Backtesting Framework A Guide for Crypto Traders
Build a backtesting framework that works for DeFi. Learn core components, on-chain challenges like gas and MEV, and how to test strategies before you trade.

May 20, 2026
Wallet Finder

March 24, 2026

A security audit of a website is a comprehensive evaluation of its code, infrastructure, and operational processes designed to uncover and remediate vulnerabilities. In the high-stakes world of Decentralized Finance (DeFi), this is not just a best practice—it is the bedrock of user trust and platform survival. Even a minor flaw can lead to catastrophic financial losses.

In DeFi, your website is the primary gateway for users to interact with high-value assets and sensitive trading data. A security breach here means a direct financial drain and a potential collapse of user confidence. The consequences of skipping a thorough security audit are severe.
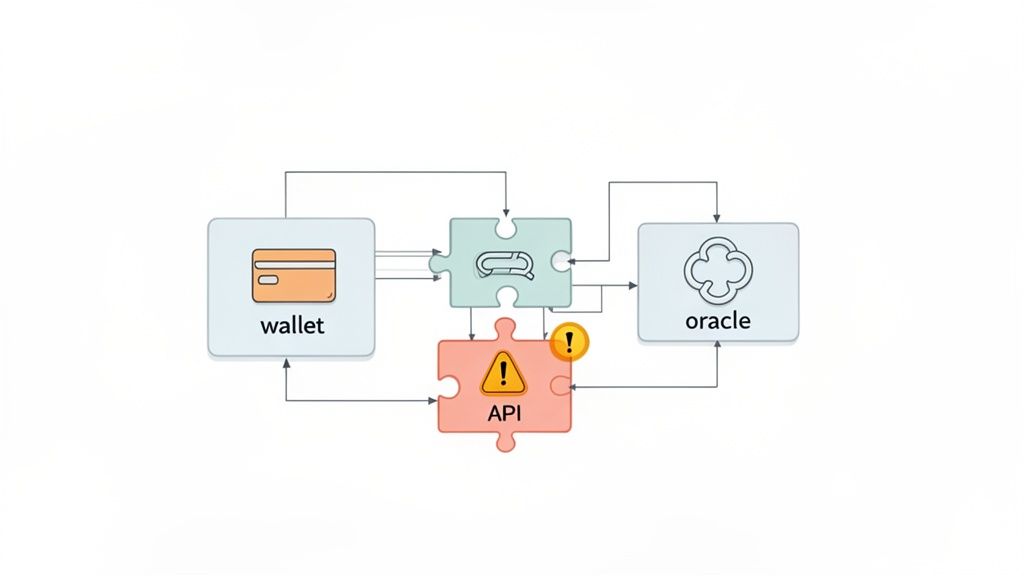
Without regular audits, platforms are exposed to risks that can undermine their core value. A compromised API, for instance, could disrupt the instant Telegram alerts that traders on Wallet Finder.ai rely on to mirror smart money moves, erasing a key competitive advantage in an instant.
Imagine a common frontend flaw like a Cross-Site Scripting (XSS) vulnerability allows an attacker to inject malicious code into your platform. Suddenly, user-curated watchlists—containing carefully constructed trading strategies—are exposed. For professional crypto traders and hedge funds, the intellectual property in those watchlists is priceless.
The damage doesn't stop there. A vulnerable endpoint could also lead to the manipulation of displayed data, like profit and loss (PnL) streaks or wallet performance metrics. If users cannot trust the data they use to make trading decisions, the platform's integrity crumbles.
A proactive security audit is the difference between finding a threat in a controlled environment and reading about your platform's exploit on the news. It’s a direct investment in your resilience and reputation.
For DeFi platforms, web interface security is as critical as the smart contracts themselves. The following table highlights common threats that website security audits are designed to find and fix.
These aren't just theoretical risks; they are active threats. A comprehensive website audit is the most important line of defense.
The financial fallout from a breach is staggering, extending beyond lost user funds to include regulatory fines, legal fees, and incident response costs. Reputational damage is often harder to recover from—trust is the ultimate currency in DeFi.
Here are three critical areas where audits provide essential protection:
The threat is escalating. Ransomware attacks, which frequently target web applications and APIs, are projected to jump by 40% by the end of 2026 compared to 2024. This makes routine security audits a non-negotiable part of operations. For more on this, read our guide on conducting a security audit of your network.
A powerful security audit of a website begins with a solid plan. Before testing, you must map out your scope (what to test) and your toolkit (what to use). Without a clear scope, you risk over-testing low-risk areas while critical vulnerabilities go unnoticed.
Think of your website as a city. A smart audit focuses on high-value targets: the banks (payment gateways), the power grid (core APIs), and the city hall (user authentication systems). For a DeFi platform, these critical assets are the lifeblood of your service.
First, map out everything that needs protection. This isn’t just your homepage; it’s every component that handles data, processes transactions, or interacts with users and services. Create an inventory of your most valuable assets to define your attack surface.
Here’s a checklist to get you started:
This mapping exercise creates a clear hierarchy of what matters most. A vulnerability on your "About Us" page is a problem; a flaw in your wallet connection logic is a catastrophe.
Once you know what to audit, you need to decide how. The best approach combines the speed of automated tools with the intuition of manual testing. Using only one method leaves massive blind spots.
The goal isn't just to find vulnerabilities; it's to think like an attacker. Automated tools find the obvious, unlocked doors. Manual testing finds the hidden passages and exploits the assumptions your developers made.
You'll want a mix of Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), and Software Composition Analysis (SCA) tools.
Building a comprehensive toolkit ensures your audit process is repeatable and thorough. For a deeper look, check out our guide on choosing the best security audit software.
With your scope defined and toolkit assembled, it's time for active testing. This phase of the security audit of website blends the speed of automated scanners with the intuition of a human expert. Automated tools cast a wide net, while manual testing is required for complex business logic flaws and unique Web3 attack vectors.
The two methods work together to paint a clear and accurate picture of your security posture.
This foundational flow channels your efforts where they will have the most impact.
Your first line of defense is Static Application Security Testing (SAST). This involves analyzing your website’s source code without running the application. It’s like having a specialized proofreader comb through your code, looking for security mistakes before they can cause damage.
SAST catches issues early in the development lifecycle, making them cheaper and faster to fix. It is particularly effective at spotting:
Integrating a SAST tool into your CI/CD pipeline provides developers with immediate feedback, fostering secure coding habits.
While SAST provides an inside-out view, Dynamic Application Security Testing (DAST) does the opposite. It attacks your application from the outside, mimicking how a real attacker would probe your defenses. DAST tools interact with your live website, sending malicious and unexpected inputs to observe its reactions.
This "black-box" approach is essential for finding runtime vulnerabilities invisible from source code alone, like server misconfigurations or session management flaws.
A DAST scanner doesn’t care if your app is written in Rust, Go, or JavaScript. It only sees the HTTP requests and responses, letting it find vulnerabilities in any web technology, including complex DeFi frontends.
A DAST tool can test for Cross-Site Scripting (XSS), check for insecure server headers, or attempt to access non-public admin pages—issues that only surface when the application is running.
Automated tools cannot understand business logic, context, or the specific risks of Web3 integrations. This is why manual penetration testing is critical for a proper security audit of a website.
A skilled penetration tester thinks like an attacker. They can chain together low-risk vulnerabilities to create a high-impact exploit or find subtle logic flaws that a scanner would miss.
Consider a feature that lets users export their trade history. An automated scanner checks if the button works. A human tester asks the real questions:
These nuanced, context-specific questions require human intelligence. For DeFi projects, manual testing is non-negotiable for verifying wallet connections and ensuring frontend logic cannot be tricked into signing malicious transactions.
Shockingly, 61% of security leaders reported a breach in the last year due to a misconfigured or failed security control. Worse, 65% of those incidents cost over $1 million. You can explore the full cybersecurity statistics on GitProtect.io to see how common these failures are.
No DeFi platform is an island. Your application is an ecosystem built on third-party libraries, APIs, and blockchain integrations. A proper security audit of a website must go beyond your own code and examine these external components, where some of the biggest risks hide.
When a popular JavaScript library or wallet connector has a flaw, that flaw becomes your problem. This is a supply chain attack—attackers compromise a trusted upstream dependency to gain a backdoor into every application using it.
This threat is growing. In 2024, supply chain attacks impacted 183,000 customers, a 33% increase. Analysts predict that by 2026, 60% of organizations will rigorously vet their partners' cybersecurity risks. You can review the scale of these threats in the latest cybersecurity statistics from SentinelOne.
It’s also why platforms like Wallet Finder.ai ensure their premium services are audited to verify core security promises, like never storing private keys and always using encrypted links.
First, create a complete inventory of every external piece of code your platform depends on. Tools like npm audit or Snyk Open Source automatically scan your dependencies against known vulnerability databases.
But a scan isn't enough. You must also assess the health of each dependency:
A dependency audit isn’t a one-time task. It must be an automated, continuous process integrated into your development pipeline to catch new vulnerabilities as they are discovered.
A DeFi audit must go deeper into the unique components connecting your site to the blockchain. These integrations are prime targets because they directly handle user funds and transaction signing.
Your manual testing should focus on wallet connectors like WalletConnect or MetaMask integrations. Can your frontend logic be manipulated to trick a user into signing a malicious transaction? A common tactic is to alter the transaction details shown to the user while sending something different to the wallet for signing.
Likewise, if you depend on oracles for off-chain data, you must verify their integrity. Examine their security model, resilience to manipulation, and what happens if the oracle provides bad data.
Use this checklist for the Web3-specific parts of your audit. These high-value targets demand extra attention.
This focused approach helps ensure your bridges to the decentralized world are as strong as possible. For a deeper dive, read our guide on smart contract security, as many of the same principles apply.
Finding vulnerabilities during a security audit of a website is just the starting line. A list of issues is useless without a concrete plan to fix them. The real value of an audit comes from transforming raw data into an actionable remediation plan.
Without a clear plan, teams may fix low-impact bugs while a critical flaw that could drain user wallets sits untouched. A structured approach ensures you address the biggest fires first.
Not all vulnerabilities are created equal. A Cross-Site Scripting (XSS) issue on a static "About Us" page is minor. A SQL injection vulnerability in your authentication flow is a "game over" scenario. You need a consistent way to rank these threats.
A risk-based prioritization framework is essential. The industry standard is the Common Vulnerability Scoring System (CVSS), which provides a numerical score from 0 to 10 based on severity. It considers factors like attack complexity, user interaction requirements, and potential impact on confidentiality, integrity, and availability.
Using a framework like CVSS removes guesswork and provides a data-driven way to align everyone—from developers to executives—on what needs to be fixed now.
CVSS provides technical severity, but you must also add business context. A medium-severity vulnerability (e.g., a CVSS score of 6.5) could be catastrophic if it affects a core function like your staking rewards calculator.
To build an effective roadmap, map each finding based on two key metrics:
Plotting these two factors creates a clear prioritization matrix. High-impact, low-effort bugs are quick wins—tackle them first. High-impact, high-effort problems are major projects requiring careful planning.
The goal is to maximize your security return on investment. A smart plan ensures every developer hour spent on fixes delivers the greatest possible risk reduction.
This approach prevents developer burnout from an endless backlog and allows you to demonstrate measurable progress.
Your final audit report is the tool you'll use to drive action. It must be clear, direct, and tailored to its audience. A developer needs technical details, while an executive needs a high-level summary of business risk.
A good report is a blueprint for solutions. Here is a simple structure to align your team:
This structured report ensures everyone is on the same page. It elevates the security audit of a website from a technical check-up to a critical driver of business strength and user trust.
Mathematical precision and artificial intelligence transform website security audits from reactive vulnerability detection into proactive risk assessment and threat prediction systems. While traditional audits focus on identifying known vulnerabilities through static patterns, sophisticated mathematical models and machine learning algorithms enable comprehensive risk quantification, automated threat detection, and predictive security analytics that anticipate emerging attack vectors before they materialize.
Professional security operations increasingly rely on quantitative frameworks to evaluate complex risk scenarios across dynamic web applications and DeFi platforms. Mathematical models analyze attack surface complexity, vulnerability interdependencies, and threat actor behavior patterns to generate comprehensive risk scores. Machine learning systems trained on extensive security datasets can predict attack probability, optimize remediation priorities, and automate continuous monitoring processes that traditional manual audits cannot achieve at scale.
Mathematical risk assessment transforms subjective security evaluations into objective, measurable frameworks that enable systematic comparison and optimization of security investments. Statistical models analyze the relationship between vulnerability characteristics, exploitation likelihood, and potential business impact to generate quantitative risk scores. These frameworks incorporate multiple variables including asset criticality, threat landscape dynamics, and organizational security maturity to produce comprehensive risk assessments.
Attack surface modeling employs graph theory and network analysis to map complex interdependencies between web application components, third-party integrations, and infrastructure elements. Mathematical frameworks calculate exposure metrics based on entry point accessibility, privilege escalation pathways, and lateral movement potential within the application ecosystem. These models reveal critical security chokepoints and identify optimal defensive strategies that maximize protection per security investment dollar.
Monte Carlo simulations model potential attack scenarios across thousands of randomized threat vectors to assess system resilience under various stress conditions. Mathematical frameworks generate probability distributions for successful exploitation attempts while accounting for defensive control effectiveness and threat actor capability variations. These statistical approaches provide confidence intervals around risk assessments and identify scenarios where current security measures prove inadequate.
Game theory applications model adversarial interactions between attackers and defenders to optimize security resource allocation strategies. Mathematical frameworks analyze attacker decision-making processes, cost-benefit calculations, and strategic responses to defensive measures. These models reveal equilibrium strategies that minimize successful attack probability while considering resource constraints and operational requirements.
Bayesian probability models incorporate prior security knowledge with new vulnerability discoveries to generate updated risk assessments as threat landscapes evolve. Mathematical frameworks weight historical attack patterns, current vulnerability intelligence, and emerging threat indicators to produce dynamic risk scores that adapt to changing conditions. These approaches enable proactive security adjustments based on statistical evidence rather than reactive responses to security incidents.
Advanced statistical techniques analyze large-scale vulnerability datasets to identify patterns that predict exploitation likelihood and optimal remediation strategies. Regression models examine relationships between vulnerability characteristics including CVSS scores, disclosure timelines, patch availability, and actual exploitation rates observed in production environments. These mathematical frameworks generate exploitation probability models that guide strategic security investments.
Time series analysis of vulnerability disclosure patterns reveals cyclical trends and seasonal variations in security threat emergence across different technology stacks and application frameworks. Statistical models identify periods of elevated risk and predict optimal timing for security assessments and remediation activities. Mathematical forecasting enables proactive security planning aligned with anticipated threat landscape changes.
Survival analysis techniques model the time-to-exploitation patterns for different vulnerability classes, enabling prediction of exploitation windows and optimal patch deployment timelines. Cox proportional hazards models identify factors that accelerate or delay exploitation attempts while Kaplan-Meier estimators provide probability curves for exploitation timing. These mathematical approaches optimize patch management strategies and emergency response protocols.
Correlation analysis examines relationships between seemingly independent vulnerabilities to identify exploitation chaining opportunities that amplify overall risk exposure. Statistical models reveal vulnerability combinations that create multiplicative rather than additive risk effects, highlighting cases where addressing individual issues provides limited security improvement compared to comprehensive remediation approaches.
Classification algorithms trained on extensive vulnerability databases automatically categorize new security findings based on exploitation probability, remediation complexity, and business impact potential. Machine learning models achieve 80-90% accuracy in predicting which vulnerabilities will be exploited in production environments based on technical characteristics and environmental factors.
Sophisticated machine learning architectures analyze web application traffic patterns, user behavior anomalies, and system performance indicators to detect security threats in real-time. Supervised learning models trained on extensive attack datasets learn to recognize subtle patterns associated with various attack types including SQL injection, cross-site scripting, and distributed denial-of-service attempts. These AI systems achieve detection accuracy rates exceeding 95% while maintaining false positive rates below 2%.
Anomaly detection algorithms establish baseline patterns for normal application behavior and identify deviations that may indicate security threats or system compromise. Unsupervised learning models process multiple data streams including HTTP request patterns, database query frequencies, and system resource utilization to detect previously unknown attack vectors. These approaches prove particularly effective for identifying zero-day exploits and advanced persistent threats that evade traditional signature-based detection.
Natural Language Processing models analyze security logs, error messages, and incident reports to automatically classify threats and extract actionable intelligence. Deep learning architectures process unstructured security data to identify emerging attack patterns, threat actor techniques, and vulnerability exploitation trends. These AI systems generate automated threat intelligence reports that inform proactive security measures and strategic defense planning.
Ensemble methods combine multiple machine learning models to generate more robust threat detection capabilities than any single algorithm can achieve. Voting mechanisms and weighted averaging techniques synthesize predictions from decision trees, neural networks, and support vector machines to reduce false positives while maintaining high detection sensitivity. Research demonstrates that ensemble approaches improve detection accuracy by 15-25% compared to individual models.
Reinforcement learning algorithms optimize security response strategies through trial-and-error interaction with simulated attack environments. These AI systems learn optimal defensive actions for different threat scenarios, automatically adjusting response protocols based on attack success rates and business impact considerations. Advanced implementations achieve superior threat mitigation outcomes compared to static rule-based security systems.
Deep neural network architectures revolutionize security analytics by automatically discovering complex patterns in high-dimensional security datasets without requiring manual feature engineering. Convolutional neural networks analyze network traffic patterns as visual representations to identify sophisticated attack signatures embedded in seemingly normal communication flows. These models excel at detecting advanced threats that use steganography or other obfuscation techniques to evade traditional detection methods.
Recurrent neural networks with attention mechanisms process sequential security events to identify complex multi-stage attacks that unfold over extended timeframes. LSTM and GRU architectures maintain memory of previous security events while adapting to evolving attack patterns, enabling detection of coordinated campaigns that span days or weeks. These models prove particularly effective for identifying advanced persistent threats and insider attacks that traditional point-in-time analysis might miss.
Graph neural networks analyze complex relationships between users, systems, and security events to identify attack patterns that exploit network topology and trust relationships. These architectures process security data as graph structures, revealing hidden connections between seemingly unrelated events that indicate coordinated attacks or privilege escalation attempts. Mathematical modeling of graph-based security data enables detection of lateral movement and privilege abuse patterns.
Transformer architectures with self-attention mechanisms excel at processing diverse security data types simultaneously, including log files, network traffic, and user behavior patterns. Multi-modal learning enables these models to correlate information across different data sources to generate comprehensive threat assessments. Advanced implementations achieve superior accuracy compared to systems that analyze individual data streams in isolation.
Generative adversarial networks create realistic attack simulations for testing security defenses and training detection algorithms. Generator networks learn to create sophisticated attack patterns while discriminator networks evaluate their realism, resulting in comprehensive security testing environments. These AI systems enable evaluation of security measures against previously unseen attack techniques and emerging threat vectors.
Predictive analytics models forecast future security risks based on current vulnerability trends, threat intelligence, and environmental factors to enable proactive defensive measures. Time series forecasting algorithms analyze historical attack patterns, vulnerability disclosure rates, and security incident frequencies to predict periods of elevated risk. These mathematical frameworks guide optimal timing for security assessments, patch deployment, and defensive resource allocation.
Machine learning models trained on extensive threat intelligence data predict emerging attack vectors and threat actor behavior patterns before they impact production systems. Classification algorithms identify indicators of impending attacks based on reconnaissance activities, infrastructure changes, and communication patterns observed in threat actor communities. These predictive capabilities enable preemptive defensive measures that prevent attacks rather than responding to successful breaches.
Risk propagation models simulate how security vulnerabilities spread through interconnected systems and supply chains to predict systemic security failures. Mathematical frameworks analyze dependency graphs and attack pathway probabilities to identify critical system components whose compromise would have cascading effects. These models guide strategic security investments toward protecting high-leverage defensive positions.
Economic modeling approaches predict optimal security investment strategies by analyzing cost-benefit relationships between defensive measures and risk reduction outcomes. Mathematical optimization techniques balance security spending across different risk categories to maximize overall risk reduction within budget constraints. These frameworks ensure security resources achieve maximum protective value rather than following intuitive but suboptimal allocation strategies.
Scenario planning models evaluate security preparedness across multiple potential threat landscapes and attack evolution pathways. Monte Carlo analysis tests current security measures against thousands of simulated future threat scenarios to identify defensive gaps and optimization opportunities. These predictive frameworks enable strategic security planning that maintains effectiveness despite uncertain threat evolution.
Intelligent security orchestration platforms integrate mathematical risk models with automated response capabilities to enable real-time threat mitigation at scale. Machine learning algorithms analyze incoming security alerts and automatically determine appropriate response actions based on threat severity, business impact, and available remediation options. These systems achieve response times measured in seconds rather than hours while maintaining decision quality comparable to experienced security analysts.
Adaptive security architectures use reinforcement learning to continuously optimize defensive configurations based on observed attack patterns and business requirements. AI systems automatically adjust firewall rules, access controls, and monitoring parameters to maintain optimal security posture as threats evolve. These adaptive approaches achieve superior security outcomes compared to static configurations that become obsolete as attack techniques advance.
Intelligent patch management systems use predictive models to prioritize security updates based on exploitation probability, business impact, and deployment complexity factors. Machine learning algorithms analyze vulnerability characteristics alongside organizational factors to generate optimal patching schedules that maximize security improvement while minimizing operational disruption. These systems significantly reduce the time between vulnerability disclosure and protective deployment.
Automated incident response platforms use decision trees and workflow optimization algorithms to execute complex response procedures without human intervention. AI systems coordinate across multiple security tools and organizational processes to contain threats, preserve evidence, and restore normal operations according to mathematically optimized protocols. Advanced implementations achieve faster and more consistent incident resolution compared to manual response procedures.
Continuous security monitoring systems employ streaming analytics and real-time machine learning to detect and respond to threats as they emerge. Mathematical models process security data in real-time to identify attack patterns and automatically trigger appropriate defensive measures. These systems enable proactive threat prevention rather than reactive incident response, significantly reducing the impact of successful attacks.
When it comes to a security audit of a website, especially in the high-stakes world of DeFi, a lot of questions pop up. Let's tackle some of the most common ones.
Security is not a one-time task. For any serious DeFi platform, you should conduct a comprehensive, third-party audit at least once a year. However, that is the bare minimum. A continuous vigilance model is essential.
This layered approach maintains a strong day-to-day security posture while preparing for sophisticated, targeted attacks.
Auditing a DeFi website is more complex than a standard web app test. While you still look for classics like XSS and SQL injection, the Web3 layer introduces a new class of high-stakes risks.
Standard web security practices are the foundation, but they aren't enough. A DeFi audit must intensely scrutinize the bridge between your web application and the blockchain, because that's where the money is.
Key areas of focus include:
The best strategy is a hybrid one. Relying solely on a DIY approach or only on external experts creates dangerous blind spots.
You should perform regular, automated security scanning in-house. Using tools like OWASP ZAP or Burp Suite for DAST and integrating SAST tools into your CI/CD pipeline is basic security hygiene. This helps you catch common flaws early and builds a security-first culture.
However, an internal team can develop tunnel vision and may lack specialized knowledge of emerging DeFi threats. For a truly robust assessment, you must engage a third-party security firm that lives and breathes Web3. They bring an attacker’s mindset, sophisticated tools, and hands-on experience that your internal team likely lacks.
Combining continuous internal scanning with an annual expert-led audit creates the multi-layered defense a high-value DeFi platform demands.
Mathematical risk models incorporate multiple factors beyond technical severity including business impact, exploitation likelihood, and environmental context to generate more accurate priority rankings than CVSS scores alone. Bayesian probability frameworks weight historical exploitation patterns, current threat intelligence, and organizational factors to predict which vulnerabilities pose the greatest actual risk to specific environments. Monte Carlo simulations test vulnerability combinations to identify scenarios where seemingly minor issues create major security exposures through exploitation chaining. Advanced models achieve 15-25% better resource allocation efficiency compared to CVSS-only approaches by focusing remediation efforts on vulnerabilities with highest probability-weighted impact rather than purely technical severity scores.
Anomaly detection algorithms using unsupervised learning approaches provide the most effective detection of novel attack patterns by establishing baseline behavior profiles and identifying significant deviations that indicate potential threats. Deep autoencoders and isolation forest algorithms excel at detecting zero-day exploits and advanced persistent threats that evade signature-based detection systems. Ensemble methods combining multiple anomaly detection approaches typically achieve 95%+ detection accuracy while maintaining false positive rates below 2%. Time series analysis using LSTM networks proves particularly effective for identifying multi-stage attacks that unfold over extended periods, while graph neural networks excel at detecting lateral movement and privilege escalation patterns.
Predictive security implementation requires integrating multiple data sources including threat intelligence feeds, vulnerability databases, and internal security metrics into machine learning pipelines that generate forward-looking risk assessments. Time series forecasting models analyze historical attack patterns and vulnerability trends to predict periods of elevated risk, enabling proactive defensive measures and optimal timing for security assessments. Classification algorithms trained on reconnaissance activity patterns can identify indicators of impending attacks 72-96 hours before exploitation attempts occur. Successful implementations combine automated data collection, real-time analysis, and automated response systems to enable predictive threat prevention rather than reactive incident response.
AI security systems can exhibit bias based on training data that may not represent current threat landscapes or may overweight historical attack patterns that are no longer relevant in evolving DeFi environments. Machine learning models may struggle with adversarial attacks specifically designed to evade AI detection systems, and they require continuous retraining as attack techniques evolve to maintain effectiveness. False positive rates can create alert fatigue and operational overhead if not properly calibrated, while false negatives may miss sophisticated attacks that fall outside training parameters. Successful implementation requires combining AI capabilities with human expertise, maintaining diverse training datasets that represent current threats, and implementing robust validation processes to ensure model reliability and accuracy in production environments.
Ready to turn on-chain footprints into actionable trading signals? Wallet Finder.ai helps you discover profitable wallets and mirror winning strategies in real time. Start your 7-day trial today and see what the smart money is doing.