10 Best Cryptocurrency Screeners for 2026
Find the best cryptocurrency screener for your strategy. We review 10 top tools for on-chain data, copy trading, TA, and fundamental analysis.

May 21, 2026
Wallet Finder

April 6, 2026

Let's get one thing straight: a strong password isn't enough to protect your crypto. It's just the first lock on the door. A crypto 2FA code is the second, and it's what truly keeps your assets safe.
Think of your password as the permanent key to your house. It works every day, but if a thief steals it, they can walk right in. A crypto 2FA code is completely different. It’s like a unique PIN a security guard gives you at the front gate, which expires in 60 seconds.
Even if that thief has your house key (password), they're stuck at the gate. By the time they try to get a new PIN, the old one is gone and a new one has taken its place. This moving target is what makes two-factor authentication a non-negotiable for anyone serious about crypto.
In the high-stakes world of crypto, where a single wallet can hold a fortune, 2FA is your most critical line of defense. Account takeover attacks are a constant threat, and the losses can be staggering. The crazy part? Data shows that up to 80% of security breaches could be stopped cold with 2FA, but many platforms and users still don't make it a priority. You can read more on how 2FA thwarts common attacks on Coinbase's security blog.
This simple step is one of the most powerful ways to prevent the kind of hack that can drain a portfolio in minutes. Whether you’re just starting out or you’re a pro trader, you need it. Without 2FA, you’re trusting a single, static password to protect your entire financial future.
Key Takeaway: A password proves what you know, but a 2FA code proves what you have (like your phone or a hardware key). Requiring both makes your account exponentially harder to crack.
To put it all together, here’s a quick breakdown of what a crypto 2FA code is and what it does.
This table simplifies the core job of a 2FA code in securing your accounts.
| Concept | Description | Analogy |
|---|---|---|
| Crypto 2FA Code | A short, time-sensitive numerical code used as a second verification step. | A one-time PIN for a secure facility. |
| Source | Generated by an authenticator app, SMS, or hardware key. | The security guard who issues the PIN. |
| Purpose | To verify your identity and protect against unauthorized access. | To confirm you are the authorized person entering. |
Ultimately, a 2FA code adds a physical or device-specific layer to your login process, making it incredibly difficult for anyone but you to gain access.
Picking the right second factor to secure your crypto is a huge deal. Not all 2FA methods are created equal, and while having any 2FA is a massive improvement, you need to understand the trade-offs to properly protect your assets. Your choice really boils down to your personal risk tolerance and how much you have at stake.
This flowchart says it all. If you hold crypto, using 2FA isn't optional—it's essential.
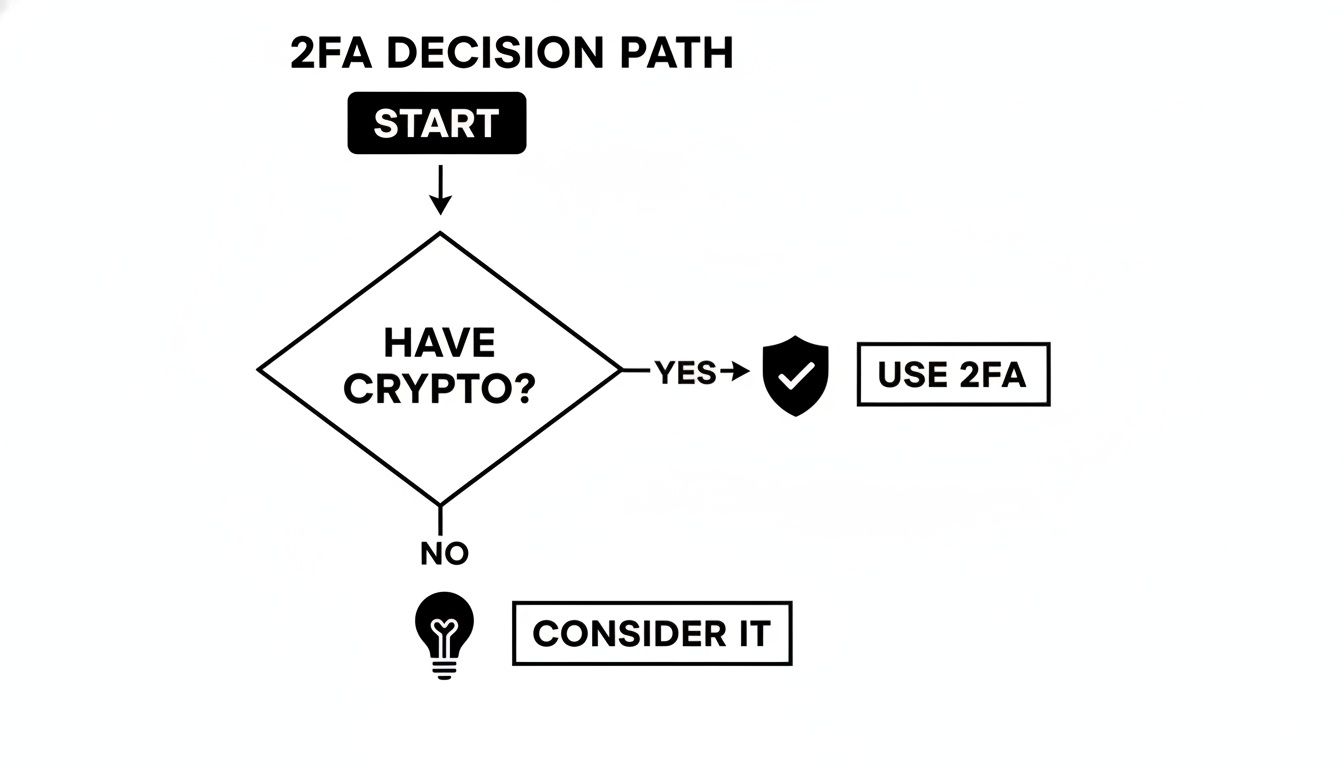
The bottom line is simple: owning crypto means you absolutely need the extra security that 2FA provides.
The most familiar method for many is getting a crypto 2FA code sent to your phone via SMS. When you try to log in, the platform texts a temporary code to your phone. You punch it in, and you're in.
A scammer can fool your phone company into porting your number to a new SIM card they control. Once they've hijacked your number, they get your 2FA codes and can walk right into your accounts.
A much safer option is to use an authenticator app like Google Authenticator, Microsoft Authenticator, or Authy. These apps generate Time-based One-Time Passwords (TOTP) that change every 30-60 seconds.
Because the codes are generated on your device and never sent over a network, they are completely immune to SIM swap attacks. This method strikes a great balance between strong security and ease of use, making it the go-to recommendation for most crypto holders.
A massive supply chain attack on the JavaScript ecosystem a while back involved a "crypto-stealer" malware. The whole thing started when a developer was phished and handed over their password and 2FA credentials. This is a stark reminder that even with solid 2FA, you have to stay sharp and watch out for phishing scams trying to trick you.
If you're looking for the absolute best protection, nothing comes close to a physical hardware key. Devices like a YubiKey or a Ledger hardware wallet are the gold standard for two-factor authentication.
To log in, you plug the key into a USB port or tap it to your phone (using NFC) and then touch a button. Since the crucial data never leaves the physical device, an attacker can't steal it remotely. This method protects you from everything—phishing, malware, and SIM swaps—making it the no-brainer choice for anyone securing a large crypto portfolio.
Thinking through these options is crucial. While SMS is better than nothing, most people should be using an authenticator app. If you have significant funds, investing in a hardware key is one of the smartest moves you can make. The security of the platform itself also plays a big role; for instance, you can check out our guide on whether Coinbase is safe to store crypto to see how all these security layers fit together.
This table neatly summarizes the key trade-offs to help you make your decision.
| 2FA Method | Security Level | Ease of Use | Key Vulnerability | Best For |
|---|---|---|---|---|
| SMS Codes | Low | Very Easy | SIM Swap Attacks | Non-crypto accounts or absolute beginners. |
| Authenticator App | High | Easy | Device Loss/Theft | The average crypto holder. |
| Hardware Key | Very High | Moderate | Physical Loss/Damage | High-value portfolios and active traders. |
At the end of the day, choosing the right crypto 2FA code method is about matching your security to the value you're protecting. Don't just go with the default setting. Make a smart, informed choice.
Switching on two-factor authentication is a solid move for your crypto security, but don’t get complacent. Thinking any 2FA is an unbreakable shield is a rookie mistake that can cost you everything.
Clever attackers have specific ways to get around weaker 2FA methods. Knowing how they operate is the only way to stay a step ahead and turn their tactics into red flags you can easily spot. The biggest mistake traders make is assuming all 2FA is created equal—it’s not. An SMS code is worlds away from the security of an authenticator app or hardware key. Attackers go after the path of least resistance, and for most people, that's their phone number.
One of the most devastating attacks is the SIM swap. This has nothing to do with hacking your device and everything to do with manipulating your mobile carrier. The attacker simply calls your provider's customer service line, pretending to be you.
They'll use personal info scraped from old data breaches or even your social media profiles to answer security questions. Once they've convinced the support agent, your phone number is instantly ported to a SIM card in their possession. From that moment on, all your texts and calls—including those precious crypto 2FA codes—go straight to the thief.
The scariest part of a SIM swap? Your phone suddenly loses service. That’s often the first and only warning you get. By the time you figure out what happened, the attacker has already used the SMS codes to empty your accounts.
This is precisely why security pros are so adamant about ditching SMS for 2FA. Its security relies entirely on your mobile provider, putting the keys to your crypto kingdom completely out of your hands.
Another brutally effective method is good old-fashioned phishing. Attackers build fake login pages for major exchanges like Coinbase or Binance that look identical to the real deal. They’ll blast out emails or texts with an urgent warning—"suspicious login detected"—and a link to "secure your account."
You click the link and land on their bogus site. You enter your username and password, which they steal instantly. But the scam doesn’t end there. The fake site then asks for your crypto 2FA code. The moment you type in that 6-digit code from your authenticator app, their automated script uses it—along with your password—to log into the real exchange and hijack your account.
This man-in-the-middle attack happens in seconds. Here's how to spot it:
c0inbase.com instead of coinbase.com is a dead giveaway.For DeFi traders and on-chain analysts, the stats are sobering. A high-profile breach at a major exchange was caused by employees being socially engineered. While user data was compromised, the attackers couldn’t drain the funds. Why? They couldn't get past the hardware 2FA keys. Learn more about this breach and its security implications to see how a physical key can stop even a targeted, internal attack in its tracks.
Finally, some attacks are just straight-up confidence tricks. A scammer might call, claiming to be from your exchange’s fraud department. They'll tell you your account is at risk and, to "verify your identity," they need you to read them the 2FA code that just popped up on your phone.
Handing over that code is like giving a thief the key to your bank vault. No legitimate company will ever call or email you asking for your password or your crypto 2FA code. That information is for you and you alone. Your ability to spot and shut down these psychological games is just as critical as the security tech you use.
Knowing you need two-factor authentication is one thing, but actually setting it up correctly is where the real security happens. We’ll walk you through setting up a crypto 2FA code using an authenticator app—the method we recommend for its strong blend of security and ease of use.
The process is pretty much the same whether you're on a major crypto exchange or a specific wallet. Our goal here is to demystify the setup so you can lock down your accounts with confidence.
First things first, you need the tool that generates the 2FA codes. Your phone is about to become your digital key, so head to the official Google Play Store or Apple App Store and download a reputable authenticator app.
Some of the most popular and trusted options are:
Pick one and get it installed on your smartphone. We’ll move forward assuming you’ve got one of these ready to go.
Now, log into your crypto exchange or wallet account on a desktop computer. You'll need to dig into your account's security settings. Usually, you can find this under "Profile," "Account," or a tab clearly labeled "Security."
Look for an option called "Two-Factor Authentication," "2FA," or "Authenticator App." Clicking this will kick off the setup process. Most platforms will ask you to re-enter your password just to be safe.
Pro Tip: Always set up 2FA on a device and network you trust completely. Never use public Wi-Fi for this, as it could expose your setup key to anyone snooping on the network.
As DeFi traders hunt for the next alpha wallet, securing their own is non-negotiable. By 2026, the majority of users will be using 2FA, and for crypto investors, that number is even higher. Getting this right isn't just a suggestion—it’s a core skill. You can explore detailed research on multifactor authentication trends to see just how critical it's become.
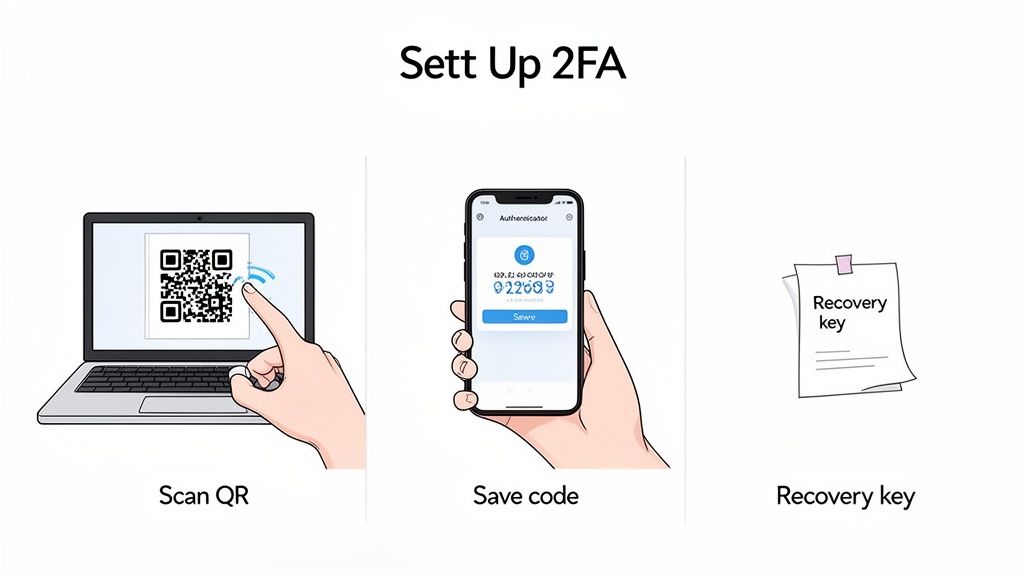
The exchange will now show you a QR code on the screen. Right next to it, you'll see a long string of text, which is your "setup key" or "secret key." This is what creates the unique link between your account and your authenticator app.
To finish up, the exchange needs to make sure everything is synced correctly. Your authenticator app will now be generating a fresh 6-digit crypto 2FA code every 30 to 60 seconds.
Type the current code from your app into the verification field on the website. Hit "Enable" or "Confirm," and you're done! Your account is now officially secured. From now on, logging in will require both your password and a time-sensitive code from your app. The process is nearly identical across platforms, and you can check out our guide on setting up the Robinhood authenticator app to see another example.
Flipping the switch on a strong crypto 2FA code is a huge win for your security. But it also creates a new point of failure: what if you lose your 2FA device? A lost or broken phone can lock you out of your own accounts just as effectively as a hacker can.
That’s why a solid backup and recovery plan isn't just a "nice-to-have"—it's a critical piece of your security setup. Without it, you could be staring down a long, painful, and sometimes impossible account recovery process.
When you first enable 2FA with an authenticator app, you're given a vital piece of information: the secret key or recovery phrase. It’s usually a long string of random characters shown right next to the QR code. This key is the master blueprint for your 2FA.
Think of it like this: the QR code is just a quick snapshot, but the secret key is the original film negative. With that key, you can regenerate your 2FA codes on any new device, anytime. Losing your phone without it is like locking your life savings in a vault and throwing away the only key.
You must treat your 2FA backup key with the same extreme caution as your crypto wallet's seed phrase. It's your only lifeline for regaining access if your main device is ever lost, stolen, or broken.
Your absolute first priority during setup is to secure this key. Skipping this step leaves a gaping hole in your security. The concept is identical to protecting a wallet, and you can get a deeper understanding in our guide on what a seed phrase wallet is and why it's so important.
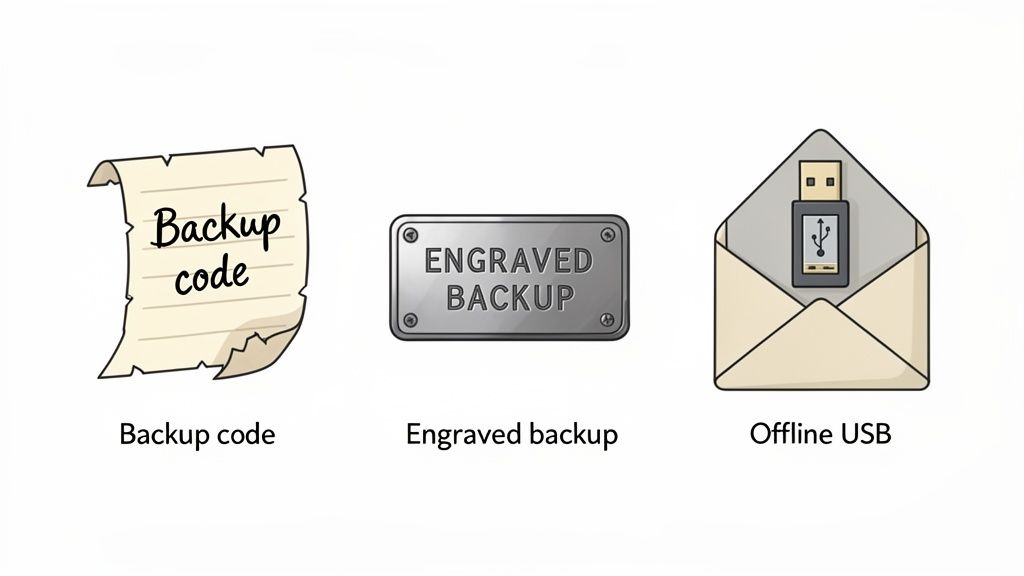
The number one rule for storing your backup key is simple: keep it offline. Saving it in a notes app, an email draft, or a cloud drive completely defeats the purpose and puts it right where hackers can find it. Here are a few practical, battle-tested methods for storing your keys safely.
So, the worst has happened—your phone is gone. Don't panic. If you saved your backup key, recovery is surprisingly simple and takes just a couple of minutes.
Having this key on hand turns a potential disaster into a minor hiccup. It's the only guaranteed way to get back into your accounts on your own terms, without begging a support team for help.
If you're an active trader or a DeFi power user, standard security just doesn't cut it. When you’re managing a high-value portfolio or copy trading profitable wallets with a tool like Wallet Finder.ai, you have to think like a pro. Going beyond basic 2FA is a must to protect serious assets from determined attackers.
Think of these advanced strategies as building a layered security system. The idea is to create a fortress where, even if one wall is breached, your crypto stays locked down. This is exactly how smart money operates in the fast-paced, high-stakes world of digital assets.
One of the smartest moves you can make is to "air gap" your authentication. This means getting a dedicated, offline smartphone that you use only for generating your crypto 2FA codes. This device shouldn't have any other apps, it should never connect to public Wi-Fi, and you should remove its SIM card.
This simple move isolates your 2FA codes from your everyday phone, which is a constant target for malware, phishing links, and SIM swap attacks. By keeping your authenticator on a separate, offline device, you take the most common attack vectors completely off the table. It's a straightforward but incredibly powerful way to guard your master keys.
A massive supply chain attack on the JavaScript ecosystem not long ago involved a "crypto-stealer" malware hidden in popular code libraries. The breach started when a developer got phished and gave up both their password and 2FA code. It’s a harsh reminder that even a strong crypto 2FA code can be useless if social engineering gets an attacker onto your internet-connected device.
For any account holding a significant amount of money, a hardware security key is non-negotiable. Whether it's a YubiKey or you're using a Ledger wallet for 2FA, these physical devices are the gold standard for a reason: they are practically immune to remote attacks.
The secret key never leaves the physical device, so it’s impossible for a phisher or malware to snatch it from afar. The login process demands you physically touch a button on the key—an action an attacker on the other side of the world simply can't fake. For any serious trader, the small price of a hardware key is nothing compared to the near-ironclad security it provides.
Your personal 2FA setup is crucial, but you need to pair it with every security tool your exchange offers. These features add extra layers of defense that work hand-in-hand with your 2FA.
When you combine these practices—a dedicated 2FA device, hardware keys, and exchange-level controls—you’re building a comprehensive security ecosystem. This multi-layered approach ensures your portfolio is defended from every possible angle.
Let's be real—crypto security can feel like a minefield. You've probably got questions about using a crypto 2FA code, and that's smart. Here are some straightforward answers to the most common concerns we hear from traders.
This is the number one fear for most people, but it doesn't have to be a catastrophe. If you followed the right steps when you set it up, losing your phone is just an annoying hiccup, not a disaster.
The entire game comes down to your 2FA backup code. That's the long string of characters the exchange or wallet told you to save somewhere safe and offline. If your phone gets lost or fried, you just grab a new device, install your authenticator app, and look for an option like "enter setup key manually." Punch in that backup key, and your new app will sync up and start spitting out the correct codes. Problem solved.
But if you skipped saving that key? You’re in for a world of hurt, facing a long, painful support process with the exchange to prove you are who you say you are.
Yes, but it’s a whole lot tougher than just cracking a password. How a hacker might get around your 2FA depends entirely on which type you're using.
Putting all your 2FA codes into a single app like Authy or Google Authenticator is undeniably convenient. But you have to recognize that it also creates a massive single point of failure. If someone compromises that one device, they could potentially get into every single account tied to it.
A more paranoid—and more secure—approach is to diversify. Use your most secure method, like a hardware key, for the exchange holding most of your funds. Maybe you use an old, offline phone with an authenticator app just for your main cold wallet. Then, use your primary phone's app for less critical services. It's all about balancing convenience with your personal risk tolerance.
Without a doubt, yes. SMS 2FA is leaky and has well-known vulnerabilities like SIM swapping, but it's still way better than relying on a password alone.
Think of it this way: a password is one lock on your door. Adding SMS 2FA is like adding a second, albeit weaker, lock. It forces an attacker to jump through another hoop. While we can't stress enough how important it is to upgrade to an authenticator app or hardware key, starting with SMS is a thousand times better than leaving your door wide open.
Securing your crypto is the first step, but finding the next winning trade is the goal. Wallet Finder.ai turns on-chain data into actionable alpha by helping you track and mirror the strategies of the most profitable wallets in real-time. Start your 7-day trial and see what the smart money is doing. Discover winning wallets with Wallet Finder.ai.