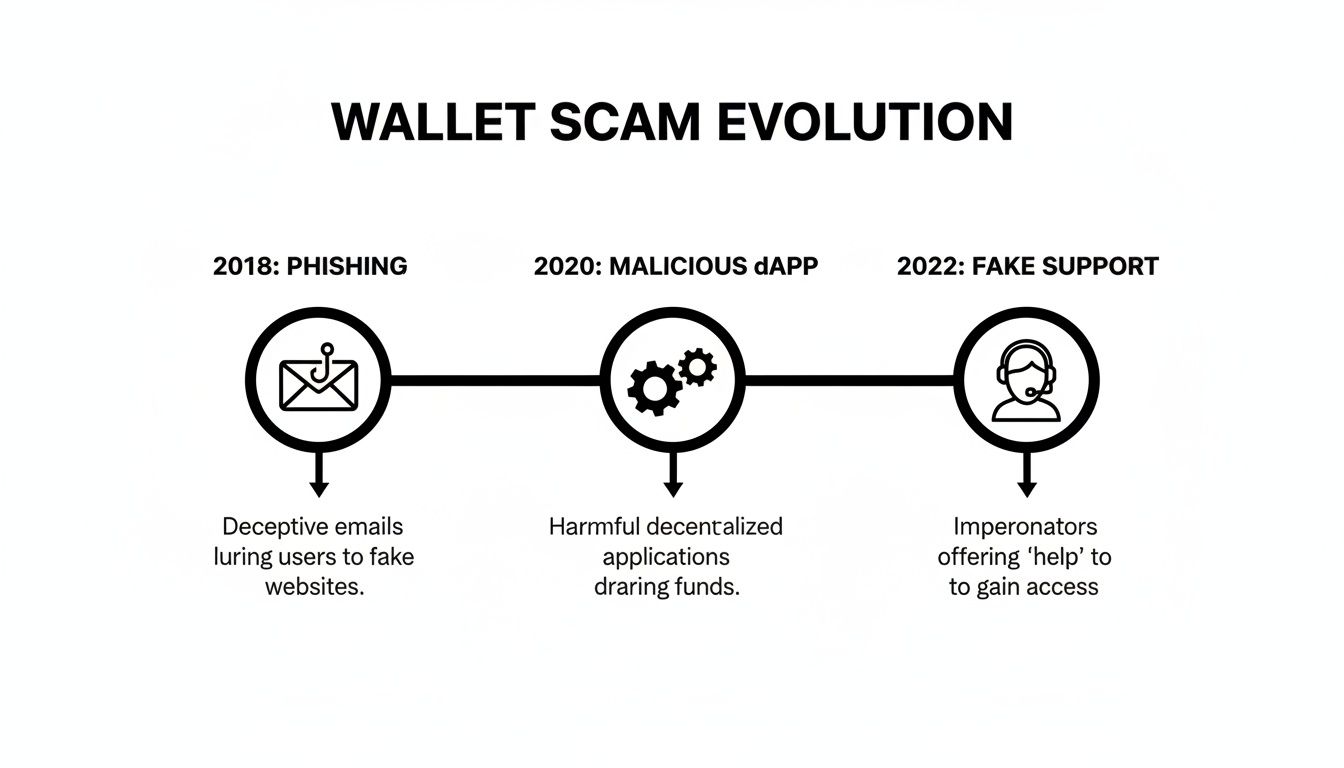
As you can see, phishing, malicious dApps, and fake support are no longer separate threats. Attackers now combine them into a single, cohesive strategy.
These criminals are experts at psychological warfare. They know exactly which buttons to push to make you panic and bypass your rational thinking.
| Tactic | How It Works | How to Counter It |
|---|---|---|
| Urgency and Fear | "Your funds will be gone in minutes if you don't act now!" Creates panic to force impulsive decisions. | Slow down. A real security issue won't require you to break security rules. Hang up. |
| Authority | They use official titles ("Senior Agent") and your personal data to seem credible. | Remember that real support will never DM you or ask for your recovery phrase. |
| Problem and Solution | They invent a crisis (e.g., a "hack in progress") and position themselves as the only possible fix. | Be skeptical. Hang up and contact support through official, verified channels only. |
The lesson from these organized attacks is simple. It doesn't matter how convincing someone seems or how much they know about you. You have to stay skeptical. The entire security of your wallet rests on one rule: never share your recovery phrase or sign a transaction for anyone, especially under pressure. Real Coinbase support will never ask you to.
Knowing how scams work is one thing, but building a solid defense is what really matters. It's time to create your security playbook for hardening your Coinbase Wallet against attackers.
Think of these steps as essential habits, not just suggestions. Turning them into a routine is what builds a real barrier between your crypto and the scammers trying to get it. Let's walk through your security checklist.
Your 12-word recovery phrase is everything. If a scammer gets it, your funds are gone—no password resets, no customer support, and no second chances. It's the master key to your entire crypto life.
Actionable Steps:
This is the absolute foundation of self-custody. To get a better handle on this, check out our guide explaining why your seed phrase is your wallet.
Connecting to decentralized applications (dApps) is where things often go wrong. You have to treat every new interaction as a potential risk and act accordingly. This is all about changing how you explore Web3.
The key is to limit your main wallet's exposure.
Your best friend for exploring new dApps is a "burner wallet." This is just a separate wallet you fund with a small amount of crypto you can afford to lose. If you connect to a malicious site and it gets drained, you only lose a tiny sum while your main savings stay safe.
A burner lets you experiment without risking your life savings. Only after you've confirmed a dApp is legitimate and plan to use it regularly should you even think about connecting your primary wallet.
Scammers need you to click first and think later. They create urgency to get you to act impulsively. Your best defense is to simply slow down and check everything before you sign or click.
Before approving any transaction, pause and ask yourself these questions:
C0inbase-support.io instead of the real Coinbase.com).When you connect to a dApp and sign a transaction, it’s not just a one-time thing. You're giving that dApp's smart contract an ongoing permission to interact with your funds. Forgetting to revoke these permissions leaves a backdoor wide open.
Think of it like giving a valet the key to your car. Even after you get the car back, they could have made a copy. Revoking permissions is like changing the locks.
Make it a monthly routine to review all the active connections to your wallet. Use a trusted token approval checker to see which dApps can access your funds, and immediately revoke any you don't use or trust anymore.
| Security Action | Why It's Critical | How to Implement It Now |
|---|---|---|
| Protect Recovery Phrase | It's the master key to your wallet. Losing it means losing everything. | Write it down physically. Store it offline in a secure location. Never share it. |
| Use a Burner Wallet | It isolates risk, protecting your main funds when trying new dApps. | Create a new wallet and fund it with a small, disposable amount of crypto for testing. |
| Verify Transactions | Prevents you from signing a malicious contract that can drain your funds. | Read every wallet pop-up carefully. Scrutinize permissions before approving. |
| Revoke Permissions | Closes old backdoors into your wallet from dApps you no longer use. | Use an approval checker like the one on Etherscan monthly to review and revoke old connections. |
By making these four habits part of your crypto routine, you dramatically lower your risk. Security isn't a one-time setup—it's a constant state of vigilance.
That sinking feeling when you realize you’ve been hit by a Coinbase Wallet scam is unmistakable. Panic is natural, but what you do in the next few minutes is critical. Acting fast can stop the bleeding and kickstart the reporting process.
Think of this as your emergency action plan. We’ll break it down into three stages: containment, reporting, and realistic expectations. Every second counts.
Your number one priority is to cut the attacker off. If they have access to your wallet, they won't stop with what they’ve already taken—they’ll drain anything else you add. You have to shut them out, now.
With the immediate threat contained, it’s time to report the incident. This isn’t just about the slim hope of getting your funds back; it’s about giving law enforcement the data they need to track these criminals and protect others.
Who to Notify:
Your report is a puzzle piece in a much larger investigation. It helps authorities connect dots between different crimes and build cases against organized criminal groups.
Here’s the tough part: getting stolen crypto back is incredibly rare. Blockchain transactions are designed to be irreversible. Once the funds are gone, they’re almost impossible to claw back. Still, reporting is far from a wasted effort.
Coinbase impersonation schemes are just one piece of a massive illicit ecosystem, estimated to be worth $158 billion in 2025. Research shows that while these specific scams contributed to the $23 billion in verified fraud across crypto platforms in 2025—plus another $12 billion from community complaints—this attack vector is a favorite for organized crime. You can read the full breakdown in these 2026 crypto crime findings.
By reporting a Coinbase Wallet scam, you're feeding crucial data into the system that helps law enforcement fight this widespread problem. Your actions might just keep someone else from becoming the next victim.
When you’re managing your own crypto, questions are bound to come up, especially with the constant threat of a Coinbase Wallet scam. Let’s tackle some of the most common concerns head-on. The idea is to clear up any confusion and give you the confidence to keep your assets safe.
The short answer is no. Because Coinbase Wallet is a non-custodial wallet, you are the only one who controls the private keys and the 12-word recovery phrase. Think of Coinbase as the company that built your personal digital vault—they provide the software, but they have no key or combination to open it.
This is a core feature of self-custody, not a bug. It’s what gives you total control over your funds. The flip side is that if your assets are stolen, Coinbase has no technical ability to reverse the transaction or get into your wallet to retrieve them. That's why your own awareness and security practices are everything.
A hardware wallet is a fantastic security tool. It keeps your private keys in "cold storage," meaning they're completely offline. This makes it almost impossible for a hacker to steal your keys directly from your computer or phone. But it's not a magic shield against every type of scam.
A hardware wallet’s primary job is to securely sign transactions. If you get tricked into approving a malicious transaction—like giving a scam dApp unlimited spending access—the hardware wallet will do exactly what you tell it to and sign away.
A hardware wallet protects your keys, not your judgment. It will execute any transaction you authorize, even a fraudulent one. You still need to double-check every transaction before you approve it.
At the end of the day, a hardware wallet can't stop you from being socially engineered. It protects you from remote hacks, but it won't save you from signing a bad contract yourself.
You should be extremely wary of any unsolicited tokens or NFTs that just show up in your wallet. This is a classic move in a Coinbase Wallet scam. Scammers love to send "free" NFTs or a bunch of worthless tokens to grab your attention.
The real danger isn't the asset itself, but what it tempts you to do next.
If it looks too good to be true, it is. Never, ever interact with unsolicited assets or click on any links they contain. The smartest and safest thing you can do is just ignore them. Legitimate projects don't need to use shady tactics to find users.
Ready to turn on-chain data into your trading advantage? With Wallet Finder.ai, you can discover the strategies of top-performing wallets and get real-time alerts on their moves. Stop guessing and start mirroring winning trades today with our powerful DeFi wallet tracker. Start your 7-day free trial at Wallet Finder.ai.