Chain Trade Size Chart: Spot Smart Money Moves
Master the on-chain trade size chart to analyze market structure and copy trade with precision. Learn to build and read charts with Wallet Finder.ai.

May 24, 2026
Wallet Finder

February 23, 2026

Think of a website security audit as a deep-dive health check for your entire web application, servers, and anything connected to them. The goal is simple: find the security holes before an attacker does. It's a mix of smart automated scanning and hands-on manual testing to pinpoint weaknesses, figure out how bad they are, and give you a clear plan to shore up your defenses. This isn't just a "nice-to-have"—it's your frontline defense against breaches.
In the high-stakes world of DeFi and FinTech, trust isn't just a marketing buzzword; it's the bedrock of your entire business. One security slip-up can do more than just cause a massive financial loss—it can instantly vaporize years of credibility you've worked so hard to build. That’s why a proactive security audit for your website goes beyond a simple tech task. It’s a core business function.
Modern web apps, especially those juggling financial data or user logins, are incredibly complex. They have countless potential entry points for attackers, from an overlooked software dependency that's out of date to subtle flaws in your own business logic. Every single component is a potential vulnerability waiting to be found.
Hackers aren't just gunning for the big fish anymore. In fact, many see smaller, fast-moving platforms as low-hanging fruit. This is especially true for DeFi trackers and FinTech SaaS products that manage sensitive, high-value data.
Here are some key statistics that highlight the modern threat landscape:
A proper audit gives you a clear roadmap to securing your platform. It’s not about just running a quick scan; it's about getting a complete, 360-degree view of your security.
Before we get into the step-by-step process, let's break down the most critical components of any website audit. This table gives you a quick snapshot of what we'll be covering.
This isn't an exhaustive list, but it covers the foundational pillars of web security that every audit must address. Getting these right is non-negotiable.
A security audit is like a full-body scan for your website. It’s not just about checking if the front door is locked; it's about examining every window, testing every internal door, and verifying the alarm system works as intended.
Ultimately, performing regular security audits is about making a crucial shift from being reactive to proactive. Instead of waiting for a breach to happen and then scrambling to fix the damage, you're actively hunting for weaknesses on your own terms. This gives you the power to fix them before they can ever be exploited, protecting your users, your data, and the future of your business.
Before you run a single scan or write a line of code, you have to answer a simple question: what are you actually protecting? A successful security audit starts with a well-defined scope. Without that clear map, you’ll just be spinning your wheels, wasting time on low-priority areas while your most valuable assets are left wide open.
Think of your website as more than just a single entity. It’s a whole network of interconnected components, and each piece carries a different level of risk. Your first job is to create an exhaustive inventory that leaves no digital stone unturned.
This is the basic flow every audit should follow.
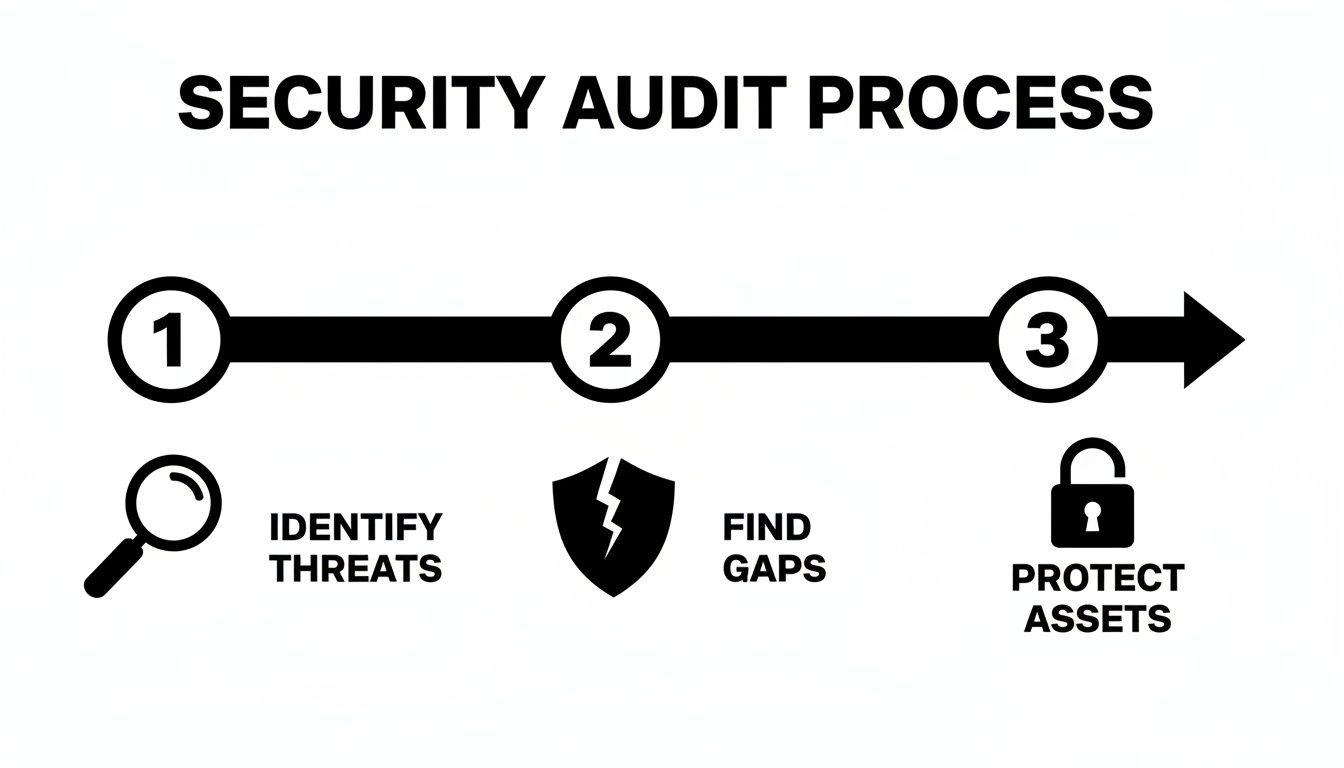
As you can see, protecting your assets is the last step. It all starts with the foundational work of identifying threats and finding the existing security gaps.
The first part of scoping your audit is to identify every single asset tied to your web application. This isn't just about your main domain name; it's a deep dive into your entire digital infrastructure. A thorough inventory is the only way to eliminate "shadow IT"—those unmanaged assets that create the perfect blind spots for attackers.
Your asset list should document:
A common mistake I see all the time is teams focusing only on the production website. A compromised staging server with old credentials or unpatched software can give an attacker an easy backdoor into your main systems. Treat every single environment as if it were live.
Once you know what you have, you need to understand how it all fits together. Tracing data flows is absolutely critical for figuring out where sensitive information is stored, processed, and transmitted. This process reveals the most important pathways you need to protect.
To make this actionable, ask these questions for each key user action (e.g., login, transaction, profile update):
This mapping helps you prioritize your audit. An API endpoint that handles wallet transaction data is obviously far more critical than a simple blog comment form. By classifying your data, you can build a clear hierarchy of risk.
Not all assets are created equal. You need to classify them based on their sensitivity and business impact to allocate your audit resources effectively. A simple three-tier system is a great way to start.
For a platform like Wallet Finder.ai, the user database and the systems processing subscription payments would be Class 1. The marketing blog, on the other hand, would likely be Class 3. This classification system lets you focus your deep-dive manual testing where it matters most.
While this guide focuses on web applications, many of these principles apply directly to blockchain components. For a closer look at that side of things, check out our guide on smart contract security.
A top-tier website security audit isn't about picking one tool; it’s about building a versatile toolkit. The most effective approach combines the brute-force speed of automated scanners with the sharp, intuitive eye of a human expert. Relying on just one leaves you exposed.
Automated tools are incredible for casting a wide net and catching common, well-documented vulnerabilities. But they're clueless about business logic flaws—the kind of creative exploits a human attacker loves to find. A balanced strategy uses automation for the heavy lifting and saves manual, human-led testing for your most critical and custom-built features.
The stakes are just too high for half-measures. The global average cost of a data breach has ballooned to $4.44 million. Worse, it takes companies an average of 213 days just to realize they've been compromised. In the SaaS-heavy world of DeFi, a shocking 7% of companies monitor all their applications, while 68% track less than half. This is exactly the kind of gap a hybrid audit closes.
Think of automated scanners as your tireless front-line soldiers. They crawl your website and infrastructure relentlessly, checking for thousands of known vulnerabilities. They are your first, best defense for flagging low-hanging fruit like outdated software, sloppy server configurations, and classic injection flaws.
Your toolkit should include:
Here’s a look at what the dashboard for a powerful open-source tool like OWASP ZAP looks like in action.
Notice how it clearly organizes potential threats by risk level and points to the exact URL. This makes it much easier to triage and start digging into the most critical findings first.
For all its power, automation has a blind spot: context. Scanners are notoriously bad at understanding business logic or spotting complex, multi-stage attacks. This is where a human expert is indispensable. A skilled penetration tester thinks like an attacker, creatively searching for flaws an automated tool would never even know to look for.
Manual testing is the only way to reliably find issues like:
A scanner can tell you if a door’s lock is a known weak model, but it can’t tell you that someone left the key under the mat. That requires human ingenuity and a deep understanding of how the system is supposed to work.
A strong audit uses both automated tools and manual testing, but it's crucial to know what each method excels at. This comparison will help you deploy them strategically to get the most comprehensive view of your security posture.
For a closer look at specific tools you can add to your arsenal, check out our guide on choosing the right security audit software for your project's needs.
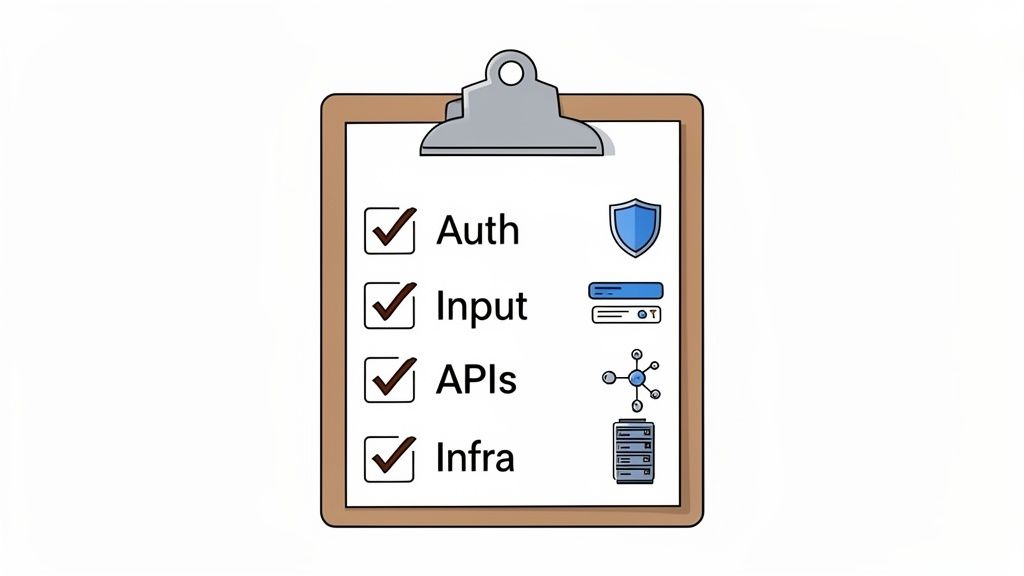
A solid security audit isn’t about randomly poking around for holes. It's a methodical hunt. To do it right, you need a system. A checklist, organized by the most critical parts of your application, turns a huge, scary task into something you can actually manage.
This checklist is built for modern web apps, especially for those of us in the DeFi and web3 world where a single mistake can be catastrophic. We'll break it down into four core areas: Authentication and Authorization, Input Validation, API Security, and Infrastructure Configuration. Think of each one as a potential battleground you need to defend.
This is all about who gets in and what they can do once they're inside. Get this wrong, and you might as well hand an attacker the keys to your entire platform.
/admin into their browser and get access to sensitive controls? You need to test every single user role to make sure they are completely walled off from doing anything they aren't supposed to.I see this all the time: teams focus on authentication but completely forget about authorization. It’s not enough to confirm who a user is. You have to be absolutely ruthless in enforcing what they're allowed to do. An attacker who can't pick the front lock will always check for an open window.
Every single spot a user can type something—a search box, a profile update, a file upload—is a potential weapon they can use against you. Your default mindset should be: all user input is hostile.
Your checklist needs to hammer on these points:
<script> tags into every field. If that script runs, you have a problem.In modern apps, APIs are the central nervous system. They move data between your frontend, your backend, and any other services you're connected to. If your APIs aren't secure, your entire application is compromised.
/api/v1/user/123 to /api/v1/user/456) and see someone else's data? Test this everywhere.Your code could be a fortress, but if it's built on a foundation of sand, it'll crumble. This part of the audit looks at the servers, cloud services, and software that run your application. It’s a huge deal, as 61% of security leaders have seen breaches because of a control failure, and most of those incidents cost over $1M. You can dig into more of these sobering cybersecurity statistics on gitprotect.io.
This systematic review must cover:
*.* to get something working?Discovering vulnerabilities is really only half the battle. Now comes the hard part: turning those findings into actual fixes. You can’t just stare at a long list of problems; you need a structured plan that tells you what to tackle first and what can wait.
The first step is always to figure out what's on fire and what's just a minor burn. A risk-rating matrix helps you quantify the impact and likelihood of each vulnerability, assigning clear categories like High, Medium, and Low.
Key takeaway: Always prioritize the high-risk findings. Neutralize the biggest threats before they have a chance to do real damage.
Once you know your priorities, you need a clear workflow to keep everyone on track. This isn't about bureaucracy; it's about accountability. Every vulnerability needs an owner, a deadline, and a clear status.
A simple, effective workflow looks like this:
For a deeper dive, check out our guide on finding the right security audit service and building expert remediation workflows.
Nothing gets done without clear ownership. Using your project management tool is essential for this process.
Here are a few key practices for effective tracking:
A single source of truth is crucial. When every team member can see real-time updates on each fix, it cuts down on errors and miscommunication.
For critical vulnerabilities, my rule is simple: block the release. No fix, no deploy. This policy keeps your production environment safe and reinforces a culture of accountability.
As you work, document all your remediation actions in a standardized report template. You'll want to include dates, owners, risk ratings, and the steps taken to verify the fix.
Here’s a simple template to get you started:
Consistency is key. When your remediation process is methodical and well-documented, compliance becomes a natural byproduct, not a chore.
Security isn't a one-and-done project. Once your fixes are verified, you need to schedule follow-up scans. This confirms that the patches are holding up and that no new issues have cropped up in the process.
This transforms your audit from a one-off event into a continuous cycle of improvement.
Set up automated alerts to flag any regressions. It's also a great idea to keep a version history of your audit plans and results, which makes it incredibly easy to spot trends over time.
Finally, use reporting dashboards to visualize your progress. Stakeholders love seeing a clear before-and-after view of your security posture. It’s the best way to demonstrate the value of your team's hard work and build confidence in your web3 platform.
Let's be clear: a website security audit isn't a finish line. It's the starting gun. The threats facing your platform are shape-shifters, constantly evolving, which means your defenses have to do the same. This isn't about a one-off project; it's about making security a core, living part of your team's culture.
This shift starts with your calendar. A single audit is just a snapshot in time. To build real, long-term resilience, you need regular, recurring assessments. For high-risk platforms, that means in-depth audits at least quarterly. But every site out there can benefit from automated vulnerability scanning running weekly, if not daily.
If you want to stay ahead of attackers, you have to see what they see—as they see it. This is where continuous monitoring comes in. It gives you a live feed of your security status, flagging new threats the moment they pop up. It’s the difference between being reactive and getting proactive.
A solid monitoring setup needs a few key pieces:
Think of continuous monitoring as your website’s immune system. It’s always on, silently hunting down and neutralizing threats before they can do any real damage. It keeps your security audit from being a static report and turns it into a living process.
Finally, once you've implemented the fixes from your audit, you absolutely have to re-test. This part is non-negotiable. You need to verify that each patch not only plugged the original hole but didn't accidentally create a new one. This final check closes the loop on the audit cycle, ensuring all your hard work translates into genuine security improvements and a much tougher, more resilient platform.
Diving into the world of website security can definitely bring up a lot of questions. Let's walk through some of the most common ones we hear about security audits for web3 platforms.
There's no single magic number, but for most platforms, a deep, comprehensive audit is something you should pencil in annually. Think of it as your yearly security physical.
That's just the baseline, though. You should absolutely be doing more frequent, targeted checks after any major shake-up.
This includes things like:
If you're running a high-stakes platform—think DeFi protocols, NFT marketplaces, or anything handling sensitive user data—you need to be more aggressive. For these, tightening the schedule to semi-annually or even quarterly is a smart move to keep your security posture rock-solid.
Yes, you can absolutely get started on your own. Using automated tools and a solid checklist (like the one in this guide) is a great first step to catch common issues and shore up your basic defenses. It’s a cost-effective way to find and fix the low-hanging fruit.
However, for a truly thorough assessment, nothing beats bringing in a professional cybersecurity expert or a specialized firm. A pro brings an entirely different mindset to the table—a creative, adversarial one. They're trained to think like an attacker and find complex business logic flaws or multi-stage attacks that automated scanners will sail right past.
A scanner checks for known problems; an expert looks for unknown ones. For critical applications, that difference is everything.
People often use these terms interchangeably, but they're not the same thing.
A proper audit usually involves both: the scan finds the potential doors, and the pen test tries to kick them down.
At Wallet Finder.ai, we live and breathe security to protect your on-chain research and trading strategies. While you focus on finding the next alpha, we're busy making sure the platform you rely on is built on a foundation of robust security. Discover profitable wallets and mirror winning trades with confidence. Start your free trial today at Wallet Finder.ai.