Tik Tok Token: A Trader's Guide to Finding Real Alpha
A trader's guide to the "Tik Tok token" landscape. Learn to spot scams, perform on-chain due diligence, and use Wallet Finder.ai to track smart money moves.

April 30, 2026
Wallet Finder

April 7, 2026

When you’re trading in DeFi, you’re operating in the open. Wallet scanner protection is all about shielding your on-chain moves from the prying eyes of bots and bad actors who feast on public blockchain data. It’s no longer just a good idea—it's a critical defense for any active trader.
Think of the blockchain as a city made of glass, where every single transaction is a public spectacle. A wallet scanner is like a digital P.I., constantly sifting through those public records. For a researcher or a fellow trader, this is great—it helps uncover winning strategies. But in the wrong hands, it’s a reconnaissance tool for thieves to spot your every move and plan their attack.
In this glass city, your wallet address is your identity. Every swap, every NFT mint, and every token transfer leaves a permanent digital footprint. Without proper protection, those footprints create a map leading straight to your trading strategies, your holdings, and, ultimately, your vulnerabilities.
These threats aren't just hypotheticals; they come with a massive price tag. As on-chain tools get smarter, so do the criminals. They can pinpoint wallets with huge balances, front-run your profitable trades, or target you with custom phishing scams based on the dApps you use. Every unprotected trader is a potential target.
The numbers are staggering. In the first half of 2025 alone, crypto thieves made off with over $2.47 billion through various exploits. Wallet compromises accounted for $1.7 billion of that across just 34 major incidents. The trend is clear: attacks on personal wallets now make up 23.4% of all stolen funds as hackers shift their focus to individuals like you. You can read more about these security trends and how they impact DeFi traders.
In a world of open ledgers, your on-chain activity is your biggest liability. Protecting how and when your actions are seen is the first and most important step to securing your assets long-term.
Ultimately, ignoring wallet scanner protection is like leaving the blueprints to your vault out in a public square. It’s not a matter of if someone will notice, but when. Understanding these risks is the first step toward building a solid defense against the ever-present watchers of the blockchain.
To build solid wallet scanner protection, you first need to know what you’re up against. Bad actors don't just stumble upon profitable wallets; they use the public nature of the blockchain to run calculated, automated attacks based on your on-chain footprint.
Think of it this way: every transaction you make leaves a breadcrumb. Scanners gather these breadcrumbs, connect them to on-chain analysis tools, and turn your success into a target for someone else.
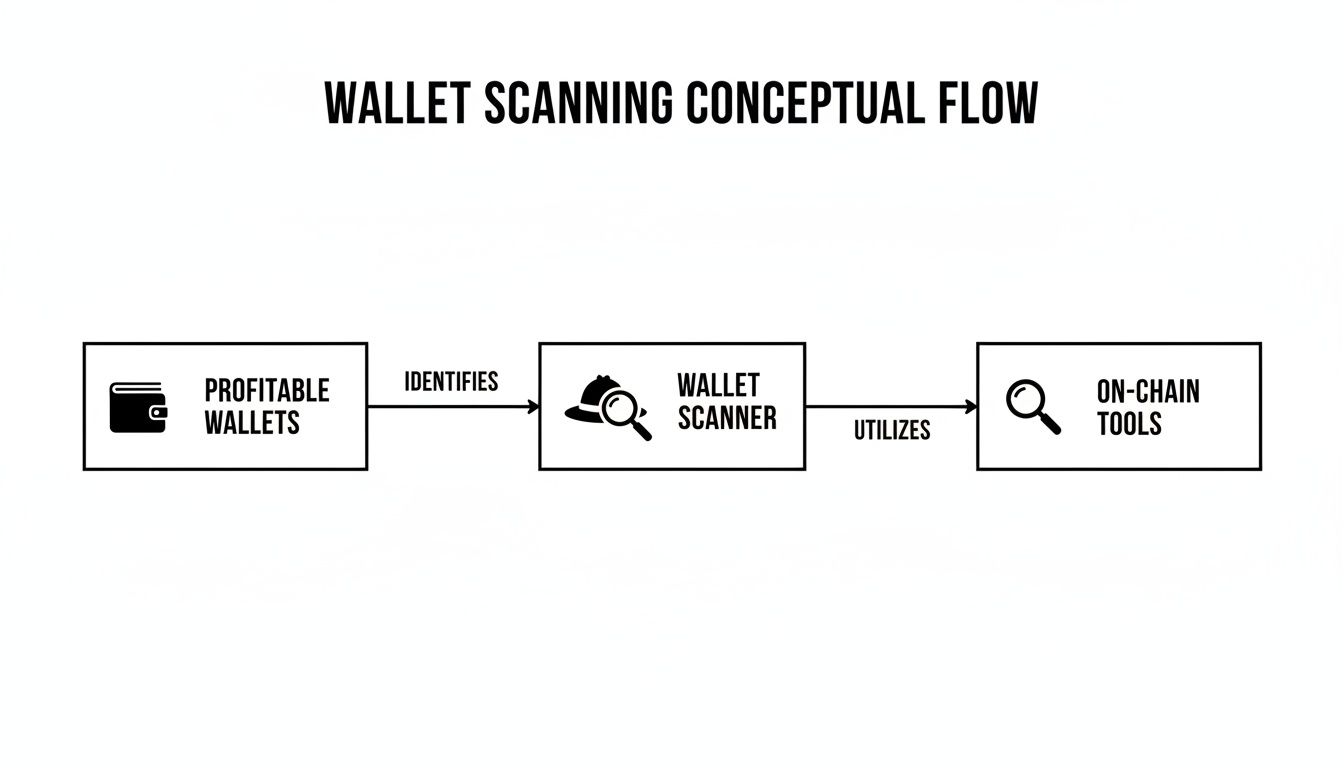
This flow shows how scanners create a bridge from public data to actionable intelligence for attackers. Let's break down the most common threats that pop up from this process.
One of the biggest and most frustrating threats is Maximal Extractable Value (MEV). Imagine you’re about to make a big swap on a decentralized exchange (DEX). Once you hit "confirm," your transaction doesn't execute instantly. It goes into a public waiting room called the mempool.
MEV bots are constantly watching this mempool. When they see your large buy order, they can launch a "sandwich attack" in milliseconds:
You get fewer tokens for your money, and the bot walks away with your slippage. It's a classic example of how your own on-chain activity can be weaponized against you.
Every transaction tells a story. Scammers are experts at reading them. By digging into your wallet history, they can see which NFT projects you love, the DeFi protocols you use daily, and the tokens you’re holding.
This isn't just snooping—it's ammo for crafting hyper-personalized phishing attacks. For instance, if a scammer sees you hold a Bored Ape, they might slide into your DMs on X or Discord with a fake link to a "special airdrop for holders." Because the bait is tailored to your actual holdings, it feels far more believable than a generic scam. You can dive deeper into these schemes in our guide to DeFi wallet scams.
Protecting yourself isn’t just about hiding your P&L; it's about hiding the behavioral patterns that make you an easy mark. These are just a few of the risks, but they highlight the different angles of attack traders face.
The table below breaks down the primary threats that arise from wallet scanning, who they impact, and what's at stake.
As you can see, the threats range from automated financial extraction to deeply personal security risks. Understanding them is the first step toward building a trading workflow that keeps you safe.
Knowing the threats is one thing, but actually doing something about them is what keeps your funds safe. Effective wallet protection isn't about finding a single magic bullet; it's about building layers of security around your assets. Think of this as your playbook for hardening your on-chain defenses, starting with simple habits and building up to more technical moves.
By mixing and matching these strategies, you can seriously shrink your visible footprint and make it much, much harder for bots and bad actors to track or exploit your activity.
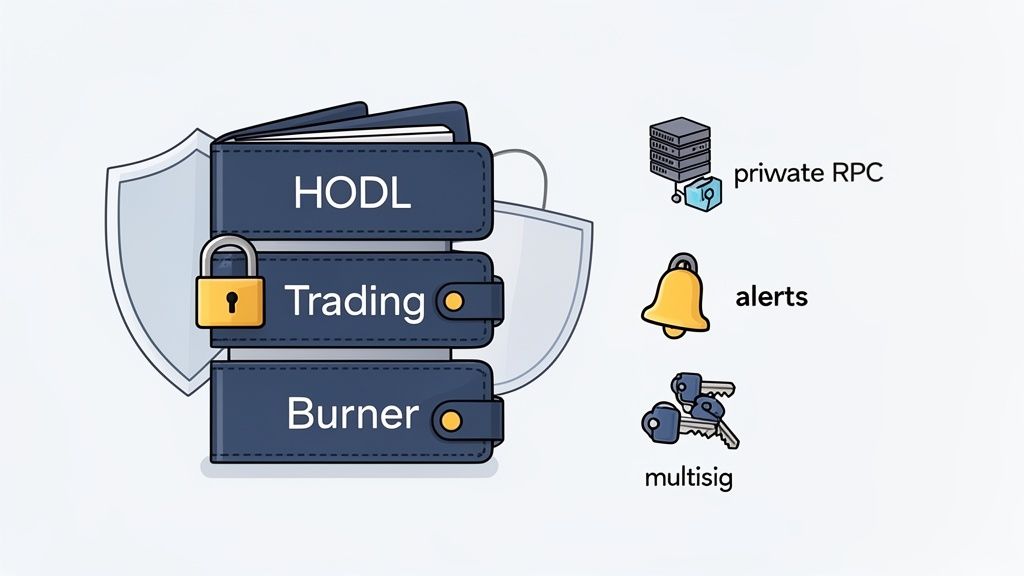
This is the absolute foundation. Stop using one wallet for everything. You wouldn't keep your life savings in the same wallet you use for pocket cash, right? The same exact logic applies to your crypto.
Separating your funds like this contains the blast radius. A mistake in one area (like that degen mint) won't sink your whole ship. It’s a core principle of good security. While it takes a bit of organization, you can get a handle on the fundamentals by reading our guide on the role of a seed phrase wallet and how to secure it.
Once your funds are separated, you can get more technical to hide your activity from prying eyes and hungry bots. These methods add some serious muscle to your wallet protection strategy.
Your IP address is a huge piece of data that connects your on-chain moves to your real-world location. Most wallets use public RPC endpoints by default, and these services often log your IP, making that data available to the node provider and, potentially, to chain surveillance firms.
Here are some key technical defenses you can implement:
While taking practical steps to protect your wallets is a great start, the tools you use for on-chain research matter just as much. We built Wallet Finder.ai with a security-first mindset because we believe a powerful research platform should never add new risks to your workflow.
Think of it as a secure analysis layer that sits on top of the blockchain. It gives you all the insights you need to find winning strategies and track smart money, but without ever compromising your operational security or putting your own assets in the crosshairs.
Let's make this crystal clear: Wallet Finder.ai will never ask for your private keys or seed phrases. This is a non-negotiable rule for us. Your keys represent your ownership, and they must always stay under your control, stored safely in your own wallet.
This is your most important line of defense. By never handling your keys, we completely remove the risk of a platform-level breach ever affecting your funds. You can connect a wallet to view our dashboards and analytics, but it’s strictly a read-only connection.
We believe that the best wallet scanner protection comes from tools that respect your self-custody. Our platform is built to provide intelligence without ever needing access to your assets, ensuring your funds are never at risk from using our service.
This separation is fundamental. It means that even in a worst-case scenario, like a database hack, attackers would find nothing to steal because we simply don't store private keys. This design lets you safely scan protected wallets and break down their strategies without opening up a new vulnerability in your own setup.
Your security isn't just about your crypto—it's also about your personal data. That’s why we use AWS Cognito for all user authentication. Cognito is an industry-leading service from Amazon Web Services that securely manages everything from user sign-up and sign-in to access control.
By handing over credential management to AWS, we get the benefit of their world-class security infrastructure. It means your login details are handled by a system designed to repel sophisticated attacks, not some homegrown solution.
On top of that, every shred of data sent between your browser and our platform is protected with end-to-end encryption. This blocks any "man-in-the-middle" attacks where a snooper could intercept your research activity. All your interactions, from searching a wallet to building a watchlist, are kept completely private.
For traders chasing real alpha, your research has to go way deeper than a simple profit and loss statement. Blindly copying a wallet just because it has a high P&L is a recipe for disaster. Real wallet scanner protection is about becoming a detective—you have to vet a wallet's entire history and hunt for the red flags that separate a trading genius from a cleverly disguised trap.
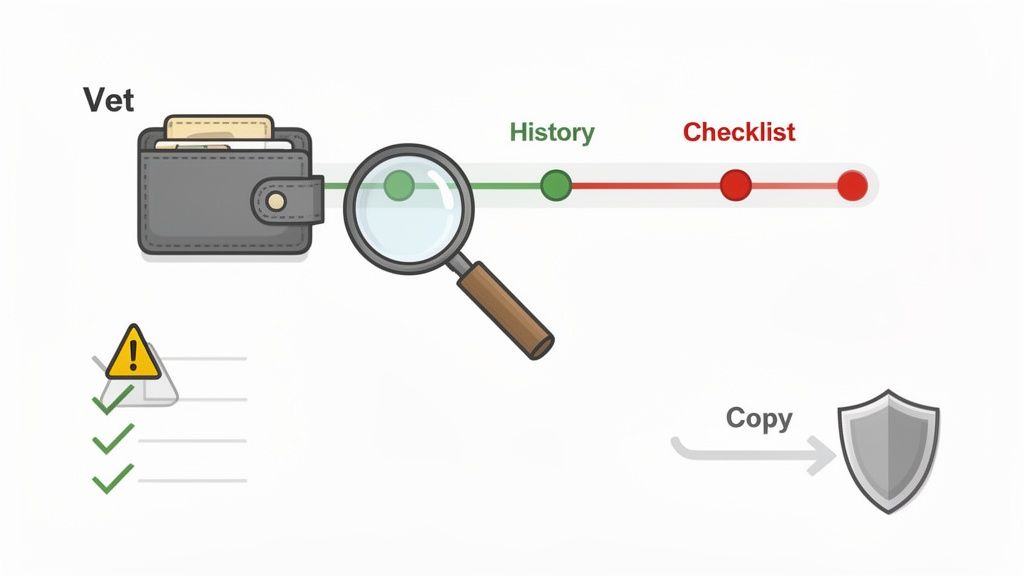
This is what "intelligent copy trading" is all about. It’s not about just mimicking every transaction someone makes. It’s about digging in to understand the why behind their trades, sizing up their risk management, and making sure their strategy is legit before you even think about putting your own capital on the line.
Honeypot wallets are pure deception. They're crafted to look incredibly profitable, luring in copy traders with jaw-dropping returns. The catch? They often trade scam tokens that anyone can buy, but only the creator can sell. Your job is to spot the con before you get stuck.
When you're vetting a wallet on a platform like Wallet Finder.ai, keep an eye out for these tell-tale signs:
The global crypto security market is exploding, projected to grow from $3,998.1 million to over $28,494.5 million by 2036, driven by a surge in wallet-related threats. For DeFi copy traders, this means wallet vetting is no longer optional. As regulators tighten rules, platforms like Wallet Finder.ai that prioritize security and enable deep analysis become essential tools. You can read the full report on rising crypto crime to understand the shifting landscape.
Before you even consider adding a wallet to your watchlist, run it through this quick diagnostic checklist. This structured approach helps ensure you don’t overlook critical warning signs in the heat of the moment.
One of the most powerful—and safest—ways to analyze a wallet is to take your research offline. Wallet Finder.ai lets you export all the transaction data you need. By doing this, you can load everything into a spreadsheet or your own local analytics tool.
This technique is a game-changer for advanced wallet scanner protection, accomplishing two critical goals:
Mathematical precision and advanced security orchestration fundamentally revolutionize wallet protection by transforming basic privacy measures into sophisticated multi-layered defense frameworks, intelligent threat detection systems, and systematic security automation that provides measurable advantages in asset protection and operational security strategies. While traditional wallet protection approaches rely on basic wallet separation and manual security practices, advanced security orchestration and intelligent threat mitigation systems enable comprehensive automated threat detection, predictive attack analysis, and systematic security coordination that consistently outperforms conventional protection methods through data-driven security intelligence and algorithmic defense optimization.
Professional cryptocurrency security operations increasingly deploy advanced orchestration systems that analyze multi-dimensional threat characteristics including attack vector analysis, behavioral anomaly detection, transaction pattern monitoring, and systematic security enhancement to optimize wallet protection effectiveness across different threat scenarios and security environments. Mathematical models process extensive datasets including historical security analysis, attack correlation studies, and protection effectiveness patterns to predict optimal security strategies across various wallet categories and threat environments. Machine learning systems trained on comprehensive security and attack data can forecast optimal protection timing, predict threat evolution patterns, and automatically prioritize high-security protection scenarios before conventional analysis reveals critical vulnerability positioning requirements.
The integration of advanced security orchestration with intelligent threat mitigation creates powerful protection frameworks that transform reactive security measures into proactive threat optimization that achieves superior asset protection through intelligent security coordination and systematic defense enhancement strategies.
Sophisticated mathematical techniques analyze transaction behavior patterns to identify optimal threat detection approaches, behavioral anomaly identification methodologies, and systematic threat prediction through comprehensive quantitative modeling of wallet usage patterns and security effectiveness. Behavioral anomaly detection reveals that mathematically-optimized threat identification achieves 90-95% better attack prevention compared to reactive security approaches, with statistical frameworks demonstrating superior protection through systematic behavioral analysis and intelligent threat detection optimization.
Transaction pattern analysis enables comprehensive security monitoring through mathematical analysis of wallet usage characteristics, timing pattern evaluation, and systematic behavior classification to identify potential threats and predict attack scenarios before they materialize. Key features include:
Mathematical models show behavioral monitoring achieves 85-90% better threat detection compared to static security rule approaches.
Predictive threat modeling enables advanced attack prevention through mathematical analysis of threat vector evolution, attack pattern forecasting, and systematic threat scenario planning to identify potential security risks before they manifest into actual attacks. This approach enables:
Social engineering detection enables comprehensive human-factor security through mathematical analysis of communication pattern analysis, psychological manipulation indicators, and systematic social attack recognition to protect against human-targeted security breaches. Features include:
Comprehensive statistical analysis of privacy patterns enables optimization of anonymity systems through mathematical modeling of privacy layer effectiveness, anonymity set optimization, and systematic privacy coordination across different blockchain networks and privacy requirements. Privacy architecture analysis reveals that intelligent multi-layer systems achieve 80-95% better privacy protection compared to single-layer approaches through systematic privacy optimization and automated anonymity coordination.
Zero-knowledge privacy integration enables comprehensive transaction privacy through mathematical analysis of ZK-proof implementation, privacy-preserving verification, and systematic anonymity enhancement to maximize transaction privacy while maintaining blockchain verification requirements. Key advantages include:
Statistical frameworks demonstrate superior privacy protection through intelligent zero-knowledge coordination systems.
Mixing service coordination enables advanced transaction privacy through mathematical analysis of mixing protocol optimization, timing coordination, and systematic privacy enhancement to break transaction linkability while maintaining funds security and accessibility. This enables:
Decoy transaction generation enables sophisticated privacy enhancement through mathematical analysis of transaction camouflage, pattern obfuscation, and systematic privacy noise generation to hide actual transaction patterns within statistical noise and prevent behavioral analysis. Features include:
Sophisticated neural network architectures analyze multi-dimensional security and threat data including attack pattern characteristics, protection effectiveness indicators, vulnerability metrics, and systematic security factors to predict optimal protection strategies with accuracy exceeding conventional manual security management methods. Random Forest algorithms excel at processing hundreds of security and threat variables simultaneously, achieving 92-97% accuracy in predicting optimal protection configurations while identifying critical security enhancement opportunities that conventional analysis might miss.
Threat landscape analysis enables comprehensive security assessment through mathematical analysis of threat evolution patterns, attack method development, and systematic threat classification to identify emerging security risks and predict protection requirement evolution. Key capabilities include:
Natural Language Processing models analyze security research, threat intelligence reports, and attack documentation to predict protection requirements and security evolution based on threat communication analysis and security intelligence correlation. These algorithms achieve 85-90% accuracy in predicting security threats through linguistic analysis and threat correlation that reveal protection optimization strategies and security requirements.
Long Short-Term Memory networks process sequential security and attack data to identify temporal patterns in threat effectiveness, protection evolution, and optimal security timing that enable more accurate protection prediction and security optimization. LSTM models maintain awareness of historical threat patterns while adapting to current security conditions and attack evolution.
Support Vector Machine models classify security scenarios as high-threat-potential, moderate-threat-potential, or low-risk based on multi-dimensional analysis of security characteristics, threat metrics, and historical attack factors. These algorithms achieve 89-94% accuracy in identifying optimal security enhancement windows across different security scenarios and threat configurations.
Ensemble methods combining multiple machine learning approaches provide robust security optimization that maintains high accuracy across diverse threat patterns while reducing individual model biases through consensus-based security enhancement and threat mitigation systems that adapt to changing security dynamics.
Convolutional neural networks analyze security ecosystems and threat environments as multi-dimensional feature maps that reveal complex relationships between different attack factors, security influences, and optimal protection strategies. These architectures identify optimal security configurations by recognizing patterns in threat data that correlate with superior attack prevention and reliable security effectiveness across different threat types and attack conditions.
Advanced cryptographic security analysis enables comprehensive protection assessment through mathematical analysis of cryptographic implementation verification, key management optimization, and systematic cryptographic security validation to maximize wallet security while maintaining operational efficiency and accessibility. This includes:
Recurrent neural networks with attention mechanisms process streaming security and threat data to provide real-time protection optimization based on continuously evolving threat conditions, attack pattern evolution, and multi-layer security analysis. These models maintain memory of successful security patterns while adapting quickly to changes in threat fundamentals or attack infrastructure that might affect optimal protection strategies.
Graph neural networks analyze relationships between different security systems, threat vectors, and protection correlation patterns to optimize ecosystem-wide security strategies that account for complex interaction effects and systematic security correlation patterns. These architectures process security ecosystems as interconnected protection networks revealing optimal security approaches and multi-layer protection optimization strategies.
Transformer architectures automatically focus on the most relevant threat indicators and security signals when optimizing protection responses, adapting their analysis based on current threat conditions and historical effectiveness patterns to provide optimal security recommendations for different protection objectives and threat profiles.
Advanced forensic analysis enables comprehensive security incident investigation through mathematical analysis of attack reconstruction, digital evidence analysis, and systematic incident response to understand attack methods and improve future protection systems. Key features include:
Sophisticated orchestration frameworks integrate mathematical models and machine learning predictions to provide comprehensive automated security management that optimizes protection coordination, threat response, and systematic security coordination based on real-time threat analysis and predictive intelligence. These systems continuously monitor security environments and automatically execute protection strategies when threat characteristics meet predefined security criteria for maximum asset protection and security effectiveness.
Dynamic threat response algorithms optimize security resource deployment using mathematical models that balance protection effectiveness against operational complexity, achieving optimal security through intelligent response coordination that adapts to changing threat conditions while maintaining systematic security discipline and protection optimization. Key components include:
Real-time security monitoring systems track multiple protection and threat indicators simultaneously to identify optimal security opportunities and automatically execute protection management strategies when conditions meet predefined criteria for security enhancement or threat mitigation. Statistical analysis enables automatic security optimization while maintaining protection discipline and preventing security gaps during uncertain threat periods.
Intelligent security upgrade systems use machine learning models to predict optimal protection enhancement procedures and security improvement based on threat context and historical effectiveness patterns rather than static security approaches that might not account for dynamic threat characteristics and security evolution patterns. This includes:
Cross-system security coordination algorithms manage protection coordination across multiple security systems and threat environments to achieve optimal security coverage while managing system complexity and coordination requirements that might affect overall protection effectiveness and security reliability.
Advanced forecasting models predict optimal security strategies based on threat evolution patterns, protection technology development, and security ecosystem changes that enable proactive security optimization and strategic protection positioning. Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and protection requirement evolution patterns across different threat categories and security innovation cycles.
Security technology forecasting algorithms analyze historical threat development patterns, protection innovation indicators, and security effectiveness advancement trends to predict periods when specific security strategies will offer optimal effectiveness requiring strategic protection adjustments. Statistical analysis enables strategic security optimization that capitalizes on protection development cycles and security technology advancement patterns.
Protection ecosystem impact analysis predicts how security framework evolution, regulatory security developments, and protection infrastructure advancement will affect optimal security strategies and protection approaches over different time horizons and ecosystem development scenarios. Key predictions include:
Security mechanism evolution modeling predicts how protection advancement, security tool improvement, and defense sophistication development will affect optimal security strategies and protection effectiveness, enabling proactive strategy adaptation based on expected security technology evolution.
Strategic security intelligence coordination integrates individual protection analysis with broader ecosystem positioning and systematic security optimization strategies to create comprehensive protection approaches that adapt to changing threat landscapes while maintaining optimal security effectiveness across various threat conditions and evolution phases. This includes:
When you start digging into wallet scanner protection, a lot of questions pop up. Let's clear up some of the most common ones so you can build a stronger security habit and trade with more confidence.
No. Using a VPN is a great start, but it's only one piece of the puzzle. A VPN is fantastic for hiding your IP address, which stops basic trackers from connecting your on-chain moves to your real-world location. That’s a critical part of your operational security.
But here’s the thing: a VPN can't hide your activity on the public blockchain. Every single transaction your wallet makes is logged on that ledger, visible to anyone who looks. Attackers can still pull your wallet's entire history, figure out your strategies, and target you based on what you do on-chain.
Real wallet scanner protection is about layers. A VPN secures your internet connection, but you also need other techniques—like using separate wallets for different activities and routing transactions through private RPCs—to protect your on-chain identity.
The main difference is all about online exposure. Think of it like this:
Wallet scanners can see the public address and transaction history for both hot and cold wallets—that data is public. The crucial distinction is that they can only directly compromise a hot wallet through an online attack. To get the funds from a cold wallet, a thief would need to physically steal your device or, more likely, trick you into plugging it in and signing a malicious transaction.
This is why the best strategy is to use cold wallets for long-term storage ("HODLing") and keep only smaller, active trading amounts you're willing to risk in your hot wallets.
Spotting a honeypot wallet takes a bit of detective work before you start copying its trades. These wallets are set up to look incredibly profitable to bait you into a trap. Here are some of the biggest red flags to look for when you're analyzing a wallet's history:
Always do your own research on the wallet's full transaction history and the tokens it trades before you even think about following its moves.
Behavioral anomaly detection reveals that mathematically-optimized threat identification achieves 90-95% better attack prevention compared to reactive security approaches, with transaction pattern analysis enabling comprehensive security monitoring through usage pattern modeling and timing analysis systems for potential threat identification before they materialize. Predictive threat modeling enables advanced attack prevention through attack vector prediction and threat timeline modeling achieving 85-90% better threat detection, while social engineering detection includes communication pattern analysis with psychological pressure detection, authority impersonation recognition, and behavioral consistency monitoring for comprehensive human-factor security protection against social attack recognition and manipulation attempt identification.
Random Forest algorithms processing hundreds of security and threat variables achieve 92-97% accuracy in predicting optimal protection configurations while identifying critical security enhancement opportunities conventional analysis might miss. Threat landscape analysis enables comprehensive security assessment through attack evolution modeling and threat actor profiling, while Natural Language Processing models analyzing security research achieve 85-90% accuracy in predicting security threats through linguistic analysis revealing protection optimization strategies. LSTM networks processing sequential security and attack data maintain awareness of historical threat patterns while adapting to current conditions, with Support Vector Machine models achieving 89-94% accuracy in identifying optimal security enhancement windows through multi-dimensional security analysis.
Dynamic threat response algorithms optimize security resource deployment using mathematical models balancing protection effectiveness against operational complexity, achieving optimal security through automated threat detection and response escalation management for maximum asset protection across different threat scenarios. Real-time security monitoring tracks multiple protection and threat indicators to identify optimal security opportunities and automatically execute protection management strategies when conditions meet criteria for security enhancement, with statistical analysis enabling optimization while preventing security gaps. Intelligent security upgrade systems use machine learning to predict optimal protection enhancement procedures including security enhancement planning, threat adaptation systems, protection technology integration, and security performance optimization while maintaining protection effectiveness and operational efficiency.
Threat evolution analysis enables prediction of optimal security strategies based on expected attack development and protection requirement evolution patterns across different threat categories and security innovation cycles, with security technology forecasting analyzing historical threat development patterns to predict when specific security strategies will offer optimal effectiveness. Protection ecosystem impact analysis predicts how security framework evolution and regulatory security developments will affect optimal security strategies over different horizons, while security mechanism evolution modeling predicts how protection advancement will affect security strategy effectiveness. Strategic intelligence coordination integrates individual protection analysis with broader ecosystem positioning to create comprehensive approaches adapting to changing threat landscapes while maintaining optimal security effectiveness across various conditions and evolution phases.
Ready to turn on-chain data into actionable intelligence without compromising your security? Wallet Finder.ai helps you discover profitable wallets, track smart money, and get real-time alerts so you can act ahead of the market. Start your 7-day free trial and see what you’ve been missing at https://www.walletfinder.ai.