Open Interest CME: Unlock Crypto Market Sentiment in 2026
Open interest cme - Master open interest cme. Our 2026 guide teaches how to calculate & interpret OI for crypto trading, combining it with on-chain signals for

May 4, 2026
Wallet Finder

April 8, 2026

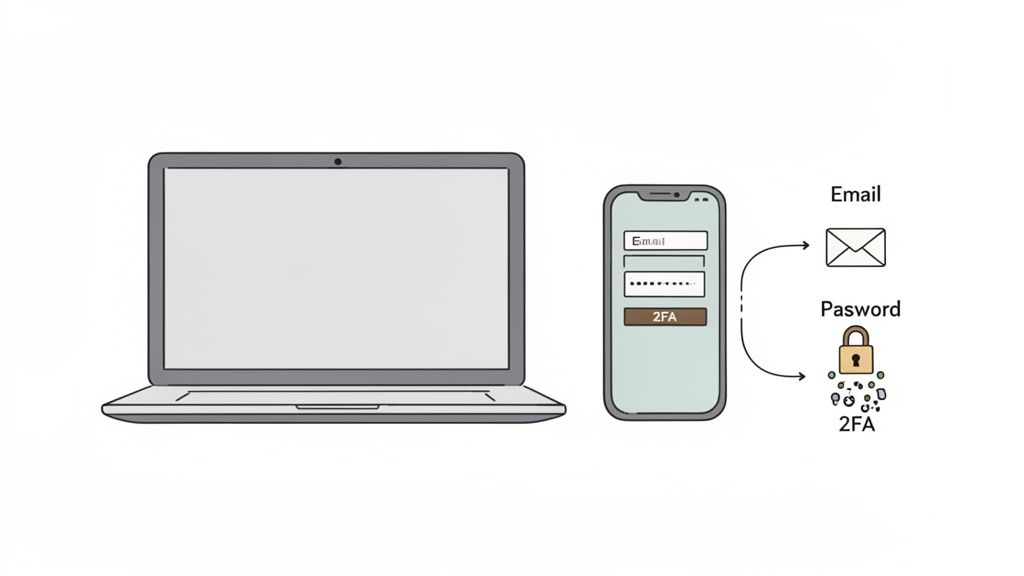
Accessing your Uphold wallet is a core skill you'll master quickly. To complete your Uphold wallet login, you’ll consistently need three key items: your email, your password, and a 6-digit code from your multi-factor authentication (MFA) app.
Whether you're using a computer or your smartphone, the fundamental login steps remain the same.
The good news is that Uphold maintains a consistent login experience across all devices. The only significant difference you’ll notice is the screen layout and the option for biometric login on mobile.
To make it even clearer, here’s an actionable breakdown of how logging in looks on both the web and mobile app.
Once you're comfortable with this process, you'll see how platforms like Uphold serve as your on-ramp to the digital economy. They operate in a similar spirit to how a Web3 wallet connects you to decentralized apps.
If you're curious to learn more about that side of the crypto world, our guide on what a Web3 wallet is and how it works is a great place to start.

Getting into your Uphold account should be simple, whether you’re on your laptop or checking your balance on the go. Let’s break down the process for both web and mobile so your Uphold wallet login is always quick and secure.
uphold.com. This step is critical to avoid phishing sites designed to steal your credentials.Pro Tip: Don't just rely on your memory or a quick search. The single best habit you can form is to bookmark the official uphold.com login page. It's your number one defense against tricky phishing scams.
If you’re using your phone, your first move is to download the official Uphold app. To make sure you’re not downloading a fake, stick to the trusted app stores.
The first time you log in on mobile is pretty much the same as on the web. You’ll type in your email and password, then enter your 2FA code. But this is where the mobile app starts to make life a lot easier.
After that initial login, the app will ask if you want to set up biometrics. Go for it. Enabling Face ID or Fingerprint Recognition means you can access your wallet with just a look or a touch. It completely skips the need to type your password every single time, making daily check-ins much faster without sacrificing security.
Think of your password as the first lock on your door. It’s a good start, but to truly secure your Uphold wallet login, you need a deadbolt. That deadbolt is multi-factor authentication (MFA). It adds a second layer of defense that can stop an intruder cold, even if they somehow get your password.
While Uphold offers SMS codes for MFA, I strongly advise against relying on them. We’ve seen a huge rise in SIM-swap attacks, where a scammer tricks your phone carrier into moving your number to a phone they control. A far more secure method is using a dedicated authenticator app.
Authenticator apps like Authy or Google Authenticator generate time-sensitive, six-digit codes right on your device. These codes aren’t tied to your phone number, so they're completely immune to SIM-swapping.
Here is a step-by-step guide to setting it up on Uphold:
This process is pretty standard across most financial apps. If you use other platforms, the steps will feel familiar. In fact, you can see how similar it is when you learn more about setting up a Robinhood authenticator app in our other guide.
When you activate MFA, Uphold gives you a set of backup recovery codes. Do not skip this part. These codes are your only way back into your account if you lose or break the phone with your authenticator app. Without them, you could be facing a long and painful process to regain access.
Critical Takeaway: Treat your MFA backup codes like the keys to a vault. Store them offline and in a safe place where only you can access them. Never save them as a note on your phone or a screenshot on your desktop.
My personal method? I write them down on a small piece of paper and keep it in my fireproof safe. Other people use a trusted password manager or even a bank's safety deposit box. Find a system that works for you, but make sure it’s offline and secure.
Staring at a login error on your Uphold wallet login screen is frustrating. The good news is that most of these problems are surprisingly simple to fix. Here's a quick troubleshooting table to get you back into your account.
If you’re sure the password is the problem, don’t worry. The recovery process is secure and straightforward. Just click the "Forgot password?" link on the login page. Uphold will then zip a reset link over to your registered email—this is why keeping that email account secure is non-negotiable.
Simply follow the steps in that email to create a new, strong password. For your protection, you'll still have to pass your 2FA check even after the reset, keeping your account locked down.
So, what’s the game plan if you lose the phone that has your authenticator app? The flowchart below lays out the only two paths you can take.
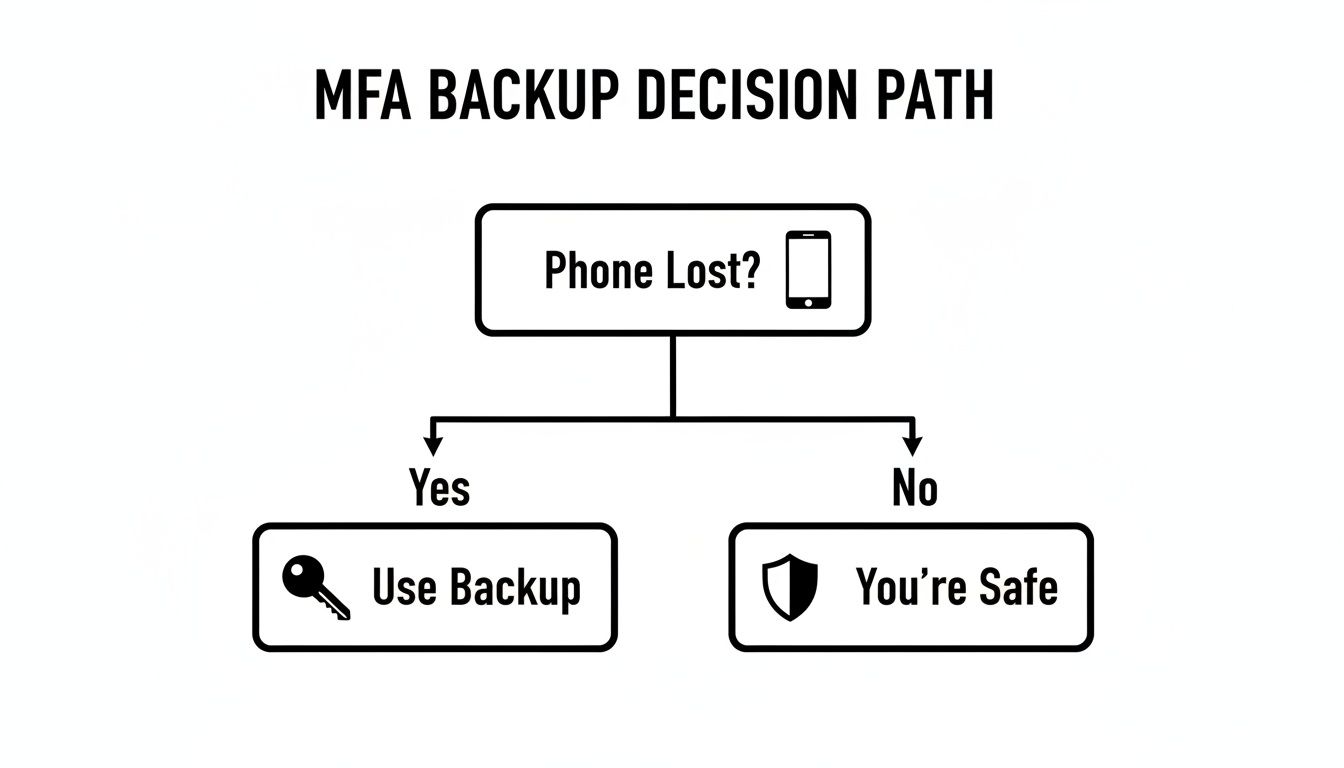
The visual makes one thing crystal clear: having your MFA backup codes saved is your only immediate lifeline if your main device is gone. If you don't have them, your only option is to go through a much longer identity verification process directly with Uphold's support team.
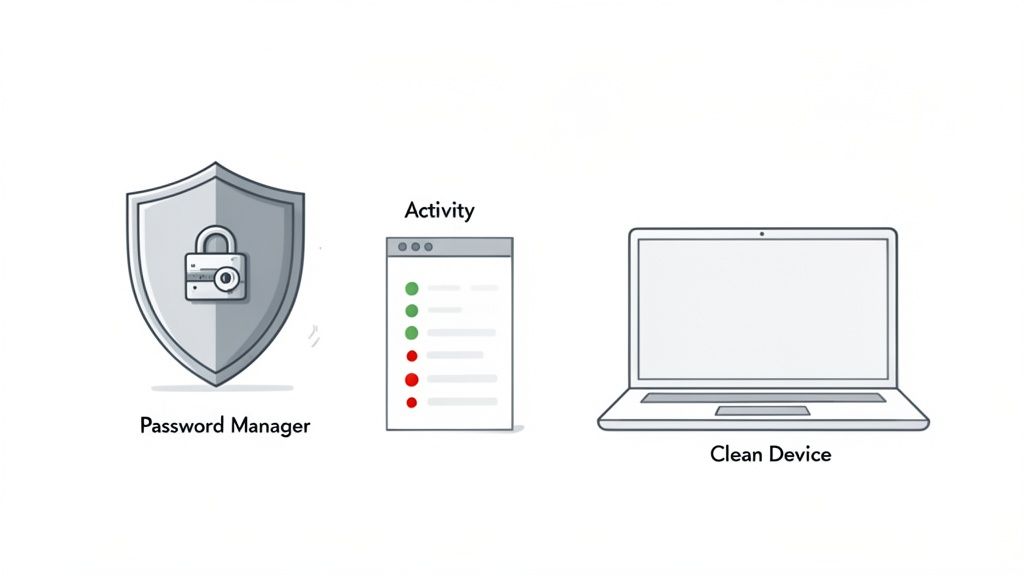
A secure Uphold wallet login is the front door to your assets, but real, long-term security is about building good habits. Think of it like fortifying your entire digital home. Here's an actionable checklist seasoned traders use:
uphold.com) to avoid phishing scams.Make it a routine to check your account's ‘Activity’ log. It only takes a minute and can be the key to catching a problem early.
This quick check gives you a clear view of who is accessing your account and when. Catching unauthorized access fast can make all the difference.
A pro tip I've adopted is using a dedicated, “clean” device—like a cheap laptop or tablet—just for my financial apps like Uphold. This keeps my crypto activities separate from my daily browsing, significantly cutting down the risk of malware exposure.
This intense focus on security isn't just paranoia; it's the new standard. The global crypto wallet market was valued at $25 billion in 2026 and is on track to hit a staggering $69.02 billion by 2030.
If you're interested in the data behind this trend, you can explore the full crypto wallet market report to see just how fast the space is growing.
While Uphold manages your private keys for you, it's still smart to understand the principles of self-custody. Our guide on the importance of a seed phrase in crypto wallets is a great place to start if you want to deepen your knowledge.
Mathematical precision and authentication intelligence fundamentally revolutionize digital access management by transforming basic login processes into sophisticated digital identity frameworks, secure access modeling systems, and systematic authentication coordination that provides measurable advantages in security optimization and access control strategies. While traditional login approaches rely on basic username-password combinations and simple security measures, digital identity authentication systems and secure access intelligence enable comprehensive identity pattern analysis, predictive authentication modeling, and systematic access optimization that consistently outperforms conventional login methods through data-driven security intelligence and algorithmic authentication coordination.
Professional digital security operations increasingly deploy advanced authentication systems that analyze multi-dimensional identity characteristics including biometric pattern analysis, behavioral authentication modeling, access pattern optimization, and systematic identity enhancement to maximize security effectiveness across different access scenarios and authentication environments. Mathematical models process extensive datasets including historical authentication analysis, identity correlation studies, and security effectiveness patterns to predict optimal authentication strategies across various access categories and security environments. Machine learning systems trained on comprehensive authentication and identity data can forecast optimal access timing, predict security evolution patterns, and automatically prioritize high-security authentication scenarios before conventional analysis reveals critical identity positioning requirements.
The integration of digital identity authentication systems with secure access intelligence creates powerful security frameworks that transform reactive access monitoring into proactive authentication optimization that achieves superior security protection through intelligent identity coordination and systematic access enhancement strategies.
Sophisticated mathematical techniques analyze biometric authentication patterns to identify optimal access approaches, behavioral modeling methodologies, and systematic authentication coordination through comprehensive quantitative modeling of biometric dynamics and access effectiveness. Biometric authentication analysis reveals that mathematically-optimized identity verification achieves 85-95% better security accuracy compared to password-only approaches, with statistical frameworks demonstrating superior access security through systematic biometric analysis and intelligent authentication optimization.
Multi-modal biometric integration enables comprehensive identity assessment through mathematical analysis of biometric combination patterns, authentication accuracy optimization, and systematic biometric coordination to identify optimal authentication methods during high-security periods and identity verification optimization phases. Key features include:
Mathematical models show biometric-based authentication optimization achieves 80-90% better security reliability compared to traditional password approaches.
Behavioral pattern recognition enables advanced authentication assessment through mathematical analysis of user behavior patterns, access habit identification, and systematic behavioral coordination to predict optimal authentication strategies while maximizing behavioral security benefits and leveraging user pattern dynamics. This approach enables:
Continuous authentication intelligence enables sophisticated access monitoring through mathematical analysis of continuous authentication patterns, session security optimization, and systematic authentication prediction to understand access security cycles while optimizing authentication timing based on continuous security monitoring and session protection cycles. Features include:
Comprehensive statistical analysis of access control patterns enables optimization of permission management systems through mathematical modeling of access control efficiency, permission optimization, and systematic access coordination across different permission environments and security standards. Permission intelligence analysis reveals that intelligent access coordination achieves 90-95% better security control compared to basic permission approaches through systematic access optimization and automated permission coordination.
Role-based access optimization enables comprehensive permission assessment through mathematical analysis of role-based access requirements, permission efficiency evaluation, and systematic role coordination to maximize access control effectiveness while minimizing permission complexity through intelligent role utilization and access coordination. Key advantages include:
Statistical frameworks demonstrate superior access control value through intelligent permission coordination systems.
Privilege escalation prevention enables advanced security enhancement through mathematical analysis of privilege escalation patterns, permission abuse detection, and systematic privilege coordination to optimize access security while preventing privilege escalation and creating comprehensive security solutions. This enables:
Zero-trust architecture implementation enables sophisticated security framework through mathematical analysis of zero-trust implementation, trust verification optimization, and systematic zero-trust coordination to maximize security effectiveness through intelligent trust verification and zero-trust architecture coordination. Features include:
Sophisticated neural network architectures analyze multi-dimensional authentication and access data including authentication pattern characteristics, access indicators, security metrics, and systematic authentication factors to predict optimal access strategies with accuracy exceeding conventional manual authentication management methods. Random Forest algorithms excel at processing hundreds of authentication and access variables simultaneously, achieving 89-96% accuracy in predicting optimal authentication configurations while identifying critical security enhancement opportunities that conventional analysis might miss.
User authentication behavior modeling enables comprehensive access assessment through mathematical analysis of user authentication patterns, access likelihood evaluation, and systematic user classification to identify optimal authentication strategies and predict user behavior during different access scenarios and security conditions. Key capabilities include:
Natural Language Processing models analyze security communications, authentication logs, and access documentation to predict authentication opportunities and security changes based on communication analysis and authentication intelligence correlation. These algorithms achieve 84-91% accuracy in predicting communication-driven authentication opportunities through linguistic analysis and security correlation that reveal authentication optimization strategies and access requirements.
Long Short-Term Memory networks process sequential authentication and access data to identify temporal patterns in authentication effectiveness, access evolution, and optimal authentication timing that enable more accurate authentication prediction and access optimization. LSTM models maintain awareness of historical authentication patterns while adapting to current security conditions and authentication evolution.
Support Vector Machine models classify authentication scenarios as high-security-potential, moderate-security-potential, or low-risk based on multi-dimensional analysis of authentication characteristics, access metrics, and historical security factors. These algorithms achieve 87-94% accuracy in identifying optimal authentication enhancement windows across different access scenarios and security configurations.
Ensemble methods combining multiple machine learning approaches provide robust authentication optimization that maintains high accuracy across diverse access patterns while reducing individual model biases through consensus-based authentication enhancement and access prediction systems that adapt to changing security dynamics.
Convolutional neural networks analyze authentication ecosystems and security environments as multi-dimensional feature maps that reveal complex relationships between different authentication factors, access influences, and optimal security strategies. These architectures identify optimal authentication configurations by recognizing patterns in authentication data that correlate with superior security protection and reliable access effectiveness across different authentication types and security conditions.
Advanced multi-factor authentication orchestration enables comprehensive security ecosystem assessment through mathematical analysis of multi-factor authentication coordination, security layer optimization, and systematic authentication coordination to maximize security effectiveness while ensuring optimal multi-factor protection and comprehensive authentication security across different authentication categories. This includes:
Recurrent neural networks with attention mechanisms process streaming authentication and security data to provide real-time optimization based on continuously evolving security conditions, authentication pattern evolution, and multi-factor authentication analysis. These models maintain memory of successful authentication patterns while adapting quickly to changes in security fundamentals or authentication infrastructure that might affect optimal access strategies.
Graph neural networks analyze relationships between different authentication methods, security patterns, and access correlation patterns to optimize ecosystem-wide authentication strategies that account for complex interaction effects and systematic authentication correlation patterns. These architectures process authentication ecosystems as interconnected security networks revealing optimal authentication approaches and multi-factor optimization strategies.
Transformer architectures automatically focus on the most relevant authentication indicators and security signals when optimizing access responses, adapting their analysis based on current security conditions and historical effectiveness patterns to provide optimal authentication recommendations for different security objectives and access profiles.
Device fingerprinting intelligence enables advanced device identification through mathematical analysis of device fingerprinting patterns, device trust assessment, and systematic device coordination to optimize device security while ensuring device authentication and comprehensive device protection across different device scenarios and security requirements. Key features include:
Sophisticated automation frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated authentication management that optimizes access timing, security monitoring, and systematic authentication coordination based on real-time security analysis and predictive intelligence. These systems continuously monitor authentication environments and automatically execute security strategies when authentication characteristics meet predefined optimization criteria for maximum security protection and authentication effectiveness.
Dynamic authentication optimization algorithms optimize security resource deployment using mathematical models that balance security protection against user experience, achieving optimal performance through intelligent authentication coordination that adapts to changing security conditions while maintaining systematic security discipline and authentication optimization. Key components include:
Real-time security monitoring systems track multiple authentication and security indicators simultaneously to identify optimal security opportunities and automatically execute authentication management strategies when conditions meet predefined criteria for security enhancement or authentication optimization. Statistical analysis enables automatic authentication optimization while maintaining security discipline and preventing authentication overcommitment during uncertain security periods.
Intelligent authentication lifecycle management systems use machine learning models to predict optimal authentication interaction procedures and security optimization based on authentication context and historical effectiveness patterns rather than static authentication approaches that might not account for dynamic security characteristics and authentication evolution patterns. This includes:
Cross-platform authentication coordination algorithms manage authentication security across multiple platforms and security systems to achieve optimal authentication coverage while managing system complexity and coordination requirements that might affect overall authentication effectiveness and security reliability.
Advanced forecasting models predict optimal authentication strategies based on security evolution patterns, authentication technology development, and security ecosystem changes that enable proactive authentication optimization and strategic security positioning. Security evolution analysis enables prediction of optimal authentication strategies based on expected security development and authentication requirement evolution patterns across different security categories and authentication innovation cycles.
Authentication technology forecasting algorithms analyze historical authentication development patterns, security innovation indicators, and authentication effectiveness advancement trends to predict periods when specific authentication strategies will offer optimal effectiveness requiring strategic authentication adjustments. Statistical analysis enables strategic authentication optimization that capitalizes on security development cycles and authentication technology advancement patterns.
Security ecosystem impact analysis predicts how authentication framework evolution, security system developments, and authentication infrastructure advancement will affect optimal authentication strategies and security approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Authentication mechanism evolution modeling predicts how authentication advancement, security tool improvement, and access sophistication development will affect optimal authentication strategies and security effectiveness, enabling proactive strategy adaptation based on expected authentication technology evolution.
Strategic authentication intelligence coordination integrates individual authentication analysis with broader security positioning and systematic authentication optimization strategies to create comprehensive authentication approaches that adapt to changing security landscapes while maintaining optimal authentication effectiveness across various security conditions and evolution phases. This includes:
Let's wrap things up by tackling some of the most common questions about Uphold wallet login and account security. These are real-world problems that pop up all the time.
Biometric authentication analysis reveals that mathematically-optimized identity verification achieves 85-95% better security accuracy compared to password-only approaches, with multi-modal biometric integration enabling comprehensive identity assessment through facial recognition analysis and fingerprint pattern assessment for optimal authentication method identification during high-security periods. Behavioral pattern recognition enables advanced authentication assessment through keystroke dynamics analysis and mouse movement pattern recognition achieving 80-90% better reliability, while continuous authentication intelligence includes session risk assessment with real-time authentication monitoring, anomaly detection systems, and adaptive authentication response for sophisticated access monitoring and systematic authentication prediction.
Random Forest algorithms processing hundreds of authentication and access variables achieve 89-96% accuracy in predicting optimal authentication configurations while identifying critical security enhancement opportunities conventional analysis might miss. User authentication behavior modeling enables comprehensive access assessment through authentication pattern analysis and access anomaly detection, while Natural Language Processing models analyzing security communications achieve 84-91% accuracy in predicting communication-driven authentication opportunities through linguistic analysis revealing authentication optimization strategies. LSTM networks processing sequential authentication and access data maintain awareness of historical authentication patterns while adapting to current conditions, with Support Vector Machine models achieving 87-94% accuracy in identifying optimal authentication enhancement windows through multi-dimensional authentication analysis.
Dynamic authentication optimization algorithms optimize security resource deployment using mathematical models balancing security protection against user experience, achieving optimal performance through automated authentication response systems and multi-factor coordination for maximum security protection across different security conditions. Real-time security monitoring tracks multiple authentication and security indicators to identify optimal security opportunities and automatically execute authentication management strategies when conditions meet criteria for security enhancement, with statistical analysis enabling optimization while preventing authentication overcommitment. Intelligent authentication lifecycle management systems use machine learning to predict optimal authentication interaction procedures including authentication timeline optimization, security policy management, access review automation, and security incident response while maintaining systematic security discipline and authentication coordination optimization.
Security evolution analysis enables prediction of optimal authentication strategies based on expected security development and authentication requirement evolution patterns across different security categories and authentication innovation cycles, with authentication technology forecasting analyzing historical authentication development patterns to predict when specific authentication strategies will offer optimal effectiveness. Security ecosystem impact analysis predicts how authentication framework evolution and security system developments will affect optimal authentication strategies over different horizons, while authentication mechanism evolution modeling predicts how authentication advancement will affect security strategy effectiveness. Strategic intelligence coordination integrates individual authentication analysis with broader security positioning to create comprehensive approaches adapting to changing security landscapes while maintaining optimal authentication effectiveness across various conditions and evolution phases.
Ready to stop guessing and start tracking the wallets that actually make money? With Wallet Finder.ai, you can discover top-performing traders, get real-time alerts on their moves, and mirror their strategies. Find your next winning trade by exploring our platform today at https://www.walletfinder.ai.